The Iranian-Saudi Conflict and Its Cyber Outlet
Analysis Summary
- Cyber warfare is an increasingly prominent aspect of the Iranian-Saudi hegemonic rivalry in the Middle East. Cyber attacks offer new revenge (e.g., 2012 attack on Saudi Aramco) and propaganda opportunities in this long-running “cold war” type conflict.
- Following Saudi airstrikes in Yemen during late March, the Iran-Saudi cyber conflict escalated. OSINT reveals a rapid exchange of website defacements and social media account hijackings between Saudi and Iranian hackers during mid-April. This period began when pro-Saudi hackers, unusually the aggressors, attacked Fars News Agency’s website on March 31. This incident appears to have spurred pro-Iranian hackers into action, as detailed below.
- The Yemen Cyber Army (YCA) emerged in mid-April. Unknown prior to its attack on Saudi newspaper Al-Hayat, the group has since been linked to a data breach at the Saudi Foreign Ministry of Foreign Affairs. The timing of YCA attacks, its communications footprint (Fars News “exclusives” and NewsQuickLeak.ir), and the tagline “Cutting Sword of Justice” used in the Saudi Aramco attack suggest, at a minimum, coordination with Iranian actors.
Among the numerous rivalries and conflicts in the Middle East, the Iranian-Saudi is one of the most unusual and unique. Stretching over several decades, it seems that this rivalry has it all – neighbouring countries with different religions, languages, culture, and history; two nations – Shiite (Iran) and Sunni (Saudi Arabia) – Persians and Arabs – competing against each other for hegemony over the Middle East.
Remarkably, this conflict confirms that it does not necessarily take a physical army and a ground confrontation to make an actual war. Over the years, the nature of this conflict has evolved and occasionally flared up; it involves diplomatic efforts against each other, gathering alliances, a public and underground involvement in the other’s political scene, indirect confrontations by supporting opposite powers in the region (as is currently the case in Yemen), and taking opposing and severe financial measures in order to weaken the rival’s stand. Nevertheless, the situation had never escalated to a real direct confrontation – it was always “behind the scenes” – until cyber warfare was introduced to the scene.
Iran vs. Saudi Arabia: Cyber Abilities and Targets
