There has been speculation the cyber attacks on Swedish media were by Russia, but our analysis shows non-state hacker groups are more likely to blame.

Analysis Summary
- Non-state hacker groups are the most likely suspects behind the attacks on Swedish media companies on March 19, 2016.
- We’ve identified links between these attacks and hackers (and hacker groups) with a documented interest in bringing down Swedish sites.
- The Twitter account that warned about the attacks has a direct link to another account, which is related to a known DDoS tool.
On the evening of March 19, several large Swedish media houses were brought down by a time coordinated distributed denial-of-service (DDoS) attack. The targets included Expressen (expressen.se), Aftonbladet (aftonbladet.se), Dagens Nyheter (dn.se), Dagens Industri (di.se), Sydsvenskan (sydsvenskan.se), and Helsingborgs Dagblad (hd.se).
There has been speculation these attacks were made by Russia, but our analysis shows non-state hacker groups with no political agenda are more likely suspects — since they have performed similar attacks during the last few months and we have not seen any evidence that these recent attacks are beyond their capabilities.
A warning was sent on Twitter earlier in the day, from an account with no previous activity:
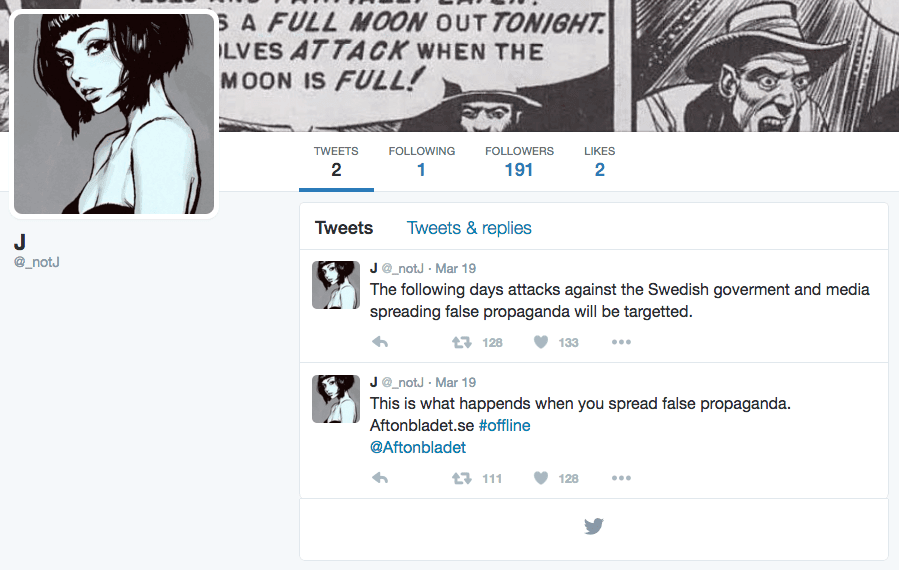
The two misspellings “targetted” and “happends” are likely an indication this is not a native English speaker. However, our data set implies those spelling mistakes are quite common.
There are 1,853 tweets in the Recorded Future index with the word “happends” and 13,989 with “targetted,” so this is not necessarily a mistake that indicates attribution beyond non-English native speakers.
The @_notJ account follows one single other account on Twitter:
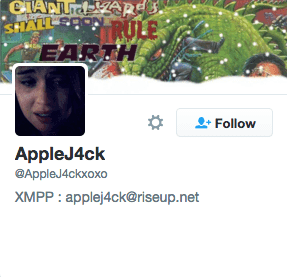
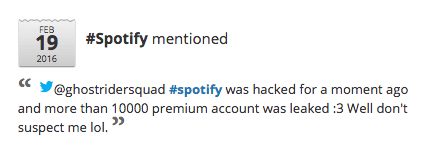
Recent interesting tweets from this account that relate to cyber attacks include:
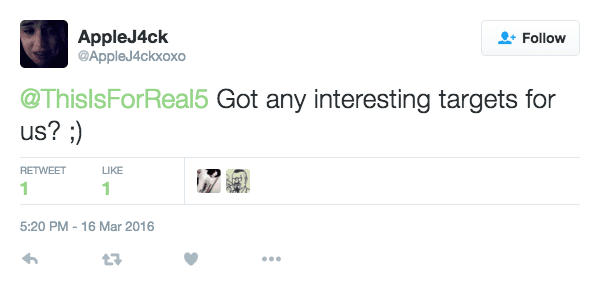
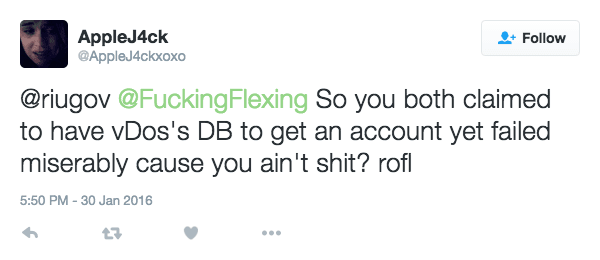
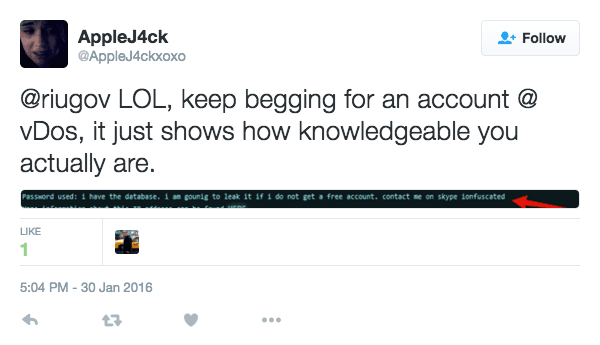
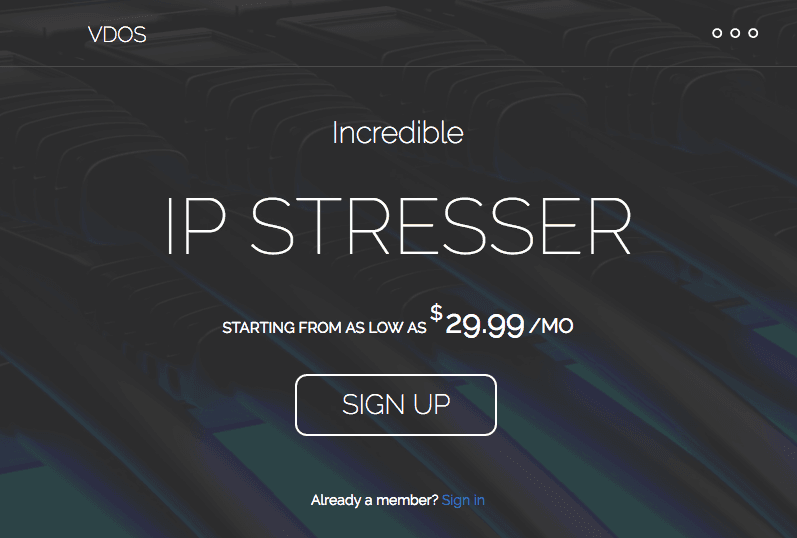
vDos is an IP stresser tool that could potentially be used in DDoS attacks. And, according to a Arbor Networks report “Attack of the Shuriken 2015: Many Hands, Many Weapons,” AppleJ4ck appears to have been one of the operators of vDos: _“The VDos service appears to be or has been operated by ‘P1st’ (a.k.a. ‘P1st0’) and ‘Apple J4ck,’ with ‘Red Sox’ and ‘jeremyfgt’ apparently joining the team at a later date.”
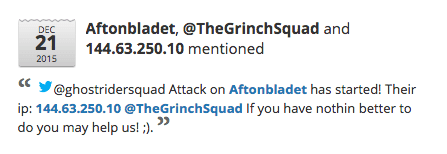
Looking into Recorded Future for previous attacks against these Swedish media companies, we find the following tweet from December 21, 2015:
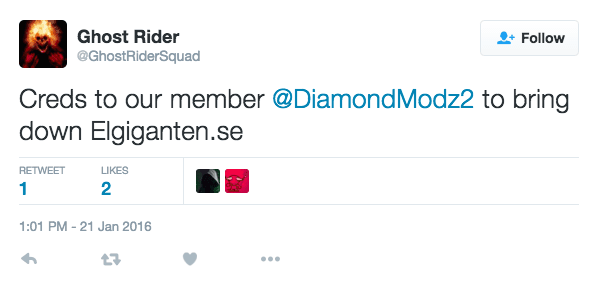
The same group, GhostRiderSquad, has also shown interest in (and hacked) other Swedish-based companies:
All the accounts mentioned here are part of a network of hackers/hacker groups, that follow each other and refer to each other’s work in different ways:

