Using Vulnerability and Exploit Analysis to Effectively Assess Cyber Threats
We’re all aware that managing and remediating vulnerabilities is an essential component for effective information security. There’s an ongoing need to identify, classify, remediate, and mitigate vulnerabilities that could compromise your network.
Effectively assessing the risk from a given vulnerability is critical, as the security impact of remediating a specific vulnerability could be dramatically higher than the average. Thousands of vulnerabilities have been disclosed over recent years, yet only a handful, some quite long in the tooth, are the key enablers of loosely targeted attacks enabled by exploit kits.
The outlook for defense of corporate networks and business applications is much more complex and vulnerabilities affecting web applications and business workstations are urgent issues — especially if mitigation and remediation happens while threat actors are still refining malicious code, or compromising exploit targets in other victim organizations.
Recent Recorded Future research entitled “Turning Criminal Forum Exploit Chatter Into Vulnerability Risk Analysis” highlighted that, “Vulnerability management teams waiting on formal CVE releases or specific remediation guidance from vendors are at a disadvantage.”
Using external threat intelligence and analysis it’s possible to observe the series of gates or milestones through which we would expect a specific vulnerability to advance.
As each gate is passed, the level of risk which we can reasonably expect the vulnerability to eventually pose increases.
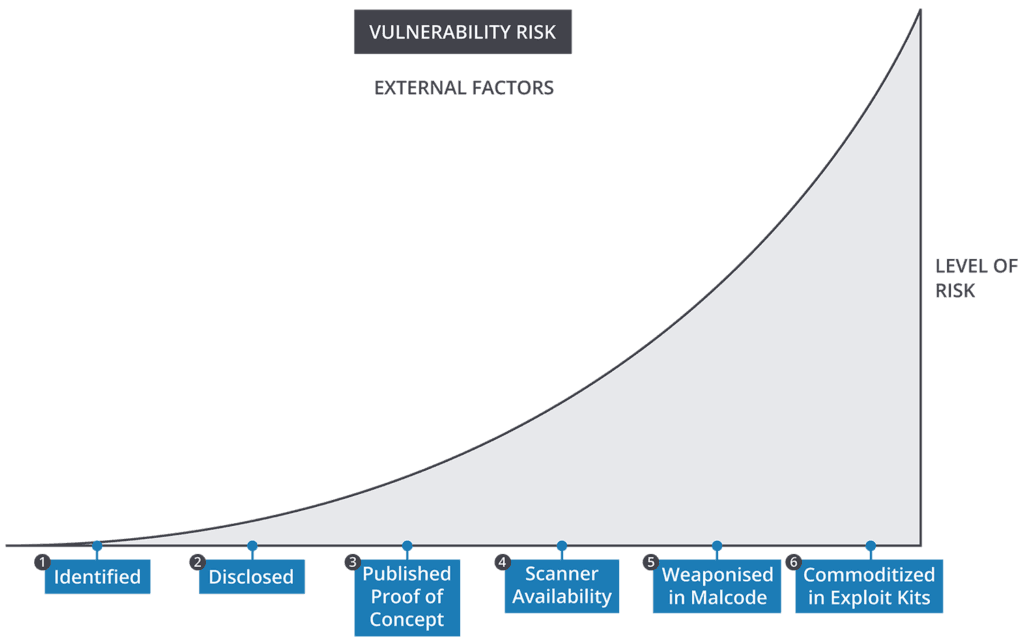
- Vulnerability is identified by the vendor, by researchers, by threat actors.
- Vulnerability is disclosed publicly, privately among security practitioners with risk of OPSEC breakdown, or privately among threat actors in dark markets.
- Proof of concepts that exploit the vulnerability are available. Again, this may be public or private in certain communities.
- Scanners are available to automate identification of vulnerable systems. These scanners are often dual-use technology that penetration testers and red teams depend upon, and threat actors can also leverage offensively.
- The exploit has been weaponized in malcode that is capable of infecting or compromising an exploit target. Malcode samples have been captured, and may be closely held or published.
- Use of the exploit has been commoditized in toolkits for building malcode, or in exploit kits that can be rented to use the vulnerability as a method for other malcode to establish unauthorized access.
Real-Time Threat Intelligence for Vulnerability Analysis
Our goal is to enable you to identify, assess, prioritize, and respond to vulnerabilities with speed and confidence. Recorded Future Vulnerability Cards are the focal point, condensing all the intelligence we’ve gathered on each vulnerability from the open, deep, and dark web into a single view and computing a risk score that’s updated in real time.
You can see the power of vulnerability analysis in this short video:
Rapidly assess risks from known vulnerabilities.
Recorded Future computes vulnerability risk scores and presents evidence with links to sources. Intel on exploitation and malcode is merged with NVD data for quick access to vendor advisories with mitigation and remediation steps. Enrich your security products with Intelligence Card™ content via our API integration. Identify vulnerabilities with a higher risk of being weaponized.
Get specific alerts when vulnerabilities of interest are linked to exploit kits and high-risk malware categories that are relevant to your enterprise. Define dashboards and alerting rules for vulnerabilities affecting products in your tech stack using specific CPE names (vendors, products, versions). Discover undisclosed or new vulnerabilities and zero-day exploits.
Recorded Future’s programmatic identification of exploit chatter for unknown vulnerabilities helps you improve remediation prioritization based on evidence of increased adversary intent and/or capabilities. See real-world examples in our special analysis report.
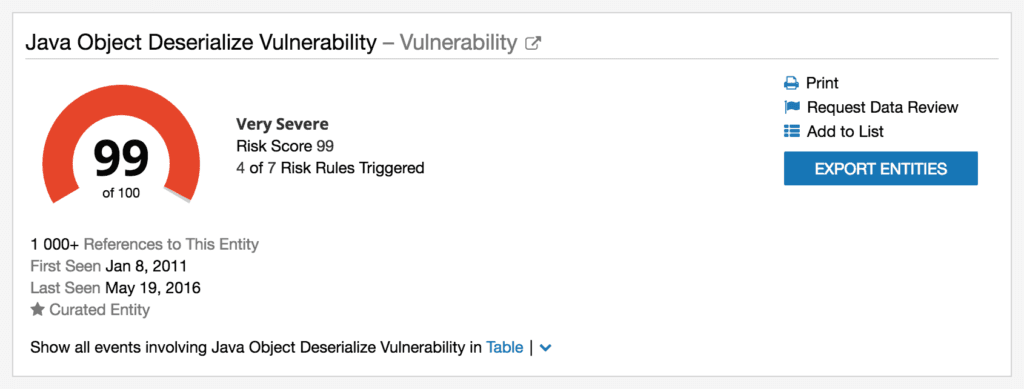
Example of a Vulnerability Card.
Want a tailored demo of how Recorded Future can help your company speed up vulnerability assessments? Request a demo now.
Related