Discovering Sandworm IOCs With Recorded Future Maltego Transforms
Webinar: How to use Maltego for better insight into cyber threats. Watch now.
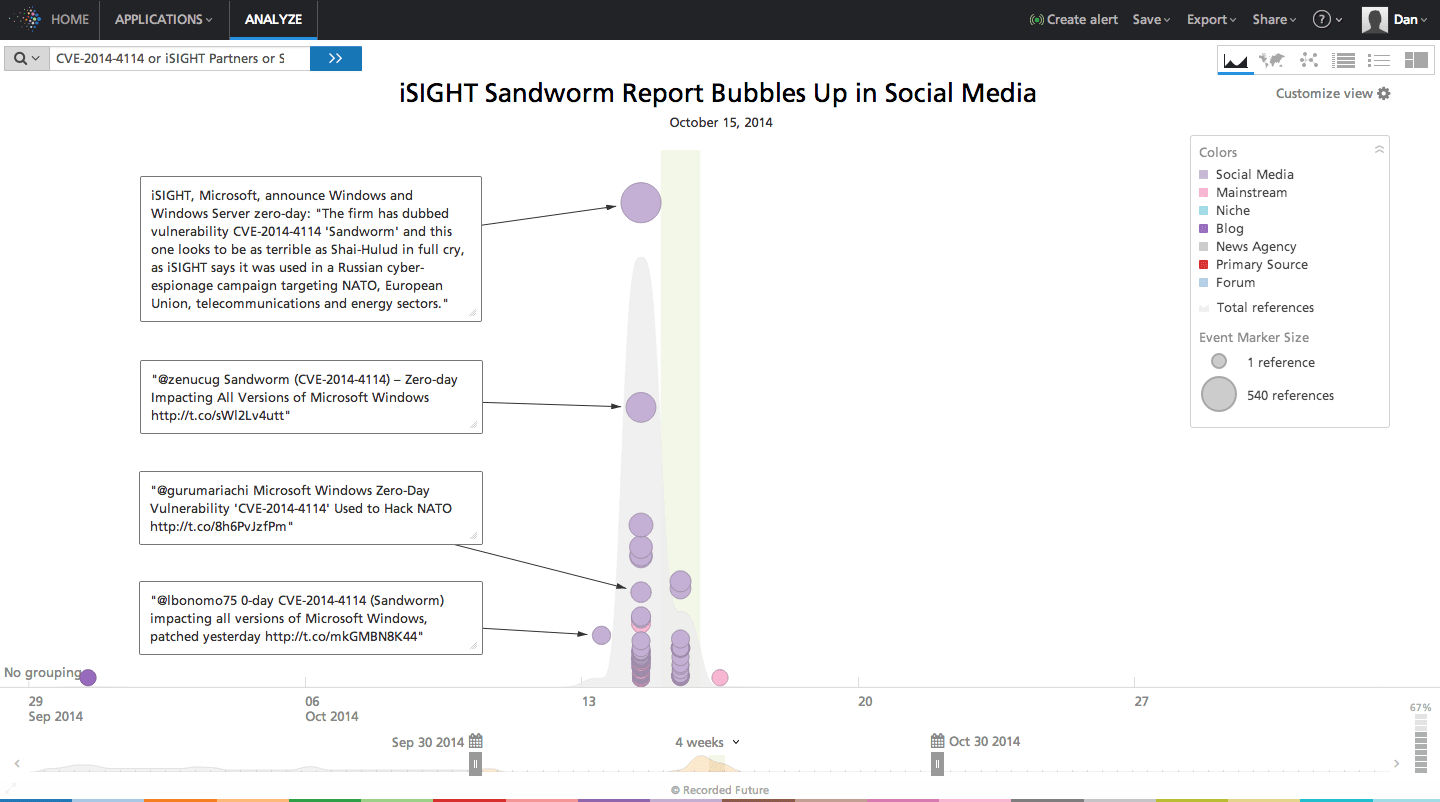
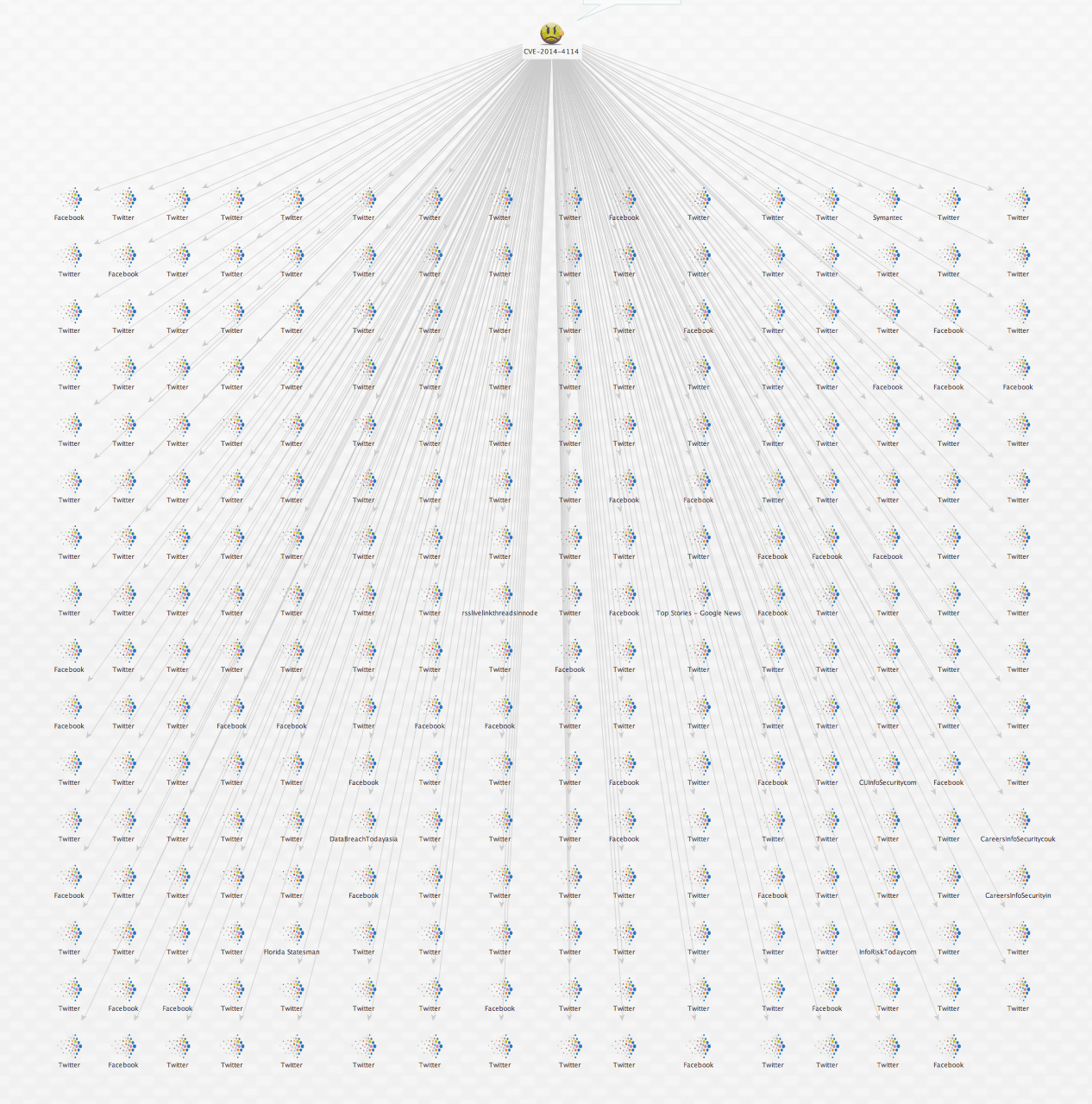
Yesterday, iSIGHT Partners published a blog post announcing the discovery of CVE-2014-4114, a zero-day vulnerability used in a Russian cyber-espionage campaign. The campaign was dubbed Sandworm and it’s getting a ton of attention via social media as seen in the Recorded Future timeline below.
