RedDelta Targets European Government Organizations and Continues to Iterate Custom PlugX Variant

Editor’s Note: This is an excerpt of a full report. To read the entire analysis with endnotes, click here to download the report as a PDF.
This report details recent activity conducted by the likely Chinese state-sponsored threat activity group RedDelta. The activity was identified through a combination of large-scale automated network traffic analytics and expert analysis. This report will be of most interest to individuals and organizations with strategic and operational intelligence requirements relating to Chinese cyber threat activity, as well as network defenders in government organizations within Southeast Asia and Europe.
Executive Summary
Recorded Future’s Insikt Group continues to track activity we attribute to the likely Chinese state-sponsored threat activity group RedDelta targeting organizations within Europe and Southeast Asia using a customized variant of the PlugX backdoor. Since at least 2019, RedDelta has been consistently active within Southeast Asia, particularly in Myanmar and Vietnam, but has also routinely adapted its targeting in response to global geopolitical events. This is historically evident through the group’s targeting of the Vatican and other Catholic organizations in the lead-up to 2021 talks between Chinese Communist Party (CCP) and Vatican officials [1,2], as well as throughout 2022 through the group’s shift towards increased targeting of European government and diplomatic entities following Russia's invasion of Ukraine.
During the 3-month period from September through November 2022, RedDelta has regularly used an infection chain employing malicious shortcut (LNK) files, which trigger a dynamic-link library (DLL) search-order-hijacking execution chain to load consistently updated PlugX versions. Throughout this period, the group repeatedly employed decoy documents specific to government and migration policy within Europe. Of note, we identified a European government department focused on trade communicating with RedDelta command-and-control (C2) infrastructure in early August 2022. This activity commenced on the same day that a RedDelta PlugX sample using this C2 infrastructure and featuring an EU trade-themed decoy document surfaced on public malware repositories. We also identified additional probable victim entities within Myanmar and Vietnam regularly communicating with RedDelta C2 infrastructure.
RedDelta closely overlaps with public industry reporting under the aliases BRONZE PRESIDENT, Mustang Panda, TA416, Red Lich, and HoneyMyte.
Key Judgments
- RedDelta has consistently conducted long-term cyber-espionage campaigns in line with the strategic interests of the Chinese government, including historical targeting of government and public sector organizations across Asia and Europe as well as overseas organizations associated with minority groups within mainland China such as Tibetan and Catholic Church-related entities.
- Despite the volume of public reporting on the group’s activity, RedDelta employs a high operational tempo relative to other state-sponsored actors. The group also maintains a rapid pace of development for its flagship backdoor (remote access trojan [RAT]), a variant of the long-running backdoor PlugX that is heavily customized for anti-analysis for detection evasion.
- In November 2022, RedDelta actors shifted from using archive files to using malicious optical disc image (ISO) files containing a simplified shortcut (LNK) file for delivery of an updated PlugX payload.
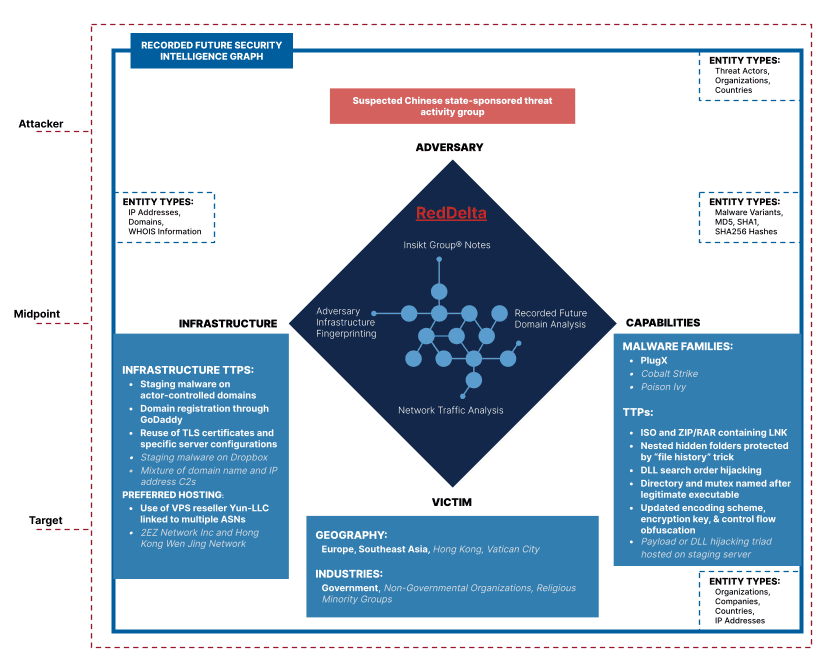
Figure 1: High-level RedDelta TTPs and Recorded Future data-sourcing graphic; historically reported TTPs are shown in gray [1,2] (Source: Recorded Future)_
Related