3 Ways Threat Intelligence Saves Time and Money

Key Takeaways
- A new IDC white paper found that organizations saw significant time and money savings after incorporating Recorded Future into their already existing security systems.
- Organizations grew more efficient in three main areas: security teams had more time to react to threats, staff productivity increased, and businesses avoided costly penalties and fines resulting from security breaches.
- Threat intelligence gave the organizations surveyed by IDC more time and context to react to threats and helped them raise their security posture across teams.
When IT security teams already rely on a vast number of security systems — sometimes nearly two dozen — to keep their organizations secure, the thought of keeping up with yet another system, like a threat intelligence solution, might sound like a headache.
But the reality is, organizations that know how to apply valuable insights from threat intelligence to their cybersecurity decision-making process are able to work faster and smarter.
That’s what IDC determined in a recent survey of organizations who incorporated Recorded Future’s threat intelligence solution into their already existing security systems. Rather than threat intelligence being just an added bonus (or even a distraction), organizations of all sizes consistently found that it saved them time and money while improving their security posture.
3 Key Results of Using Threat Intelligence
IDC’s research uncovered significant cost savings across IT security teams — $39,638 per team member per year, to be exact. Considering that the average starting salary of an IT security analyst is roughly twice that, in cost savings alone, that’s like hiring a free third analyst for every two your organization already has.
Those quick figures illustrate how IDC found that organizations saw their threat intelligence investment paid back after only four months on average. But in what ways, exactly, are the organizations who started using threat intelligence seeing their costs reduced?
IDC found that the cost savings come in three main areas: security teams have more time to react to threats, staff productivity goes up, and organizations more easily avoid costly penalties and fines resulting from security breaches.
1. Security teams have more time to react to threats.
One statistic that demonstrates how fast cybersecurity threats move is that, on average, new vulnerabilities will either be exploited within the first two weeks of being found or not at all. That means you often have a matter of only days to react when a new vulnerability affecting the systems you use is identified.
IDC found that organizations identified threats 10 times faster and resolved them 63 percent quicker when they started using threat intelligence.
It’s how these statistics break down that reveals the significant difference threat intelligence makes. Before using Recorded Future, organizations identified threats only 0.4 days on average before they became impactful, and took 15.6 hours on average to resolve them.
With Recorded Future threat intelligence, the average time that threats were identified before becoming impactful stretched to 4.1 days — 10 times faster — and the time it took security teams to resolve them was lowered to only 5.7 hours on average — 63 percent quicker.
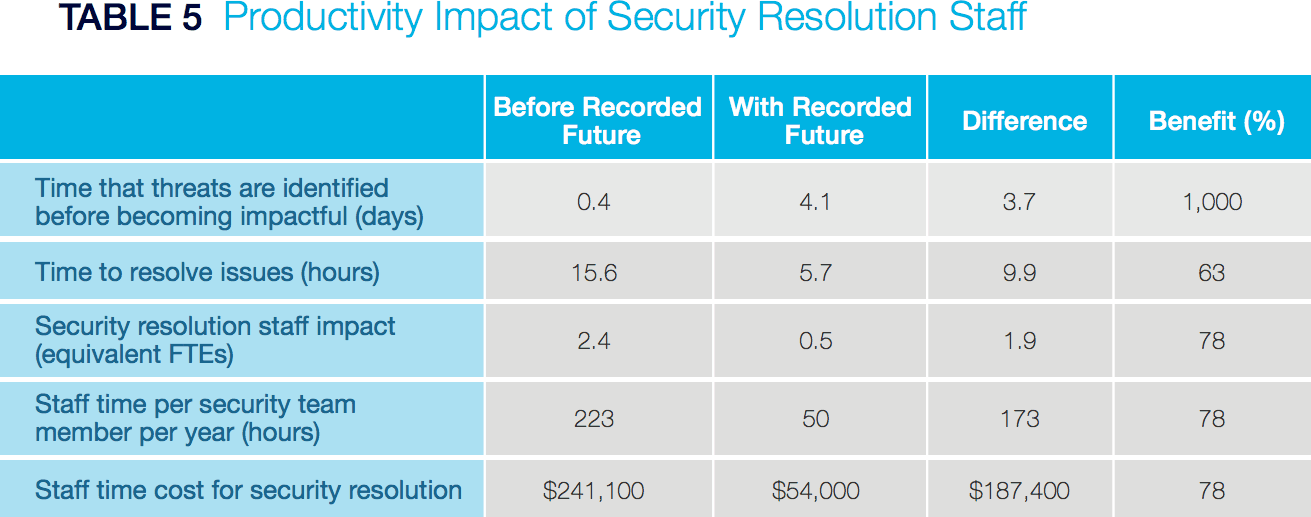
Source: IDC, 2018
Security teams are also able to identify 22 percent more threats before they become impactful. That’s especially consequential when a recent Cisco study showed that security teams ignore almost half of all alerts they see daily and only a third of those they do look at are legitimate. The huge slog of manually sorting through mountains of data and avoiding false positives is one reason why security analysts struggle to keep up with risks in a timely manner.