I recently outlined how to use Recorded Future Maltego transforms to discover indicators of compromise (IOCs) from OSINT so I decided to analyze the Sandworm vulnerability with a similar approach.
Step-by-Step Outline
First, I search for the single vulnerability entity (CVE-2014-4114) mentioned in the iSIGHT report.
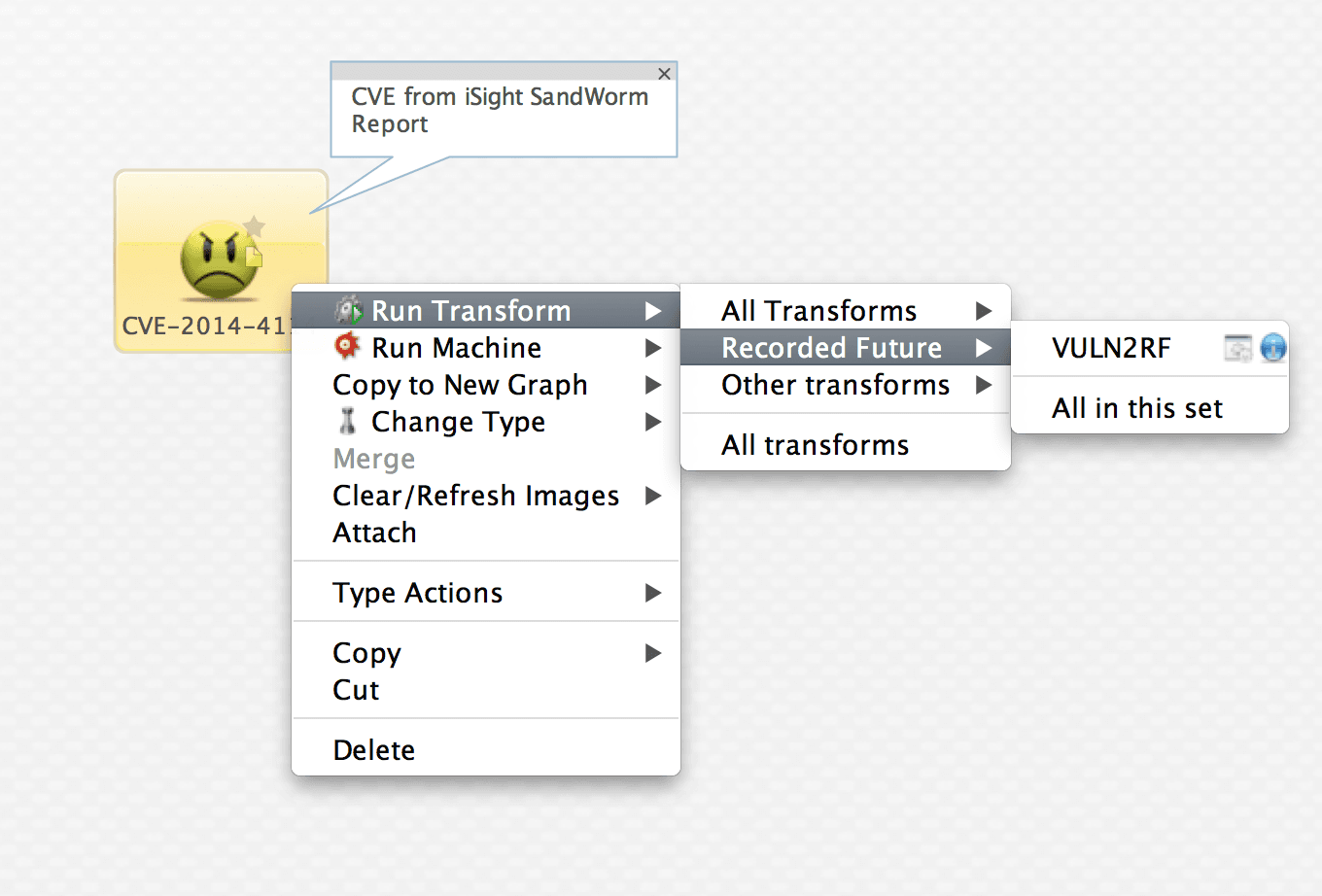
Then I run our VULN2RF transform to see what Recorded Future “knows” about this CVE.
