Mastermind Behind Andromeda Botnet Arrested in Belarus

Executive Summary
On December 4, 2017, a joint task-force of European Law Enforcement agencies, U.S. FBI, and several non-EU Member States successfully dismantled Andromeda botnet, one of the oldest and largest criminal botnet operations. According to Microsoft, more than 2 million compromised computers worldwide were identified in 48 hours of observations prior to the take down. It is estimated that the Andromeda botnet was used by various criminal groups and individual actors to distribute more than 80 families of malware.
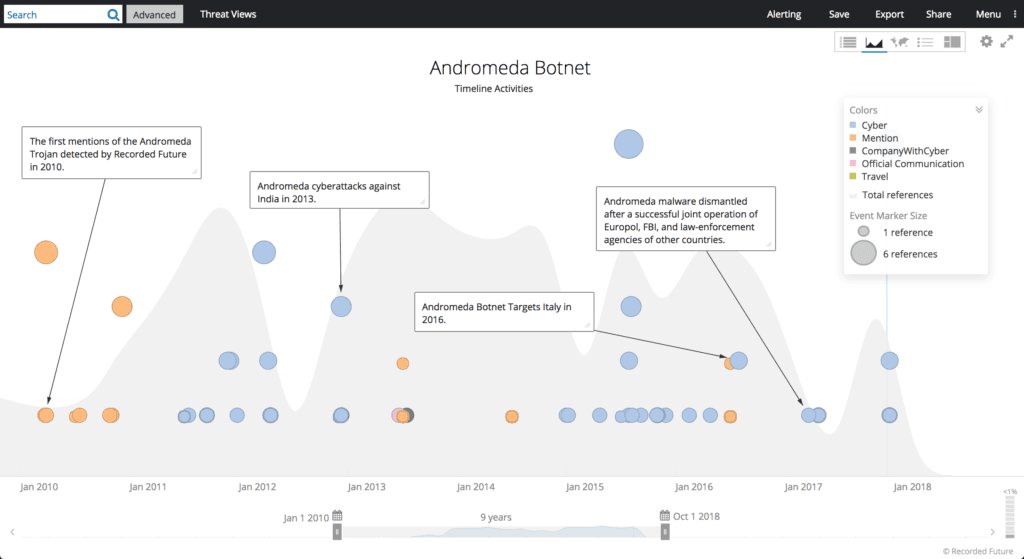
Timeline of Andromeda Botnet activity up to takedown.
The Investigative Committee of the Republic of Belarus reported that, with FBI cooperation, it arrested a member of the international cybercriminal group responsible for the distribution and maintenance of the Andromeda Trojan.
Video of officials questioning Ar3s and subsequent arrest.
We believe that the arrested person is the actor known as “Ar3s,” one of the oldest and more highly respected members of the criminal underground. Ar3s is the mastermind behind the Andromeda Trojan and a longstanding administrator of the Damage Lab hacking forum. With a high degree of confidence, we assess that the arrested person is likely Jarets Sergey Grigorevich, although the name was not revealed by the Belarusian authorities.
Key Judgments
Ar3s is recognized as a leading expert in malware development and reverse engineering, network security, and antivirus technology. On technologically sophisticated forums he acts as a highly reputable guarantor of deals on the one hand, and an analyst on the other. Based on the analysis of Ar3s’s forum activities, linguistic patterns, and photo materials, Recorded Future earlier identified him as Sergey Jarets or Jaretz, a 33-year old male residing in Rechitsa, Gomel region, Belarus.
According to the materials of the investigation, undercover FBI agents purchased malware from the Belarusian hacker to ascertain the connection between the actor and the Andromeda malware distribution. The source code of this program was verified by the security experts and confirmed to be malicious.
According to the press release, the investigation collected incontrovertible proof of his fraudulent activities and involvement in the hacker group along with other criminals: sellers, server owners, as well as users of the tool.
Recorded Future conducted additional research across cybercriminal forums and with a high degree of certainty confirms that the arrested person is Ar3s.
Background
Ar3s, also known as “Арес” (in Russian), “Ch1t3r,” or “Sergey Jaretz”/“Sergey Jarets” (see below), is one of the most respected and longest-standing members of the hacking community and has operated in the Russian-speaking underground since at least 2004.
The actor is best known as a developer of the powerful Andromeda bot created in 2011, as well as the Win32/Gamarue HTTP bot. The actor is also known as the author of the Windows SMTP Bruter v.1.2.3, an SMTP bruteforcing tool, as well as “Swf-Inj Service” which hijacks web traffic by embedding iFrame malware into SWF (small web format) files.
