Fusion Use Case: Automated Bulk Enrichment

Blog Series
In part one of our Recorded Future Fusion use case series, we looked at high-fidelity alerting. Here we look at another new features of our threat intelligence platform module — the ability to integrate proprietary feeds and customer-created threat intelligence. One of the driving forces for this feature was requests from customers to add feeds we don’t have access to. When we talk about this feature, it’s the ISAC feeds that most often come to the minds of customers.
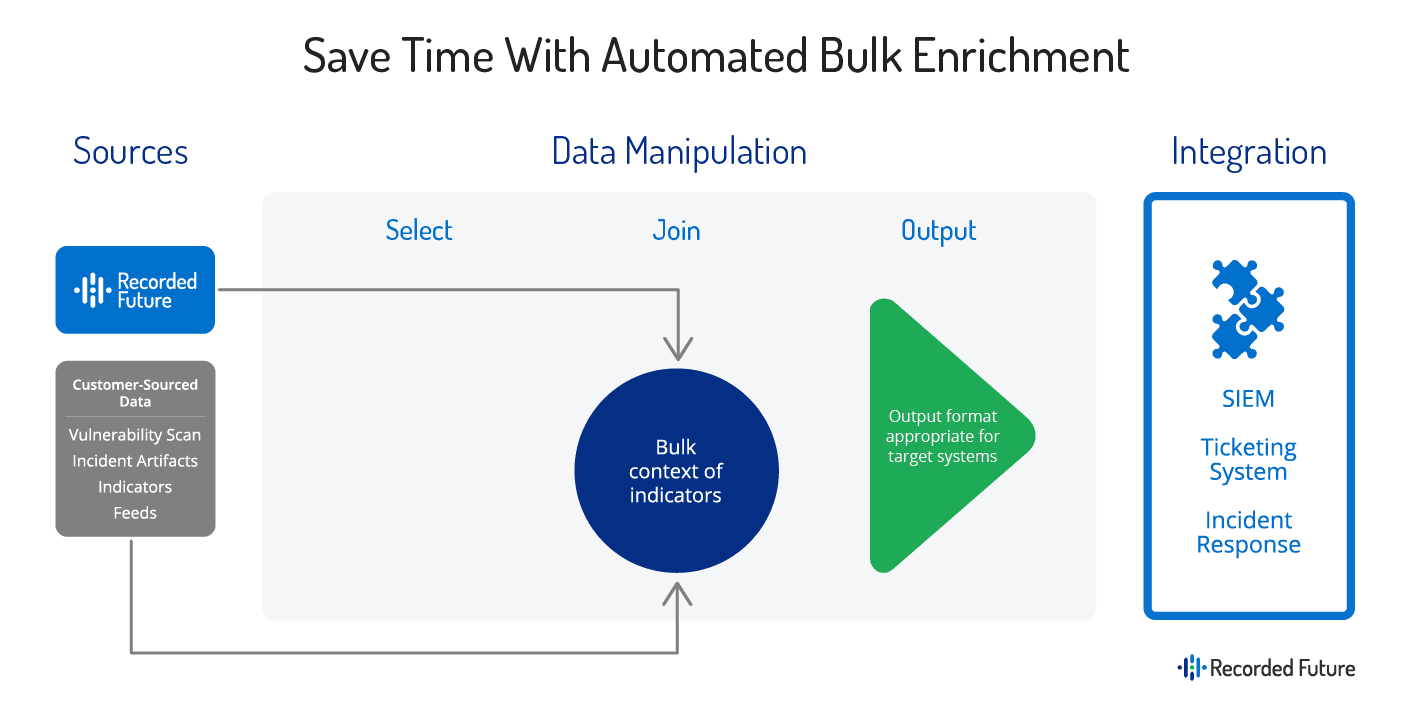
There is another significant value derived from this new feature, however, and that’s the ability to import a list of indicators or entities into Recorded Future and automatically add contextualized threat intelligence for faster, more confident decisions. We call this use case automated bulk enrichment, and it can be used in a variety of ways.
