What is the Cyber Kill Chain?
What is the cyber kill chain and why is it critical for your organization's cyber defense? Today we will try to answer this question.
Originating from Lockheed Martin, the cyber kill chain is a crucial framework for understanding and disrupting the sequence of steps attackers take during a cyberattack.
By laying out each phase, from initial reconnaissance to the execution of objectives, this model provides security professionals with a strategic advantage in detecting and halting threats before they escalate into major breaches.
In this article, we’ll cover the 7 cyber kill chain stages, explore its evolution in the face of new threats, and share defense strategies that leverage its structured approach for robust modern cybersecurity.
Key Takeaways
- The Cyber Kill Chain framework is a model that outlines the stages of a cyberattack, providing security teams with a structured approach to predict and counteract potential threats.
- While originally composed of seven stages, the Cyber Kill Chain framework has evolved to include additional steps like monetization, reflecting the changing tactics of cyber attackers influenced by advancements in technology and a shifting cyber landscape.
- The real-world effectiveness of the Cyber Kill Chain model is well-documented, with its application enabling organizations to understand and disrupt cyberattacks at various stages, enhancing proactive cybersecurity defense strategies.
What is the Cyber Kill Chain Framework?
The Cyber Kill Chain framework, also known as the cyber security kill chain, serves as an instrumental tool for blue teams, offering a structured guide to organize and interpret security events and establishing a shared language for security professionals.
Developed as a model to conceptualize the sequence of steps an attacker undergoes during a cyberattack, its design aims to achieve specific objectives. Its birth heralded a new era in understanding cyber threats, revolutionizing the way organizations perceive and respond to them.
Far from being merely theoretical, this model operates as a practical instrument for identifying and halting advanced cyberattacks before they harm an organization. In the hands of an experienced cybersecurity team, the Cyber Kill Chain framework can be the difference between a minor incident and a major disaster.
Brief History of the Cyber Kill Chain
The birthplace of the Cyber Kill Chain framework was the labs of Lockheed Martin, where the military concept was initially utilized for information security by computer scientists. This adaptation from traditional military models to the digital world was not just a simple translation, but a reimagining of concepts to fit a new environment.
The genius of Lockheed Martin’s researchers lies in their ability to translate the chaotic world of cyber warfare into this structured approach, providing a clear path for defense against digital threats.
How does it work?
The Cyber Kill Chain provides this understanding by breaking down a cyberattack into core stages, known as the cyber kill chain process.
As the cyber kill chain continues to evolve, it is crucial to stay informed on these stages and utilize cyber kill chain maps for better visualization. Understanding how the cyber kill chain works can greatly enhance your defense strategies:
- Reconnaissance
- Weaponization and delivery
- Command and control
- Lateral movement
- Data exfiltration
Each phase presents a unique opportunity to detect and stop cyber attacks as they progress through the cyber attack lifecycle.
Picture each phase as a piece of a puzzle. With every piece, the picture becomes clearer, and the attacker’s intentions are revealed. The framework’s true power lies in its ability to provide a holistic view of an attack, allowing security teams to intervene and disrupt the attack at any stage.
Adapting the Model for Today's Cyber Landscape
The Cyber Kill Chain model is far from being a static notion.** Like any effective tool, it has adapted to the evolving cyber landscape to address modern threats** such as insider attacks, advanced ransomware, and the emergence of novel attack techniques. This evolution has been influenced by advancements in technology, including cloud computing and the Internet of Things (IoT), which have significantly altered the nature of cyber attack strategies.
This evolution is a testament to the model’s flexibility and relevance. Despite new challenges and shifting attack vectors, the Cyber Kill Chain model remains a powerful tool to understand the anatomy of a cyberattack and develop effective defense strategies against ever-evolving threats.
Additionally, integrating insights from the Diamond Model of Intrusion Analysis can further refine this understanding, offering another layer of analysis to complement the Cyber Kill Chain framework.
7 Phases of the Cyber Kill Chain
Akin to a digital predator in pursuit of its prey, a cyber attacker follows a structured sequence of phases to infiltrate internal data or assets. Each phase of the cyber kill chain, from reconnaissance to monetization, presents an opportunity to detect and stop the threat. The ‘action’ phase signifies the achievement of the primary attack objectives, which could range from:
- data theft
- system disruption
- unauthorized access
- spreading malware
- identity theft
- espionage
Some experts even advocate for the inclusion of an eighth phase, monetization, acknowledging the financial motivation often at the core of cyberattacks.
Understanding these phases is akin to deciphering the attacker’s playbook. With it, organizations can predict the attacker’s next move and devise tactics to disrupt their plans.
