Are You a Target for Nation-State Propaganda?
Editor’s Note: The following blog post is a summary of a RFUN 2017 customer presentation featuring David Brown, intelligence analyst at BT.
Key Takeaways
- Hacking is only a tiny part of nation-state cyber activity. Nation states also try to derail national conversations and influence world events by using clickbait and outrage-inducing content.
- The major players include the U.S., China, Iran, North Korea, the UK, and Israel, but the real gold standard in nation-state influence campaigns is Russia.
- The internet is a huge force multiplier for nation-state propaganda. Instead of leaflets and word-of-mouth, nation states use social media, blogs, and data-dump websites to distract and enrage their target audience.
- In the 2016 presidential election, Donald Trump was clearly preferable to Hillary Clinton from a Russian perspective. State-controlled media companies and APT groups combined to discredit Clinton’s campaign, and distract from Trump’s mistakes.
"Public sentiment is everything. With Public sentiment nothing can fail. Without it, nothing can succeed. He who molds public sentiment goes deeper than he who enacts statutes or pronounces decisions. He makes statutes or decisions possible or impossible to execute.”
Abraham Lincoln
Outrage is good for business.
It sells products, fills movie theaters, and makes (or breaks) political campaigns.
Just take a scroll through your favorite social media feed. Media outlets and blog owners learned long ago that outrage-inducing headlines are clicked far more often than those targeting other emotions.
More clicks equals more ad impressions, equals more money changing hands. It’s a simple formula, and it works every time.
But not all internet users have such capitalistic intentions. For some years now, nation states across the globe have taken advantage of modern technologies to carry out sophisticated influence campaigns.
And just like your favorite media outlet, they have one target in mind: You.
Meet the Puppeteers
At least in the security world, most people are aware of nation-state cyber activity.
China steals trade secrets from the United States. The U.S. tries to disrupt terrorist cells and foreign military operations. Israel does its best to limit Iranian military development.
For the most part, though, there’s an assumption that these cyber activities are limited to hacking, data theft, and sabotage. In truth, it goes much further than that.
Enter David Brown, a former military paratrooper and chemical warfare expert, now an intelligence analyst for the Security Threat Intelligence Division at BT. This October, Brown gave a presentation on nation-state threats and influence operations at Recorded Future’s annual user conference.
He opened with a bang: "Technology is a huge force magnifier for governments and threat actors. In the past, they had to rely on local news, leaflets, and word-of-mouth. Now everybody has internet access and a cellphone, these actors can serve propaganda directly to each individual."
We’re not just talking about propping up friendly regimes, here. We’re talking about nation states attempting to covertly influence events around the world using every tactic they have available to them.
How Nation States Target You
The headline for this article is a simple question. Are you a target of nation-state propaganda?
The answer is surprisingly simple: Yes, you’re definitely a target, and possibly a victim.
Here’s how it works. As Brown explained during his presentation, each nation state has its own reason for wanting to influence world events.
Take Russia, for example. In Brown's opinion, Russia is obsessed with Western influence in the former soviet sphere, also know as its “near abroad,” which includes countries like Georgia, the Ukraine, and Montenegro. In particular, the Russian defense doctrine is designed to prevent NATO expansion into these areas.
How is this achieved? By employing highly sophisticated influence campaigns to harness the “protest potential” of major democracies around the world.
Before we get into specific cases, though, it’s important to understand some of the techniques nation states use to influence populations, and how they can be employed to achieve specific objectives.
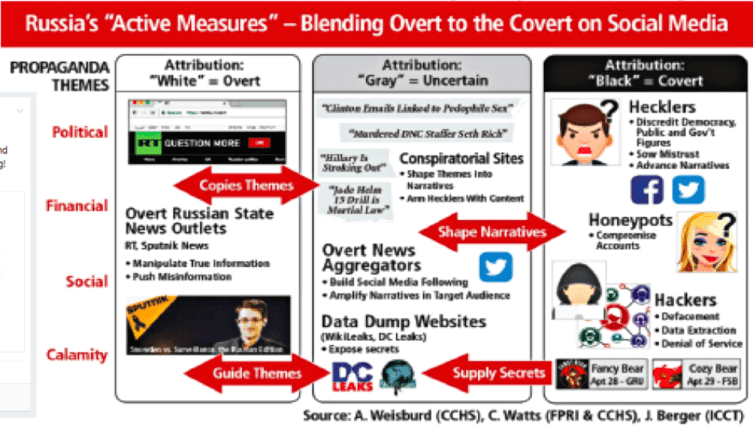
According to Brown, in simple terms, there are three layers to the average professional influence campaign.
