Rapid Response Imagery and Web Intelligence for Crisis Management: Kano Security Analysis
On Friday, March 18, 2013, a car bomb exploded in a busy luxury bus park in northeast Kano, Nigeria. The militant Islamist group Boko Haram claimed responsibility for this suicide attack that killed nearly 40 people. It was the group’s deadliest attack in Kano since its members went on a rampage against the city’s security forces in January 2012.
This post investigates this terrorist attack through the literal and figurative lens of DigitalGlobe FirstLook, a product that combines expert analyst assessments with two complementary intelligence capabilities: DigitalGlobe satellite imagery intelligence and Recorded Future open source web intelligence. The result is a new and powerful geotemporal approach to analyzing catastrophic events.
Below is satellite imagery from DigitalGlobe taken 24 hours after the bombing. The center of the image reveals the aftermath of the devastating attack. In addition to the immediate impact, imagery of this attack offers clues of patterns in mass casualty attacks organized by Boko Haram that can aid and improve ongoing security operations.
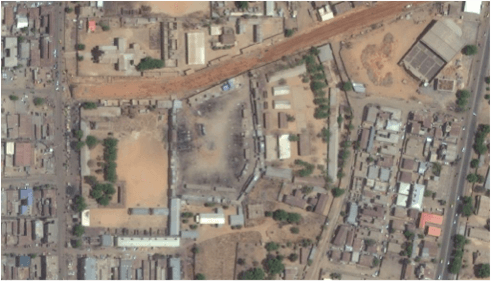
First, let’s establish the setting via DigitalGlobe’s imagery. The bus depot is bordered by several facilities: multiple schools (Kano Teachers College, Kundila Special Primary School, Danwaire Special Primary School, and Trans Holy Trinity School) and Christian churches (St. Paul’s Anglican Church and Cathedral Church of Holy Trinity).
In a fluid crisis situation, all-source analysts can use these clues as guidance for prioritizing action from assets on the ground. Given the target’s surroundings, further investigation was required to determine: had the group recently hit other Christian targets in Kano?
Using Recorded Future’s web intelligence tools to analyze information from 250,000+ open web sources, analysts can quickly generate a timeline of Boko Haram attacks suspected or known to target Christians during 2013. A notable surge in such attacks is evident beginning in March 2013:
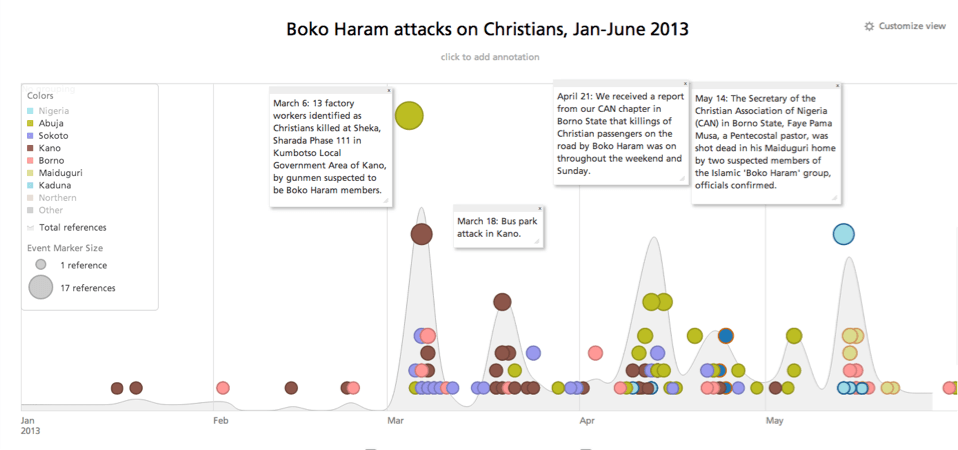
Recognition of an escalated threat against or near sites of a particular nature is critical information for stakeholders and personnel on the ground in volatile locations.
Also visible in the DigitalGlobe satellite imagery is a road running east-west to the north of the bus depot. The bus depot is located in northeast Kano and sits just north of the nexus between two major northeastern roadways: Airport Road that runs to and from Kano’s international airport and Hadejia Road, which is the primary path in and out of the city to the northeast.