As expected, I get high recall on this query in Recorded Future. So for the purpose of this example, I’ll set my Maltego slider value to 255 in order to limit the number of Recorded Future entities returned in my graph.
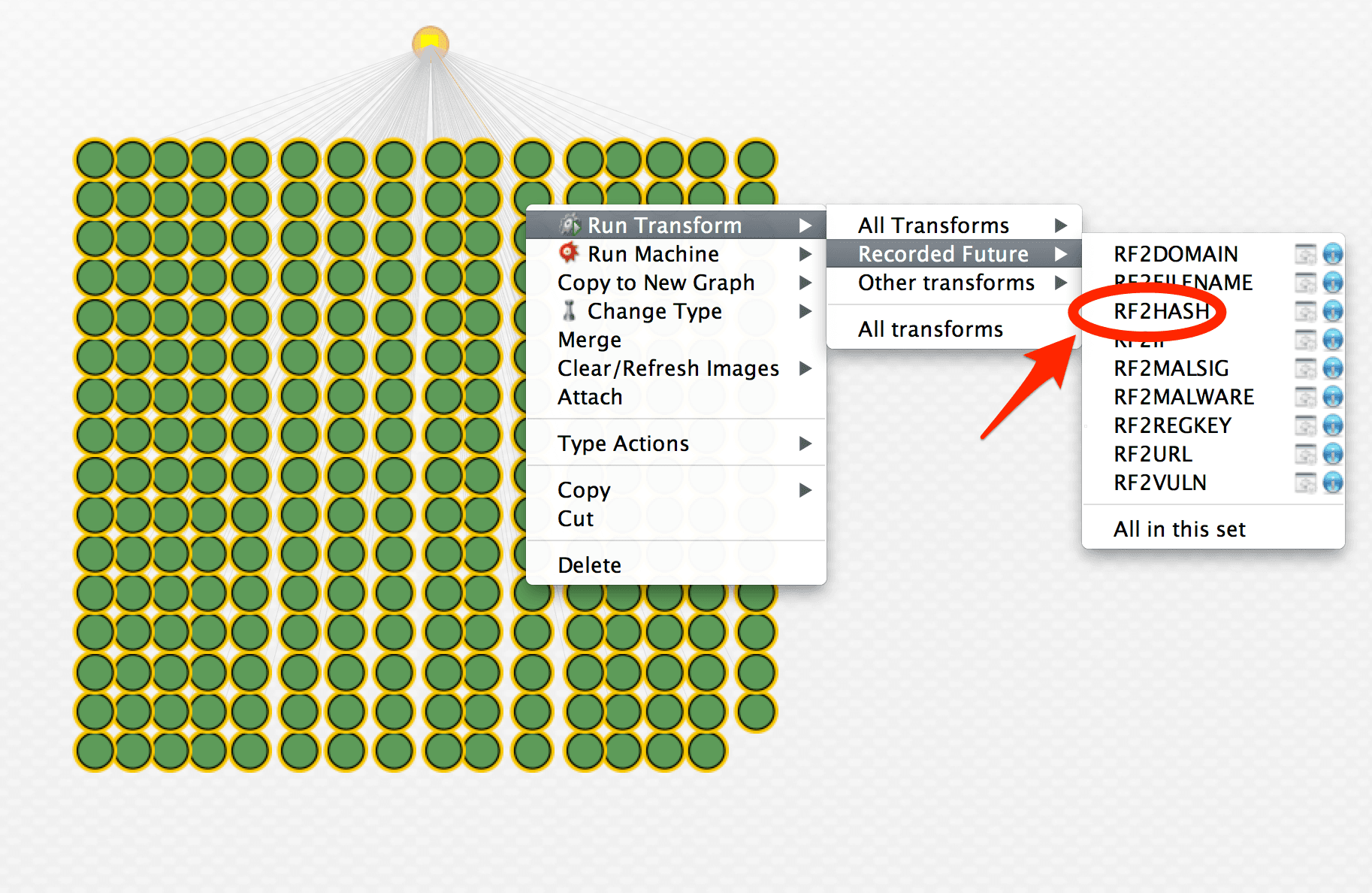
Now that I have a nice set of Recorded Future entities to work with, my next step is to hunt for IOCs. So I don’t flood my graph, I first search for hash values associated with malicious executables being used in the Sandworm campaign. To do that I run my RF2HASH transform.