According to the law enforcement statement, the criminal received $500 for each copy of Andromeda sold, and $10 for each follow-up malware update.
Threat Analysis
Recorded Future conducted additional analysis of Ar3s’s recent activities and observed that the last time Ar3s accessed DaMaGeLaB forum was on November 22, which could indicate the date of the arrest. Other members of various criminal communities have also expressed concerns that Ar3s has been unresponsive since at least November 20, 2017.
The facts mentioned above, along with the coincidence of other factors, such as his residence in Gomel Region, Belarus, date of birth, and administration of cybercriminal forums are clear evidence of Ar3s’s apprehension.
Since following Ar3s, we learned that Ar3s has used the ICQ number “5777677” as one of his primary contact methods, which was connected to the internet user “Sergey Jaretz” (very similar to the Russian spelling “Арес” and conformable with Jaretz/Ярец), who was also registered on multiple white-hacker and tech-oriented forums since the mid-2000s.
Once we had a possible name, we conducted subsequent contact analysis based on “Sergey Jaretz” and the above-mentioned ICQ number. We discovered that the phone number of the Belarusian mobile carrier MTC (+375) 29-735-56-11 tied him with an individual in Rechica, Belarus named Sergey Jarets or Jaretz (in Russian: Сергей Григорьевич Ярец), a person working at OJSC “Televid” Tele-Radio Company, broadcasting throughout Rechitsa area, Gomel Region, Belarus.
According to an open web search, as well as the LinkedIn page of the actor, Jaretz has been a Technical Director of OJSC “Televid” since 2003 and is responsible for procurement, maintenance of the company’s computer network, maintenance of its television station, contract work regarding technical issues, OSHA regulation, and staff management. His LinkedIn profile indicates that Jaretz studied at Gomel State Technical University in 2010-2012 and obtained a degree in software engineering.
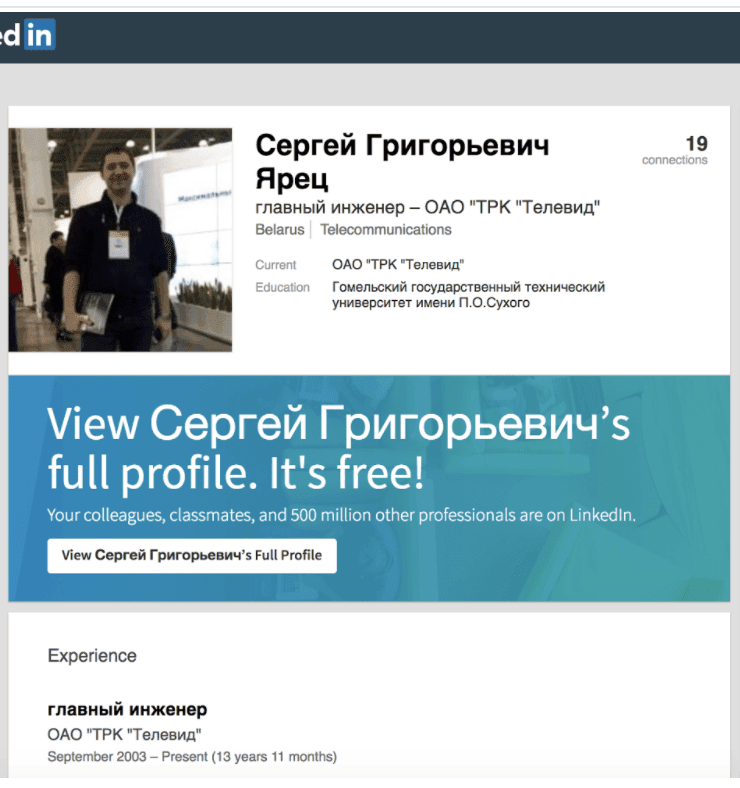
Sergey Jarets’s LinkedIn page indicating his work at OJSC “Televid” Tele-Radio company.
The actor’s Belarusian roots can also be confirmed by the testimony of other members of the underground criminal communities who call Ar3s the “Belarusian” during their conversations.
Created in August 2011, the actor’s Twitter account also indicates Belarus as his location.
Outlook
Following the Avalanche operation in 2016, the Andromeda botnet takedown and the arrest of Ar3s is an excellent example of successful cooperation between international law enforcement agencies, including non-EU Eastern European members. Once again it shows the determination of international governments to eradicate cybercrime by supporting high-level joint operations and leveraging the expertise of law-enforcement agents.
To get more information and view screenshots of the arrest, download the appendix.
Related