1. Overt Operations
Using mainstream, often state-funded news networks, a nation state can manipulate facts and spread misinformation to target populations. In the case of Russia, networks like RT (rt.com) and Sputnik (sputniknews.com) will produce a huge number of “news” stories designed to direct attention onto the issues most beneficial to their cause.
In the case of elections, which are a prime target for nation-state influence campaigns, this could mean shedding positive light on a sympathetic candidate, or negative light on an unfriendly candidate.
2. Gray Operations
Overt influence campaigns might not be wholesome, but for the most part they are perfectly legal, and sufficiently above-board to be tied directly to state governments. The next level down, so-called “gray” activities, is where we see state-sponsored groups conducting a mixture of legal and illegal activities in a way that can’t be easily tied to any official bodies.
For instance, one of the most popular tools used to influence political discussion is the humble conspiracy website or blog. Since these types of sites aren’t expected to substantiate their claims, they are the perfect place to introduce stories designed to feed the social media rumor-mill.
At the same time, state actors will set up news aggregator-style social media accounts, build up a following, and use it to spread their propaganda directly to their target audience. All of this is done, of course, using highly provocative “clickbait” style headlines designed to encourage social sharing.
Finally, nation states have often leveraged data-dump websites to embarrass or hinder individuals or organizations viewed as a threat. And where does all that embarrassing data come from? You guessed it.
3. Covert Operations
This is the darkest layer of influence campaigns — the types of activities nation states cannot admit to being a part of.
For instance, fake social media accounts are routinely setup specifically to discredit public figures, sow mistrust, and advance the desired narrative. Along the same lines, state actors will use honeypots and phishing campaigns to compromise real social media accounts and use them for the same purposes.
But that’s all child’s play compared to the real meat of influence campaigns: Stolen data. This includes emails, confidential files, and anything else that can be used to cultivate a scandal.
After all, why fabricate a story if there’s something real to talk about?
How to Rig an Election
Although Brown focused heavily on Russia in his presentation, he was quick to point out that they are far from the only nation-state threat. Russia is a useful case study, however, as they are outstandingly good at running campaigns designed to influence democratic processes all over the world, including in the U.S., France, and Germany.
For now, let’s focus on perhaps the highest-profile influence campaign of the past few years: The 2016 U.S. election.
What’s the first thing that comes to mind? If you’re like most people, it’ll be the hacks targeting the DNC, DCCC, and John Podesta, chairman of Hillary Clinton’s 2016 Presidential election campaign. These hacks enabled Russian actors to exfiltrate huge amounts of data, some of which would ultimately be used to discredit the Democratic Party and Clinton herself.
Recorded Future researchers also discovered a Russian-speaking hacker selling access to the U.S. Election Assistance Commission. Read the report here.
But let’s take a step back. Why would Russia be interested in the result of the 2016 U.S. election?
To answer this, Brown implored us to consider the two candidates in the final leg of the 2016 U.S. election. Leaving aside any speculation into an untoward relationship with Russian business and political powers, Donald Trump was considered likely to be sympathetic toward Russia and their “near abroad.”
Hillary Clinton, meanwhile, was not an obvious ally for Russia. As a staunch supporter of NATO and Russian sanctions, Clinton had openly criticized Putin’s annexation of Crimea, and as U.S. Secretary of State had opposed the Russian-supported Assad regime in Syria.
In Brown's opinion, of the two, then, Trump was a clear favorite from a Russian perspective, hence their decision to look for information that could be used to hinder the Clinton campaign, and distract from any difficulties faced by the Trump campaign.
Of course, the Russian authorities couldn’t reveal these secrets openly: To do so would be to admit direct interference with the U.S. election. Instead, Russian state actors relied on the types of activities we’ve already described.
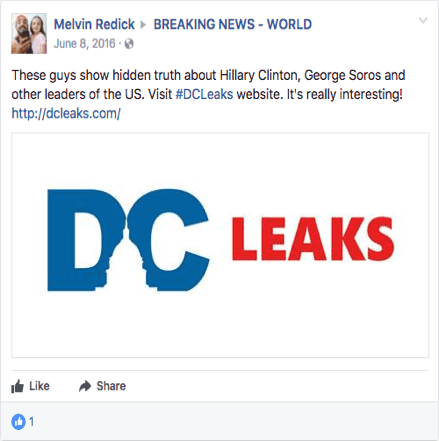
First, Russian actors scoured the data stolen from the DNC, DCCC, and John Podesta, looking for anything that could be used to sway U.S. public opinion against Hillary Clinton. Once suitable ammunition was identified, the relevant files and emails were released via WikiLeaks and the Russian-operated DC Leaks website.