Within seconds, I see a hash entity returned in my graph. It appears to be extracted from several tweets published today.
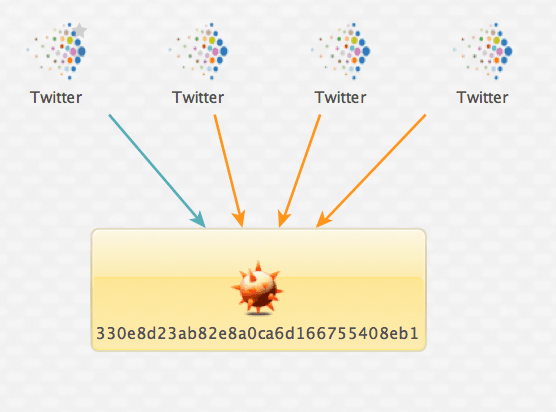
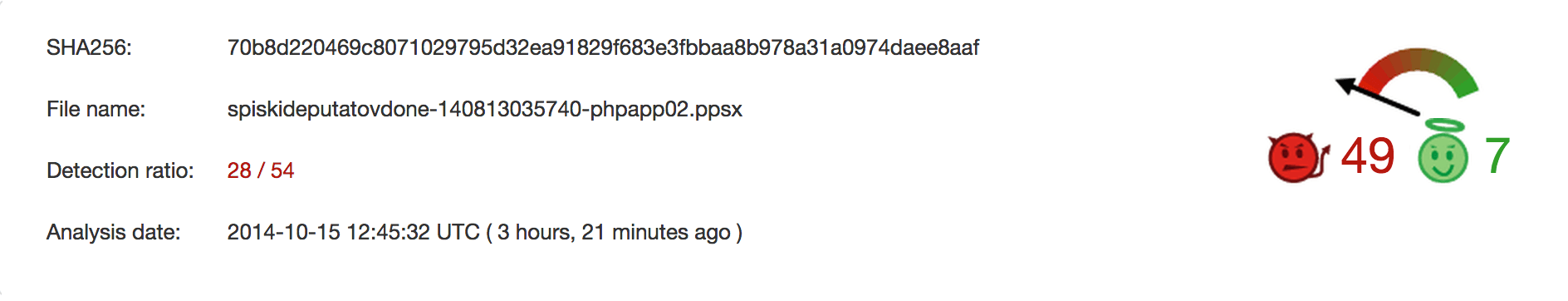
To validate this hash is relevant to my investigation, I quickly confirmed with VirusTotal the hash is in fact malicious.
Note: The hash was just analyzed three hours ago from the time I ran the query indicating the potential for this to be a fresh IOC that others may not be paying attention to yet.
Now I want to actually view one of the tweets that contained the hash. I can do this from within Maltego.
