Intent to Infekt: ‘Operation Pinball’ Tactics Reminiscent of ‘Operation Secondary Infektion’

Editor's Note: The following post is an excerpt of a full report. To read the entire analysis, click here to download the report as a PDF.
Executive Summary
Insikt Group recently identified an ongoing information operation that we assess with high confidence shares significant overlap with what the Atlantic Council’s Digital Forensics Lab (DFRLab) refers to as Operation Secondary Infektion (Secondary Infektion); a covert information operation targeting governments in the United States and Europe and believed to originate from Russia. We have named this information operation “Operation Pinball.”
Recorded Future’s investigation into Operation Pinball revealed a covert influence operation that analysts assess attempted to undermine the government of Estonia and its relationship with the European Union while exploiting the ongoing European migrant crisis. Recorded Future analysts also discovered a second instance of this campaign targeting the government of Georgia and the disputed territories of Abkhazia and South Ossetia, and seeking to undermine Georgia’s growing relationship with the North Atlantic Treaty Organization (NATO). This information operation consisted of a wide network of self-publishing webpages, one-off accounts, Reddit and social media promotion, and analysts saw evidence of an emphasis on operational security (OPSEC) and connections to sources that Insikt Group assesses to have a strong command of the Russian language. We assess with high confidence that this information operation targeted Russian-speaking audiences in Eastern Europe and among the Commonwealth of Independent States (CIS). At this time, analysts assess with high confidence that at least one of these operations is ongoing, and others, as yet unidentified campaigns, are likely in planning stages.
Further investigations into one self-publishing website revealed additional, previously undisclosed, attempts to plant false documents targeting U.S. officials and U.S. political organizations’ relationships with international policymakers and governmental bodies. It appears that these fraudulent documents attempt to emulate confidential correspondences on sensitive international issues in Eastern Europe to make them seem to be authentic leaked information on the topics. The age of these documents, ranging from January to June 2019, aligns with known activity periods of Secondary Infektion.
This report illustrates Recorded Future’s observations in detail. Analysts believe that this activity demonstrates the complexity and layers of this campaign and indicates that similar, prior campaigns were more wide-ranging among Eastern European sources than initially thought.
It is also important to note that while there is strong evidence to indicate a coordinated effort to push this false story into the mainstream, this event, like most Secondary Infektion-attributed events, was not successful. Overall, Insikt Group identified minimal shares on social platforms and Reddit threads were quickly deleted by page administrators of the various pages.
Further, we believe that the prodigious OPSEC demonstrated by this group limited the effectiveness of single-use accounts to build personas and grow audiences required for content to go viral. Based on our observations, if an active campaign does not reach mainstream sources the effort is likely to be abandoned.
Key Judgments
- We found that this activity shared significant overlap with previously reported tactics, techniques, and procedures (TTPs) used in Secondary Infektion campaigns, namely the use of self-publisher blogs with single-use personas, Reddit promotion, and multilingual obfuscation. Distinct TTPs overlapping with Secondary Infektion that we emphasize in this report include the following:
- The use of forged letters and email correspondence
- Targeting of geopolitical incidents in the greater CIS
- Language errors that are characteristic of native-Russian speakers
- Seeding on self-publisher websites to include homment.com, as well as self-publishers based within Russia’s “near abroad”
- We assess with high confidence that Estonia-targeted activity was a coordinated, deliberate attempt with four objectives:
- Undermine the relationship between Estonia and the EU
- Degrade Estonian confidence in their government
- Create internal political strife among elected Estonian officials
- Alter public opinion against migrants coming to Estonia, and to a greater degree sour the public perception of migrants in Europe
- We assess with high confidence that Georgia-targeted activity is a coordinated, deliberate attempt with five objectives:
- Prompt support and international recognition of Abkhazia and South Ossetia quests for independence
- Undermine a growing relationship between the NATO alliance and Georgia
- Undermine Georgian support of national political leadership and establish a narrative that current political figures are corrupt to the benefit of the West
- Create uncertainty in Georgia’s economy and energy independence
- Promote the narrative that NATO consists of a selfish, ruling elite that does not have Georgia’s best interests at heart
- We expect to see additional instances of Operation Pinball tactics, such as the use of planted false documents against Western governments and international institutions, even though these information operations have been largely unsuccessful to date.
- We assess that covert influence operations from Russia against the U.S. and the 2020 election will probably seek to leverage similarly manipulated and forged documents, particularly regarding attempted hack-and-leak operations when the adversary either may not have access to original files, or deems hacked authentic files as ineffective kompromat.
