Partner Spotlight: Get Extensive File Reputation Intelligence With ReversingLabs
Hunt malware faster and improve signature development with ReversingLabs and Recorded Future.
Editor’s Note
This is part of a series of blog posts on useful “all-source analysis” research and collaborative approaches using Recorded Future and our OMNI Intelligence Partners.
Summary
ReversingLabs’s File Reputation Service and deep content inspection data can be accessed via an extension built into Recorded Future Intelligence Cards™. This enables security operations center (SOC) and threat intelligence analysts to rapidly gain insight into critical file-based threats identified by Recorded Future.
Challenge
Organizations are being attacked by skilled and well-resourced adversaries who rapidly morph their techniques to hide their intent and actions. Often, known malicious payloads are reused with slight modifications to bypass even the best AV and dynamic analysis tools.
It’s no longer adequate to merely inspect, analyze, and act on some inbound network traffic, or to quarantine a subset of traffic for dynamic analysis: the inbound flow is too strong as attackers continue to evolve, enhancing and increasing attack frequency to evade existing protections.
Solution
Businesses need to regularly “tune” their defenses and prepare for what could be coming based on reliable threat intelligence. In particular, organizations need to collect all unknown and malicious payloads to enable continuous incident response readiness; this allows them to unlock their SOC team’s capability to write signatures against zero-day threats before any other vendor solution detects them. ReversingLabs collects and processes millions of files a day to build and maintain the largest commercially available private File Reputation Repository of over 3 billion unique goodware and malware samples. Each sample is regularly analyzed/reanalyzed to provide over 3,000 metadata fields of actionable information.
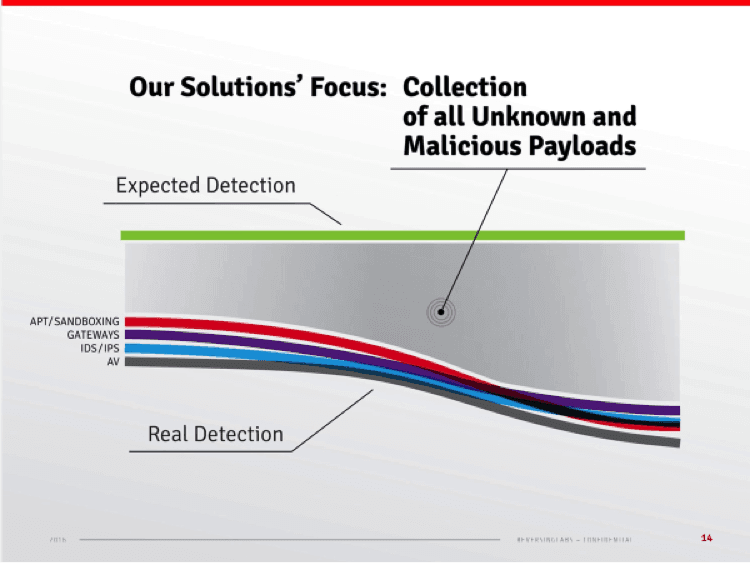
ReversingLabs’s collection exceeds typical standard malware analysis.
With their Recorded Future integration, analysts can quickly check whether ReversingLabs has any information related to an IP address, domain, or hash. In the case of IP address and domain searches, the lookup to ReversingLabs will reveal hashes that are related, and from there you can easily pivot to a Hash Card for more information. On hash queries, the ReversingLabs lookup provides a rich set of file reputation data.
| Intelligence Card™ | Extension |
|---|---|
| IP Address | Available |
| Domain | Available |
| Hash | Available |
Example
As part of a recent Recorded Future alert for a new RAT controller host IP (see analysis described in this blog post), the domain shadows.sytes[.]net was identified. Inspecting the Intelligence Card™ for this domain revealed a suspicious MD5 hash.