As a curiosity, there was a question posted on the Swedish site Flashback only an hour before the attacks started, discussing how to take down a couple of the sites that were actually affected — but this appears to just be (un)fortunate timing by someone!

What Can We Learn From This?
There are several pieces of evidence pointing towards hacker networks and individuals. Some of them (GhostriderSquad) appear to have participated in the Anonymous #OpISIS attacks on ISIS, but apart from that there’s no immediate evidence of any political engagement that would explain the attacks on Swedish media houses.
Rather, this could be just a “show off” activity — “just for the lulz,” as hackers like to call it. On the other hand, the apparent ease with which a large number of media companies could be brought down shows that other attackers could do the same — and seriously limit citizens’ access to current news.
For defenders, these events serve as a reminder that threat intelligence is necessary to be prepared for attacks like this.
The tweet above about emerging attacks on Aftonbladet shows how early warnings are sometimes available, even if it’s far from certain that any advance warning is given.
Therefore, real-time monitoring of critical systems must be in place. Also, there must be procedures for defending the network perimeter should an attack occur — and how to work with relevant ISPs to limit traffic originating from the attack.
In summary, we recommend media companies invest in:
- Monitoring the Web in real time for threats.
- Baseline DDoS protection.
- Ability to adapt network profile based on attacks.
- Learning from other industries that have sustained DDoS attacks (e.g., financial services).
Further Analysis
Based on open source intelligence we can hypothesize that non-state hacker groups were behind these attacks, and not Russia as other sources have suggested. With access to information about what IP addresses have been active in the attacks, we could use other open sources to tie these addresses to malicious infrastructures and actors known to use these resources.
Related