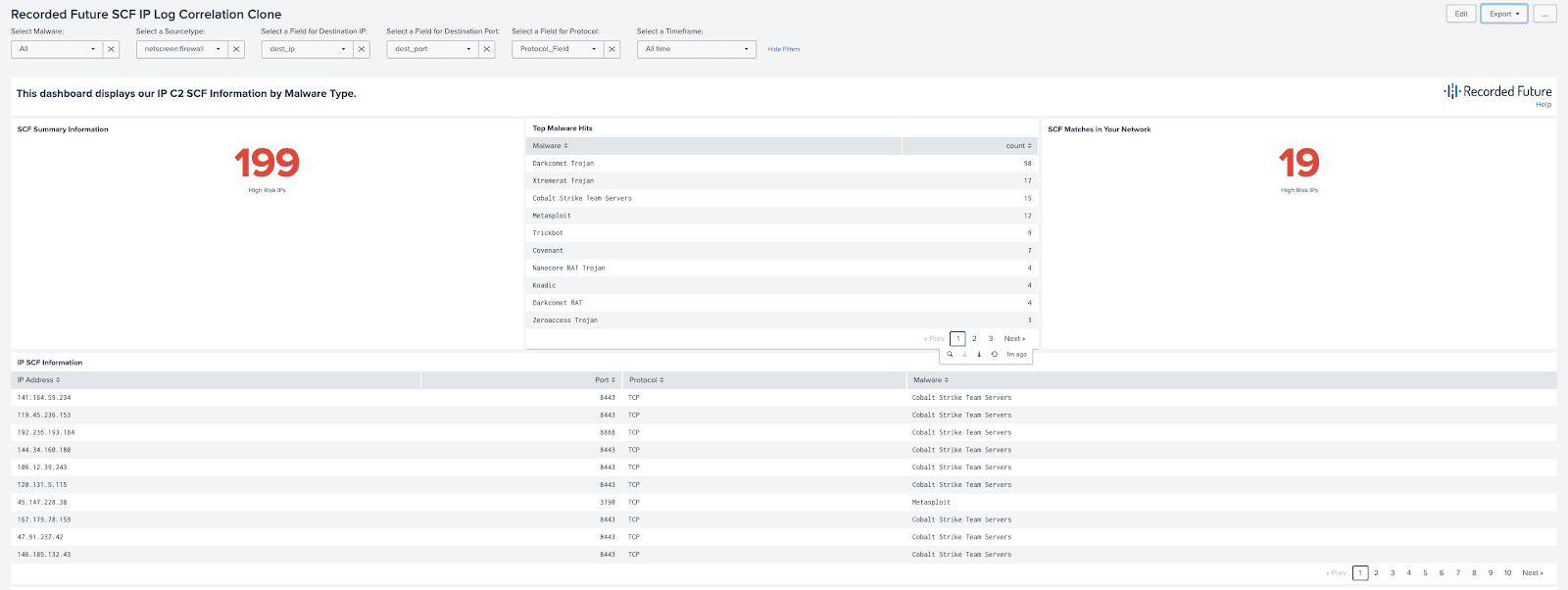
C2 Communicating IPs SCF Splunk Dashboard
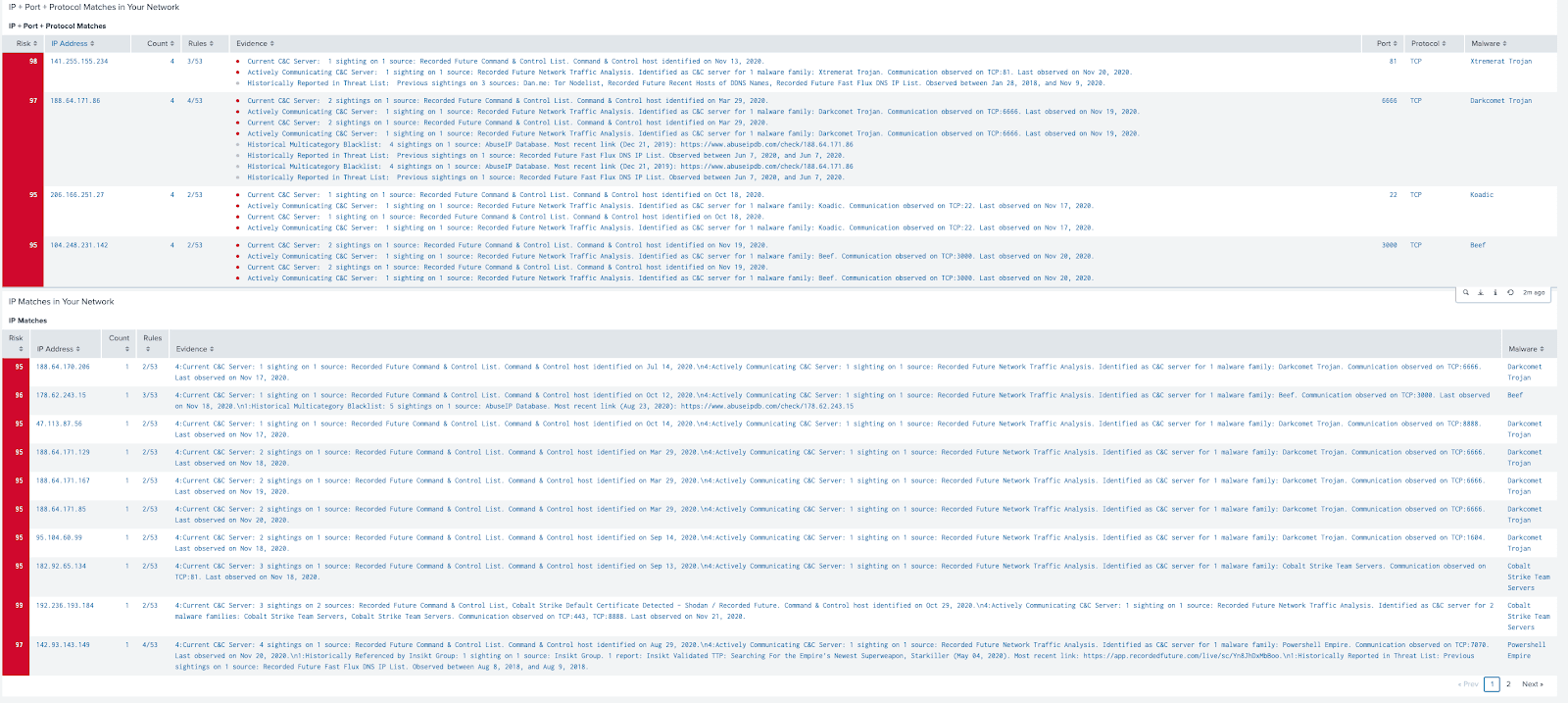
Recorded Future Internet Scanning collects live information about internet hosts and Network Traffic Analysis observes the midpoint between the adversary and their victims as they build, stage, and launch attacks. The Command and Control dataset fuses those two methods to identify and track IPs that we have scanned as positive C2 and then observed communications to understand how the C2 is interacting with infected machines as well as being controlled by the adversary. By leveraging this data in Splunk we can correlate, with high confidence, network activity in your logs with command and control infrastructure over specific ports and protocols, and tied to specific malware families.
This allows us to work towards two goals:
- Detecting communications with known C2 IPs over relevant ports and protocols.
- Hunting for activity potentially related to specific Malware.
This dashboard enables clients to detect higher confidence and fidelity correlations between their Network Traffic logs and Known C2 infrastructure by leveraging the metadata included in our C2 Communicating IPs SCF. It also marries this information with the Recorded Future Risk Score and Evidence Details to give the analyst further insight into the IP address. Finally, the user can filter results based on the malware variant if there is particular activity they are searching for.
From a technical perspective, the integration will include and need to be configured:
- C2 Communicating IPs SCF fusion file converted to risklist format with metadata added to the Recorded Future App for Splunk
- C2 SCF Correlation Dashboard XML code
This service will require Threat or Brand Intelligence Modules, Splunk Integration, and Two (2) Professional Service Credits for implementation. On-going support covered by Integration or Premium Support. If you have any additional questions, please contact your Intelligence Services Consultant.