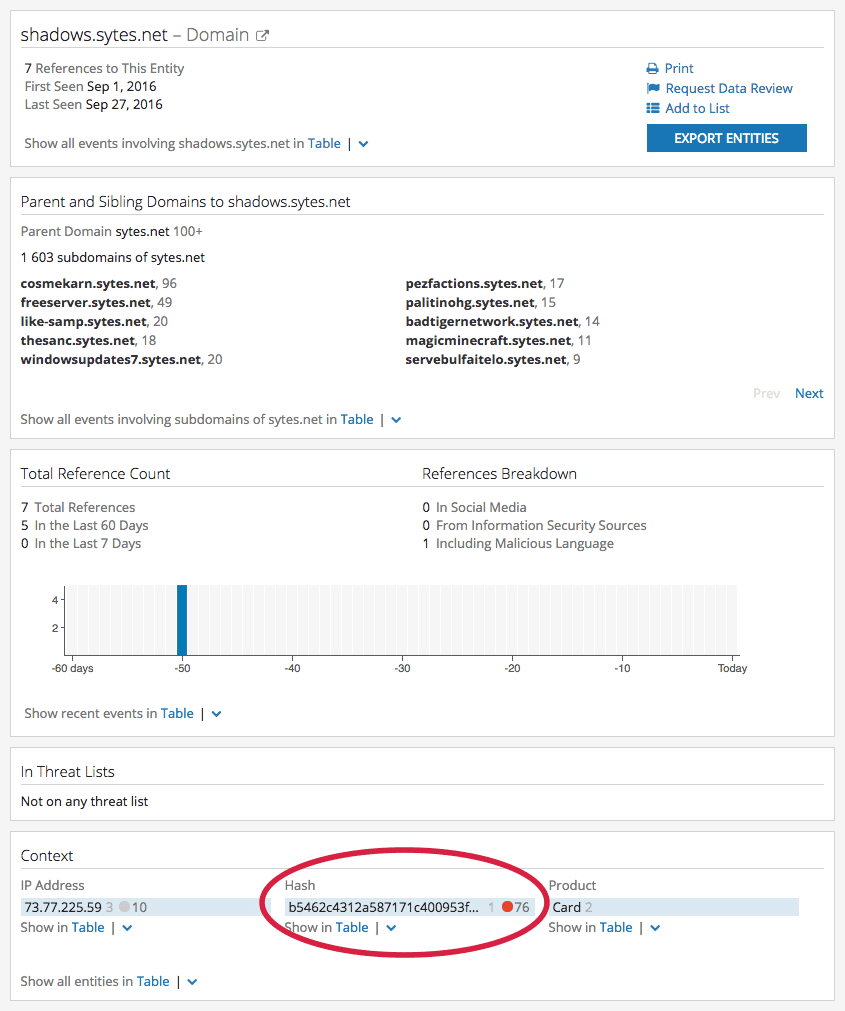 Intelligence Card™ for the domain shadows.sytes[.]net; note the high risk MD5 hash listed in the “Context” section.
Intelligence Card™ for the domain shadows.sytes[.]net; note the high risk MD5 hash listed in the “Context” section.
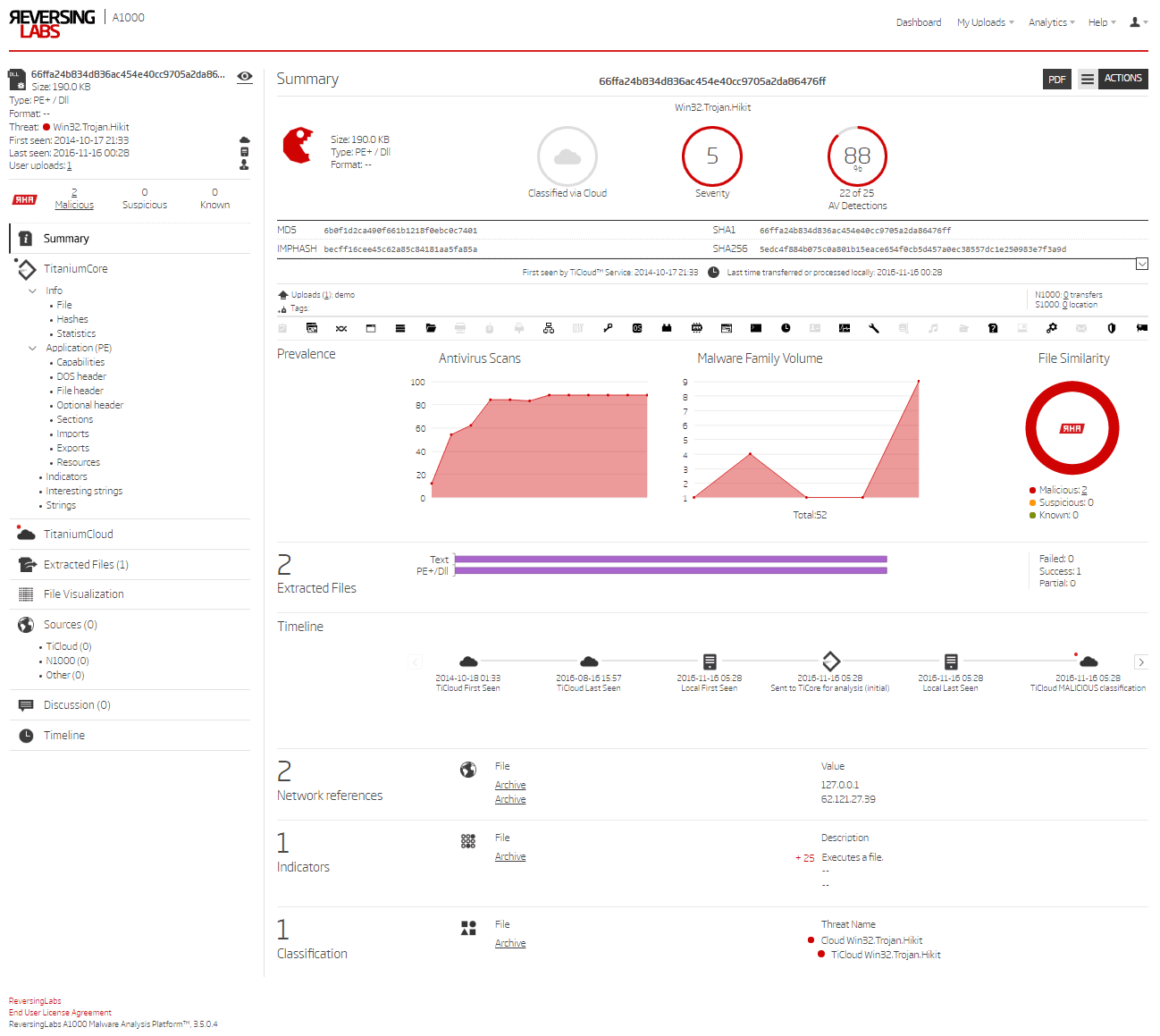
A subsequent pivot to the Intelligence Card™ for hash b5462c4312a587171c400953f8fd79f0, including a lookup to ReversingLabs for detailed file analysis, reveals the following information:
Data from ReversingLabs’s extension in the Hash Intelligence Card™. According to Malware Removal Guides, “Backdoor Win32/Fynloski.A also known as DarkComet is a repackaged version of a remote access tool (RAT),” bringing us back full circle and confirming the initial alert received about an IP believed to be hosting a DarkComet controller.
Demo
Click here to request a demo to learn more about using ReversingLabs with Recorded Future. Furthermore, all Recorded Future customers are eligible for a no-charge, two-week evaluation of ReversingLabs; just contact your Recorded Future account team for more information.
Diving Deep Into ReversingLabs
ReversingLabs’s automated static analysis engine recognizes over 3,500 file formats and contains support for 350 unpackers that malware authors use to obfuscate executables. The support for more file formats and unpackers continues to grow with each release of the analysis engine. This approach has deeper impact because it can (1) trace a sample’s lineage and provenance over time, (2) demonstrate when it was first seen and how its classification may have changed over time, and (3) impact triage, forensics, and remediation workflows.
Additionally, via the ReversingLabs RHA Algorithm, previously unknown samples can be matched against code-similar samples in the File Reputation Repository (which includes known good, suspicious, and malicious samples) to speed the triage process with quick likely reputation assessments.