But, as we already know, that’s just stage one. From here, fake and compromised social media accounts were used to propagate the story, stirring up as much controversy as possible and effectively hijacking the U.S. political conversation.
In September 2017, long after the election, Facebook stated it had identified at least $100,000 worth of advertisements had been purchased during the election campaign by a Russian company with ties to Kremlin. For the most part, the advertisements focused on dividing social issues designed to further sway public opinion away from Clinton and toward Trump.
At the same time, conspiratorial websites ran outlandish stories about Democratic Party involvement with a child-sex ring, supposedly substantiated emails stolen during the Podesta hack. These claims were quickly debunked, but there can be little doubt that they had a tangible impact on public opinion, or that the Russian propaganda machine played a part in spreading the story.
In a short period of time, the campaign spread from social media and data-dump websites to Russian-owned news website, then to major blog sites, and ultimately to mainstream U.S. news outlets. What started as a covert operation quickly became the subject of overt, legitimate political discourse.
In short, Russia conducted an expensive and highly complex propaganda campaign, requiring hundreds of personnel across a handful of state-run organizations, all to reach one person: You.
Searching for Fingerprints
At this point, you might be wondering how Brown came to be so sure Russia was responsible for influencing the 2016 Presidential election. Russia had a clear motive for influencing the election, certainly, but to be certain, more information is required.
Unsurprisingly, this is a common problem where nation-state influence campaigns are concerned. In this case the idea that Russia were responsible for the DNC hack became a matter of public speculation, but it’s highly likely that in many other cases nation-state influence goes completely undetected.
When Brown used Recorded Future to track the activity of APT groups known to work for the Russian government, this is what he found.
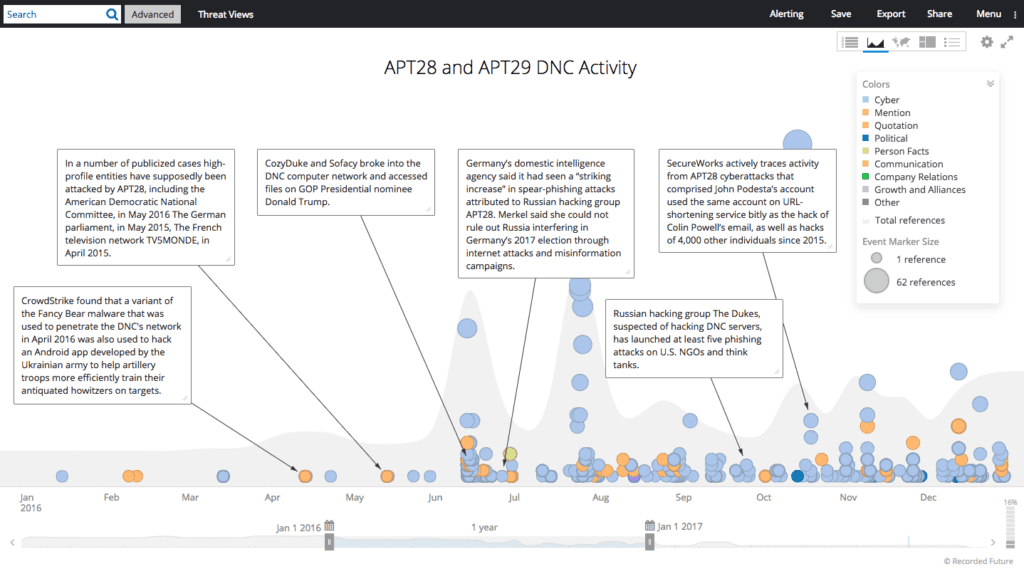
For clarity, these are the actors Brown studied:
- APT28 (Fancy Bear) — A cyber espionage group linked to Russian military intelligence agency GRU.
- APT29 (Cozy Bear) — A hacking group linked to the Russian Federal Security Service (FSB).
As you can see from the image above, spikes in these groups’ activity clearly coincided with Russian political aims.
