Mapping and Monitoring Cyber Threats
Threats to information security are part of everyday life for government agencies and companies both big and small. Monitoring network activity, setting up firewalls, and establishing various forms of authentication are irreplaceable components of IT security infrastructure, yet strategic defensive work increasingly requires the added context of real world events. The web and its multitude of channels covering emerging threat vectors and hacker news can help provide warning signs of potentially disruptive information security events.
However, the challenge that analysts typically face is an overwhelming volume of intelligence that requires brute force aggregation, organization, and assessment. What if significant portions of the first two tasks could be accomplished more efficiently allowing for greater resources allocated to the all important third step of analysis?
We’ll outline how Recorded Future can help security teams harness the open source intelligence available on various threat vectors and attacks, activity of known cyber organizations during particular periods of time, and explicit warnings as well as implicit risks for the future.
Cyber Situational Awareness
There’s sometimes the relatively general question of situational awareness: what’s going on in the world right now. In the cyber security space that may mean understanding the latest malware threats, monitoring recent targets, and identifying new groups organizing attacks.
Let’s say you want to access a daily round up of the week’s activity by hackers and hacktivists. Here’s one recent day, June 12, 2012, examining reports of hacker activity discussed in online media described through the lens of Recorded Future:
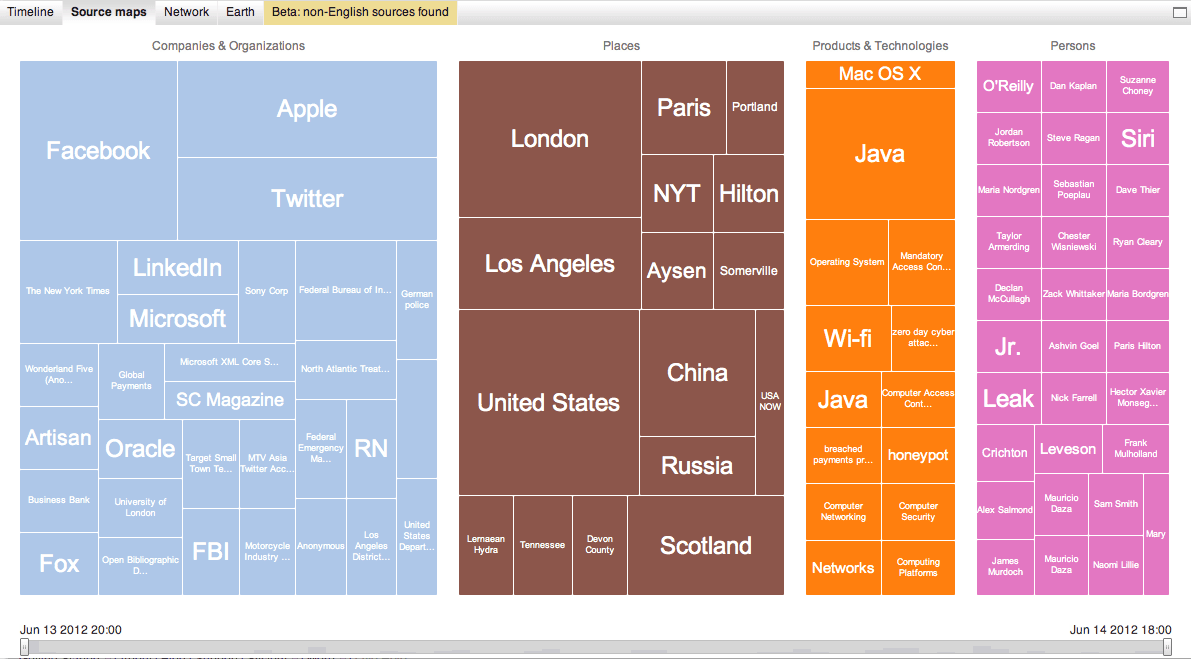
What is all of this shown above? It’s a display of the entities mentioned related to hackers or hacktivists on Thursday, June 12, broken down into categories for companies and organizations, places, technologies and products, and people. These are identified through the aggregation of intelligence from tens of thousands of online media channels ranging from mainstream media to blogs to Twitter and everything in between. Each colored block is linked to source material, and you can explore the live view yourself, but we’ll also outline examples from the results:
- The large blocks for Twitter, Facebook, and LinkedIn tie into a report warning of Andr/DrSheep-A, an Android tool that allows hackers to takeover social accounts on a wireless network.