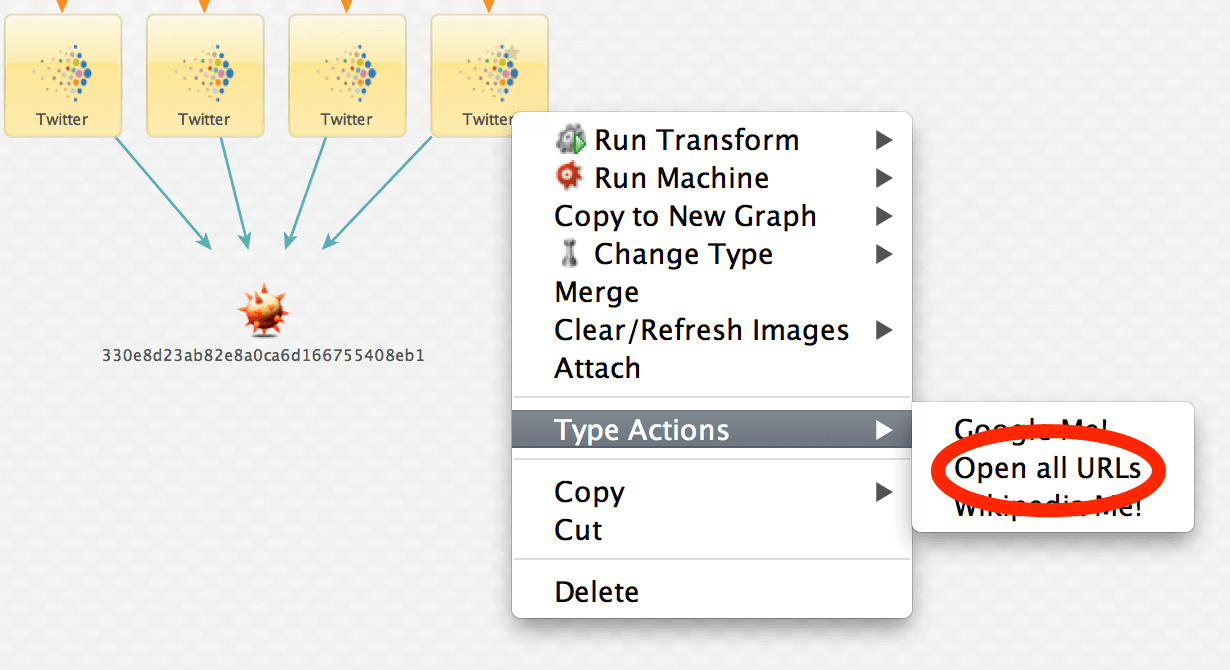
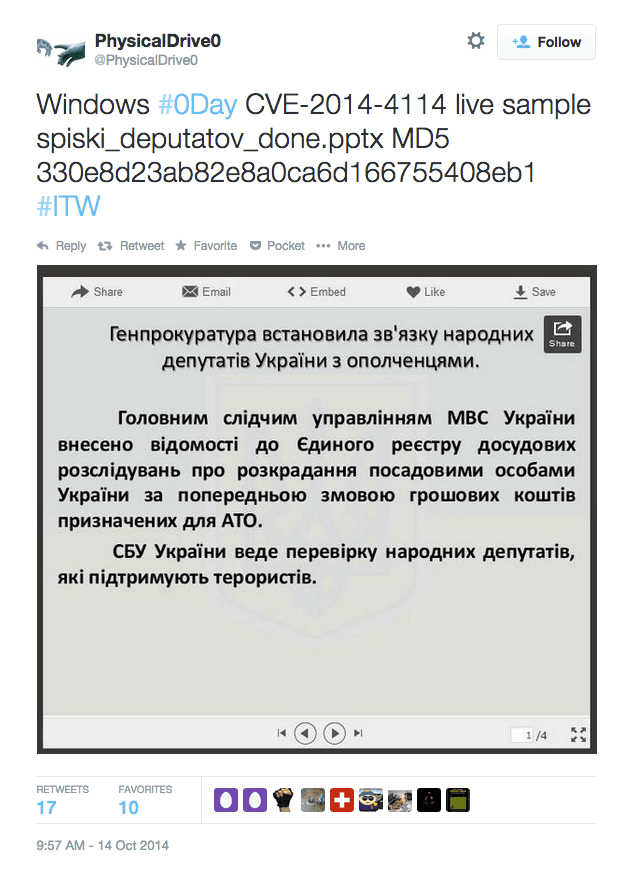
I find an interesting tweet referring to the hash. The tweet confirms its association with the CVE and the Twitter user claims to have a live sample of malicious code along with an embedded PowerPoint presentation written in Ukrainian language.
