Session Hijacking and MFA Bypass


Cookie theft, also known as a “pass-the-cookie” attack, occurs when threat actors hijack a victim’s session cookies, which are often valid for an extended period of time, even when the application is not being actively used. This is often done through the use of infostealer malware. This report covers the criminal underground ecosystem that is focused on stealing, selling, and using cookies and credentials compromised with infostealer malware.
This year, we saw a new threat from a cybercriminal group, Lapsus$ Group, that made its way onto the FBI's most-wanted list in March 2022. While most of its attack vectors are well covered by security researchers, one stands out: identities compromised with Infostealer Malware.
In most cases when the infection goes unnoticed, this type of malware obtains credentials saved in victims’ browsers. Hours, days, or sometimes even years after the initial infection, credentials to either your corporate or personal infrastructure are obtained and used by threat actors. Threat actors seamlessly hijack your sessions and remain undetected, appearing identical to you or one of your employees.
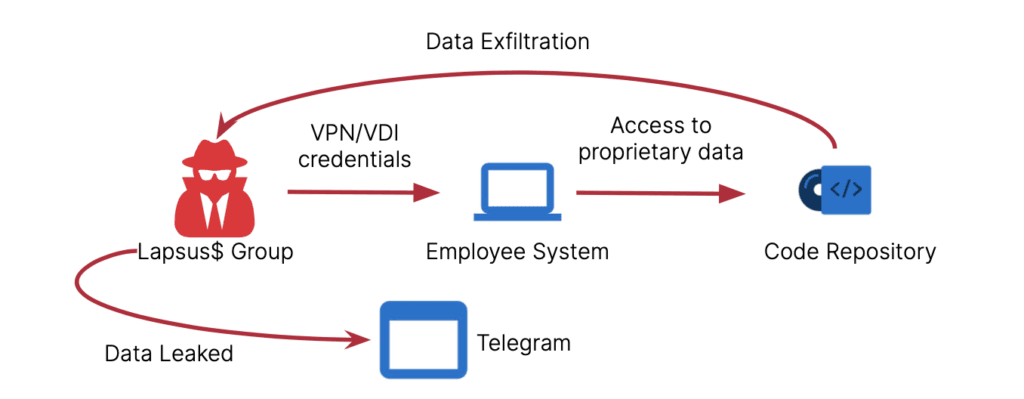 Figure 1: Criminal workflow for Lapsus$ Group (Source: Recorded Future)
Figure 1: Criminal workflow for Lapsus$ Group (Source: Recorded Future)
HTTP Cookies
HTTP cookies are mainly used to manage user sessions, store user personalization preferences, and track user behavior. They are also the cause of all of those annoying "this page uses cookies" consent forms seen across the web.
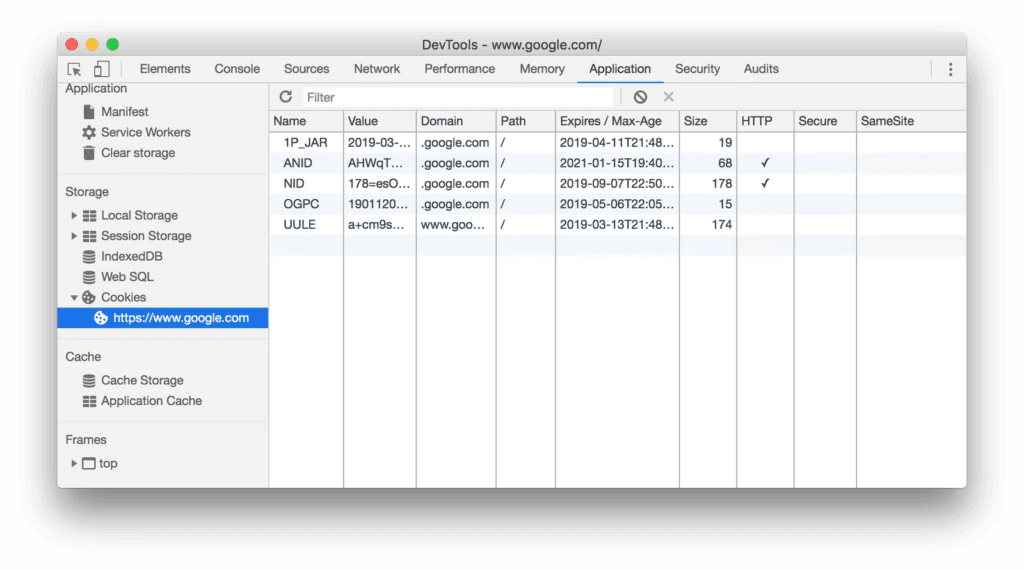 Figure 2: Chrome browser DevTools list of stored cookies (Source: Google)
Figure 2: Chrome browser DevTools list of stored cookies (Source: Google)
Session hijacking, also known as cookie hijacking, is the exploitation of a valid computer session, sometimes also called a session key, to gain unauthorized access to information or services in a computer system. In particular, it is used to refer to the theft of a magic cookie used to authenticate a user to a remote server. It has particular relevance to web developers, as the HTTP cookies used to maintain a session on many websites can be easily stolen by an attacker using an intermediary computer or with access to the saved cookies on the victim's computer. After successfully stealing appropriate session cookies, an adversary might use the pass-the-cookie technique to perform session hijacking.