During the last five years or so, Iran became a major player in the cyber landscape. Individuals and hacktivist groups, some of which are suspected to be backed by the Iranian government, have carried out damaging and sophisticated attacks.
The image below demonstrates large numbers of cyber attacks reportedly committed by Iranian hackers (both hacktivist and allegedly state sponsored) during the period from mid-2010 to the present. Of note, the timeline is focused on countries targeted and does not regard Iranian attacks on individual organizations and companies.
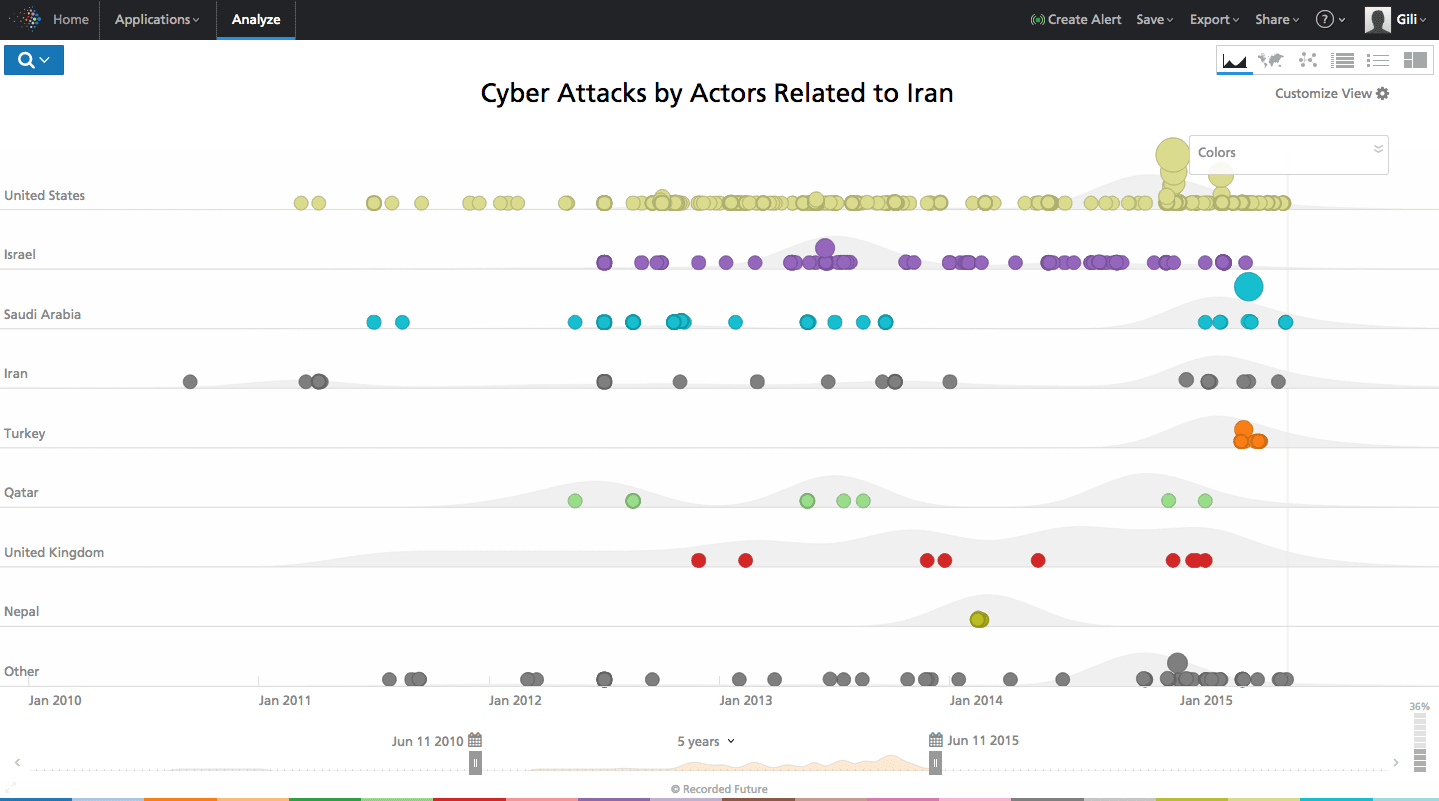
Above: Cyber attacks committed by actors related to Iran in the past five years.
It is clear that Iran’s cyber attempts are aimed towards a large number of countries, many of which are in political conflict with Iran, and some without. Looking at this list, it is notable that Saudi Arabia is one of Iran’s most targeted countries, alongside the U.S. The most significant single attack against Saudi assets attributed to Iranian hackers targeted oil company Saudi Aramco. Saudi assets were also targeted as part of a longer Iranian cyber campaign dubbed Operation Cleaver.
