Threat intelligence involves analyzing evidence-based information about cyber attacks, enabling cyber security experts to identify issues contextually and create targeted solutions for the detected problems.
Rooted in data, similar to open source intelligence (OSINT), threat intelligence provides context — like who is attacking you, what their motivation and capabilities are, and what indicators of compromise (IOCs) in your systems to look for — that helps you make informed decisions about your security.
As digital transformation reshapes industries, the importance of cybersecurity grows exponentially. A Statista study predicts that by 2033, the Cyber Threat Intelligence (CTI) market will surge beyond 44 billion U.S. dollars, underscoring the critical role of informed, data-driven defenses in modern business strategies. This corresponds with the results from our recent survey in the Recorded Future 2023 State of Threat Intelligence report, showing that 70.9% of participants have a dedicated team focused on collecting and analyzing threat intelligence.
This article offers an in-depth understanding of how effective threat intelligence can detect, analyze, and mitigate cyber risks, ensuring a proactive security approach. You will learn about its components, significance, and how to implement it within your organization to prevent intrusions and attacks.
For a more detailed overview of all things Threat Intelligence, download the comprehensive Intelligence Handbook or keep reading below.
Key Takeaways
- Threat intelligence is critical for cybersecurity, providing evidence-based knowledge that help organizations proactively strengthen their defenses by understanding and mitigating emerging cyber threats through various forms like tactical, technical, operational and strategic intelligence.
- Threat Intelligence Platforms (TIPs) are essential tools that integrate external threat feeds with internal data, enhancing threat identification and response, while artificial intelligence and machine learning are increasingly utilized for automated data collection and analysis to improve threat intelligence efficiency.
- Practical applications of threat intelligence include incident response and triage, security operations, threat hunting, and vulnerability management, which are essential for swift response and management of cyber threats, aiding organizations in maintaining business continuity and data protection.
What is Threat Intelligence?
Threat intelligence involves gathering, processing, and analyzing data to discern the motives, behaviors, and targets of threat actors, providing actionable insights to prevent and combat cyber crime.
 It's an evolving discipline that provides organizations with evidence-based insights about potential cyber threats, including emerging cyber threats, equipping them with the knowledge they need to proactively strengthen their defenses and make informed security decisions.
It's an evolving discipline that provides organizations with evidence-based insights about potential cyber threats, including emerging cyber threats, equipping them with the knowledge they need to proactively strengthen their defenses and make informed security decisions.
According to Gartner, threat intelligence delivers evidence-based insights, including context and actionable advice, on existing or emerging threats to inform response strategies.
But what exactly does threat intelligence entail, and what are its key components?
Definition and Purpose
Threat intelligence is about:
- Identifying and analyzing cyber threats to enable a proactive and informed defense
- Going beyond mere aggregation of threat data
- Offering a comprehensive view that integrates evidence and context
- Guiding organizational cybersecurity strategies
Interpreting threat intelligence enables organizations to comprehend the risks they face and enact proactive measures to mitigate potential damage.
Key Components
Effective threat intelligence hinges on comprehensive information. It requires a blend of diverse data types:
- Collected from a variety of sources
- Contextualized
- To provide actionable insights
This includes raw data from internal systems, security controls, and cloud services, all of which lay the groundwork for a solid cyber threat intelligence program.
The goal is to provide both evidence that a threat is valid and actionable insights that suggest efficient mitigation methods.
