Operation Secondary Infektion Impersonates Swedish Riksdag, Targets European Audiences

Editor’s Note: The following post is an excerpt of a full report. To read the entire analysis, click here to download the report as a PDF.
The following report is an update to Insikt Group’s August 2021 publication “Operation Secondary Infektion Continues Targeting Democratic Institutions and Regional Geopolitics”, an investigation into the likely Russian state-sponsored information operation “Secondary Infektion.” This report examines a second newly discovered campaign of Operation Secondary Infektion, aimed at impersonating the Swedish Parliament (Riksdag) to promote a claim that Sweden is set to join NATO along with Ukraine. This report contains information gathered using the Recorded Future® Platform as well as several OSINT enrichment tools.
Executive Summary
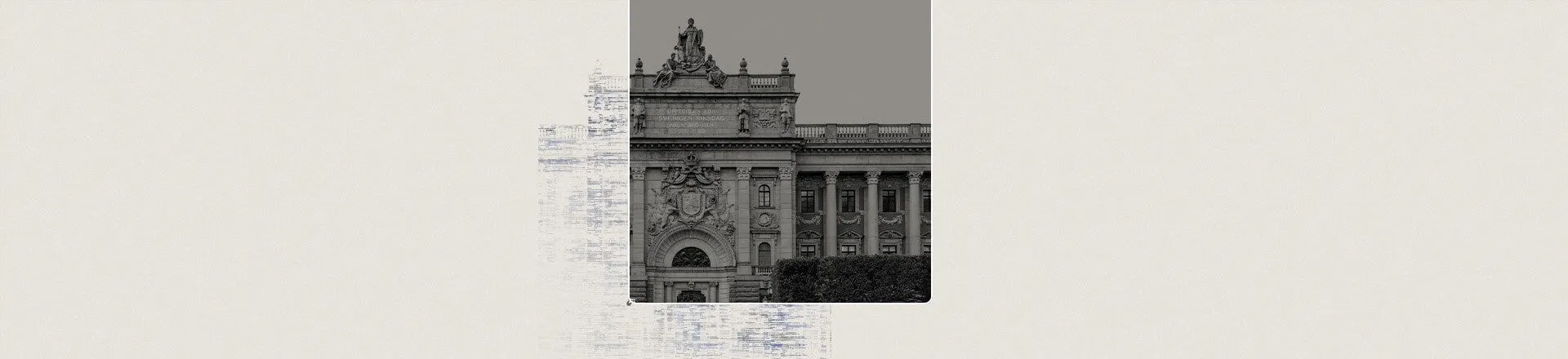
Recorded Future’s Insikt Group has located an image of a photoshopped screenshot, purportedly from the website of the Swedish Riksdag (Parliament) and circulating on a Swedish-language forum website and among Ukrainian sources, claiming that Sweden and Ukraine look to join NATO as soon as possible. We believe that this is an effort to sow mistrust of Sweden’s political figures domestically, create uncertainty and false optimism among Ukrainians, and shape negative perceptions of NATO and Ukraine among Russian audiences. This campaign is highly likely an instance of the likely Russian state-sponsored information operation “Secondary Infektion”.
Key Judgments
- This inauthentic screenshot is highly likely to be an instance of the Russia state-sponsored information operation Secondary Infektion, based on our analysis of this campaign’s tactics, techniques, and procedures (TTPs). These include language leap, first in Swedish, then appearing in Ukrainian and Russian, through self-publishing blog websites and forums published via single-use “burner” personas with no prior histories. This campaign also attempted social media amplification as expected on Reddit but failed.
- With each wave of articles, the first post appearing in Swedish, then Ukrainian, and most recently in Russian, the tone and presentation of the screenshot differs based on the specific European target audience. The strategy of deploying multiple narratives centered around confusion, discontent, and doubt is a hallmark of Russian state-sponsored strategic disinformation campaigns.
- At this time, we do not believe that this instance was successful, based much in part due to the influence actors’ continued dependence on prioritizing operational security (OPSEC) over audience building. This specific narrative is most likely dormant or abandoned as of September 2021.
Editor’s Note: This post was an excerpt of a full report. To read the entire analysis, click here to download the report as a PDF.
Related