- Reports note that Apple updated Java for Mac OS X on the same day that Oracle patched vulnerabilities in the application framework.
- German police carried out an operation investigating individuals related to a DDoS attack by hacktivist group Anonymous.
- Microsoft acknowledged exploits in Internet Explorer related to its XML Core Services.
- Motorcycle Industry Jobs board hacked resulting in leak of 6,700 account details.
- The United States Department of Defense website Defense.gov was attacked by a group called “Wikiboat” that leaked contact information.
- Hackers under the name SpexSec released thousands of records for residents of Clarksville, Tennessee after previously warning of security flaws.
Taking the results from just this single day we are able to quickly identify several, and sometimes all three, of the crucial elements in each case: attacker, target, and threat vector.
Networks of Attackers and Targets
We’ll keep the concept of situational awareness in mind but make things a bit more directional by exploring ties between known attackers – what we’ll loosely describe as hacktivist organizations – and targets in a particular industry – mobile service providers.
The network below shows links between companies, organizations, locations, and technologies (all the same categories shown above) extracted by Recorded Future for the period of April 1, 2012 through June 18, 2012.
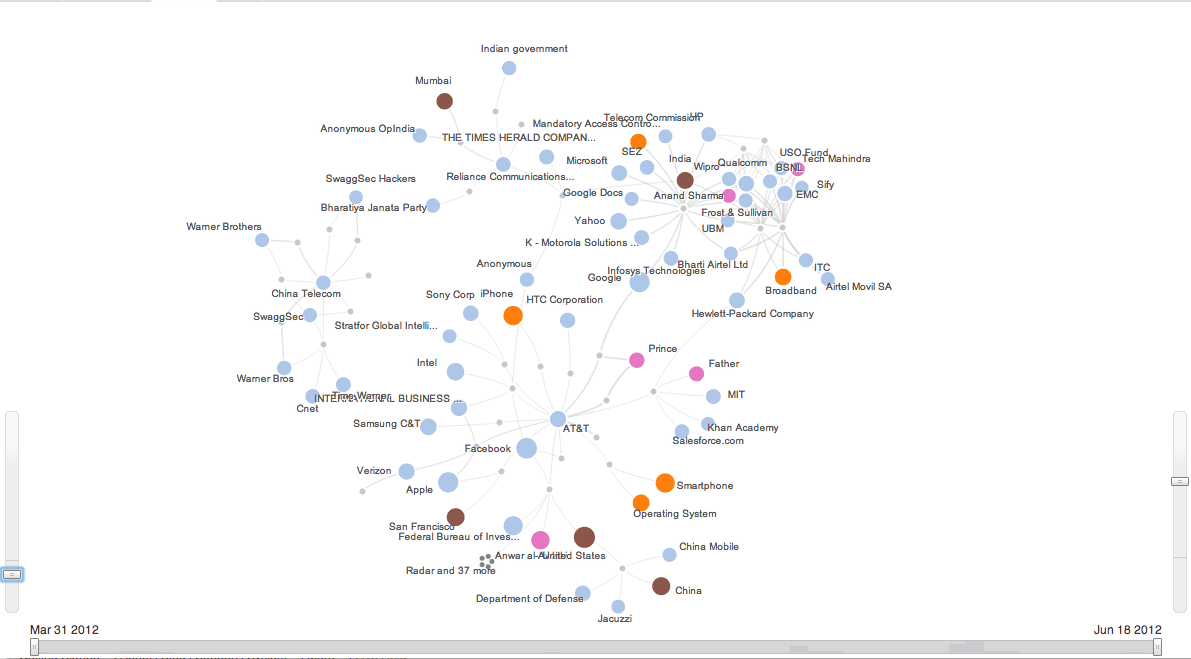
This provides us a quick overview of those mobile providers affected during the time period. It also shows several different clusters of activity (check out the live network), and we can quickly highlight the activity alleged or claimed by one group, say the Anonymous collective, versus another such as SwaggSec.