At a high level, the process looks like this:
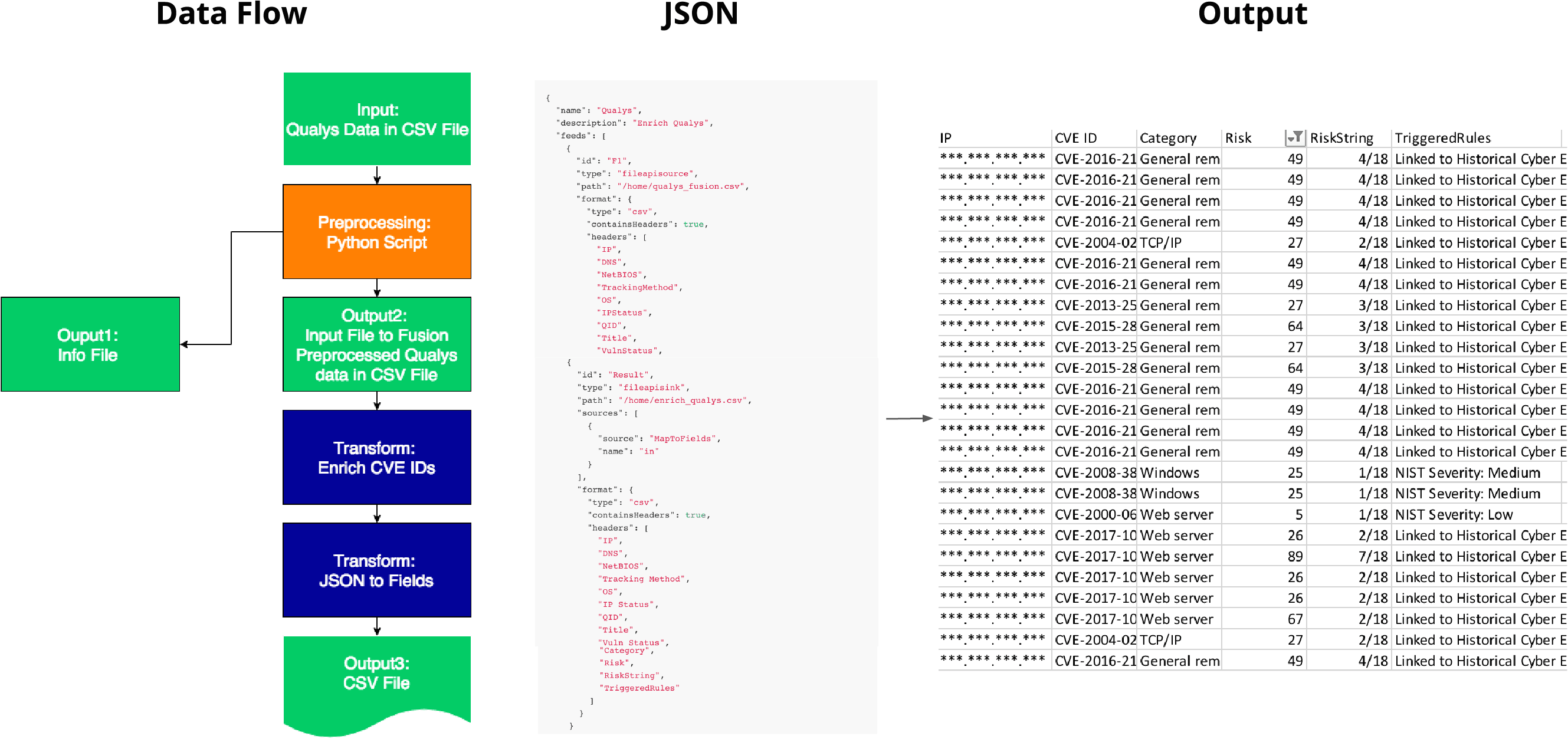
Prioritizing Vulnerabilities for Patching
A specific example of how this process might work is to enrich a list of vulnerabilities discovered during a scan. In this process, vulnerability scan results are uploaded into Recorded Future using Fusion, and then rich context including dynamic risk scores and justification, related methods and indicators from potential exploitation, and associated attack vectors and threat actors. This data can then be either imported into a separate solution or easily viewed and sorted to prioritize vulnerabilities representing the largest threats. This process is critical for maximizing risk reduction, as it has been proven that CVSS scores should not be the sole source of information for vulnerability risk.
Add Rich Context to a List of Indicators
Now, let’s return to the value in importing exclusive-access feeds such as FS-ISAC into Recorded Future. As I mentioned, this is one of the more common use cases that comes up when we discuss this feature. But what is the real value here? There is some value in simply having all of your threat intelligence in one central location. But, what we often hear is that some of these proprietary lists lack the context required to make them very useful. That’s where Recorded Future comes in. With Fusion, organizations can not only import these lists, but they can also automatically add rich context and validate and prioritize the data all within the singular Recorded Future platform.
These are just two example use cases for importing proprietary and exclusive-access lists into Recorded Future Fusion. We are working with customers every day to explore new use cases.
Stay tuned for the next blog to learn more about efficient internal collaboration with Recorded Future Fusion!
Related