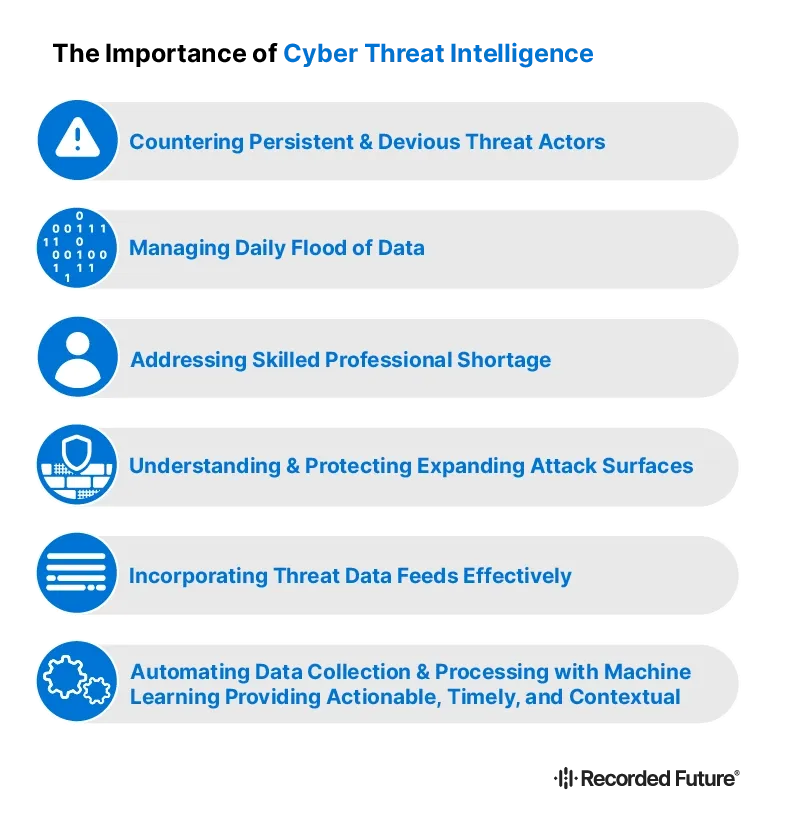
The Importance of Cyber Threat Intelligence
Threat intel plays a pivotal role in cybersecurity, making threat intel important for understanding potential cyber threats, including the cyber threat that could specifically target and impact businesses. Investing in a robust cyber threat intelligence program allows organizations to lessen the risk of cyber attacks and strengthen their security stance.
 But how does threat intelligence address cybersecurity challenges, and how does it enhance an organization's security posture?
But how does threat intelligence address cybersecurity challenges, and how does it enhance an organization's security posture?
Addressing Cybersecurity Challenges
In the world of cybersecurity, challenges abound. There's the sheer volume of data to contend with, the rapid evolution of attack vectors, and the scarcity of skilled cybersecurity personnel. However, threat intelligence provides a solution. Integrating, prioritizing, and authenticating data from various sources help threat intelligence to alleviate data overload.
Machine learning aids in handling large volumes of data, reducing the need for specialized personnel. Moreover, threat intelligence platforms (TIPs) help manage evolving attack vectors by:
- Processing external threat feeds and internal log files
- Creating prioritized and contextual alerts
- Helping organizations adapt to new and sophisticated cyber attack methods.
Enhancing Security Posture
A threat intelligence program doesn't just address challenges doesn't just address challenges; it also enhances an organization's security posture. Incorporating threat intelligence into organizational strategies empowers businesses to actively defend against cyber attacks and make informed decisions that helps security professionals manage risk more effectively.
Cyber threat Intelligence Platforms (TIPs) feed consolidated threat intelligence to security tools like next-generation firewalls and IDS/IPS, enhancing their ability to detect and block malicious threat actor activity.
Moreover, by continuously monitoring threat data, organizations can compare their security measures against industry benchmarks, recognizing areas of strength and opportunities for security enhancement.
Different Types of Threat Intelligence
Cyber threat intelligence comes in various forms, each serving distinct purposes and catering to different decision-making levels within an organization.
These forms include:
- Strategic threat intelligence
- Tactical threat intelligence
- Technical threat intelligence
- Operational threat intelligence
But what do these forms entail, and how do they contribute to an organization's cybersecurity?
Operational Threat Intelligence
Operational threat intelligence focuses on understanding specific threats and campaigns. It provides real-time insights and actionable recommendations for dealing and understanding security vulnerabilities and attack techniques. Studying past attacks and drawing conclusions about threat actors' tactics, techniques, and procedures (TTPs), facilitates operational intelligence in helping organizations understand the ‘who', ‘why', and ‘how' of each cyber attack.
Strategic Threat Intelligence
Strategic threat intelligence offers a comprehensive understanding of the threat landscape, complementing other types of threat intelligence, including strategic intelligence. This holistic approach helps organizations make informed decisions to protect against potential threats. It offers:
- Long-term trend analysis
- Identification of significant risks that could result in future attacks against organizations
- High-level overview of cybersecurity threats, including geopolitical factors and industry trends
This intelligence gives organizations a comprehensive view of the threat landscape and helps them stay ahead of potential threats.
It's designed for non-technical stakeholders, such as company boards, who rely on its high-level decision-making guidance.
Technical Threat Intelligence
Technical threat intelligence is all about the details. It zeros in on threat indicators of compromise and specific technical details such as malware signatures and IP addresses. The goal is to provide detailed information on vulnerabilities and malware, focusing on behavior, delivery mechanisms, and the potential impacts on systems.
Tactical Threat Intelligence
Tactical threat intelligence, lastly, centers on outlining the tactics, techniques, and procedures (TTPs) employed by threat actors. It provides vital insights into their methods and strategies. By offering actionable threat intelligence, tactical intelligence plays a crucial role in providing insights into the immediate threat landscape, enabling adaptation to changing attacker behaviors and threats. Cyber threat intelligence services contribute significantly to the effectiveness of tactical intelligence.