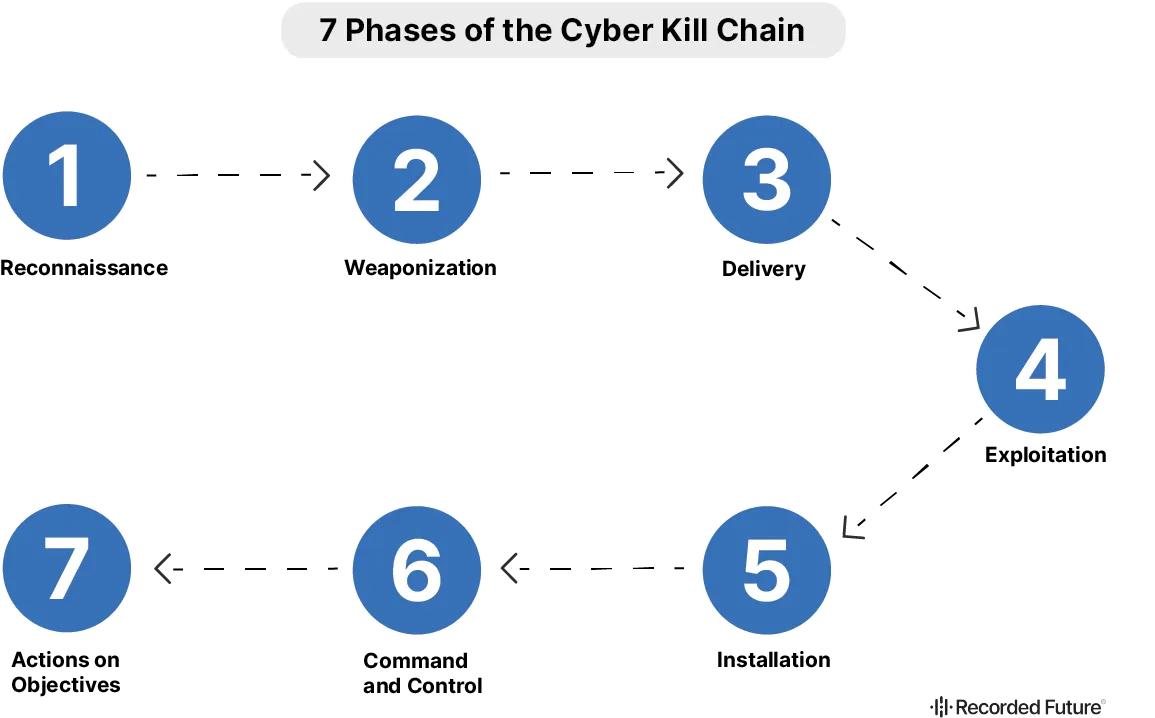
The framework consists of seven stages, each delineating a different facet of a cyberattack. The stages are:
- Reconnaissance
- Weaponization
- Delivery
- Exploitation
- Installation
- Command and Control
- Actions on Objectives
1. Reconnaissance
In the reconnaissance phase of the cyber security kill chain, threat actors identify a target that aligns with their motives, focusing on financial or strategic gains. Cybercriminals might attack financial entities and small enterprises for profit, while state actors pursue strategically important organizations. The decision on whom to target often leverages compromised credentials and is discussed in secure forums among attackers. Threat intelligence becomes a critical asset here, enabling organizations to fortify their perimeter security in anticipation of potential cyber attacks.
2. Weaponization
During this initial stage of the cyber kill chain process, attackers gather crucial information about the target network, predominantly in secret. This step is less about immediate threat detection and more about understanding the tactics and techniques of potential attackers, which is essential for developing a robust security strategy.
3. Delivery
After completing their reconnaissance, attackers select their preferred attack vector, typically behind the scenes, which makes early detection difficult. The intelligence gathered here isn't just for preventing security breaches but for informing a security system that defends against known threats by understanding adversary behaviors, such as the use of malicious code or other systems exploitation.
4. Exploitation
In this phase, attackers implement their attack to penetrate the network, often using phishing as a method to leverage compromised credentials or install malicious code. At this point in the cyber kill chain, threat intelligence proves most valuable, updating security systems with malicious signatures and enabling defenders to adjust their security strategies effectively.
5. Installation
Once inside, the attack progresses towards achieving its primary goal, which might include privilege escalation within the target network. The security system's strength is pivotal in detecting and mitigating these moves. Effective use of threat intelligence is crucial in this stage for identifying real threats and aiding in the rapid containment of security breaches.
6. Command and Control (C2)
During the command and control phase, malware communicates with external servers to receive further instructions, a core component of the cyber kill chain process. Here, threat intelligence is critical in identifying and blocking these communications to disrupt the control attackers have over their deployed malicious code.
