Exploring IP Ranges With Recorded Future: Are the APT1 Ranges Cleaned Up?

In this post we’re exploring new functionality in Recorded Future, which allows users to search the Recorded Future holdings for IP ranges. We’ll examine the IP ranges originally used by APT1 and identify continued potentially malicious activity, but unlikely very sophisticated.
Recorded Future’s holdings include a large amount of technical data, like filenames, hashes, and IP addresses. Recently we introduced the ability to search for a range of IP addresses; earlier you could only search by specific addresses. This allows analysts to, for example, rapidly identify activity involving their organization’s IP ranges or that of a particular actor.
In Mandiant’s APT1 report from February 2013 we can find the IP ranges used by APT1 as hop points – all owned by China Unicom, a major Chinese state-owned telecommunications operator.
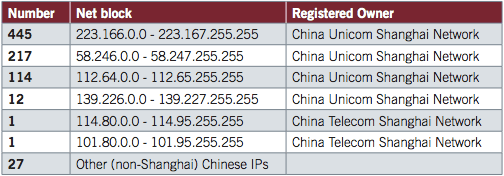
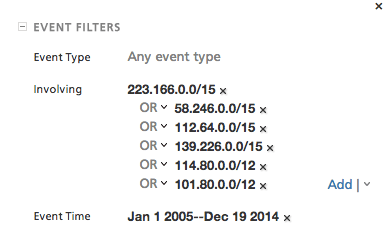
We can now easily search for these in Recorded Future, as in below. The IP ranges are written in CIDR notation (an address prefix of a specified bit length).
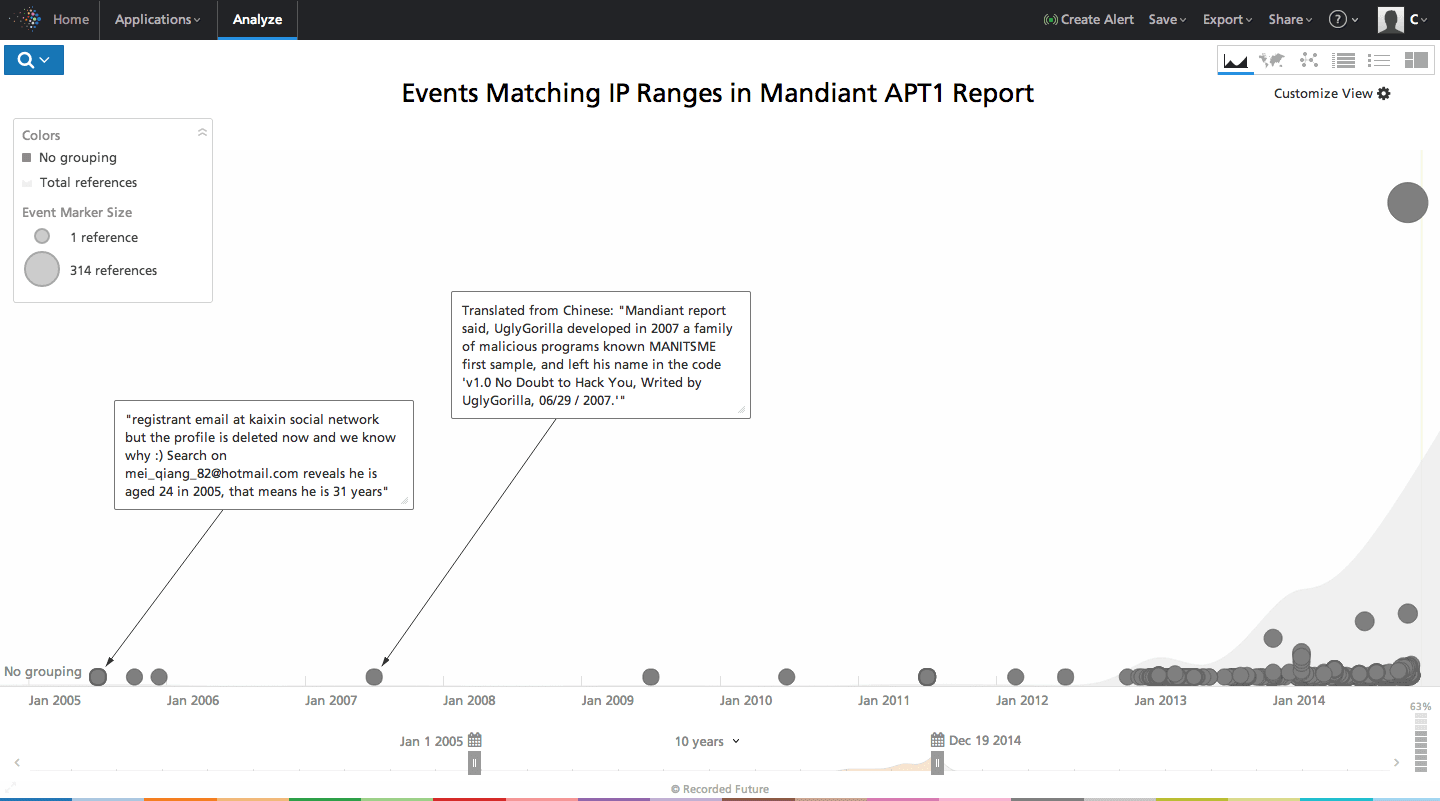
This yields us a timeline of events involving these IP ranges. We can see a clear uptick in activity post the report publication in early 2013 (of course) – and some historical data describing the activities of UglyGorilla and his friends setting up infrastructure,