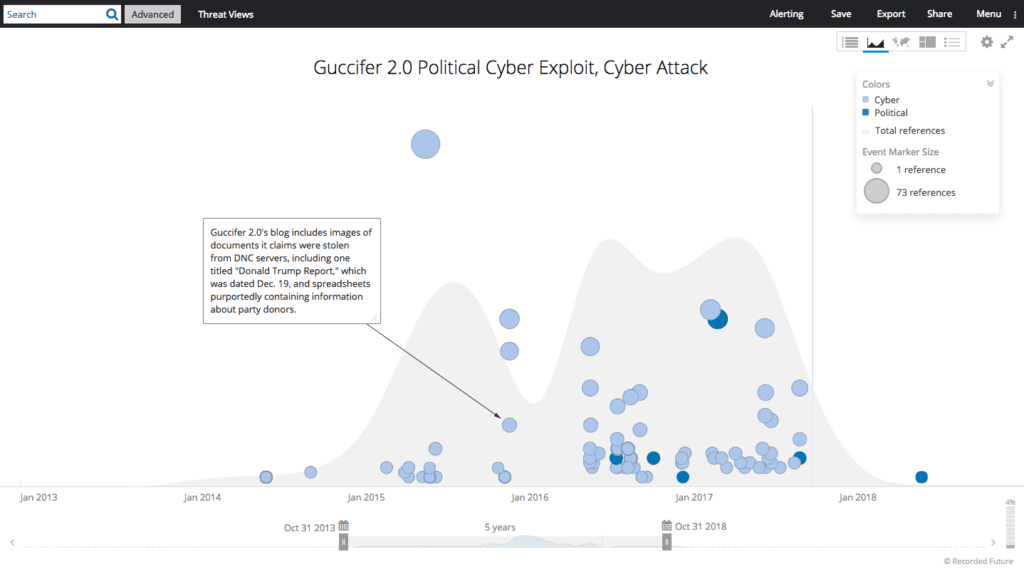
At around the same time, a supposedly Romanian actor going by the pseudonym Guccifer 2.0 claimed to be responsible for the DNC hacks. Evidence suggests, however, that the actor in question was unable to speak Romanian, and appears to have used a Russian-language VPN.
Again, while the evidence isn’t conclusive, it seems likely Guccifer 2.0 was another Russian actor put in place to muddy the waters, and make determining the real identity of the actors involved in the DNC hack more difficult.
And we can take this yet another stage further.
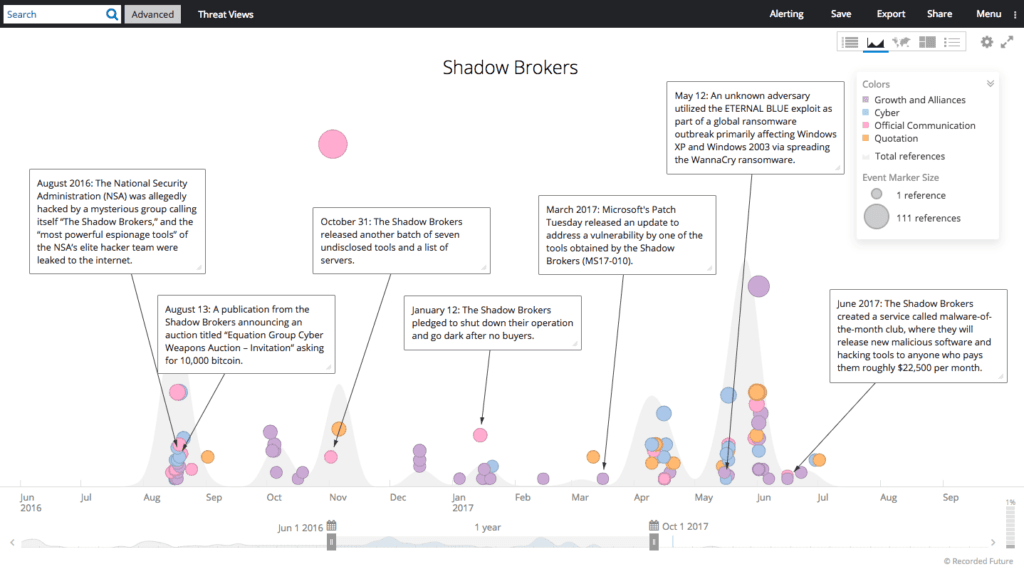
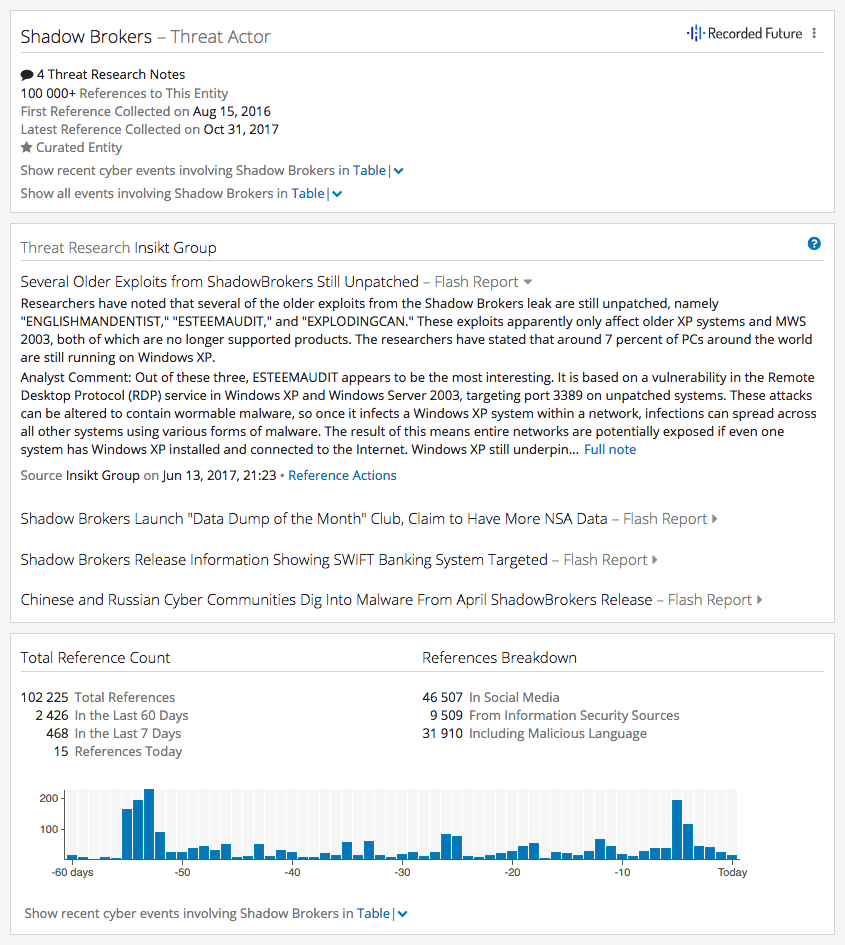
Around three months prior to the election, a group known as TheShadowBrokers became active. While the origins of the group are yet to be confirmed, a number of their posts have displayed overt support for President Trump, and the timing of their activities has routinely supported known Russian objectives.
And while all this analysis paints a compelling argument that Russia really was involved with influencing the U.S. election, there’s one more thing to consider.
When the DNC hack took place, WikiLeaks and DC Leaks didn’t simply publish the content en masse. Instead, they systematically published only the most damning documents and emails, and spread out the release to cover as much of the election campaign as possible. This is important for two reasons:
- It implies the entity responsible for the leak had a vested interest in hindering the Democratic Party campaign, and;
- While an individual hacker or group can easily obtain huge quantities of data, it takes a tremendous amount of resource to analyze thousands of documents in a systematic manner and deploy only the most damaging information.