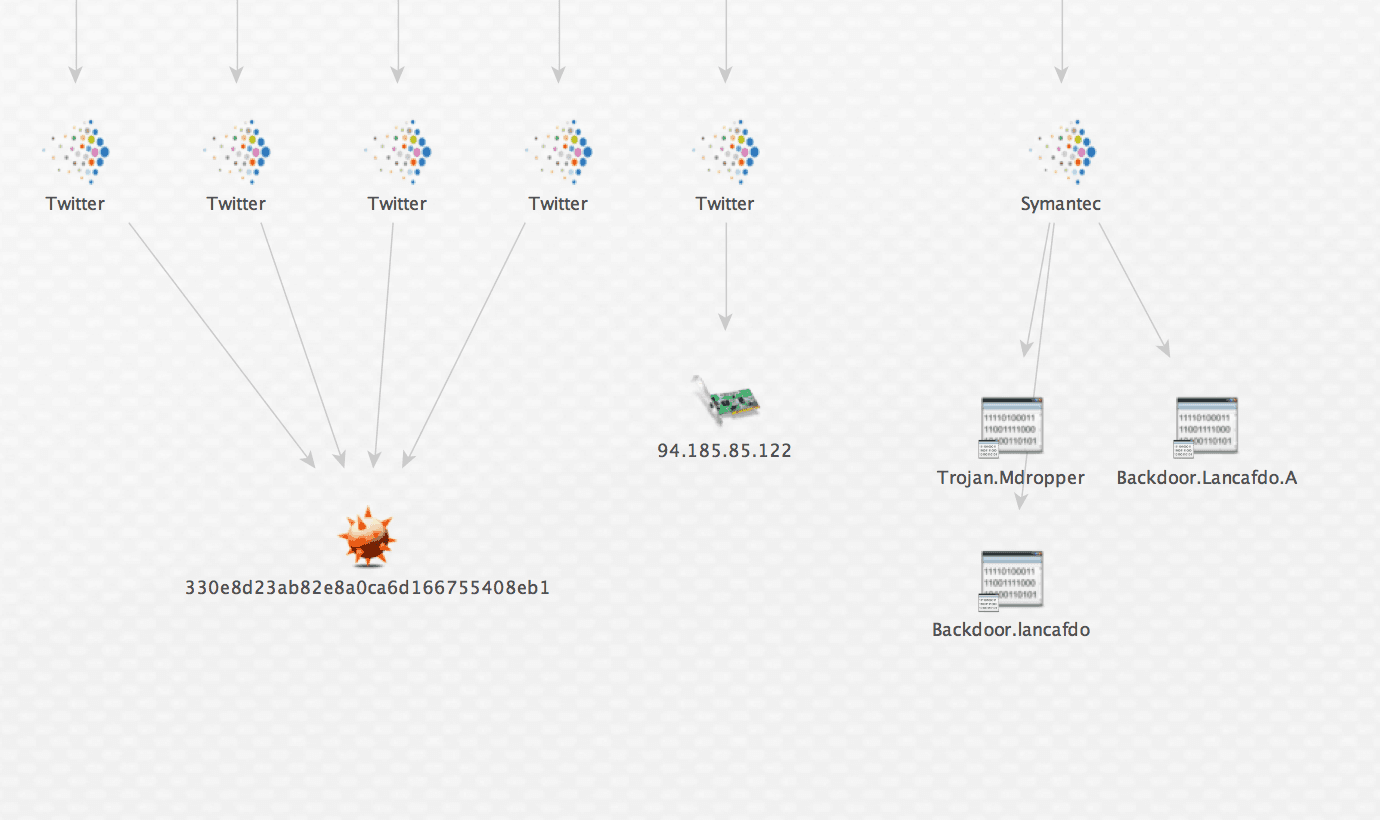
My next step is to see if I can extract from Recorded Future any known malware signatures associated with this campaign. I use the RF2MALSIG transform to do this.
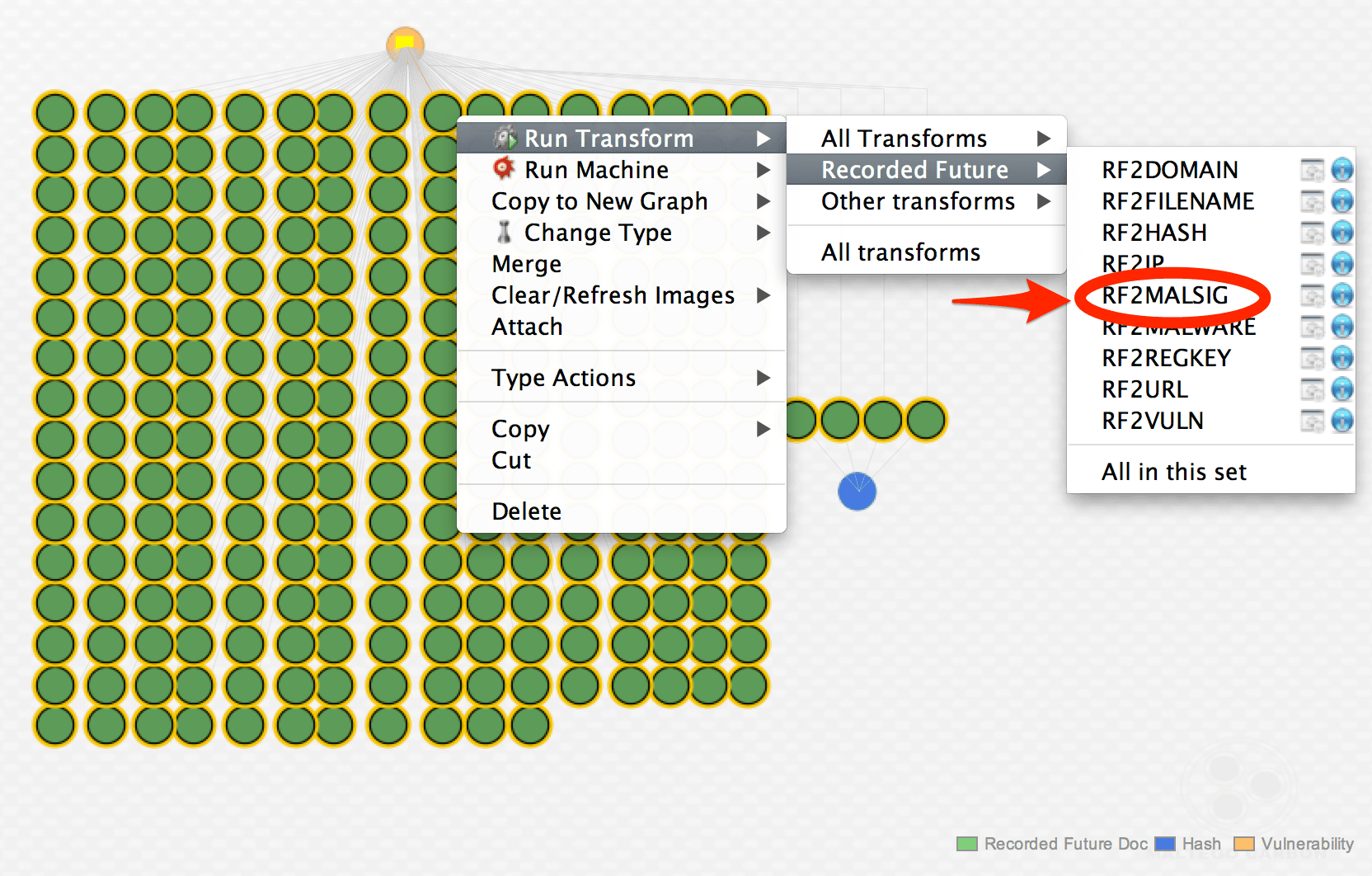
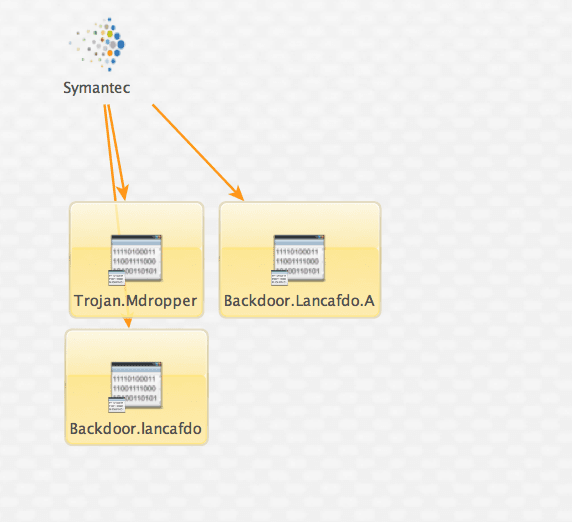
The transform returns three signatures.
Note: There are probably more but we limited our slider value to 255, so bear in mind this is a sample set of data for the purpose of this example.
Next, I would like to see if I can extract any known C&C or other malicious IP addresses. To do this I run the RF2IP transform.