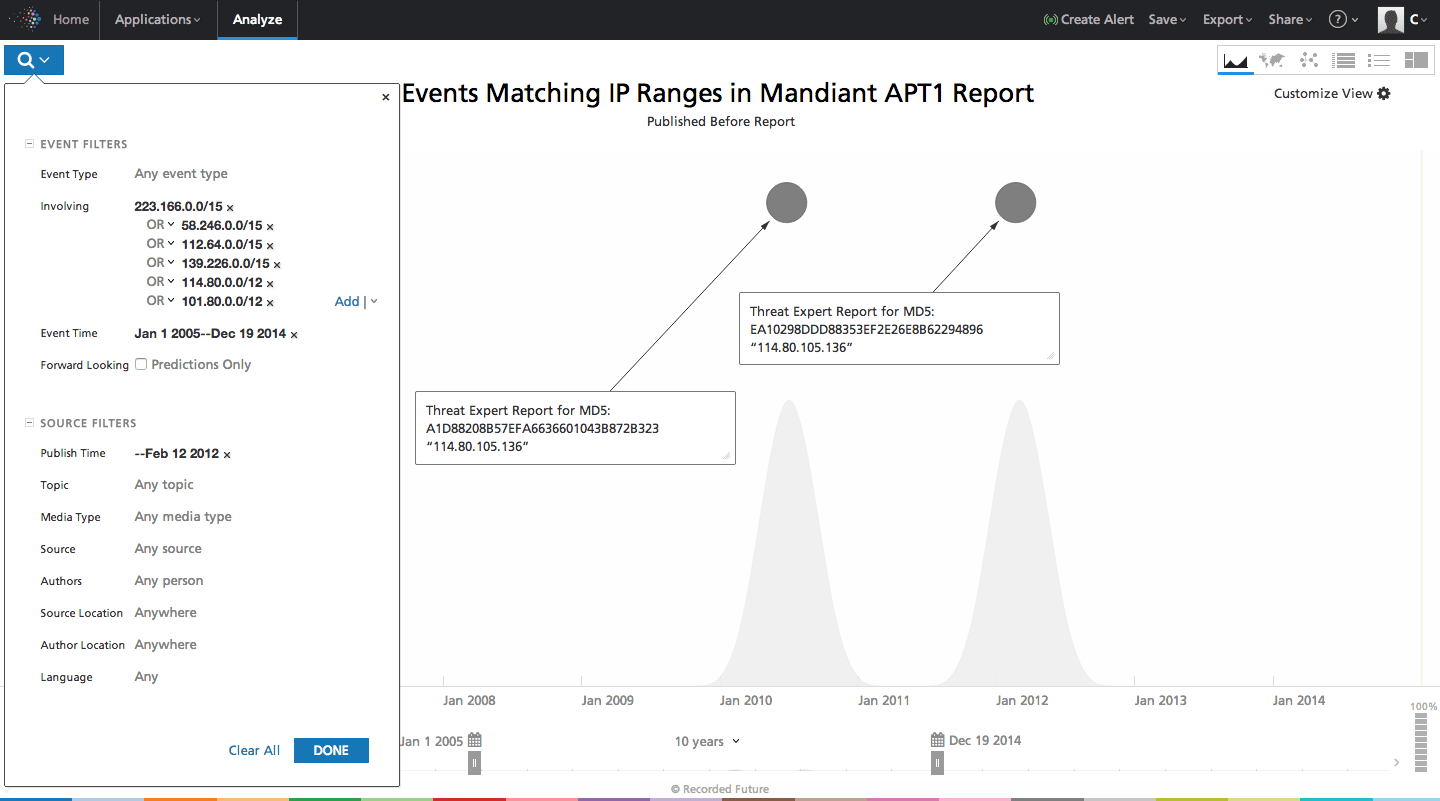
From here we can explore the same ranges in the Recorded Future holdings from the time before the Mandiant APT1 report by constraining publishing time to be before February 12, 2012. Time travel can be helpful! We identify two hits from Threat Expert, which Threat Expert at that time reported as having China as a possible country of origin.
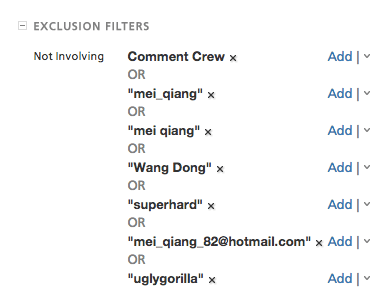
Now we can try to exclude any specific events that includes Comment Crew/APT1 and their close guys, per below. Obviously we could keep building the exclusion list as we dig in.
