String of Baffling Arrests Shakes Cyber Division of FSB
On January 12, 2017, several prominent Russian media outlets reported the imminent dismissal of Andrei Gerasimov, the head of the Federal Security Bureau’s (FSB) Information Security Center (ISC). ISC is tasked with safeguarding Russia’s information security and the investigation of high-profile computer crimes.
It operates under FSB’s counterintelligence unit. Based on publicly available sources, Andrei Gerasimov was the head of ISC beginning in 2009 and was due to retire soon.
Gerasimov’s departure coincided with public accusations made by the U.S. Intelligence community. According to these claims, Russian security services orchestrated the hacking attacks against the Democratic National Committee (DNC) and the U.S. election cycle, all under the personal supervision of Vladimir Putin. Analysts recognize Gerasimov as a necessary political sacrifice to please the new administration and to put hacking rumors to rest.
However, development of this story in recent weeks saw the most bizarre and unforeseen turn of events. It came to light this week that in early December 2016, following an inquiry by the FSB Internal Affairs unit, Sergei Mikhailov, colonel and deputy chief at the ISC, was arrested on charges of treason. He is being held at the Lefortovo pretrial detention center, and stands accused of receiving money from a “foreign organization,” facing trial by military tribunal.
Regarded by many as the “gray cardinal” and informal curator of the cyber security and e-commerce industry in Russia, the arrest of Mikhailov in the middle of an ongoing FSB board meeting and his escorting by authorities in plain sight with a sack over his head was clearly intended to send a statement.
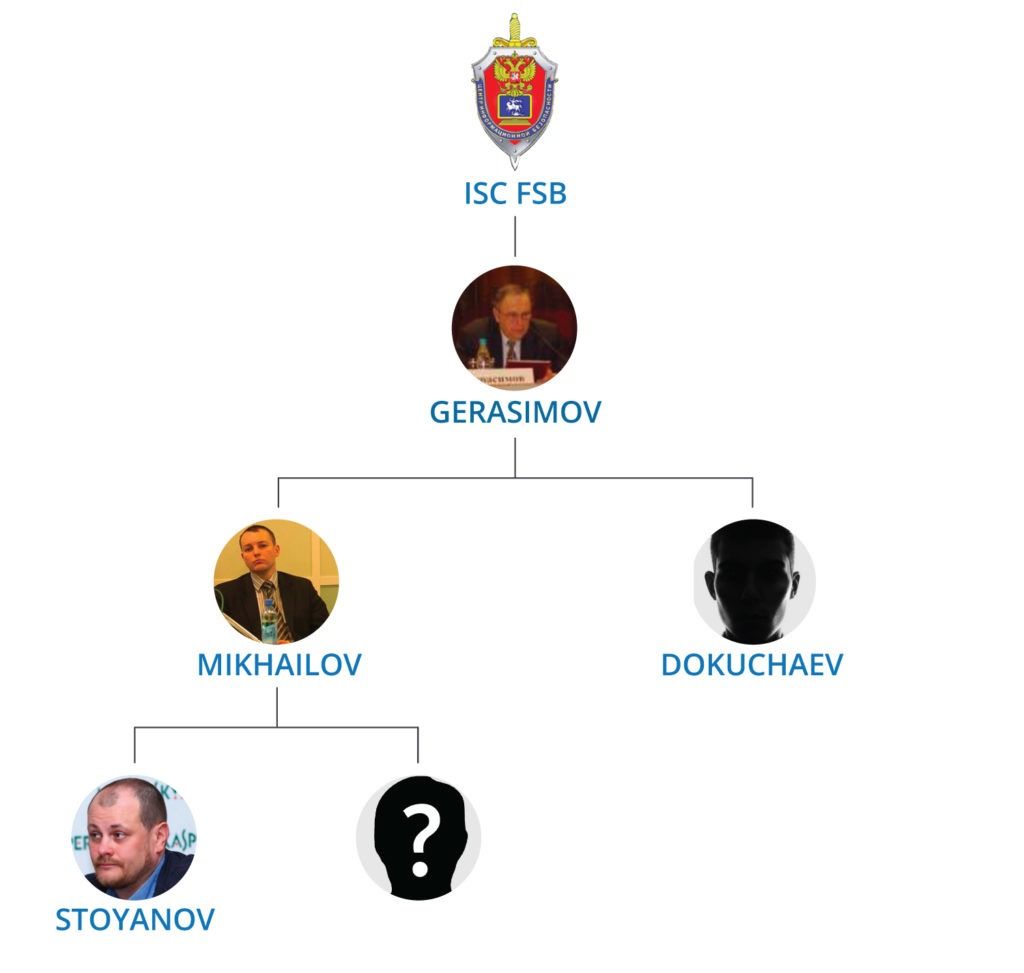
In addition to Mikhailov’s detention, the head of cyber crime investigations at Russia’s Kaspersky Labs, Ruslan Stoyanov, was arrested on similar charges. Stoyanov had previously served as a major in the Office of Special Technical Measures at the Ministry of Internal Affairs.
