5 Steps for Reducing Risk From Leaked Credentials
Leaked credential dumps make the news every month. Each credential leak seems to be larger than the last one, which means your organization is undoubtedly impacted by these data dumps. Security teams need to have answers in place to address leaked credentials, both to assure the board that appropriate steps are being taken and to keep your users safe. Some of the concerns that surround leaked credentials include:
- What can you do about leaked credentials?
- How do you operationalize leaked credentials?
- What actions and steps do you take once you hear about leaked credentials?
- Are there compensating controls in place?
At Recorded Future, we’re producing aggregate metrics around leaked credential data and the risks associated with it. Some security teams we meet with are worried about adding credential leak alerts, because while they do occasionally work with their risk team, they don’t have a strong enough relationship and are worried about the risk team’s reaction. Lacking relevant context, the risk team won’t necessarily be able to fully grasp what the alerts mean, which could lead to errant assumptions and unnecessary panic.
Here, we’ll look to answer the questions listed above by examining the value of threat intelligence in getting context around credentials leaks and deciding how serious they are, and then go through the five-step process for supply chain risk management provided by the NIST Cybersecurity Framework.
Leaked Credentials and Third-Party Risk
Part of the problem is that risk management teams generally focus on risks associated with financial, legal, or brand reputation processes, meaning they are not familiar with risk management as it applies to information security.
This is especially true when it comes to third-party risk associated with leaked credentials. The risk management team may make false assumptions, such as that the third party that leaked credentials is “bad” — either untrustworthy and not worth partnering with, or going out of business — and they might then conclude that your organization needs to stop advertising or otherwise engaging with them. But this is an oversimplification, and it’s often not the case that a relationship with third parties who have opened your organization up to risk must be abandoned.
The NIST Cybersecurity Framework
Understanding the threat posed by leaked credentials involves multiple steps.
The first level of awareness takes compliance with widely accepted practices such as the NIST Cybersecurity Framework, which now includes a category on supply chain risk management.
The second level requires additional education for risk management teams, helping them go beyond those standards. To someone outside of the company, the source of the leak might not be significant, but internally, it is useful to know whether the leak was initiated by an attacker that got a dump of usernames and passwords or if it was an employee who accidentally leaked or used weak security practices.
There has to be a focus on what to do about this context, too. What causes problems around leaked credentials are employees signing up on LinkedIn, Ashley Madison, social media sites, or really anywhere, and re-using their corporate password (or worse, their corporate email and corporate password).
Because of weak password habits like these, many fraud schemes don’t require any malware. Employees get an email saying something like, “We have access to your computer and our proof is, here’s your password,” which may not be true in most cases, but statistically will be for some. This only needs to work for a handful of victims for the bad guys to make money. The fact that one of those potential victims could work for the third parties we work with makes the risk too high for many.
How to Mitigate the Risks of Leaked Credentials
There are a number of important steps an organization can take to mitigate the dangers from leaked credentials:
- Strong security practices (better passwords or expiration)
- Two-factor or multi-factor authentication
- Central identity access management (we trust Google more than we trust Expensify, for example, so we use Google sign-in)
- Single sign-on (SSO) that’s managed centrally by someone trustworthy within the organization
Follow any one of these steps, or some combination of them, and many of the risks posed above can be mitigated.
Of course, organizations can go beyond that — now we’re into detection and response. Once the basics outlined before are covered, you can start to focus in on specific leaks.
That’s where a threat intelligence platform like Recorded Future really shines. By providing the context, you can cut through the irrelevant information and get to the point, much more quickly answering a question like, “Do I need to worry about this leak?”
For example, let’s say a new leak is discovered. Is it actually novel, or just a rehash of existing leaks? Does it have a password we care about? How strong is the password? These are usually the first questions that security teams want to know. One of the advantages that Recorded Future offers is that for large credential leaks, we can present you with only the relevant data. You don’t necessarily need all billion records in a credential dump, you only need the records relevant to your organization. That much smaller subset of data is much more manageable to ingest and analyze without having to add new resources, like automation.
NIST’s Framework for Action
Your enterprise has leaked credentials — now what?
Let’s use the NIST Cybersecurity Framework below to guide our overall response.