Background
Throughout 2019, Recorded Future observed reporting from the Atlantic Council’s Digital Forensics Lab (DFRLab) of an alleged Russian-based information operation, dubbed Secondary Infektion. The operators used covert “fake accounts, forged documents, and dozens of online platforms to spread stories that attacked Western interests and unity.” DFRLab attributed this suspicious activity to a Russia-based covert operation, based on an analysis of a small network of accounts originating from Russia that was suspended by Facebook in May 2019 after they were found to be distributing false claims and news stories tied to initial Secondary Infektion vectors.
Secondary Infektion is named after the notorious Soviet Union-era “Operation Infektion” disinformation campaign that aimed to convince the world that AIDS was invented by the United States. In all, Operation Infektion took four years to reach mainstream media mentions. What has changed recently, however, is the speed and precision targeting with which such operations can be waged using social media and other online platforms. In other words, what took Operation Infektion years to achieve potentially takes only days or weeks at most for Secondary Infektion information operations — if they are successful.
Secondary Infektion bears similarities to well-known “hack-and-leak” operations, a practice in which stolen information is subsequently released in an attempt to influence public perception for or against an issue. Hack-and-leak operations have targeted U.S. political organizations, such as the Democratic National Committee (DNC) and Democratic Congressional Campaign Committee (DCCC), with the contents of these leaks later released to the public by known GRU operations DCLeaks and Guccifer 2.0 as a means of election interference in the 2016 U.S. presidential election. Similar hack-and-leak operations have targeted international sports regulatory agencies such as the World Anti-Doping Agency (WADA), as well as malicious information campaigns against athletes.
In the case of Operation Pinball, we observed significant overlap with Secondary Infektion’s use of false stories, often including planted fake document images (“leaks”) posted by one-off burner personas on obscure online platforms such as self-publishing journalistic outlets or blog sites. These stories were often then revised or expanded upon using a second set of established burner personas on sites such as Reddit, LiveJournal, and self-published (but more frequently used) blogs with little to no moderation or policing. At this step, these information operations translated false claims into another well-known language (such as English, French, or German) both for broader consumption as well as using translation to obfuscate the origins of the claim.
The final step included personas pushing false stories on social media, with the ultimate aim of targeting mainstream media and news organizations for broader audience consumption. In the case of Guccifer 2.0 and other hack-and-leak operations tied to the GRU, the adversaries conducting the activity communicated with journalists in a likely attempt to provide greater visibility for the information. The most recent instance of this behavior pertaining to Secondary Infektion was when leaked trade documents from the U.K. National Health Service (NHS) were distributed to Global Justice Now, a U.K.-based organization, through a secure email address with no name.
According to DFRLab, Secondary Infektion information operations share attributes commonly associated with Russian intelligence services, namely that the activity their research team observed was conducted with a high degree of operational security (OPSEC), was well resourced, and persisted over a long period in support of objectives that align with ongoing Russian strategic goals. Despite these observations, there is no available information that directly links Secondary Infektion, or Operation Pinball for that matter, to Russian intelligence services as of this writing. We assess that this is because the operators are highly skilled in OPSEC and use techniques that effectively obfuscate their origins. OPSEC not only provides key plausible deniability, but allows Russian state-sponsored media to counter these observations with alternative hypotheses, insults, doubt, and other distractions.
Discovery of Operation Pinball Targeting Estonia
Threat Analysis
On December 18, 2019, the author “flokortig” published the article “Neue Flüchtlingskrise: Europa ist nicht dazu bereit,” (Translated: “New refugee crisis: Europe is not ready for it”) on the German self-publishing website homment.com. Homment was previously linked to multiple instances of Secondary Infektion document seeding as reported by DFRLab. After publication, Homment visitors viewed the article approximately 250 times.
This article began by blaming the U.S. and Europe for “wars in Middle East [sic] and Africa,” resulting in waves of refugees entering Europe since 2015. The article proceeded to illustrate “the reception of refugees in some EU countries,” highlighting France and Greece, claiming that non-transit migrants overwhelm France, and noting reports of violence among migrants in Greek refugee camps. The article then turned to Estonia, claiming that the state welcomed the EU’s migration quotas, despite “political opposition and existing government disagreements.”
The post included a copy of a letter, which we judge was inauthentic, addressed to Mr. Dimitris Avramopoulos, the European Commissioner for Migration, Home Affairs and Citizenship, from Taavi Aas, Minister of Economic Affairs and Infrastructure of Estonia. The letter made the claim that Estonia agrees with the EU refugee admission quotas despite concerns regarding statements from Foreign Affairs Minister Urmas Reinsalu and “several other Estonian politicians” that were deemed contrary to the EU’s standing on migrant quotas. The letter claimed these dissenting views were, in fact, the personal views of these individuals and were stated only to score “political points.”
