How to Make the Attack Lifecycle Actionable with Intelligence
The Cyber Attack Lifecycle and Cyber Kill Chain are time and again used as the primary reference for understanding how a cyber attack happens from the perspective of an adversary. However, just leveraging them as educational reference documents doesn’t tap into their true power—guides to enabling defensive and proactive action against attackers.
When getting into cybersecurity one of the very first things to learn is the concepts and steps associated with the lifecycle of a cyber attack. Today there are probably a million youtube videos and thousands of blogs on every step and what it all means but they usually all actually point back to a couple resources created long ago. While some of the new lifecycles on the block may be compelling, if you were to ask an analyst today where to get started in understanding a cyber attack they will likely point you towards one of two places, the Cyber Kill Chain and the Cyber Attack Lifecycle.
 Cyber Attack Kill Chain
Cyber Attack Kill Chain
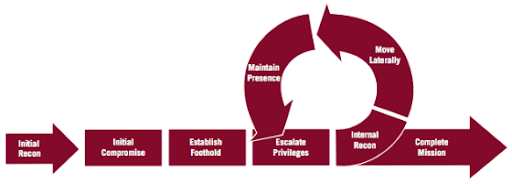 Cyber Attack Lifecycle
Cyber Attack Lifecycle
I’m sure there’s room for a lengthy debate around which model is better at depicting how attackers operate, but at the end of the day, both do a good job showing how cyber attacks are carried out. While these phases are important to learn and memorize, a security analyst needs to be able to monitor, detect, and investigate what the attacker is doing throughout the phases when it comes to their own networks. It's one thing to learn the phases and understand how the adversary navigates all the way to “mission complete” or “actions on objectives,” but it’s another thing to use elements of the various phases of these models to understand collection and analysis gaps—or how to hunt for indicators of attacker activity in your network.
This is where threat intelligence comes in. The kill chain and attack lifecycle models are more than just learning or reference tools. They provide security analysts a source of truth that can be used to guide collection, proactive hunting for indicators, monitoring and alerting on potentially malicious activity in the early phases.
When talking about threat intelligence, I’m not just talking about free threat feeds or machine generated indicators which are often stale; I’m talking about intelligence that incorporates a full-scale human and machine approach so there is actionable coverage across every phase of the lifecycle.
Let’s take a deeper look at what the attacker is doing throughout these phases and how intelligence can help you detect, remediate, and report on the activity throughout the entire lifecycle. Disclaimer for all of the kill chain lovers out there: I’m sorry, but I’m going to use the cyber attack lifecycle to explain this concept but rest assured, the same applies to the kill chain as well.
In the attack lifecycle early phases:

What’s the attacker doing in these phases?
- Identifying, assessing, and selecting their target through OSINT research and analysis of low hanging fruit versus more impactful targets
- Identifying ways into the target network. Examining if methods like phishing, exploitable vulnerabilities, leveraging credentials, etc. could work
- Exploiting vulnerabilities or using credentials to gain access to target network
- Establishing a foothold or creating a method to maintain persistent access to the target network once inside
What does real-time and contextualized intelligence uncover in these phases?
- Vulnerability data including pre-NVD, Proof of Concept (PoC) code, and active exploits in the wild
- Dark web mentions and stolen credentials
- Third party data to understand vendor infrastructure risk
- New domain and certificate registrations
What can analysts be doing to identify activity in these phases?
- Setting up tailored, useful alerts that don’t just produce noise but enable action
- Proactively monitoring threat actors and groups of interest
- Searching indicators of known malware, malicious tools, and high priority technical threats
- Monitoring for vulnerabilities in your tech stack
In the later phases of the attack lifecycle all the way to completion:
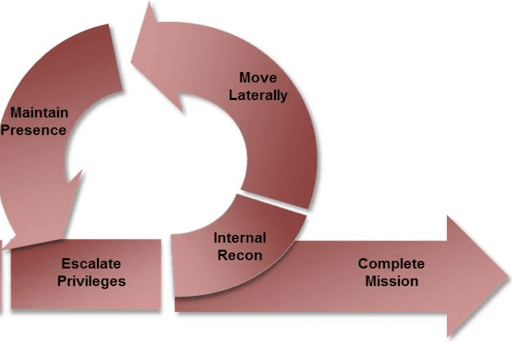
What’s the attacker doing in these phases?
- Escalating their privileges through various means like kerberoasting or passing the hash
- Gathering and using additional credentials to perform lateral movement and privilege escalation to establish further access
- Dropping additional tools to facilitate additional access or capabilities
- Identifying, collecting, and exfiltrating data of interest
How can threat intelligence augment our defensive approach in these stages?
- Tailored detection rulesets such as YARA, Sigma, and Snort
- Network traffic analysis data to provide evidence of C2 traffic from malware and malicious tools, possible data exfiltration and more
- Known and suspected Command & Control (C2) server feeds
- Finished intelligence reporting on attacker TTPs and how to detect them
- Endpoint data
- Passive & active network scans
What can analysts be doing to identify activity in these phases?
- Leveraging finished intelligence such as human-generated threat hunting packages with detection rulesets to proactively hunt for indicators
- Conducting deep research on ongoing campaigns to identify new indicators and understand the severity of the threat
- Compiling internal intelligence reports to brief leadership and cross-functional teams
- Testing and validating security controls once detection rulesets are in place
So while understanding the attack lifecycle in depth is great as a baseline, it doesn’t give you much more than an education on how an attack happens. It becomes a much more valuable tool when you can use it to enable defensive and proactive action across all phases. But there are a lot of questions that come up like how do you get all those data sources? Where do you start when it comes to things you or your analysts could be doing for each phase? Once I have the intelligence how do I make sense of it?
The good news here is that, we can help…with all of it. While there are other cyber threat feeds and data providers out there, Recorded Future is able to collect, process, and disseminate real-time intelligence that sheds a light on all phases of the attack lifecycle. On top of the unmatched scope and quantity of machine generated intelligence, there is a dedicated team of intelligence experts within the Insikt Group writing detailed reports and enabling analysts to take action through their tailored hunting packages with included detection rulesets. To give you an idea, here’s some ways that Recorded Future’s intelligence can help you across the attack lifecycle phases:
Machine Generated Intelligence:
- Typosquat detection and alerting
- Identifying malicious and vulnerable applications
- Domain and certificate registration monitoring and alerting
- Monitoring the dark web for mentions of your brand and leaked credentials
- Recorded Future-validated technical links between indicators
- Identification of pre-NVD vulnerabilities, proof of concept code, and active exploits in the wild
- Third party monitoring for potentially vulnerable vendors, subsidiaries, and partners
Human Generated Intelligence & Guidance:
- In-depth finished intelligence reports highlighting adversary & TTP trends
- Human-generated validated links between entities in product
- Custom Priority Intelligence Requirement (PIR) and adversary prioritization workshops through dedicated intelligence consultants
- Tailored hunting packages with detection rulesets included
- On-demand analyst support for ad hoc report creation, requests for information, and scheduled reporting
If you want to learn more about this concept and how Recorded Future helps, be sure to register for a two part attack lifecycle webinar series. This will give you a better sense of the different phases of an attack lifecycle, and give you the opportunity to learn from intelligence analysts about real-world examples of methods attackers use across the phases so you can identify and remediate attacks!
Related