Among other things, cybercriminals can use stolen sessions to authenticate to web applications and services, allowing them to bypass multi-factor authentication (MFA) checkpoints. With the increasing adoption of MFA across enterprises, the technique has recently been on the upswing with attackers, with the Cybersecurity and Infrastructure Security Agency (CISA) in January 2021 warning of a surge in cookie theft attacks.
As researchers point out, Once the threat actor had a Chrome cookies file from a user that had already passed an MFA challenge recently (for example, a timeout was 24 hours), they decrypted the cookies file using the user’s DPAPI key. The cookies were then added to a new session using a “Cookie Editor” Chrome extension that the threat actor installed on victim systems and removed after use.
Genesis Store
Genesis Store is a criminal shop created by the threat actor “GenesisStore” in 2018. The store is advertised across multiple Russian- and English-language underground forums. Genesis Store sells packages of compromised account credentials and associated user data designed to allow threat actors to bypass anti-fraud solutions.
Victim data is sold in a single package referred to as a "bot", or “log”, which includes account credentials, IP address, browser fingerprint (system information), and cookies. After purchasing a bot, the victim data can be imported into a browser plugin called Genesis Security, allowing the attacker to masquerade as the victim to perform account takeover and session hijacking attacks. The price for each bot varies depending on the amount of account credentials, types of accounts, and geographical location of the victim.
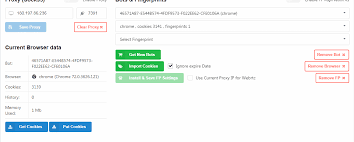 Figure 3: Import cookies with the Chrome browser plugin “Genesis Security” (Source: Genesis Store)
Figure 3: Import cookies with the Chrome browser plugin “Genesis Security” (Source: Genesis Store)
Initial Access Brokers
Multiple prolific criminals specialize in selling access to corporate and government networks on criminal underground forums, such as the high-tier forums Exploit and XSS. They have several ways to get valid credential pairs (T1078) for sale. Threat actors exploit public-facing applications (T1190), attack external remote services (T1133), and leverage brute force techniques (T1110).
For example, “Crasty_bro”, an initial access broker (IAB) on XSS Forum, parses stealer malware logs for VPN, RDWeb, Citrix credentials, using specific patterns (known parts of the login URL).
After the credentials are validated, Crasty_bro sells them publicly on high-tier criminal underground forums, such as XSS or Exploit, to ransomware operators and their affiliates. If the access to the network requires MFA, Crasty_bro will check if the stealer captured the cookie with a valid access token, and will import the cookie to the browser before the login attempt.