This yields us a timeline like the following where we’ve filtered out explicit references to APT1 actors (which of course doesn’t mean what’s left is not APT1). We still see a lot of activity coming out of reporting on these IP ranges – so let’s dive in and see what we can find. In the timeline below we can observe ongoing activity, up until this very day.
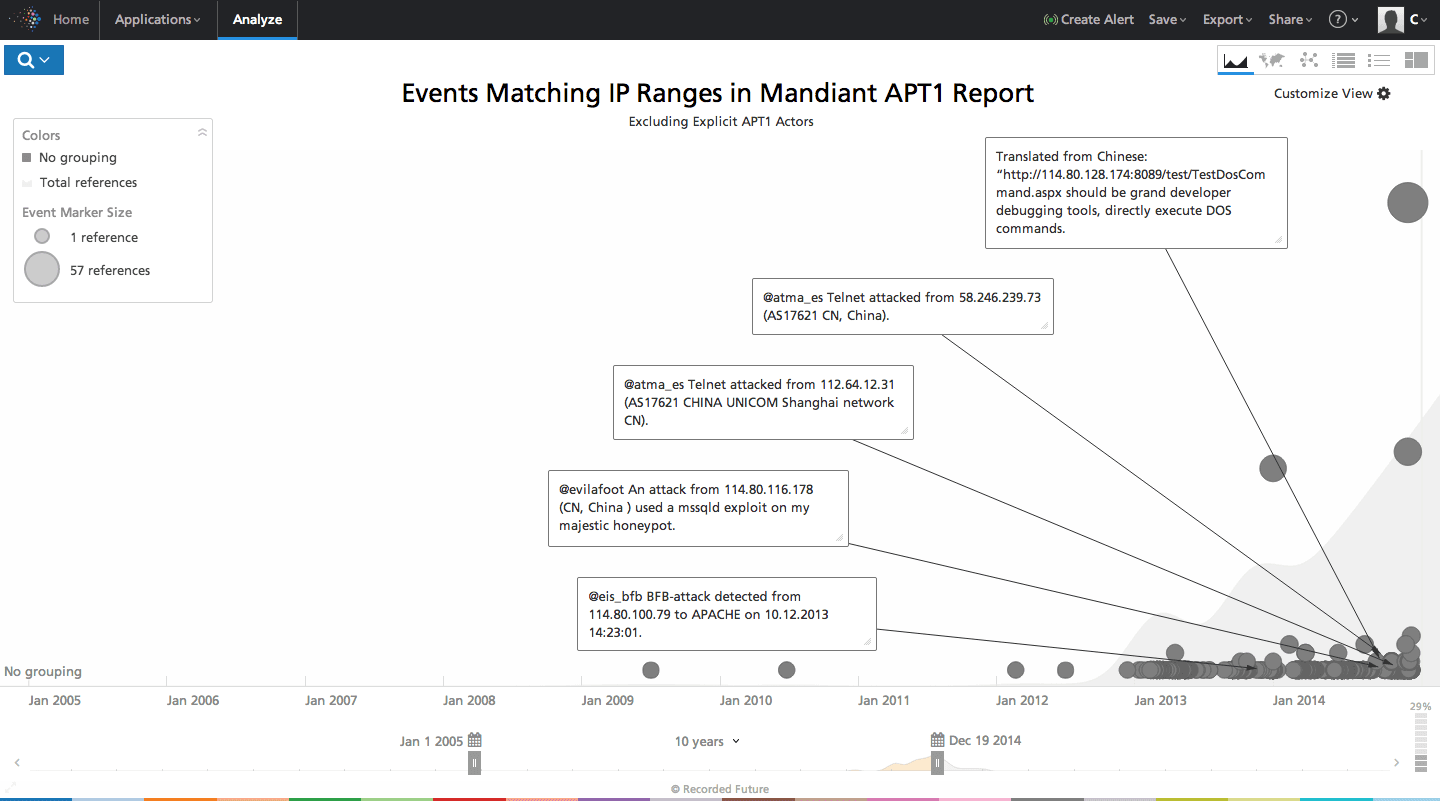
We can easily pivot our analysis to analyzing the sourcing for the above timeline, and we can see how Pastebin is a big source (probably users dumping lists of “bad” IP numbers predominantly), Clean MX (again reporting IPs with issues) and then a series of more specialized security blogs reporting on various issues seen out of these ranges.
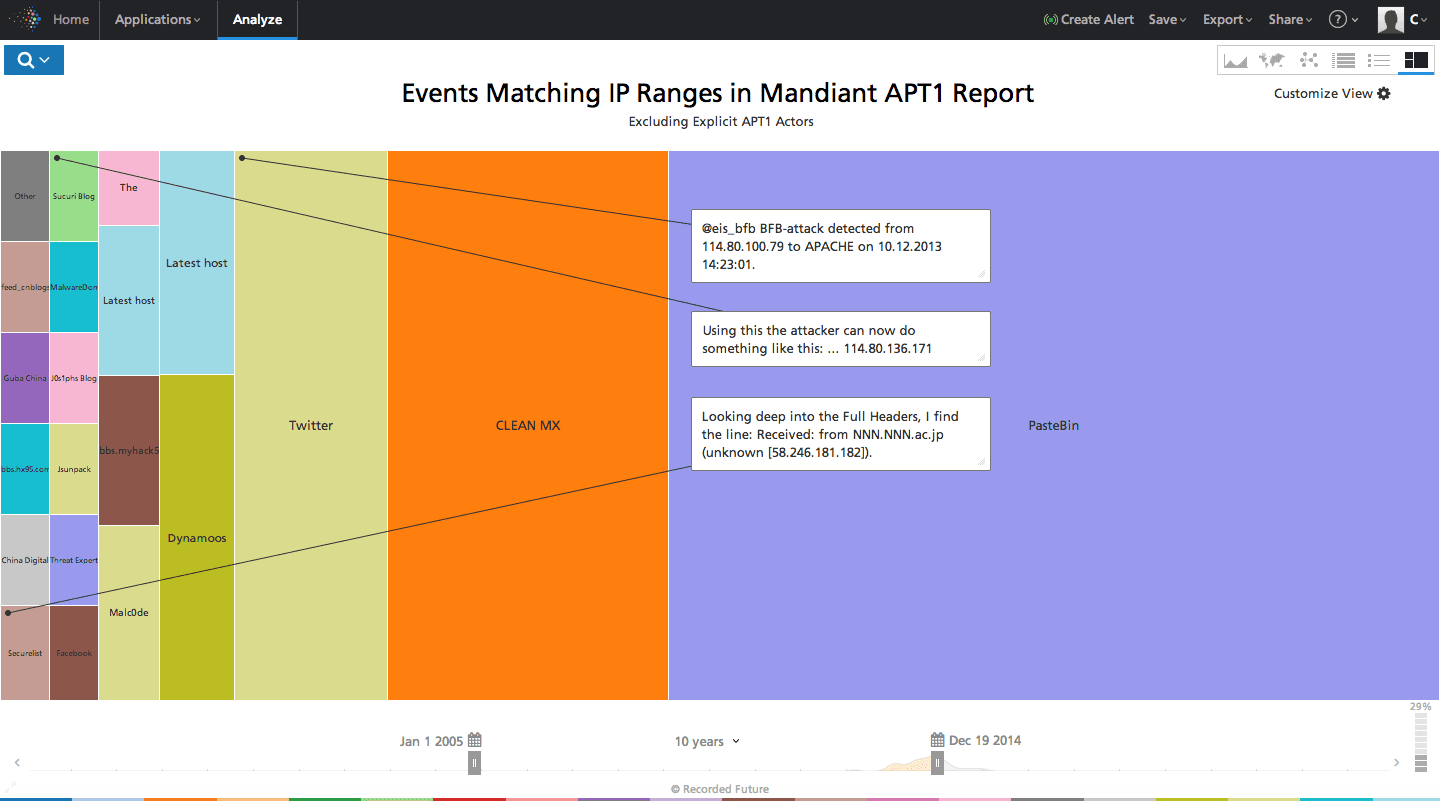
