What the 6 Phases of the Threat Intelligence Lifecycle Mean for Your Team
Editor’s Note: Over the next several weeks, we’re sharing excerpts from the newly released second edition of our popular book, “The Threat Intelligence Handbook: Moving Toward a Security Intelligence Program.” Here, we’re looking at chapter two, “The Threat Intelligence Lifecycle.”
On your journey to security intelligence, comprehensive, real-time intelligence must be woven tightly into your security processes, third-party risk management program, and brand protection strategy. But in order to get there, how can you develop threat intelligence that truly adds value to your organization? And how can you ensure the intelligence you deliver is actionable for teams across security functions?
To answer these questions, it’s important to view threat intelligence production as a multi-step, cyclical process — not a point-in-time task.
First, the goals of the cyber threat intelligence cycle must be defined by key stakeholders. These objectives may vary widely from organization to organization depending on use cases, priorities, and risk. From there, data must be gathered from a range of sources — internal, technical, and human — to develop a complete picture of potential and actual cyber threats. Then, this data must be processed and turned into actual intelligence that is timely, clear, and actionable for everyone — whether they’re staffing a SOC, responding to security incidents, managing vulnerabilities, analyzing third-party risk, protecting your digital brand, or making high-level security decisions. This finished intelligence output then goes back to key stakeholders, who can use it to continuously improve future intelligence cycles and hone their decision-making process.
The following excerpt from “The Threat Intelligence Handbook: Moving Toward a Security Intelligence Program” has been edited and condensed for clarity. In it, we'll examine each of the six phases of the threat intelligence lifecycle, review sources of threat intelligence, and look at the roles of threat intelligence tools and human analysts.
Threat Intelligence Lifecycle in 6 Steps
Threat intelligence is built on analytic techniques honed over several decades by government and military agencies. Traditional intelligence focuses on six distinct phases that make up what is called the “intelligence cycle”: direction, collection, processing, analysis, dissemination, and feedback.
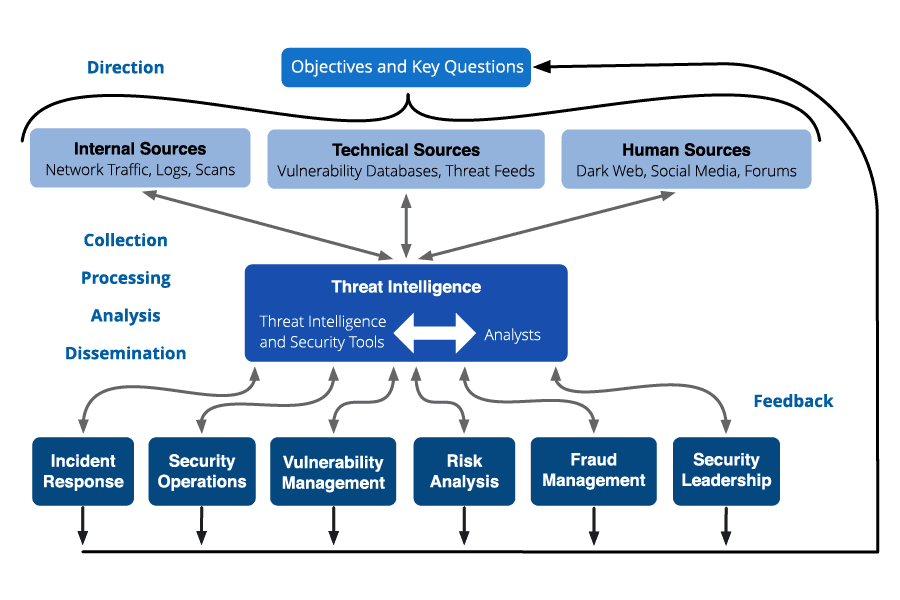
Threat intelligence and the six phases of the intelligence lifecycle.
1. Direction
The direction phase of the lifecycle is when you set goals for the threat intelligence program. This involves understanding and articulating:
- The information assets and business processes that need to be protected
- The potential impacts of losing those assets or interrupting those processes
- The types of threat intelligence that the security organization requires to protect assets and respond to emerging threats
- Priorities about what to protect
Once high-level intelligence needs are determined, an organization can formulate questions that channel the need for information into discrete requirements. For example, if a goal is to understand likely adversaries, one logical question would be, “Which threat actors on underground forums are actively soliciting data concerning our organization?”
2. Collection
Collection is the process of gathering information to address the most important intelligence requirements. Information gathering can occur organically through a variety of means, including:
- Pulling metadata and logs from internal networks and security devices
- Subscribing to threat data feeds from industry organizations and cybersecurity vendors
- Holding conversations and targeted interviews with knowledgeable sources
- Scanning open source news and blogs (a common OSINT practice)
- Scraping and harvesting websites and forums
- Infiltrating closed sources such as dark web forums
The data collected typically will be a combination of finished intelligence information, such as intelligence reports from cybersecurity experts and vendors, and raw data, like malware signatures or leaked credentials on a paste site.