Comparatively, Saudi Arabia is far behind in outward attacks attributed to its government and/or hacktivists. Looking at the following image, we can see that there is much less activity with country specific targets reportedly originating in Saudi Arabia.
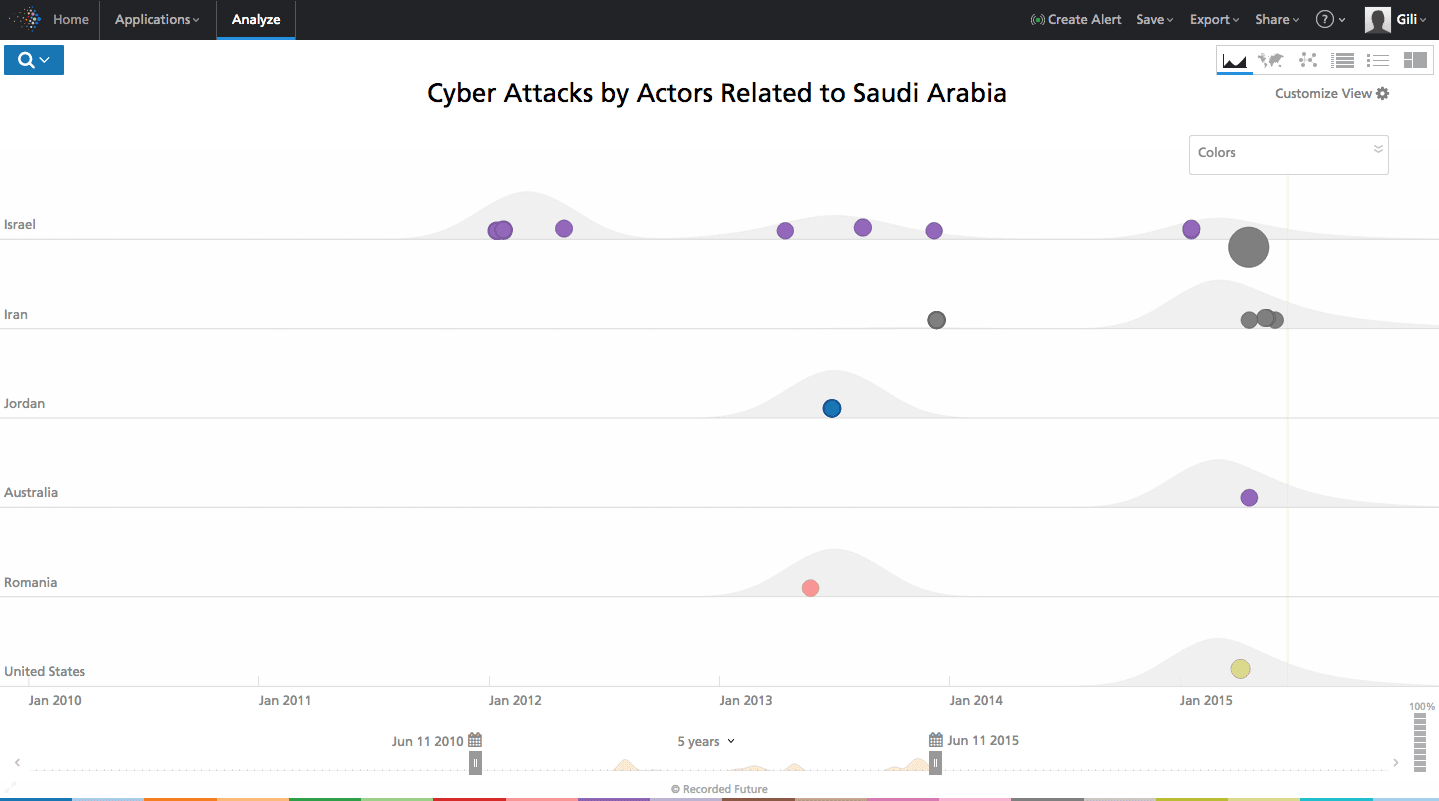
Above: Cyber attacks committed by actors related to Saudi Arabia in the past five years.
Comparing the attacks of both of these countries on each other shows that there are more attacks by Iran on Saudi Arabia than vice versa. Even taken altogether, the number of unique events is fairly small; many of the dots on the below timeline show follow-on reporting to the Aramco incident. These two countries, until very recently, don’t have a significant history of publicly waged cyber warfare.
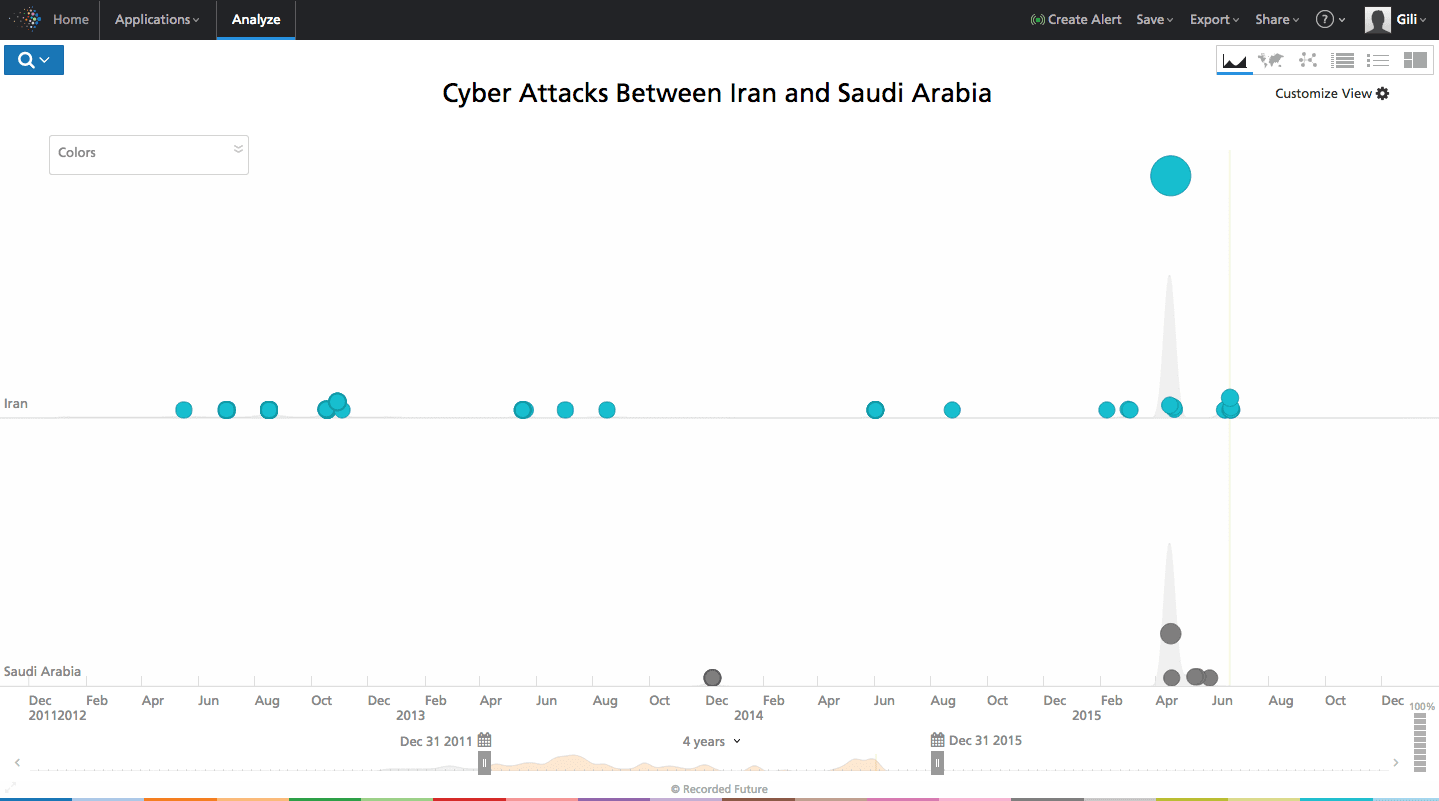
Above: Comparison of Iran’s attacks on Saudi Arabia, and Saudi Arabia’s over Iran.
The imbalance that exists may be partially explained by Iran’s demographic advantage: While only 30% of Iran’s citizens have Internet access, this amounts to 23.5 million users, significantly more than the 60% of the Saudis who have Internet access – a total of 17.28 million users.