7. Actions on Objectives
Finally, the attackers execute their primary mission, from data theft to system disruption. At this advanced stage of the cyber kill chain, the use of security certificates and other authentication measures can help detect anomalous behavior, aiding in the containment and mitigation of the attack. Threat intelligence plays a crucial role in alerting organizations to the presence of their data on dark web markets, facilitating quick action to mitigate the impacts of the attack.
Identifying and Mitigating Attack Vulnerabilities
While deciphering the attacker’s playbook is vital, it’s equally imperative to understand how to fortify your defenses. Organizations can strengthen their defenses against external attacks and safeguard sensitive data from insider threats by implementing various security measures. These measures include the use of strong, unique passwords and enabling multi-factor authentication to significantly reduce the risk of breaches during cyberattacks.
Some best practices for protecting against malware attacks include:
- Keeping systems updated and patched to close security vulnerabilities quickly
- Regularly backing up data and testing restore processes to prevent data loss
- Using Unified Threat Management (UTM) systems to consolidate multiple security functions into a single system
Hardening the Target Network Against External Attacks
In the context of internal or external attack, the primary strategy revolves around fortification. Organizations protect against these attacks by employing technologies such as firewalls, intrusion detection systems, and adopting a defense in-depth strategy with multiple security layers. Adopting HTTPS for secure internet communications is a critical measure for protecting against external cyber threats.
Technical controls are important for cyber defense, restricting user access to essential data and applications to protect against external security risks. Some examples of technical controls include:
- Firewalls
- Intrusion detection systems
- Encryption
- Access control lists
Threat intelligence training is also vital in fortifying a target’s network security, as awareness programs help users identify phishing attempts and other malicious activities to prevent external attacks.
How Important is the Cyber Kill Chain in Cybersecurity?
In the strategic game of cybersecurity, maintaining a robust offense often constitutes the best defense. Security systems play a crucial role in disrupting the Cyber Kill Chain by applying security controls such as:
- detection
- denial
- disruption
- degradation
- deception
The zero-trust security framework secures users, devices, APIs, IoT, and more by requiring verification of trustworthiness before granting access, which helps prevent lateral movement and unauthorized access.
A layered security approach protects against malware with tools such as next-generation endpoint monitoring, firewalls, and intrusion prevention systems, covering security from the endpoint to the DNS attack surface layer.
Network segmentation reduces the risk of widespread exposure during an attack by isolating different parts of the network. Security analytics and real-time threat intelligence enable close monitoring of network traffic for better visibility and understanding of security incidents.
Advanced Malware Prevention Techniques
Advanced prevention techniques serve as the essential shields for your kingdom in the fight against malware. Organizations can prevent malware during the delivery phase by implementing:
- Endpoint malware protection
- Application allowlisting
- Proxy filters
- Host-based intrusion prevention systems
Regular updates to antivirus software, along with caution towards suspicious links and downloads, are essential to cyber security defense efforts against malware. These techniques form the first line of defense against malicious code, ensuring that your systems are fortified against potential attacks.
Deception Measures and Lateral Movement Detection
Deception transcends being merely a defensive strategy and becomes an offensive weapon. Deception measures are employed in cyber defense to disrupt attacker communications, degrade attack effectiveness, and mislead attackers with false information or decoys.
Honeypots (a type of deception technology) on the other side, attract attackers by presenting false information or setting up decoy assets, aiding in the detection of unauthorized movements within a network.
Detecting lateral movements within the network is crucial for identifying attackers who may have bypassed initial defenses and are attempting to move within the network. By creating a maze of deception, organizations can misdirect attackers, wasting their time and resources while revealing their tactics.
Beyond the Kill Chain
While the Cyber Kill Chain framework is indeed a potent instrument, it’s not the sole tool at our disposal. Evolving defense strategies include unified approaches to cybersecurity and leveraging AI and machine learning for real-time threat detection and response.
The traditional Cyber Kill Chain model, with its focus on malware detection, prevention, and perimeter security, has evolved to improve its recognition and anticipation of diverse and sophisticated threats such as insider threats, social engineering, and advanced ransomware.
The unified kill chain model has emerged as an alternative framework that synthesizes methodologies from both the Cyber Kill Chain and MITRE ATT&CK Framework, offering a more detailed and integrated approach with 18 distinct stages. This evolution shows that while the Cyber Kill Chain remains a vital tool, it is part of a broader, more comprehensive cyber defense strategy.
Unified Approaches to Cybersecurity
Truth is, there isn’t a single framework that possesses all the answers. Integrating concepts from both the Lockheed Martin Cyber Kill Chain and MITRE ATT&CK frameworks can result in a more comprehensive cybersecurity defense strategy.