3. Processing
Processing is the transformation of collected information into a format usable by the organization. Almost all raw data collected needs to be processed in some manner, whether by humans or machines. Different collection methods often require different means of processing. Human reports may need to be correlated and ranked, deconflicted, and checked.
An example might be extracting IP addresses from a security vendor’s report and adding them to a CSV file for importing to a security information and event management (SIEM) product. In a more technical area, processing might involve extracting indicators from an email, enriching them with other information, and then communicating with endpoint protection tools for automated blocking.
4. Analysis
Analysis is a human process that turns processed information into intelligence that can inform decisions. Depending on the circumstances, the decisions might involve whether to investigate potential emerging threats, what actions to take immediately to block an attack, how to strengthen security controls, or how much investment in additional security resources is justified.
The form in which the information is presented is especially important. It is useless and wasteful to collect and process information and then deliver it in a form that can’t be understood and used by the decision maker. For example, if you want to communicate with non-technical leaders, your report must:
- Be concise (a one-page memo or a handful of slides)
- Avoid confusing and overly technical terms and jargon
- Articulate the issues in business terms (such as direct and indirect costs and impact on reputation)
- Include a recommended course of action
Some intelligence may need to be delivered in a variety of formats for different audiences, say, by a live video feed or a PowerPoint presentation. Not all intelligence needs to be digested via a formal report. Successful cyber threat intelligence teams provide continual technical reporting to other security teams with external context around IOCs, malware, threat actors, vulnerabilities, and threat trends.
5. Dissemination
Dissemination involves getting the finished intelligence output to the places it needs to go. Most cybersecurity organizations have at least six teams that can benefit from threat intelligence.
For each of these audiences, you need to ask:
- What threat intelligence do they need, and how can external information support their activities?
- How should the intelligence be presented to make it easily understandable and actionable for that audience?
- How often should we provide updates and other information?
- Through what media should the intelligence be disseminated?
- How should we follow up if they have questions?
6. Feedback
We believe that it is critically important to understand your overall intelligence priorities and the requirements of the security teams that will be consuming the threat intelligence. Their needs guide all phases of the threat intelligence lifecycle and tell you:
- What types of data to collect
- How to process and enrich the data to turn it into useful information
- How to analyze the information and present it as actionable threat intelligence
- To whom each type of intelligence must be disseminated, how quickly it needs to be disseminated, and how fast to respond to questions
You need regular feedback to make sure you understand the requirements of each group, and to make adjustments as their requirements and priorities change.
Cyber Threat Intelligence Cycle FAQs
Why is the cyber threat intelligence cycle crucial for security teams?
The cyber threat intelligence cycle is pivotal for security teams as it provides a structured methodology to gather, analyze, and utilize threat intelligence. This cycle aids in understanding the threat landscape better, which in turn helps in preparing for and reacting to security threats efficiently. Through this cycle, actionable intelligence is generated which is instrumental in making informed decisions to bolster the organization's security posture against cyber attacks.
What are the main benefits of implementing a threat intelligence program?
Implementing a threat intelligence program empowers organizations with the capability to anticipate, prepare for, and mitigate potential security threats. This program is an integral part of the threat intelligence process, facilitating a deeper understanding of threat actors and their tactics. It thereby enables the threat intelligence team to deliver finished threat intelligence crucial for proactive defense measures. Moreover, a threat intelligence program enriches incident response strategies and fosters a culture of continuous learning and adaptation to the evolving threat landscape.
Which organizations benefit the most from the cyber threat intelligence cycle?
Organizations operating in sectors with high-value data such as finance, healthcare, and government are often prime targets for threat actors, hence they greatly benefit from the cyber threat intelligence cycle. This cycle, with its defined threat intelligence lifecycle stages, aids in intelligence collection and threat intelligence analysis, crucial for understanding and mitigating potential risks. Additionally, organizations with a significant online presence, businesses that focus heavily on uptime, or those subject to regulatory compliance also find the cyber threat intelligence cycle indispensable in navigating the complex security landscape.
What are the common challenges faced when implementing the cyber threat intelligence cycle?
The common challenges during implementation include the initial setup of a robust threat intelligence platform, ensuring continuous and relevant intelligence collection, and analyzing data accurately to generate actionable insights. The effectiveness of threat intelligence reports can be hindered by a lack of skilled personnel or inadequate resources. Furthermore, integrating the insights obtained from the threat intelligence analysis into the existing incident response procedures and ensuring a seamless flow of information can also pose significant challenges.
Get 'The Threat Intelligence Handbook'
There’s a lot more essential content in the full chapter of the book, including helpful diagrams, notes and tips on applying these explanations to your own effective threat intelligence program, and more detailed information on things like threat data.
To read the rest, download your full (and completely free) copy of “The Threat Intelligence Handbook” today.
This article was originally published Jan. 15, 2020, and last updated Feb. 5, 2024.
Related