Furthermore, Saudi hackers focus some of their efforts domestically, participating in operations such as “#opSaudi” – an ongoing campaign by SaudiAnonymous in protest against the Saudi regime. This phenomenon does not happen in Iran in such a large scale.
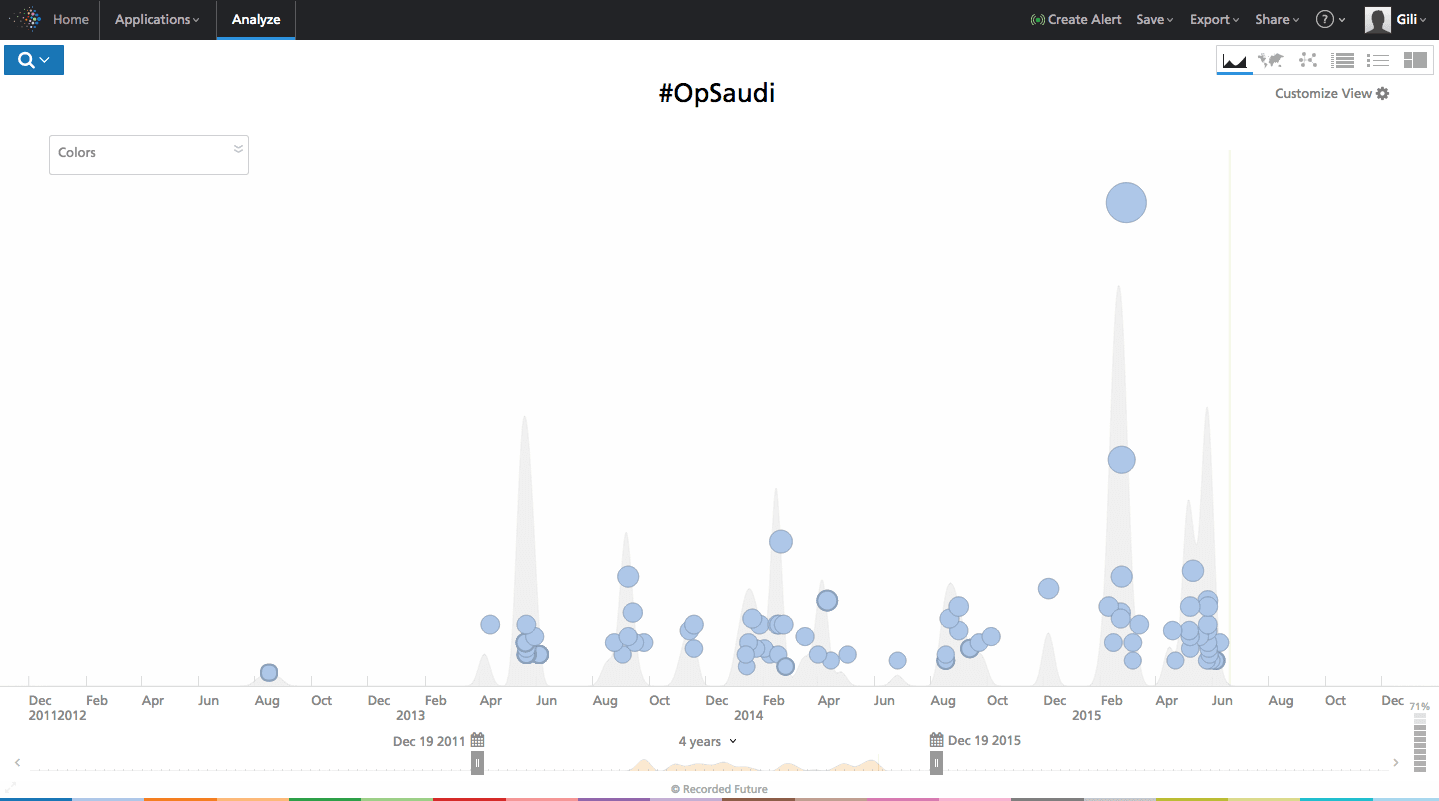
Above: Cyber attacks on Saudi-Arabia during #OpSaudi, most of which are from within Saudi Arabia itself.
Another explanation of the difference between Iran and Saudi Arabia on the cyber front is that while Iran mostly acts alone in the cyber arena, Saudi Arabia is said to have some strong allies that share its geopolitical interest. A claim often made by the Iranians is that the Saudis sometimes tend to let other countries do their “dirty work” in their stead.
Present Time Events: Cyber Propaganda in Yemen
In 2004, a Shiite uprising started in northern Yemen that continues today. Both Iran and Saudi Arabia are involved in this saga – Iran supporting the rebels, and Saudi Arabia advising and funding the Sunni-led Yemeni government.
The Saudi involvement escalated from mere diplomatic and political actions against Iranian involvement to airstrikes on Houthi rebels in Yemen at the end of March. This ignited a cyber war between hackers affiliated with the two countries.
