New Capabilities to Create a Unified View of Your Threat Landscape, Prioritize Relevant Threats, and Accelerate Response to Threats

Your unique threat landscape is constantly changing, based on countless data points: things like the industry you are in, what technologies you use, your supply chain, and threat actors themselves. With so many data points to keep track of and research, it can be a time-consuming process to scale, especially as your attack surface expands.
That’s where we come in - Recorded Future has long pioneered making threat research and prioritization easier for organizations with our Intelligence Cloud, which collects and structures adversary and victim data from text, imagery, and technical sources, then uses natural language processing and machine learning to analyze and map associations across billions of entities in real-time.
This week, at our annual industry conference, PREDICT, we announced exciting new capabilities related to AI and Collective Insights. These capabilities extend our mission of creating a unified view of your threat landscape, prioritizing relevant threats, and accelerating response to threats.
At RSA 2023, we unveiled Collective Insights, a new capability that combines your internal telemetry with threat insights from Recorded Future and Threat Maps, representing your unique threat landscape.
A Holistic View of Your Threat Landscape
Today, we’re excited to announce the combination of these two incredible capabilities. Now, the Threat Map will take into consideration detections seen in your environment, making it a tool for the holistic prioritization of threats. This enables you to set priorities, identify areas of focus, and tailor additional security activities - like red-teaming and other proactive initiatives.
Taking it a step further, we have made Collective Insights more holistic, enabling clients to bring more insights from all of their security tools, including EDR, email, and identity - in addition to SIEM and SOAR.
Automate Threat Investigation & Prioritization
Once you have a view of your holistic and unique threat landscape, it’s essential to streamline investigation and prioritization of those threats. The Threat Map already goes a long way to showing you what threats matter and today we launched additional features to enhance threat investigation and prioritization workflows.
During RSA 2023, we unveiled AI Insights, revolutionizing the way analysts conduct research on entities, summarizing everything Recorded Future knows about an entity into natural language to quickly understand impact, without needing to spend precious time summarizing yourself. Today, we’ve launched the next generation of Recorded Future AI, a tool to engage with our Intelligence Cloud through a simple conversational interface. Think of us as an invaluable extension of your team, assisting you in obtaining the essential answers to swiftly prioritize your investigation and response efforts!
Additionally, we’ve expanded availability of AI Insights to our Threat Map - meaning you receive a summary of your specific threat landscape to understand the impact on you, without having to spend precious time crafting it yourself.
AI Insights Client Testimonial
A Forbes Global 2000 travel company found Recorded Future AI valuable for accelerating the vulnerability triage process, as the AI summary provides the team with an understanding of the initial risk and usually also highlights important factors like the initial source of the exploit right off the bat. With the AI summary, the team can quickly assess whether the CVE merits additional investigation and which vulnerabilities he should spend his time prioritizing.
Accelerate Response to Threats
Prioritizing the threats that matter most to your organization and then investigating them further, either as part of the prioritization or response process is important. However, closing the loop by driving action with intelligence and accelerating response to those threats is essential. Over the past quarter, Recorded Future has been developing capabilities with our integration partners to run threat hunts automatically based on changes in your Threat Map, inside your SIEM or SOAR tools to find evidence related to the malware that has been identified as a potential threat. This helps ensure that you are only focusing on the threats that are critical today.
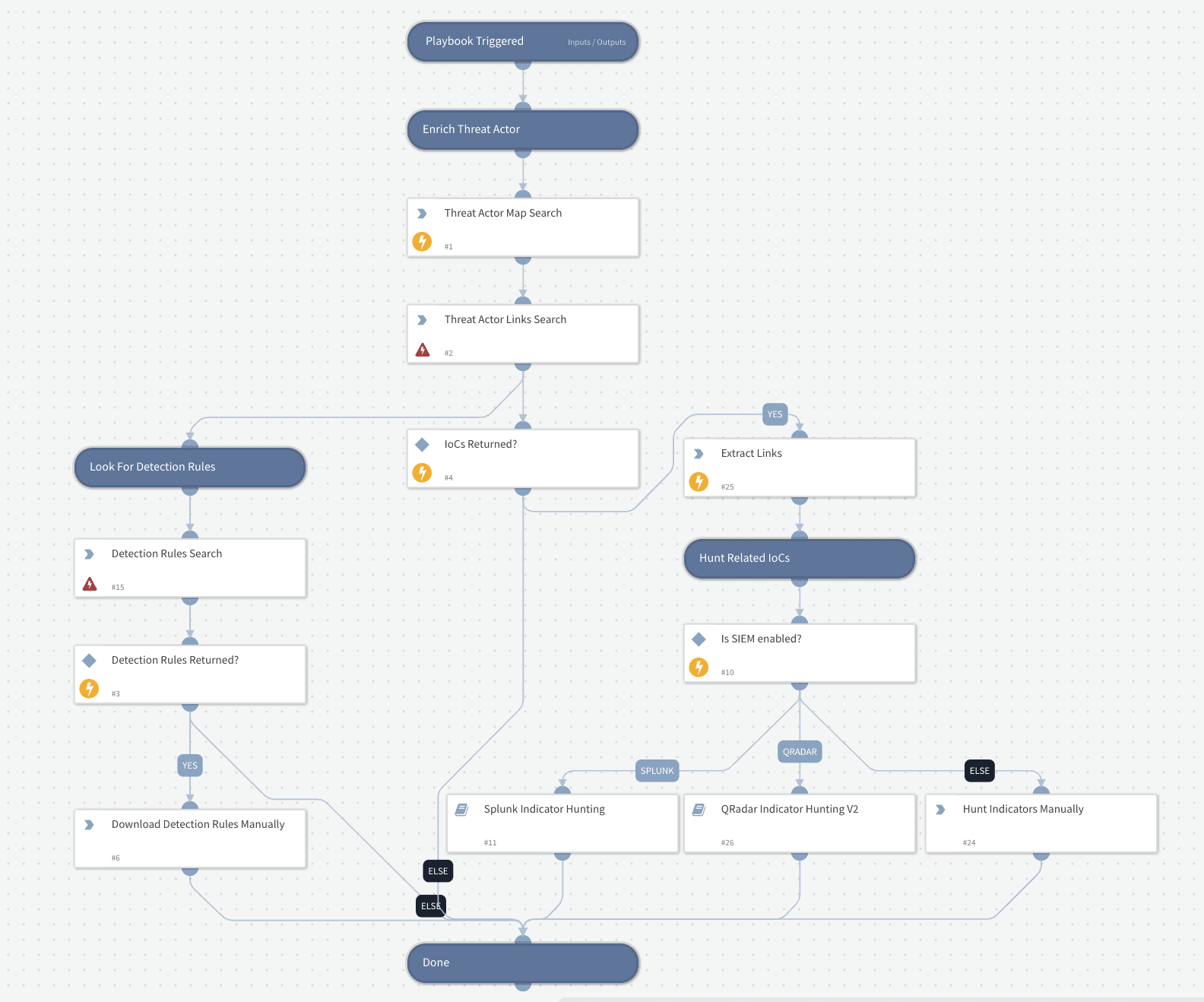 Playbook that automates threat hunting based on changes to entities in an organizations unique Threat Map.
Playbook that automates threat hunting based on changes to entities in an organizations unique Threat Map.
Interested in learning more about our product improvements in action?
Related