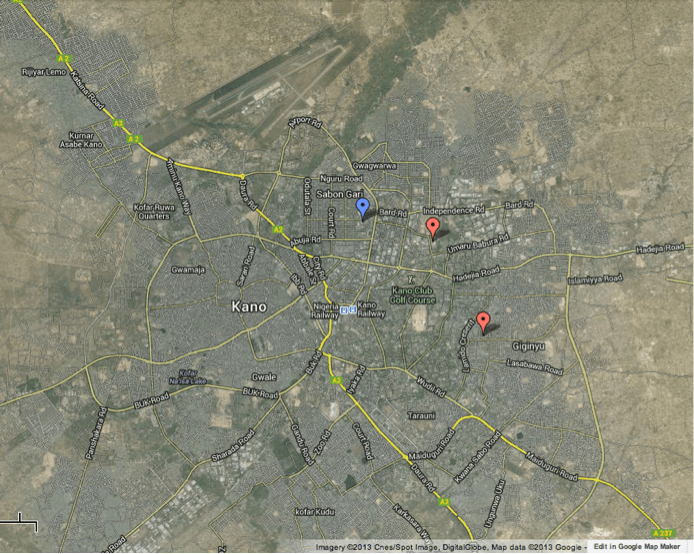
The blue pin marks the bus depot; the red pins show the locations of two previous attacks carried out on January 20, 2012.
Having quickly contextualized the setting of this attack through the post-attack imagery, we’ll now conduct further analysis using web intelligence to seek out patterns after the bombing. These signals, along with rapidly delivered imagery, provide actionable intelligence for organizational and government security operations. We’ll do so by using Recorded Future’s Temporal AnalyticsTM Engine, which organizes information from 250,000+ open web sources, to analyze Boko Haram activity in Kano before and after the March 18 bus depot bombing. We’ll then compare to a separate mass casualty attack carried out by Boko Haram that occurred 14 months prior on January 20, 2012.
Aftershocks
FirstLook is designed to provide rapid response satellite imagery after a catastrophic event as the example above shows. It also allows us to understand recovery timelines. For example, we can see (image below) sixty days after the Kano bus depot attack the immediate area in and around the bus depot appears to be business as usual. But how long did this take and what events occurred in between?

In our first timeline, we found that attacks aimed exclusively at Christian targets in Kano fell off slightly after March. But there were a series of separate attacks after the bus depot bombing that affected security forces and the larger population at large in Kano.
Below, you’ll find a timeline from Recorded Future that displays those aftershocks including a series of firefights, thwarted bombings, and subsequent, smaller scale assaults with explosives.
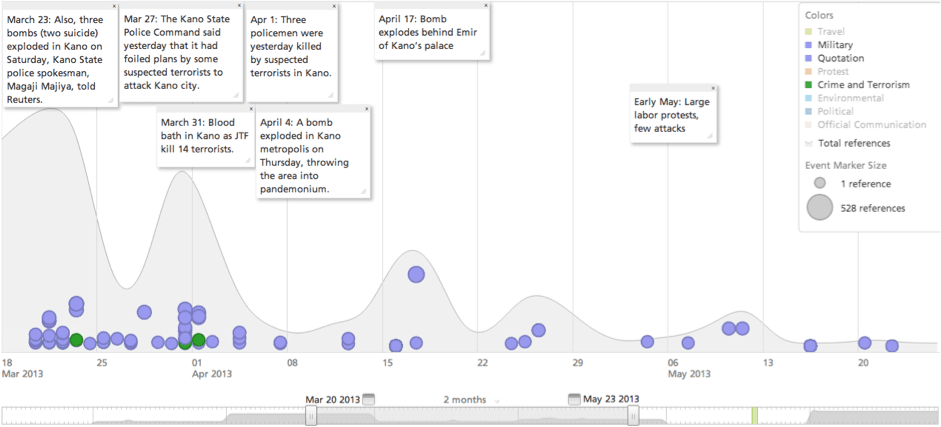
Details of post-bus depot attack – Boko Haram activity:
- March 23, five days after the bus depot attack, three bombs, two of which were suicide attacks, exploded in Kano.
- March 27, nine days after the bus depot attack, police intercepted a car reportedly containing the following: an AK 47 Rifle, Rocket Launcher, remote-control bombs, two cylinder remote-control devices, 14 hand grenades, four rolls of wire connector and 12 power sources.