The article also pointed out that Hungary, the Czech Republic, and Poland are campaigning against the EU immigration policy “by building a wall as they wish and deciding for themselves who will enter their territory ... Such steps by the Eastern European countries make it difficult to implement the common EU migration policy.” These domestic policies, according to the article, only further hinder other EU states from adequately accommodating migrants.
In relation to the European migrant crisis, the article stated the following:
“The situation looks bleak on the whole. The state of the infrastructure for the reception of asylum seekers in the EU shows that Europe is not ready for the wave of refugees like in 2015. The EU-Turkey Refugee Agreement, which aimed to reduce the number of refugees entering the EU, has stopped working. EU migration policy is paralyzed. It is unclear whether one can find the way out. Because of the disagreements between Western and Eastern Europe, the real unity of the European continent is very doubtful.”
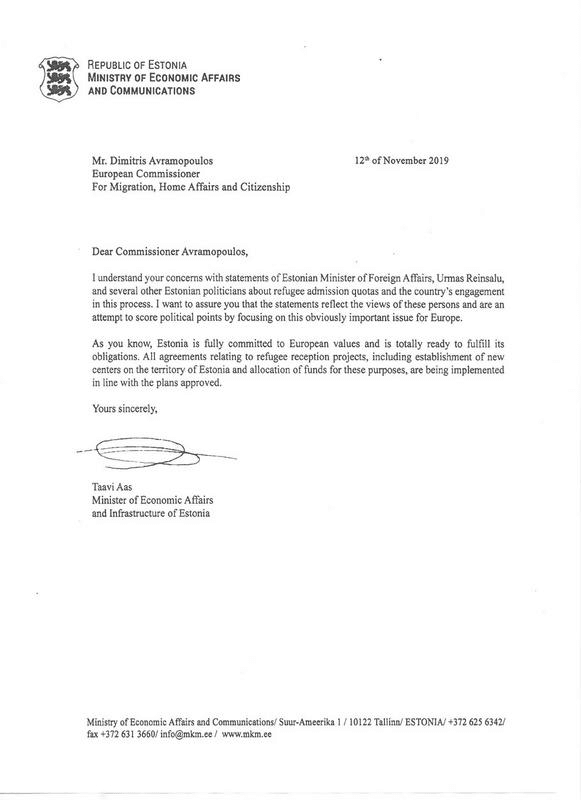
Forged letter addressed to Mr. Dimitris Avramopoulous from Estonian Economic Affairs Minister Taavi Aas. (Source: Homment)
By analyzing the document, it is quickly apparent that native English-language speakers did not prepare this document, but was a well-crafted attempt at appearing authentic. We are aware that Taavi Aas speaks fluent English and official correspondence from the Ministry would most likely not include any of the following errors and observations.
One indicator of inauthenticity is located in the first statement, "I understand your concerns with statements of Estonian Minister of Foreign Affairs…," which is a grammatically incorrect English construction. Insikt Group Russian-language experts note that potential linkage of this sentence to a Russian speaker is the use of the genitive case in Russian, which, when translated into English, sometimes results in the incorrect use of the preposition "of" to denote ownership. Furthermore, this example demonstrates a consistent lack of indefinite/definite articles throughout the forged document, to include this example. Russian does not have a definite or indefinite article (i.e. the/a/an) or the verb "to be" in the present tense, and many English-speaking Russians have considerable trouble using “the” and “a” correctly, often using them interchangeably or leaving them out entirely. If a fluent English speaker correctly wrote this statement, it would likely state "I understand your concerns with [the] statements of [the] Estonian Minister of Foreign Affairs..."
In the body of the document, there are multiple instances of unusual or colloquial language that are unlikely to appear in formal government correspondence, such as the use of the words “totally ready,” “scoring political points,” as well as the statement “establishment of new centers on the territory of Estonia,” rather than simply, in Estonia. We note that на территории (on the territory of) is commonly spoken in Russian and is grammatically correct.
The forged letter contains what we refer to as imprecise language, meaning that the author likely did not have a concrete position on Estonian migrant quotas or specific government projects and was likely not entirely well versed in the subject matter. Therefore, the author of this document resorted to vague or confusing phrases such as “establishment of centers” rather than specifying refugee centers or specific housing projects for migrants in Estonia.