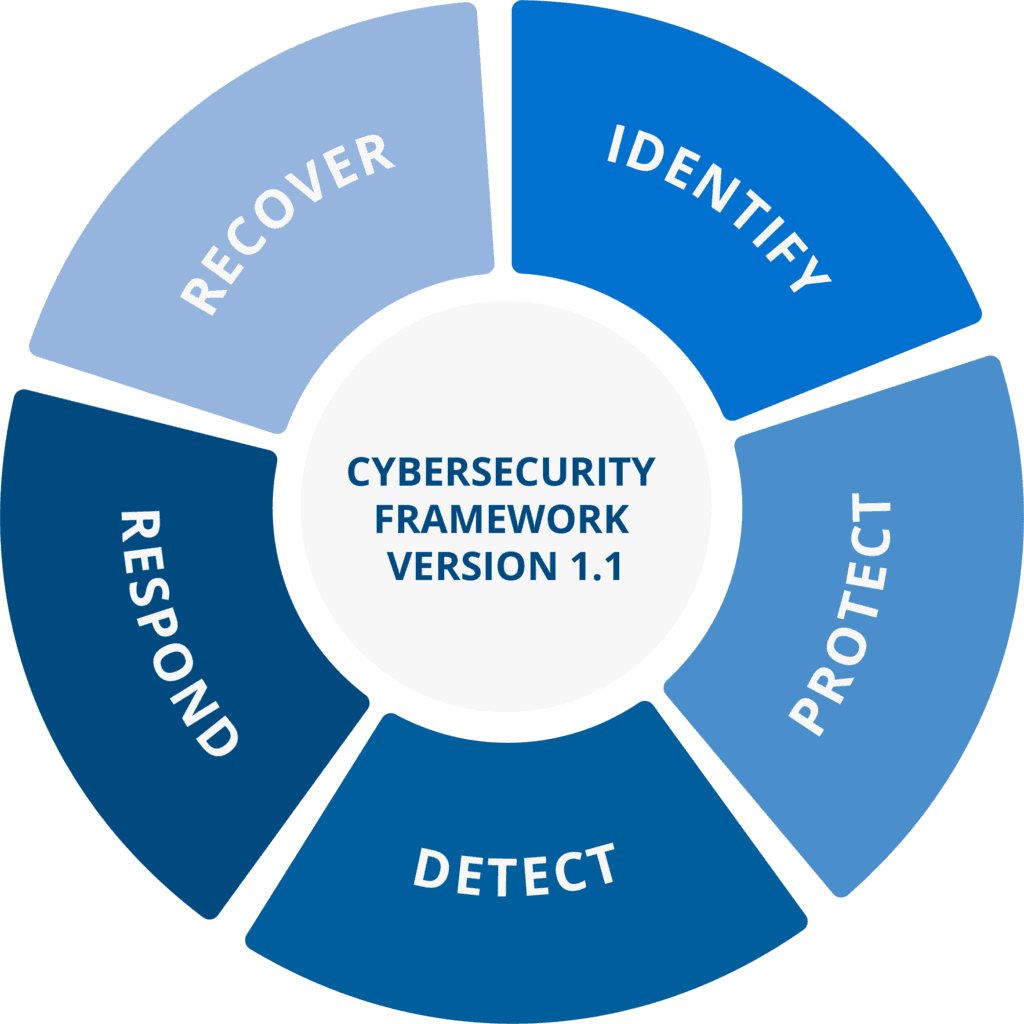
1. Detect
In this case, let’s assume that one of your threat intelligence sources or own research made you aware of a number of credentials from your domain available on the deep or dark web, and that the source provided you with the email addresses and password hashes for a number of your accounts.
2. Respond
What are the steps that one should take? Do you have your procedures all defined? Are there any gaps? These are not a one size fits all, but here are some basics:
- Reset or Lock Accounts: If your organization doesn’t use SSO, you might need to check multiple systems.
- Check for Abnormal Authorization Events in Logs: Is the percentage of failure versus success different from the usual? Are the login and logoff times outside of the norm?
- Check Access Levels: For C-suite executives or administrators, check the systems to which they have access. For regular users, reset their password and inform them why.
- Review Compensating Controls: Two-factor authentication may not need to be reset. Try user behavior analytics (UBA) — what do you see?
- Notify Users: Change other account passwords, remind them that password sharing is unwise, and suggest a password manager for home use.
3. Recover
Research the leaked credentials. Are they all from the same password dump? Is it an old dump or new information? Keep in mind that most “new dumps” are just rehashes of older dumps.
Is it your leak, or did it come from a third party? If the leaked credentials are from your organization, the next step is going into incident-response mode.
Did your process and procedures work? If not, modify them and start over.
4. Identify
Reevaluate your risk based on this information. Were there gaps in your controls and/or process? Did you know to which systems each compromised account had access? If not, conduct an access audit and restrict access to only those systems each user needs to perform their duties.
5. Protect
Do you need to add two-factor authentication for critical accounts? It’s also a good idea to add controls to monitor for access.
Learn More
For more information about how Recorded Future can help organizations better understand and prevent threats, request a personalized demo today.
Related