We can also see entries for these ranges out of Chinese hacker sites like myhack58.com.
Alerting Going Forward
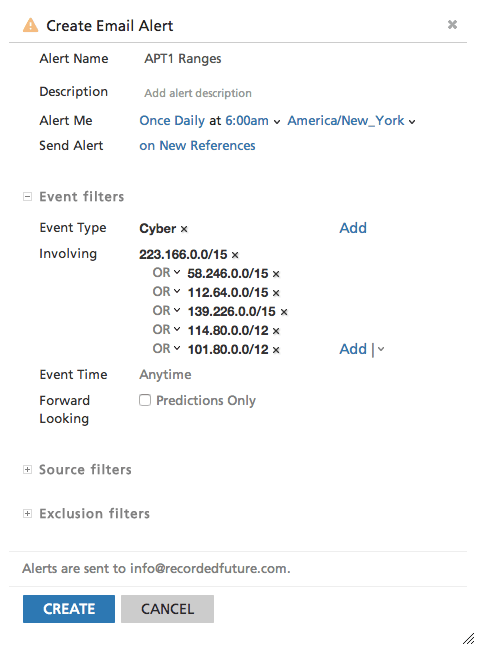
Finally, to stay on top of new events related to these ranges, we can quickly set up an alert to track any further malicious activity.
Conclusion
The ability to search IP ranges rather than just individual IP addresses is quite powerful, and allows us to cover a lot of space in one query/analysis. We utilize this to search the hop point IP ranges originally used by APT1 and identify continued potential malicious activity. We make no conclusions on whether this is continued APT1 activity or not, but at the surface level it does not appear to be very serious behavior.
Related