The footer of the document itself has improper spacing, which would likely not pass by a government-level editor. Further, the titles of Mr. Avramopoulos and Mr. Aas on the letter are improperly and inconsistently formatted.
The signature of Mr. Aas also raises concerns. While his signature is not commonly found in open sources, a 2010 document prepared by The Civitas Initiative and the EU, which contains Mr. Aas’s legitimate signature during his tenure as Tallinn deputy mayor, indicates that the signature found in the 2019 letter was likely an attempted, far-less fluid, forgery. Given the simplicity of the signature itself, this opens opportunities for attempted emulation.
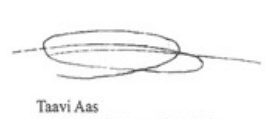
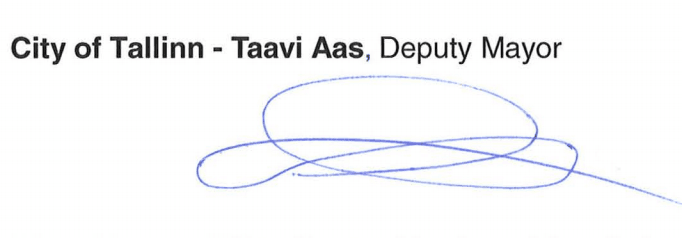
Comparing a verified signature of Taavi Aas (top) to the forged document (bottom).
Outlook
These operations targeting Estonia, Georgia, the EU, and NATO follow similar patterns of activity documented in connection to historic personas constructed by the GRU. According to reporting by Stanford University’s Internet Observatory Cyber Policy Center, “[GRU] Pages were created and run within a distinctly short time frame, often with frenetic posting patterns. They were spun up in response to a geopolitical event or provocation — including to serve as a public drop for hacked materials.” However, unlike hack-and-leak operations, there is no reported evidence indicating that these were leaked documents from breached sources, such as the most recently publicized Secondary Infektion operations targeting the UK’s National Health Service.
We are confident that this is a deliberate, coordinated, and methodical operation to undermine relationships among political figures and democratic institutions across Europe perpetrated by actors with a strong command of the Russian language. These operational aims and tactics align with the disinformation arm of the Russian political warfare policy of “активные мероприятия” (Translated: “active measures”), and the tactics are strongly reminiscent of historic activities of Russian security services. This report, however, does not link these activities to the GRU or any other Russian intelligence service because we have insufficient information on the actors or any connections to the Russian intelligence services.
To date, institutions in North America and Europe were the subjects of this activity and are likely to remain targets in the future. Though we have not identified specific cases of Operation Pinball targeting the U.S. 2020 election process, we believe that the operatives behind this information operation are likely capable of doing so. They have consistently demonstrated the ability to craft forged documents and quickly disperse them over a variety of sources in a clearly organized manner.
For influence campaigns, operational success remains an ill-defined goal. Some metrics of success likely include views, reposts, engagement numbers, propagation of the message or story, presence in “mainstream” media, and ultimately manipulating the opinions of viewers. However, many of these goals are hard to measure. From our perspective, Operational Pinball actors would need to improve the fluency of their fraudulent and inauthentic communications and build networks of older and more trusted personas to conduct a successful influence campaign in the U.S. Inadequate fluency in target language and over reliance on known inauthentic influence tactics will likely hinder Operation Pinball actor’s ability to penetrate mainstream U.S. media.
In the lone case in which these tactics achieved success — in the U.K. regarding the NHS — we believe it was simply a matter of being in the right place, at the right time, with a particularly divisive topic in the heart of an election cycle. Well-crafted false documents and letters planted on Reddit, social media, and self-publishing sites (like Medium or WordPress) which attempt to emulate correspondence between U.S. political figures remains a significant possibility, and, if successful, could have wide-ranging consequences for the U.S. elections. We believe it is possible that actors could leverage Operation Pinball tactics against U.S. political figures this year.
Mitigations
Though preventing these tactics is difficult, the impact of this information operation can be mitigated using a whole-of-community approach, including the following steps:
- Sites and additional pages that are likely to be exploited by these operatives should be continually monitored.
- Administrators should quickly isolate and remove this content once it is identified and confirmed.
- Targets of these operations, such as politicians who are impersonated, should be made aware of these operations and publicly highlight the inaccuracies and falsehoods of forged letters for further public assurance.
- Affected organizations and individuals must foster greater public awareness of blatantly false claims and the key indicators to identify forged materials.
Editor's Note: This post was an excerpt of a full report. To read the entire analysis, click here to download the report as a PDF.
Related