A well-known and respected researcher in the security community, it’s alleged he acted as a middleman and mediator in a funds transfer between unknown foreign organizations and Sergei Mikhailov. Stoyanov could also be tried under Russian treason law which carries a sentence of up to twenty years in prison.
The latest available information suggests that at least two more people were arrested during this investigation. One is Dmitry Dokuchaev, another operative at ISC, and a direct subordinate of Sergei Mikhailov. The identity of the fourth person remains unknown.
Unconfirmed reports suggest that prior to his arrest Mikhailov unsuccessfully attempted to convince senior management at a leading bank in Russia to provide ISC direct access to its customer base. The agency had plans to use this in an ongoing big data analysis and monitoring project. Further speculation points to the collaboration of both men in the creation of a “super-trojan” with the agenda of infiltrating Russian banking organizations for clandestine monitoring of financial transactions and hidden data aggregation.

The most controversial theory claims Mikhailov had personal involvement or even direct patronage of the “Shaltay Boltay” hacking collective also known as Anonymous International.
The Boltay group became famous for leaking highly sensitive documents belonging to the most senior public officials and prominent businessman in Russia. These leaks included private correspondence of Dmitry Medvedev and the case has been actively investigated by law enforcement for several years. Coincidentally, despite the previous history of regular Twitter activity and blog updates, the latest messages from this profile were posted on December 12, 2016, only one week after the arrest of Mikhailov and Stoyanov.
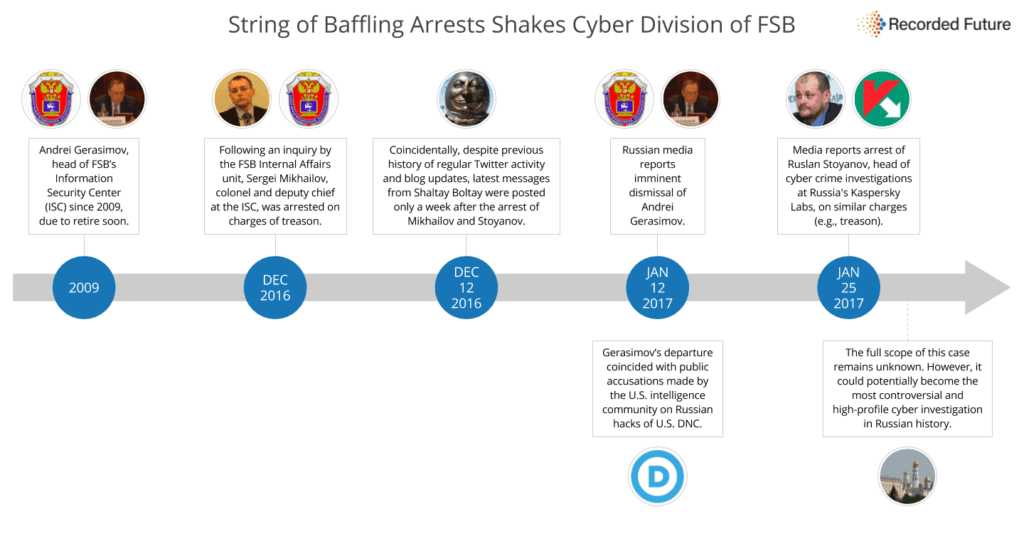
The full scope of this case remains unknown; however, it could potentially become the most controversial and high-profile cyber investigation in Russian history.
Related