ReversingLabs File Reputation and Automated Static Analysis, integrated with Recorded Future’s Intelligence Cards™, further enables organizations to fully investigate suspicious file hashes and empowers initial response, remediation, and future preparedness. A recent analysis by the Recorded Future team nicely demonstrated this integration (see the example above).
The Recorded Future integration highlights one aspect of the full set of ReversingLabs solutions that focus on continuous incident response to drive custom rule enforcement: take organizational context-specific information, investigate it, and use it to tune the defenses.
In the current integration, when Recorded Future discovers “interesting” file-related content: hashes, IP domain names, URLs, etc., the Intelligence Cards™ display high-level information about the threat from ReversingLabs File Reputation Repository including:
- Threat name
- Malware family name
- File reputation status (malicious, suspicious, known, unknown)
- File hashes
- Threat level
- Sample source trust level
- First seen and last seen date
- AV detections including regular updates and historical perspective
- Scanner details with a link to advanced threat analysis inside A1000
Click here to learn more about the A1000 Malware Analysis Platform by ReversingLabs.
ReversingLabs
ReversingLabs is the leading real-time automated static analysis capability, resulting in the world’s largest commercially available private File Reputation Repository of goodware and malware. ReversingLabs solutions focus on continuous incident response with custom rule enforcement, file threat reputation cloud for malware hunting and isolation, and rapid elastic file analysis for cloud apps, network, storage, and endpoints.
Related