Modeling potential attacks using industry-wide threat information aids organizations in better preparing for specific threats.
The Role of the Threat Intelligence Lifecycle
Understanding the various forms of threat intelligence is one thing, but navigating the threat intelligence lifecycle is another. This lifecycle comprises six stages: Direction, Collection, Processing, Analysis, Dissemination, and Feedback. Each stage plays a crucial role in ensuring continuous improvement and refinement of the intelligence process. But what does each stage involve, and why is each one critical?
Requirements and Objectives
The ‘Direction' phase is where it all begins. Here, the goals for the cyber threat intelligence program are established, with key stakeholder input. Intelligence requirements are set to answer cybersecurity questions relevant to the organization. Stakeholder feedback is crucial for understanding the intelligence priorities of the security teams utilizing the cyber threat intelligence, which in turn guides the documentation of these intelligence requirements.
Data Collection Methods
Once the direction is set, the focus turns to data collection. This involves gathering information from various internal and external sources, including security logs, threat feeds, and expert interviews. The goal is to collect as much relevant data as possible to inform the next stages of the threat intelligence lifecycle.
Processing and Organization
After data collection comes processing. This stage transforms the collected data into a usable format. It involves filtering out irrelevant data and structuring the remaining information for efficient analysis. With the help of artificial intelligence and machine learning, trends can be identified, providing valuable insights for the next stage.
Analyzing and Interpreting Data
The threat intelligence analysis phase involves:
- Converting the processed information into actionable intelligence
- Adversary profiling
- Threat correlation
- Behavioral analysis
These are critical elements in this phase.
These elements are integral to understanding the nature and potential impact of threats.
Dissemination and Reporting
Once the analysis is complete, the dissemination phase ensures that the key recommendations and conclusions are received by the relevant stakeholders. The format of dissemination can vary, ranging from formal threat intelligence reports to video feeds or presentations, depending on the audience's needs.
Feedback and Iteration
Finally, feedback is a critical component of the cyber threat intelligence lifecycle. It ensures that the intelligence provided meets the evolving needs and priorities of the organization. Any new questions or intelligence gaps identified in the feedback phase can be addressed in the next cycle, ensuring continuous improvement and refinement.
Machine Learning for Better Threat Intelligence
Data processing on today's large scale necessitates automation to effectively combine data from diverse sources like the open web, deep web, dark web, and technical channels, creating a comprehensive overview.
Recorded Future uses machine learning techniques in four ways to improve threat data collection and aggregation — to structure data into categories, to analyze text across multiple languages, to provide risk scores, and to generate predictive models.
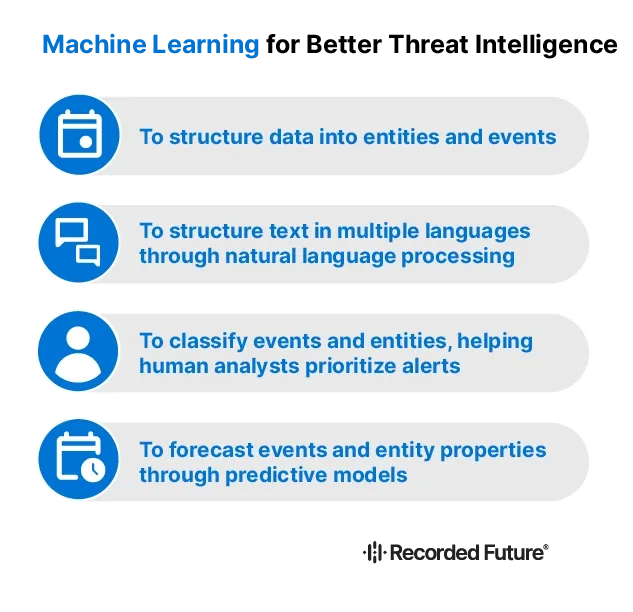
- To structure data into entities and events: Machine learning categorizes data using ontology, making it easier to manage by defining entities and their relationships. This helps in recognizing events across languages without manual sorting, leveraging ontologies to understand categories and hierarchies.
- To structure text in multiple languages through natural language processing: It translates unstructured text from different languages into structured data, enhancing clarity and accessibility. By distinguishing between similar entities (e.g., "Apple" the tech company vs. the fruit), it streamlines data analysis and improves accuracy.