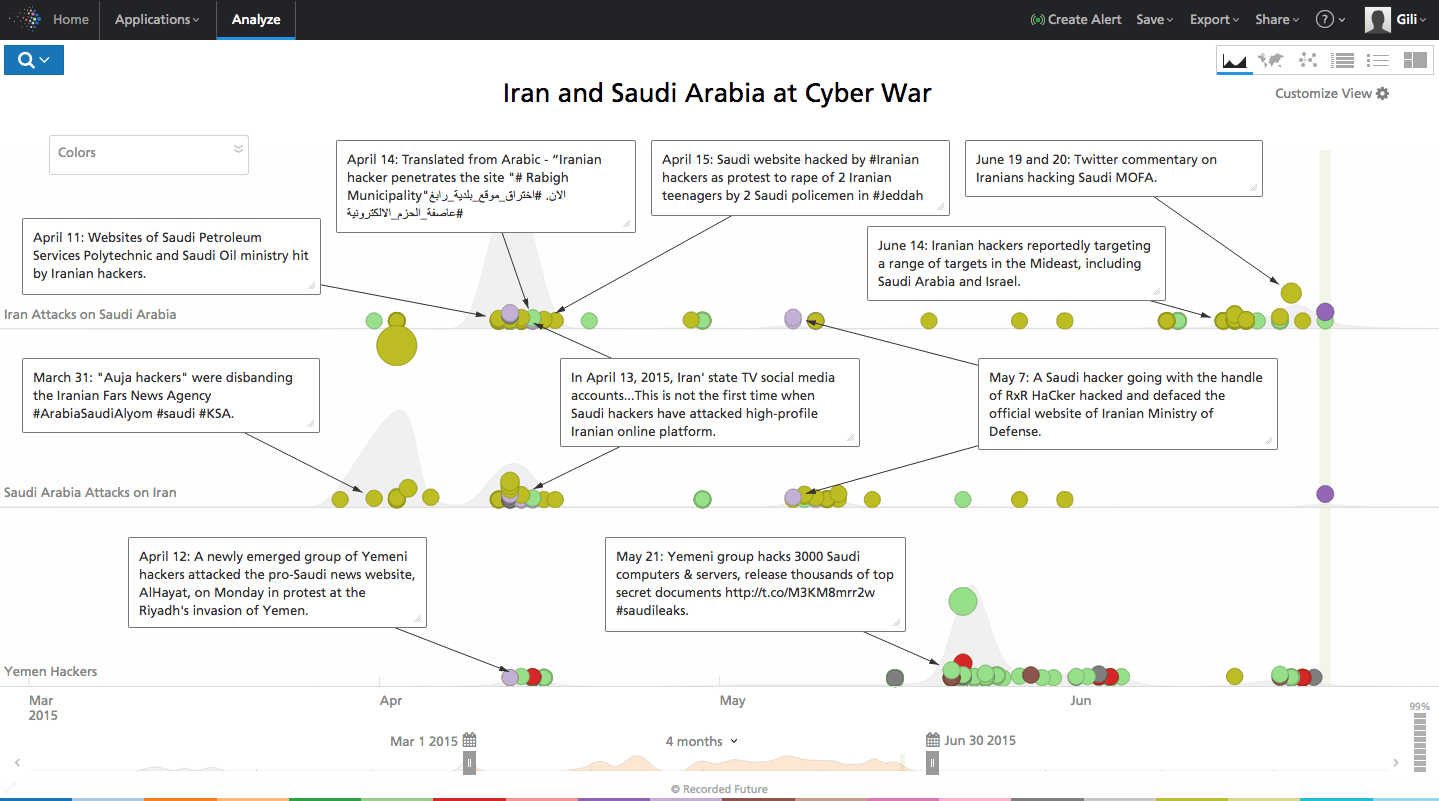
Within a week of the first airstrikes, we see an alleged attack by Saudi hackers on Iran’s Fars News Agency website. This incident, at the time an isolated act of propaganda against a news agency widely considered to be the Iranian government’s news outlet, was only the beginning.
Soon a rash of hacktivist operations spread. For example, on April 13 an Iranian state TV network’s (Al-Alam) Twitter account was hacked and published a false announcement of the death of the Iranian-supported rebel leader. The YouTube channel of Al-Alam was also hacked and played a song praising the Saudi king, while later in the month Iran’s Ministry of Defense website was defaced by a Saudi hacker.
On the other side, a Twitter account belonging to a small Saudi petrol company was defaced and tweets cursing the Saudi king were posted (those were since deleted). Other local Saudi news and municipal sites were also hacked.
Of the many attacks that took place in quick success, the most interesting was claimed by a new “Anonymous” style hacktivist group called the Yemen Cyber Army (YCA). Their first claimed attack was carried out on April 12 when they shut down Al-Hayat’s website (one of the largest pro-Saudi news sources in the world, published in London). The group claimed this was done in protest to the Saudi intervention in Yemen; they would soon claim an even more significant target.
Yemen Cyber Army and Its Links to Iran
As noted above, the Yemen Cyber Army hacked the Saudi news site Al-Hayat on April 12. This incident took place while other Saudi sites were also being targeted by pro-Iranian actors, all between April 11 and April 15.