- April 4, seventeen days after the bus depot attack, a bomb exploded and shootout ensued on Zoo Road in Kano.
- April 17, nearly a month after the bus depot attack, a suicide bombing took place near the Emir of Kano’s palace.
There was then a decline, although not a complete break, in violence attributed to Boko Haram edging into May. So, we can say with confidence a steady stream of follow on attacks occurred in Kano that fell off several weeks after the large scale terrorism event.
Why is this potentially interesting in the context of security signals and operational intelligence? This can serve as a starting point to look for patterns compared to previous attacks and inform security teams about what to anticipate the next time an attack by Boko Haram occurs.
To determine any patterns, analysts will need to compare events to a similar event. In this case, the aftermath of a Boko Haram attack in Kano on January 20, 2012. This was a more distributed, multi-stage attack directed at security forces that left nearly 200 dead, but had the markings of a well planned operation akin to the bus depot bombing.
The post-event timeline can be seen below:
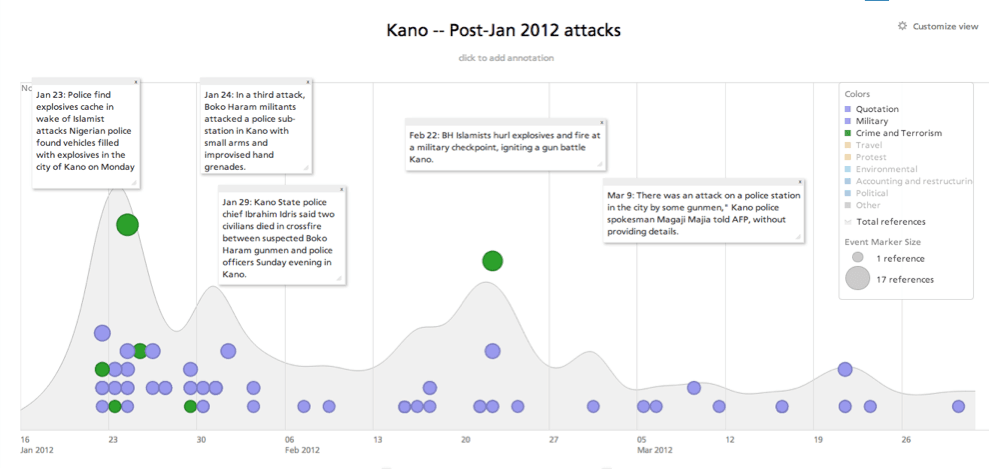
Day zero for this event was Friday, January 20, 2012. The timeline above shows us that, like the March 2013 attack, violence did not immediately subside. Here are post-attack activity details:
- Jan 23, police find explosives cache in vehicles stopped at a checkpoint in Bompai neighborhood in northeast Kano.
- Jan 24, Boko Haram militants attacked a police sub-station in Kano with small arms and improvised hand grenades.
- Jan 29, civilians were killed in crossfire between Boko Haram gunmen and police after attack on a police station.
- Feb 22, explosives and armed attackers hit a military checkpoint in Kano that results in a gun battle.
- March 9, a police station in Kano was reportedly attacked by gunmen that also threw explosives at the security post.
The similarities are striking. The large scale, mass casualty events of March 18, 2013 and January 20, 2012 were both followed by a series of aftershock events that included shootouts, bombings, and suicide attacks. Both post-event periods saw security services as primary targets but included direct and collateral civilian casualties.
Rapid, Actionable GeoTemporal Intelligence
The intelligence gathered above provides a series of guideposts for crisis management in Kano:
- Boko Haram attacks against Christian targets were breaking out across the country at the time of the bus depot bombing so locations close to such sites should be avoided.
- Attacks appear to be focused in areas of north and east Kano where lower density and accessibility to major city arteries serve as an advantage to transporting attackers.
- Aftershock events should be expected following large scale attacks as Boko Haram hits at security forces using both small arms and explosives.
Combining pre- and post-event imagery of disasters with web intelligence of the same crisis-hit locations provides security teams an incredible depth of information at a rapid pace. The complementary intelligence provided by DigitalGlobe and Recorded Future supports security teams managing emergency planning, risk assessment, monitoring of staging areas and emergency response, damage assessment, and recovery.
For more information, see DigitalGlobe’s FirstLook and Recorded Future’s security applications.
Related