We can then go into those links and further explore the nature of each attack with the purpose of understanding how each organization was attacked, why it took place, and if a similar scenario could occur for another entity.
Looking Ahead
While it’s not often that attacks are forewarned, there are the occasional threats made public ahead of time as well as key dates to watch that could be touch points for driving campaigns on sociopolitical foundations. Looking forward thirty days from the date of this post’s publication, we find two interesting moments to watch.
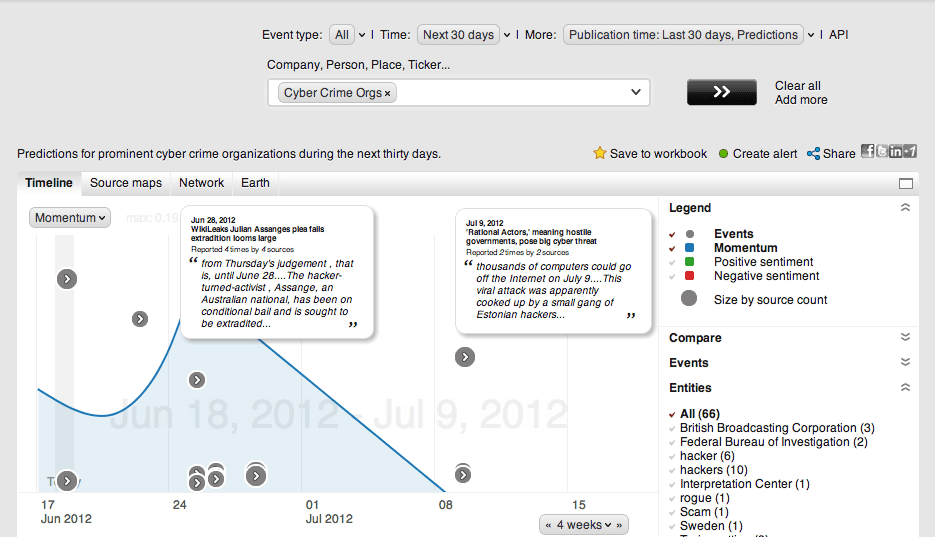
One might look at the above timeline and think that there’s little out there on the web being forecast about attacks. Well, let’s provide a little more context by looking back at events forewarned – true or not – related to activity by Anonymous during the first half of 2012.
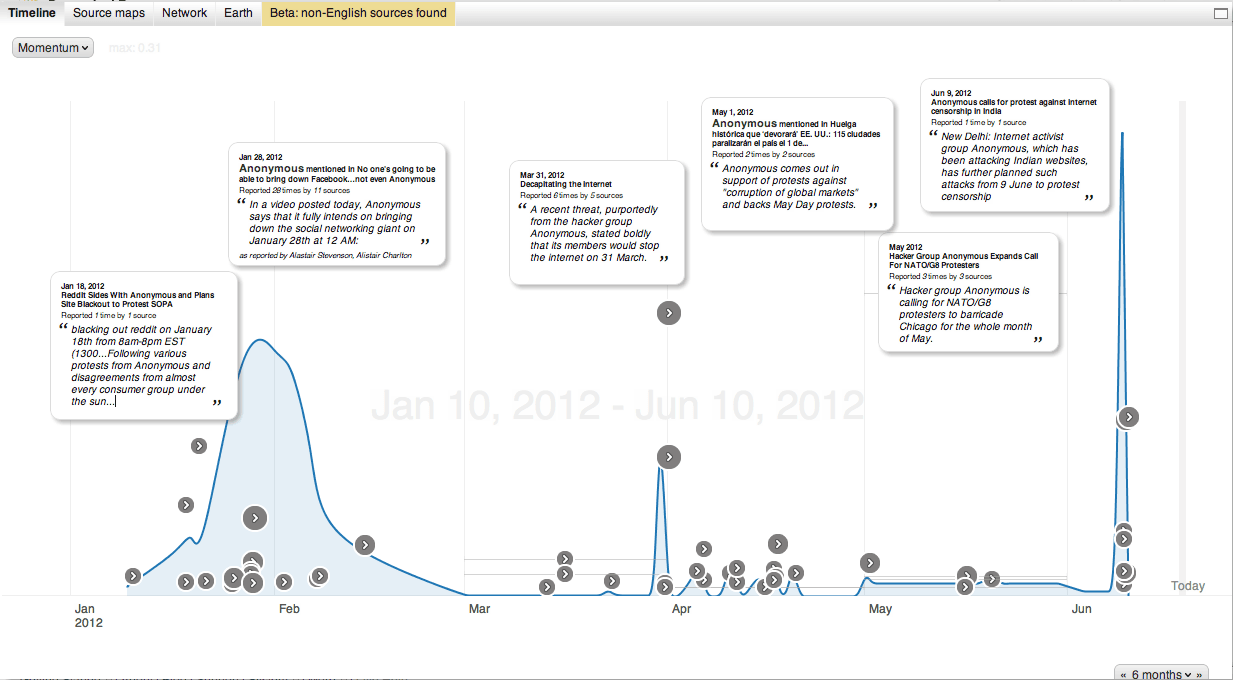
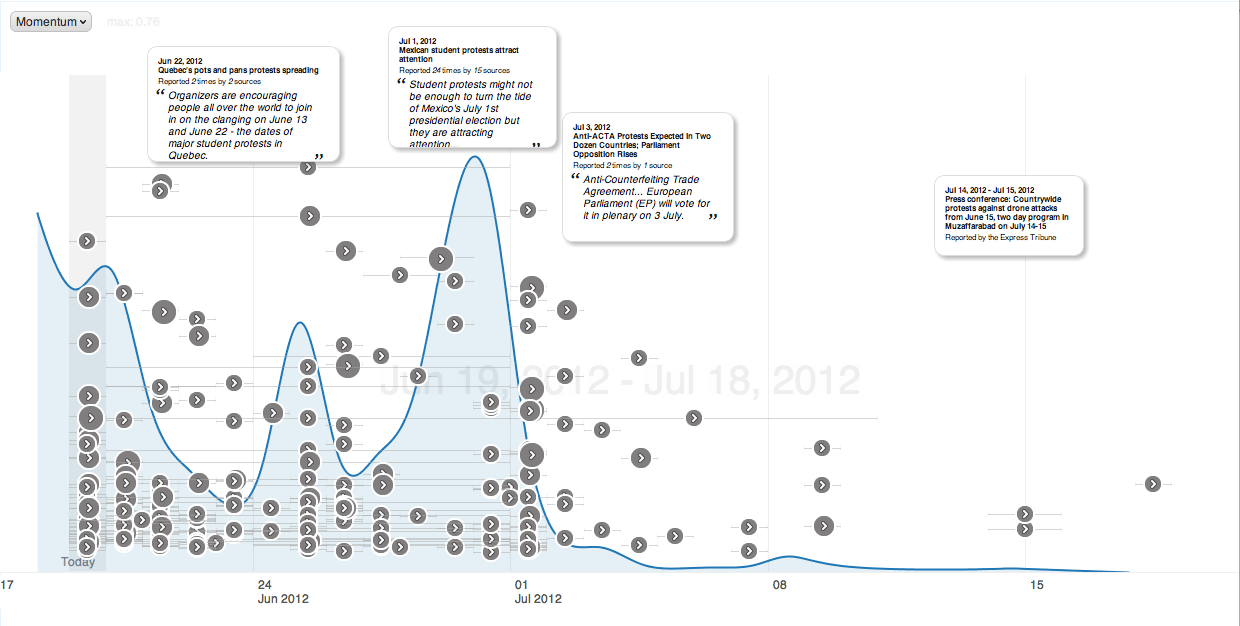
Seeing that some of these events are related to tactics used for strategic goals – stands against legislation, attacks on companies for their standards or corporate responsibility, or political protests – we can also plot out upcoming sociopolitical risk scenarios. It leaves the analyst to then ask questions about their organization’s apparent ties or support to contentious causes that might make them a target on these dates.
Putting It All Together
We’ve outlined three broad ideas in the segments above including:
- Situational Awareness – Quickly understanding the cyber threat environment at a given point in time.
- Analysis – Mapping out the ties between different actors – attackers and targets – plus the threat vectors used or threatened in each case.
- Monitoring – Arranging a real time alerting system or dashboard for events of interest whether those are threats, breaches, and attacks or potentially catalytic future events to watch.
Related