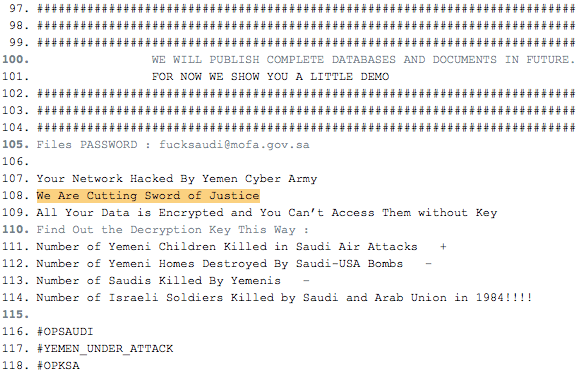
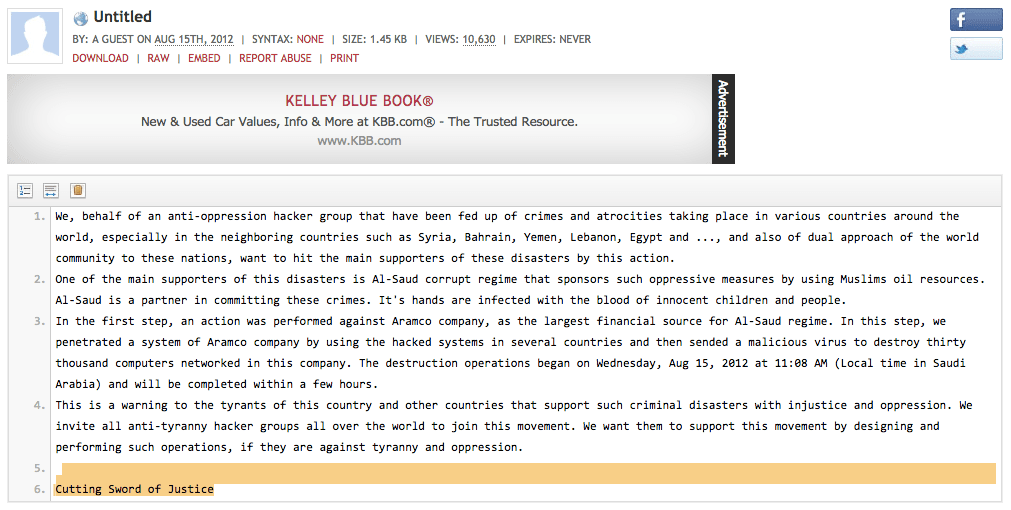
Interestingly, the YCA shows similarities to other Iranian hacker teams. The group included the phrase “Cutting Sword of Justice” in its Pastebin post claiming the Saudi MOFA attack (see cached page here and screen cap below). This is particularly interesting given the same unique phrase was used in a Pastebin post by attackers against Saudi Aramco in August 2012 claiming to be the “Cutting Sword of Justice.” The Aramco attack was conducted allegedly as protest against Al-Saud regime policies; this phrase appears in very few other places on the Web and seems to be distinctive to these attacks.
Like Qassam Cyber Fighters, Parastoo, and the Iranian Cyber Army, the YCA has no presence on popular social media outlets like Facebook and Twitter. This is extremely odd for a hacktivist group seeking support for its cause.
The YCA uses the website QuickLeak.ir, which is similar to Parastoo, to dump data breach content and communicate. The site otherwise does not see much in the way of posts from hacktivist groups. Lastly, it’s worth pointing out that there was NO activity by Yemeni cyber groups visible in OSINT prior to the sudden emergence of the Yemen Cyber Army.
The Al-Hayat hack was first reported by Iran-based Fars News Agency in an “exclusive” report. The news outlet quickly emerged as the YCA’s mouthpiece. It again led with an “exclusive” a month later (May 21) when the YCA claimed it breached various Saudi government agencies, including the Ministry of Foreign Affairs. The full trove of information captured as part of this operation was ultimately published by WikiLeaks on June 19 on the three year anniversary of Julian Assange seeking asylum at the Ecuadorian embassy in London.