- To classify events and entities, helping human analysts prioritize alerts: Machine learning assigns risk scores to identify and prioritize threats, combining human expertise with AI precision. This classification reduces the time analysts spend on false positives, allowing for more efficient threat assessment. Automating how risks are classified saves analysts time sorting through false positives and deciding what to prioritize, helping IT security staff who use Recorded Future spend 34 percent less time compiling reports.
- To forecast events and entity properties through predictive models: predictive modeling uses historical data to anticipate future threats, making threat detection more proactive. As more data is gathered, these models become increasingly accurate, offering a powerful tool for anticipating and mitigating potential risks.
Implementing Threat Intelligence Tools and Services
Threat intelligence platforms, threat data feeds, and artificial intelligence all play crucial roles in enhancing cyber threat intelligence capabilities and streamlining processes. But what are these threat intelligence tools and services, and how do they contribute to the threat intelligence process?
Threat Intelligence Platforms
Threat intelligence platforms (TIPs) integrate external threat feeds with internal data, providing features such as rapid assessments, prioritized risk assessments, and smart threat data analysis and visualization. A cyber threat intelligence platform provides granular visibility into threats that are relevant both in the broader marketplace and specific to the organization's industry, which is critical for effective team response and adapting to new challenges.
Threat Data Feeds
Threat data feeds deliver current information such as threat actor ttps, vulnerabilities, and new attacks. They comprise a diverse set of information such as:
- malicious IP addresses
- domains
- file hashes
- malware signatures
- security trend data
These feeds streamline the decision-making process and enable quicker deployment of countermeasures.
Artificial Intelligence and Machine Learning
Artificial intelligence and machine learning techniques are increasingly used in:
- Structuring data
- Analyzing text
- Providing risk scores
- Generating predictive models for improved threat intelligence
They support automated data collection and analysis, reducing time and costs associated with operational threat intelligence.
Practical Use Cases for Threat Intelligence
Threat intelligence isn't just theoretical; it's a vital component of a threat intelligence program with practical applications across various security domains. From security incidents response and triage to security operations and threat hunting, it provides essential insights that help organizations swiftly manage and respond to cyber threats. Let's now review the top use cases for threat intelligence.
Incident Response and Triage
In incident response and triage, threat intelligence plays a pivotal role. It allows for the measurement of key performance metrics such as Mean Time To Detect (MTTD) and Mean Time To Respond (MTTR), aiding in the evaluation of incident response effectiveness.
Integrating threat intelligence into incident response allows organizations to significantly reduce response time, thereby maintaining business continuity and data protection.
Security Operations and Threat Hunting
Within security operations, threat intelligence plays a critical role in the proactive identification and mitigation of sophisticated cyber threats (such as advanced persistent threats). AI technologies and behavioral analytics enhance the ability to find threats by developing profiles for network applications and analyzing user and device data.
Vulnerability Management and Risk Analysis
In vulnerability management, an effective threat intelligence program that includes operational intelligence is vital. It identifies critical vulnerabilities being actively exploited, enabling organizations to prioritize patching and preemptively address potential software vulnerabilities.
Fraud Prevention
To keep your organization safe, it's crucial to prevent fraudulent uses of your data or brand. Integrating threat intelligence from both underground and surface sources offers deep insights into the tactics and motivations of threat actors. You also need to of your data or brand.
Security Leadership
Security leaders must balance limited resources with the need to protect against evolving threats. Threat intelligence helps map the threat landscape, assess risk, and provides the necessary context for making informed, timely decisions, something all security professionals need at the end of the day.
Reducing Third-Party Risk
As organizations digitize and expand data collection, traditional risk management methods fall short, lacking the necessary context for modern security challenges. Threat intelligence provides real-time insights into third-party threat environments, enhancing risk assessment and management.
Frequently Asked Questions
What are the 3 Ps of threat intelligence?
The three Ps of threat intelligence are proactive, predictive, and preventive. These approaches are key in enhancing security professionals' threat intelligence capabilities by actively seeking out and identifying potential threats before they materialize.
What does a threat intelligence team do?
A threat intelligence team analyzes data about attackers, their capabilities, and motives, to prevent cyber attacks (like security breaches, data theft, and more). It is an essential aspect of information security.
Wrapping up
Threat intelligence is crucial for robust cybersecurity, equipping organizations with the knowledge to anticipate and mitigate cyber threats, thus enhancing their security posture. By understanding different forms of threat intelligence, its lifecycle, and employing appropriate tools and services, organizations can proactively stay ahead of cyber threats.
To see firsthand how Recorded Future's threat intelligence services can transform your cybersecurity strategy, book a demo with us today.
This article was published on June 12, 2024.