While the Cyber Kill Chain framework outlines a chronological sequence of an attack, the MITRE ATT&CK framework provides a detailed library of attacker actions and motivations, which is not constrained by sequence.
Threat intelligence frameworks such as MITRE ATT&CK, when combined with the Cyber Kill Chain, enable a robust strategy for identifying and addressing tactics, techniques, and procedures used by adversaries. The use of MITRE ATT&CK alongside the Cyber Kill Chain can enhance cyber threat intelligence and, when coupled with AI and machine learning, can improve threat detection and response.
Integrating AI and Machine Learning
The advent of AI and machine learning has revolutionized the field of cybersecurity. They allow for:
- Real-time detection and response to threats
- Proactive identification of risks
- Reinforcement machine learning in cybersecurity uses trial and error to enable algorithms to identify and respond to attacks in real-time.
Machine learning can automate repetitive security tasks, thereby increasing efficiency and effectiveness in identifying threats compared to humans. Some ways machine learning is used in security include:
- User and entity behavior analytics (UEBA) incorporate machine learning to establish normal behavior baselines and detect unusual activities.
- Supervised machine learning predicts or classifies specific security threats by training on both benign and malicious data samples.
- Unsupervised machine learning sifts through unlabeled datasets to uncover hidden patterns without prior human guidance.
These applications of machine learning in security help improve threat detection and response.
Real-life Use cases for the Cyber Kill Chain Model
A comprehensive study conducted by Glorin Sebastian from the Georgia Institute of Technology, utilizing the Lockheed Martin Cyber Kill Chain model, revealed critical insights into several high-profile data breaches.
This research meticulously traced the stages of these breaches, from reconnaissance to the final actions on objectives, offering a detailed understanding of how each attack unfolded and the key vulnerabilities exploited. The analysis covered the following breaches:
- Equifax Breach (May 13 - July 30, 2017): This breach, caused by delayed patching of a known vulnerability in Apache Struts, led to the compromise of personal data of millions.
- Target Breach (November 2013): A supply chain attack that began with a phishing email to a vendor, leading to the theft of credit card information from over 110 million customers.
- Yahoo Breach (Late 2014): Stemming from a spear-phishing attack on an employee, this breach compromised at least 500 million user accounts, making it one of the largest breaches in history._
- Sands Casino Attack (February 2014): A politically motivated attack by nation-state actors, exploiting a vulnerability in a test version of the casino’s website.
- Atlanta & Not Petya Case (March 22, 2018): This ransomware attack, using the SamSam virus, significantly disrupted the city of Atlanta's IT infrastructure.
Glorin Sebastian's research uses these breaches to demonstrate the practical application of the Cyber Kill Chain model in cybersecurity. Each case highlights different aspects of cyber threats and the importance of comprehensive security strategies across various stages of an attack.
Frequently Asked Questions
What is the difference between Mitre framework and Cyber Kill Chain?
The Cyber Kill Chain claims that all cyberattacks must follow a specific sequence, while MITRE ATT&CK makes no such claim. The Cyber Kill Chain offers a simplified overview of the attack lifecycle, whereas the MITRE ATT&CK framework provides a more detailed understanding of attacker TTPs.
How has the Cyber Kill Chain model evolved to address modern threats?
The Cyber Kill Chain model has evolved to address modern threats by adapting to insider attacks, advanced ransomware, and the emergence of novel attack techniques.
Is the Cyber Kill Chain still useful?
Yes, the Cyber Kill Chain is still useful. It remains a valuable framework for identifying and defending against cyber threats, especially as the complexity and frequency of these threats continue to grow. By breaking down the stages of a cyber attack, it helps organizations understand and improve their defensive strategies systematically.
Wrapping up
From understanding its genesis to exploring its real-world applications, the Cyber Kill Chain framework emerges as a vital tool in the cybersecurity arsenal. It provides a structured approach to understanding and mitigating cyber threats, offering insights into the anatomy of a cyberattack.
However, as the cyber landscape continues to evolve, so too must our defense strategies. By integrating the Cyber Kill Chain with other models like MITRE ATT&CK, leveraging AI and machine learning, and maintaining flexibility and adaptability, organizations can stay one step ahead in the ever-evolving world of cybersecurity.
To see how you can effectively implement these strategies using cutting-edge threat intelligence, book a demo with Recorded Future today.

Esteban is a seasoned security researcher and IT professional with over 20 years of experience, specializing in hardening systems and networks, leading blue team operations, and conducting thorough attack surface analysis to bolster cybersecurity defenses. He's also a skilled marketing expert, specializing in content strategy, technical SEO, and conversion rate optimization. His career includes roles as Security Researcher and Head of Marketing at SecurityTrails, before joining the team at Recorded Future.
Related