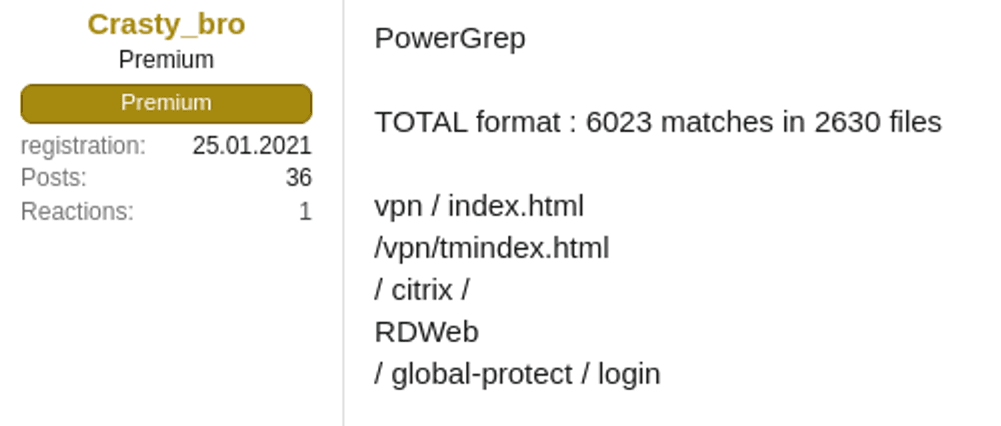 Figure 4: Crasty_bro selling valid network access credentials (Source: XSS Forum)
Figure 4: Crasty_bro selling valid network access credentials (Source: XSS Forum)
Mitigation strategies against infostealer malware include the following:
- Configure intrusion detection systems (IDS), intrusion prevention systems (IPS), or any network defense mechanisms in place to alert on any malicious activity with YARA rules and Hunting Packages available in the Recorded Future Platform.
- The Recorded Future Identity Intelligence module can assist with the detection of credential information compromised by infostealer malware.
- Keep all systems current with the latest security patches and updates.
- Explore possible solutions to enforce MFA for every user session.
Conclusions
The Recorded Future Platform identified 14,905 references to criminal underground posts in the past year which include the keywords “cookies”, “session cookies”, “session hijacking”. As it is illustrated in Figure 5 below, there is a steady increase in the number of references from April 2021 to April 2022. This indicates an increase of interest to the aforementioned attack techniques as well as an increase in the number of threat actors interested in or using underground services, such as malware-as-a-service (MaaS) variants RedLine and Vidar, to obtain valid credential pairs with session tokens.
This will result in an increased number of compromised identities with a consequent increase in ransomware attacks, data breaches, and significant leaks.
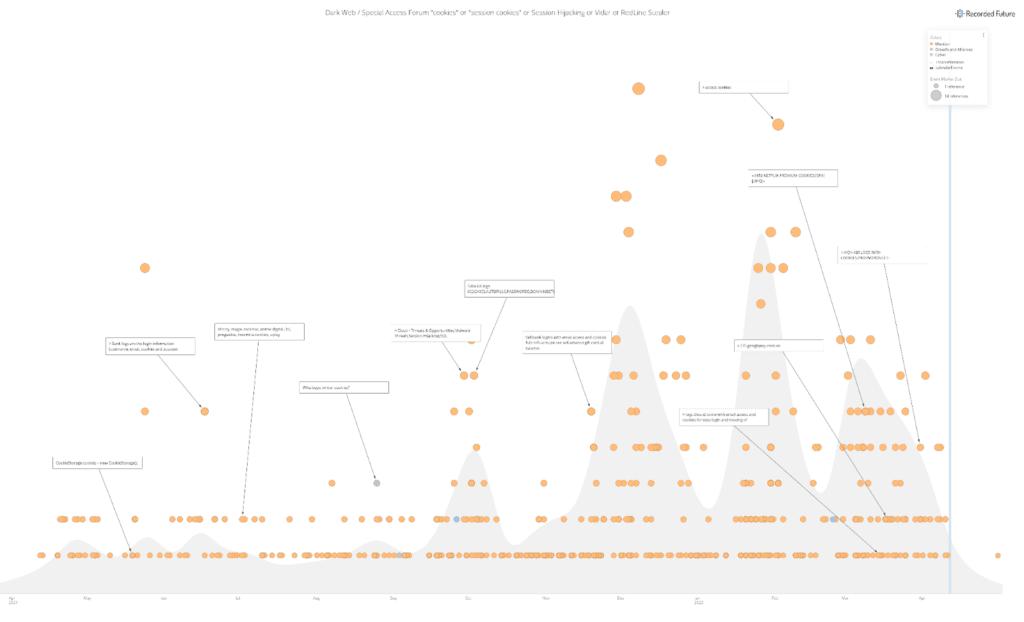 Figure 5: Recorded Future graph illustrating the timeline of references in the past year (Source: Recorded Future)
Figure 5: Recorded Future graph illustrating the timeline of references in the past year (Source: Recorded Future)
Related