Automating the collection and processing of threat data is a scalable solution to this problem, helping organizations more quickly and accurately assess their risk profile. “As we have grown and acquired new technologies and expanded into new areas,” one organization surveyed by IDC noted, “[threat intelligence] allows us to monitor for threats in areas where we are fairly new entrants and where we might not have the same security infrastructure as we would have in our existing business.”
2. Staff productivity increases.
Every team, including staff responsible for operations, investigation, report compilation, and threat resolution, saw their work made easier by incorporating threat intelligence into their already existing security systems, with 32 percent lower costs overall.
Organizations that started using threat intelligence also reduced unplanned downtime due to security breaches or last-minute, critical updates needing to be applied.
Handling threats before they became critical issues let security teams reduce unplanned downtime by 86 percent — not a small number when considering that the average cost for every minute of downtime is around $9,000, depending on the size of your organization.
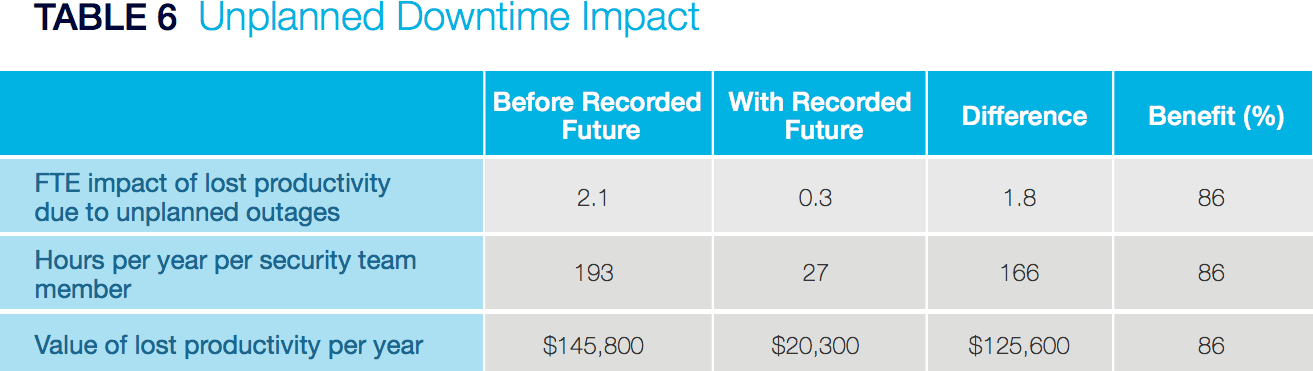
Source: IDC, 2018
3. Organizations avoid more damaging penalties and fines resulting from security breaches.
With most organizations keeping the personally identifiable information of their customers on file — things like credit card numbers, dates of birth, and so on — data breaches represent huge risks, incurring not only expensive fines and penalties, but also less quantifiable damage, such as a tarnished reputation and loss of public trust.
Threat intelligence helps mitigate that risk, to the order of $1,033,300 dollars per breach on average among the organizations surveyed by IDC.
Threat Intelligence Mitigates Risk
It’s a huge challenge trying to make sense of the vast amounts of raw data and alerts that teams face today across multiple unconnected security platforms. Making sense of it all takes a threat intelligence solution that aggregates all of that data automatically and provides additional context.
To learn more about how threat intelligence can help your organization achieve significant time and cost savings, download your free copy of the recent IDC white paper, “Organizations React to Security Threats More Efficiently and Cost Effectively With Recorded Future.”
Related