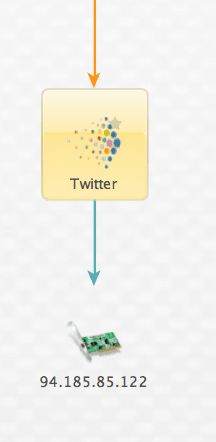
Next, I want to validate the IP address from the tweet using a simple VirusTotal query and, sure enough, I observe it has been associated with malicious activity as recently as this morning! Possibly a C2?
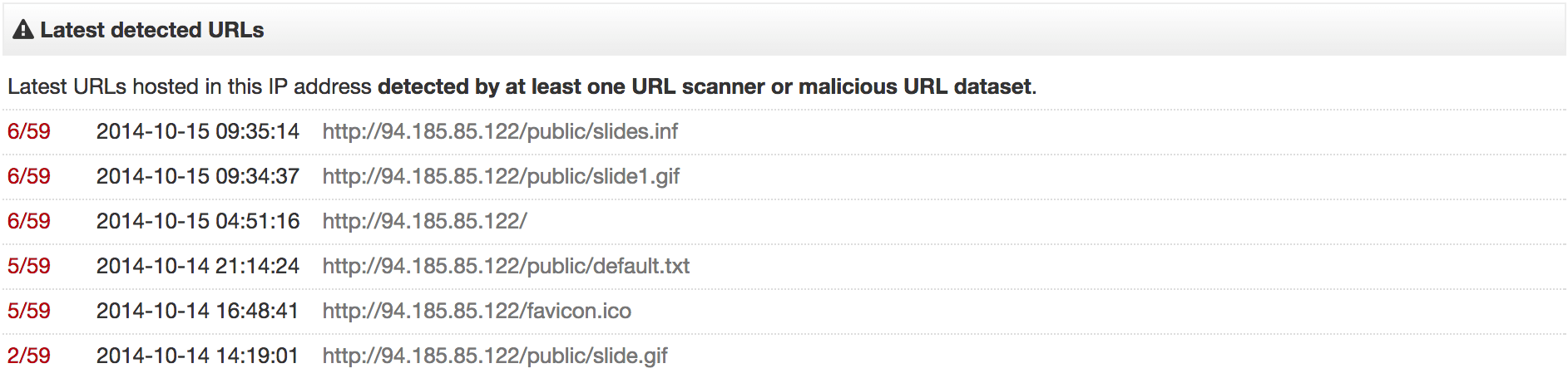
Zooming in, we find some great indicators for a story that’s just breaking today. I’m sure more IOCs will soon start popping up and I only need to re-run my Recorded Future transforms to discover them.