When all this is considered, it’s difficult to argue with Brown's assertion that Russia really did influence the 2016 U.S. election.
Fake News, Everywhere
Of course, not all nation-state influence campaigns focus on elections. Elections are the most obvious candidate, certainly, but they’re far from the only target.
Think back to the Abraham Lincoln quote we opened this article with:
"Public sentiment is everything. With Public sentiment nothing can fail. Without it, nothing can succeed. He who molds public sentiment goes deeper than he who enacts statutes or pronounces decisions. He makes statutes or decisions possible or impossible to execute."
Simply put, if state actors can influence public opinion inside another nation state, they have an opportunity to influence actual policy decisions. It’s difficult and expensive, yes, but possible nonetheless.
Unfortunately, there are no easy solutions. Attempts to block or restrict artificial entities or groups are almost completely ineffective, since new accounts and IP addresses can always be used, and in many cases even attributing activities to the correct nation state is easier said than done.
This, Brown concluded, is why threat intelligence solutions like Recorded Future are such an important tool for analysts to use. By monitoring political and military events in the real world, and comparing them to current and historic cyber activity, you can build up a picture of adversary behavior.
From there, you can start to calculate the likely targets and timings of future attacks, and better protect yourself and your clients from future influence campaigns.
To see a full list of links sourced in this blog post, download the appendix.
Related