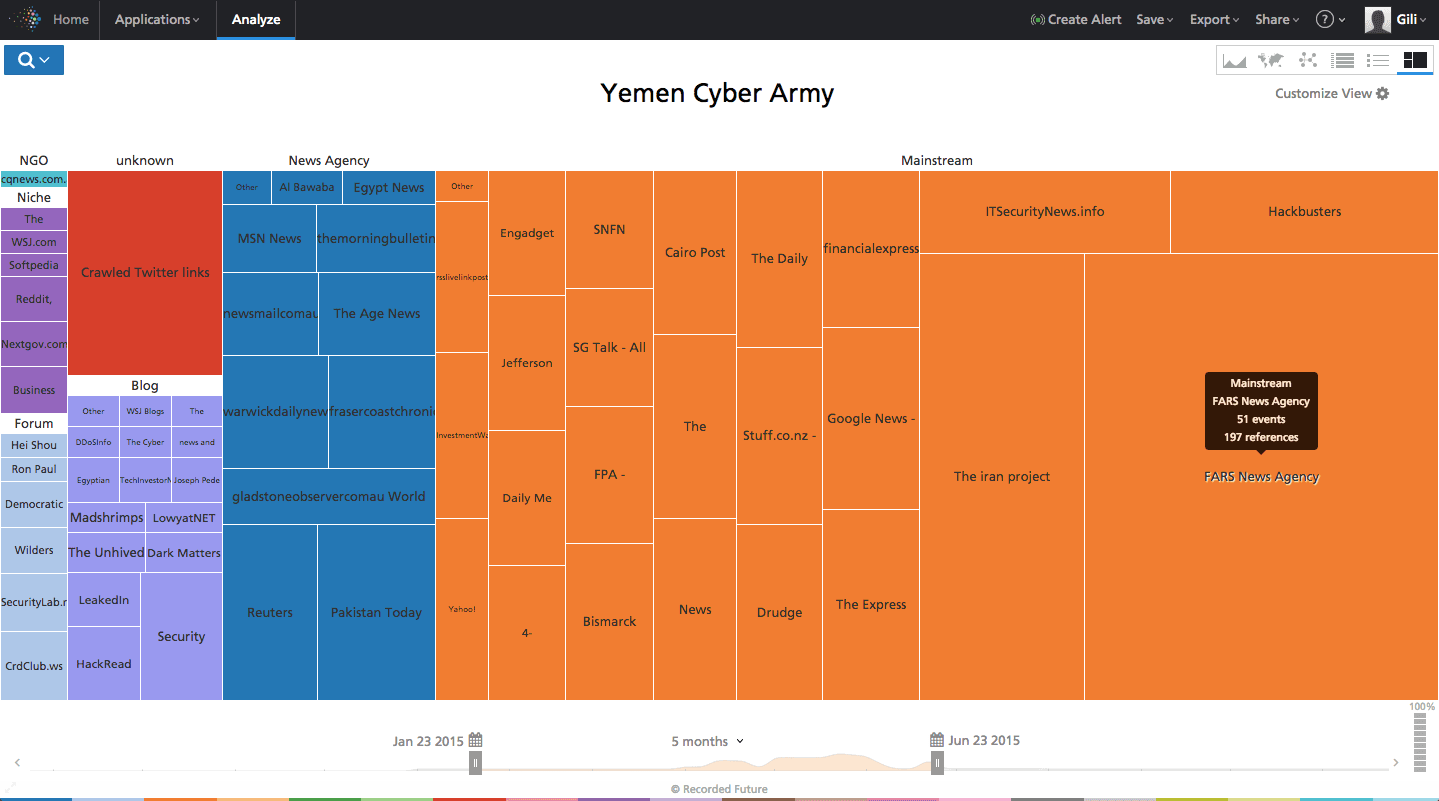
We also notice an outsize amount of reporting on the YCA by Fars News (seen below). It’s far and away the most prominent source outside of social media posts to report on the YCA’s activities, and as noted above, repeatedly claims the YCA activities as “exclusive” reports.
There’s no “smoking gun” in OSINT that allows us to directly link the Yemen Cyber Army to Iranian actors. However, if the attacks are being conducted by Yemeni not Iranian hackers, coordination with Iranian actors seems highly likely given the timing of the YCA’s efforts and its close coordination with Iranian media.
The case perfectly demonstrates how cyber is perfect for conducting (or furthering) proxy wars. Attribution can be difficult, and there’s a low barrier to effective action given technical training, provision of infrastructure, and strategic guidance. As the current case of Yemen demonstrates, the continued struggle for dominance in the Middle East between Iran and Saudi Arabia now finds both its physical and cyber outlets.
Related