So as with any Maltego investigation, we could continue running transforms and expanding our graph. For the purpose of this outline, we’ll stop here since I have enough information to execute some proactive measures in my security operation. Having done my research in Maltego I can now put together a timeline in Recorded Future referencing the IOCs I found.
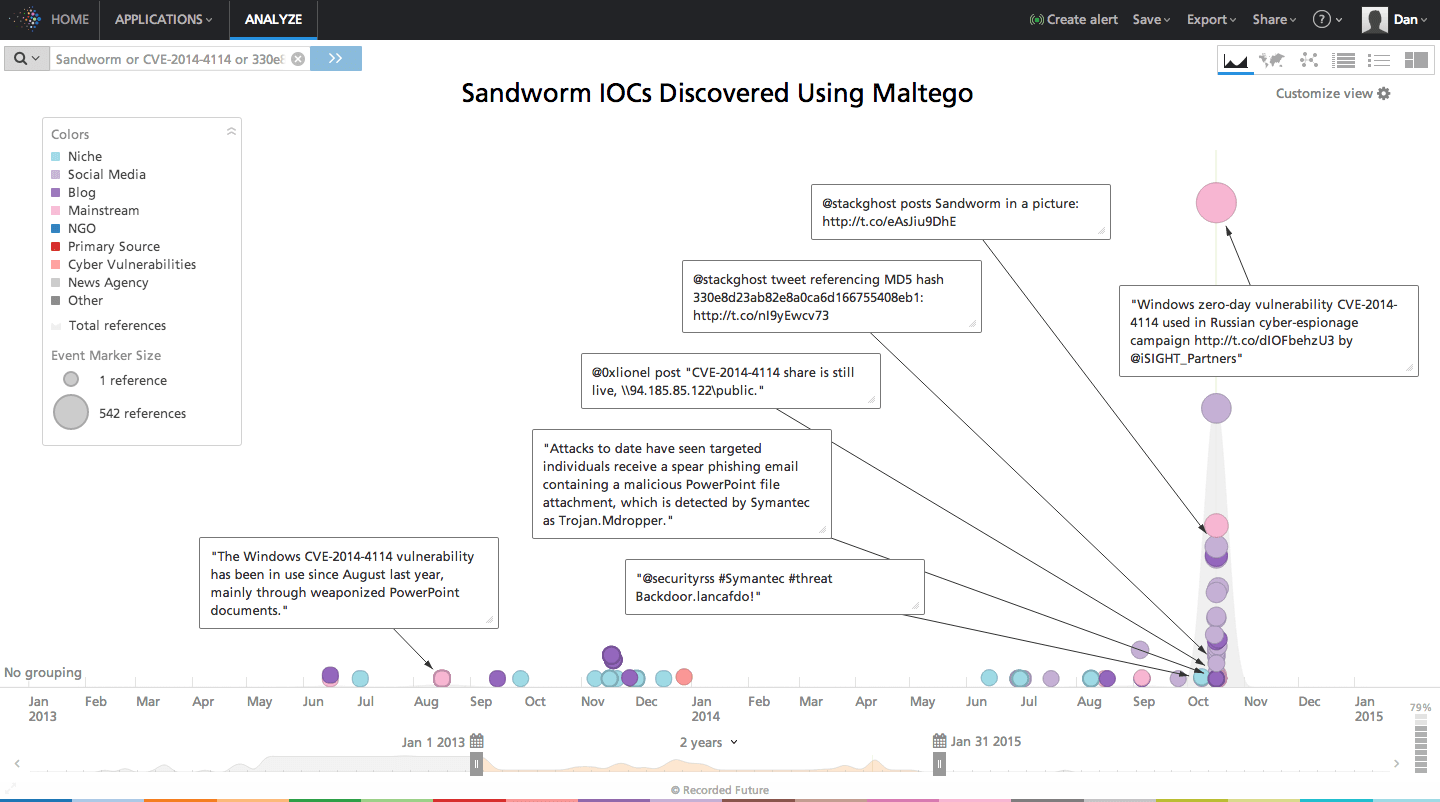
So what are my next steps?
- I have a few IOCs I can use to create detection content in my SIEM or other network security monitoring platforms.
- I can use these IOCs as search criteria internally against my logs or packets to see if I find any indication Sandworm has infected my network.
- I have one known bad IP address (so bad it was apparently removed from Twitter) I can immediately block.
- I can plug in the IOCs I discovered to my additional third-party or homegrown Maltego transforms and continue my analysis.
This table summarizes the relevant IOCs I was able to extract in just a few clicks.
| Hash | 330e8d23ab82e8a0ca6d166755408eb1 |
|---|---|
| IP Address | 94[.]185[.]85[.]122 |
| Malware Signatures | Trojan.Mdropper, Backdoor.Lancafdo.A |
Warning: Do not click or connect directly to this IP.
Happy hunting!
See These Maltego Transforms in Action
I recently presented a live demo of the Maltego transforms used in this analysis. I encourage you to grab the recording and watch firsthand how public Web sources can help you uncover IOCs.
Related