Accurately Calculate Cyber Risk With the Threat Category Risk Framework

Risk is a fundamental concept in cybersecurity. Unfortunately, the most commonly used cybersecurity frameworks — the Diamond Model of Intrusion Analysis, MITRE ATT&CK framework, and the Lockheed Martin Cyber Kill Chain — aren’t based on risk. They’re designed to help you identify and remediate threats.
However, there is a tool that any organization can use to accurately calculate the risk associated with different threat vectors — and even assign a dollar value to them.
The Threat Category Risk Framework
The threat category risk (TCR) framework — which builds on work by Douglas Hubbard and Richard Seiersen — is a practical, quantitative cyber risk framework. It’s designed to help security teams identify the likelihood and scale of annual financial loss posed by different cyber threats.
The TCR framework is an ideal tool to build a risk-based security program around. It starts with a set of general threat categories. For each category, a security team estimates:
- The likelihood that an event will occur within the next year
- The likelihood that the event will result in a data breach, loss of data availability, or both
- The extent of financial damage that could be caused by the event
- The potential number of hours that data could be made unavailable, and the cost per hour
Using a simple calculation, these estimates can help identify the most likely loss from an event and the range of possible losses from the threat category.
This makes the TCR an extremely valuable tool for calculating cyber risk. Not only does it present risk in monetary terms (making it easily understandable by any audience), it’s also quite easy for a well-rounded security team to use with a reasonable degree of accuracy.
The Value of Broad Threat Categories
To use the TCR framework, you’ll first need to identify which threat categories are relevant to your organization.
The table below shows a list of threat categories. For the sake of simplicity, the categories are divided into initial compromise methods and post-compromise methods — also known as “left of boom” and “right of boom,” in reference to military phrasing used to describe the moments before and after an explosion.
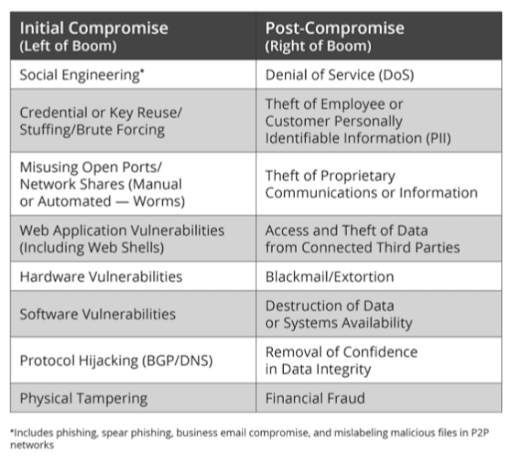
The TCR threat categories are generalized because there’s no need for great precision in estimating the impact and loss caused by a highly specific attack vector. While there might technically be a difference between two DoS attacks, the business risk and impact fall within the same range.
At the same time, there is no need to consider adversary-specific factors, because the risk scores take the form of monetary loss. It doesn’t matter who might conduct an attack — only how much that attack might cost the organization.
Finally, there is no need to analyze every possible threat. You should only concern yourself with threats that might directly cost the business financially.
Estimating Cyber Risk
For the TCR framework to have value for an organization, the process of making estimates for each threat category needs to be consistent and well-informed. To show how this process should work, we’ll use the example threat category “credential reuse.”
Credential reuse is among the most common uses of stolen credentials — attackers simply test credentials against as many websites and online accounts as possible. It’s a highly effective technique for penetrating networks and gaining access to data and resources.
To evaluate the risk posed by credential reuse, you can start by estimating the likelihood that your organization will be affected by a credential reuse attack within the next year. Ideally, this estimate should take the form of a risk range — for instance, the likelihood might fall between 80 – 100%.
Assuming a threat category is relevant to your organization, the next step is to estimate:
- How often it will affect data confidentiality/integrity
- How often it will affect data availability
- How often it will affect both
Again, each of these estimates should take the form of a high/low percentage probability range.
Next, you should estimate the potential financial impact of a credential reuse attack, once again in the form of a high/low range. For instance, you might estimate that the minimum impact within the next year could be $100,000, while the maximum could be $5 million.
Finally, if it is determined that a threat category could affect data availability, you should estimate the potential number of hours that data could be made unavailable for within the next year and the cost per hour of that lack of availability. To calculate these estimates, you’ll need a good understanding of credential reuse TTPs in current use by attackers, as well as any security controls you have in place to protect against them. The same goes for any other threat category for which you need to calculate risk scores.
Estimating Financial Loss With Monte Carlo Simulations
Monte Carlo simulations can be used to identify the range of potential impacts a threat category could have on your organization. When it comes to calculating risk, averages aren’t good enough. You need to know not just what the most likely outcome of a threat is, but also what the best and worst-case scenarios are. It’s no use being prepared for an average incident when you could very well be hit by a serious one.
Once all of the estimates described above have been made, a set of tens (or even hundreds) of thousands of Monte Carlo simulations can be run. Each simulation takes a random value from each of the categories estimated above and calculates the effect that scenario would have on the organization.
Once a complete set of simulations has been run, you’ll know the expected impact of each risk category and the worst-case scenario you need to prepare for.
By analyzing the spread of results, you’ll also be able to identify the likelihood of different severity scenarios. This is important, because while you may be happy to accept the risk associated with an average incident, the risk of a higher-end incident may actually be much worse.
For instance, one threat category might present a 40% chance of costing the organization $1.1 million in the next year, but a 10% chance of costing $5 million. While the risk in the first scenario might be deemed acceptable, the second may not be acceptable.
Calculating the Dollar Value of New Security Controls
So, what do you do if your calculations suggest unacceptable levels of risk?
Beyond estimating losses, the TCR framework also helps security professionals estimate the value of new security measures. By running the same simulations as above — but with a revised set of estimated ranges based on the implementation of new controls — you can generate a new set of potential losses.
If the amount saved by implementing a new control exceeds the cost of implementation, you may well have a valuable initiative on your hands. This information is extremely useful for justifying the need for a security expenditure, particularly if executive approval is required.
What You Need to Know About Risk-Based Cybersecurity
In “The Risk Business: What CISOs Need to Know About Risk-Based Cybersecurity,” a new book for cybersecurity leaders, Recorded Future’s Levi Gundert draws from his extensive career in cybersecurity risk management across the public and private sectors to share:
- A comprehensive case for risk-based cybersecurity, and how it contributes to business profitability
- How to accurately estimate risk in the real world (including the specifics of how to run Monte Carlo simulations)
- Why most cybersecurity frameworks aren’t based on risk, and what to do about it
- How strategic and operational threat intelligence can help your organization more accurately calculate and track cyber risk
- Why the true solution to reducing cyber risk lies in people (not technology), and how to make sure you hire and retain the best talent for your threat intelligence positions
Download your free copy of “The Risk Business” today.
Related