Turbocharge Your Threat Hunting Capability With Intelligent TTP Alerting
Every hour of every day you are either hunting or being hunted. The only question you have to ask is which side do you want to be on?Eric Cole, PhD, SANS Analyst and Network Security Expert
86% of IT professionals say that their organization is now involved in some kind of threat hunting. Today, businesses are increasingly looking to combine an effective defense against attackers with proactively identifying the tactics, techniques, and procedures (TTPs) of threat actors.
Traditionally, investments would be made in technology and security professionals expected to work with that technology to defend a network. Moving to a posture we would describe as an active cyber defense is driving a change to the role technology plays in combating risk. A finer balance between the skills of people and the capabilities of technology must be struck if threat hunting is to become de facto in cyber security strategy.
IT security professionals recognize that their goal is no longer just to respond and stop threats but also to find adversaries already in the network. Most organizations are investing effort in this way already and it certainly helps to minimize the amount of damage and loss caused by an attacker. But responding to known indicators of compromise (IOCs) to identify threats is just the start of what’s possible with the right threat hunting people and tools in place.
To illustrate this point, seasoned computer security professional David Bianco created the “Pyramid of Pain.”
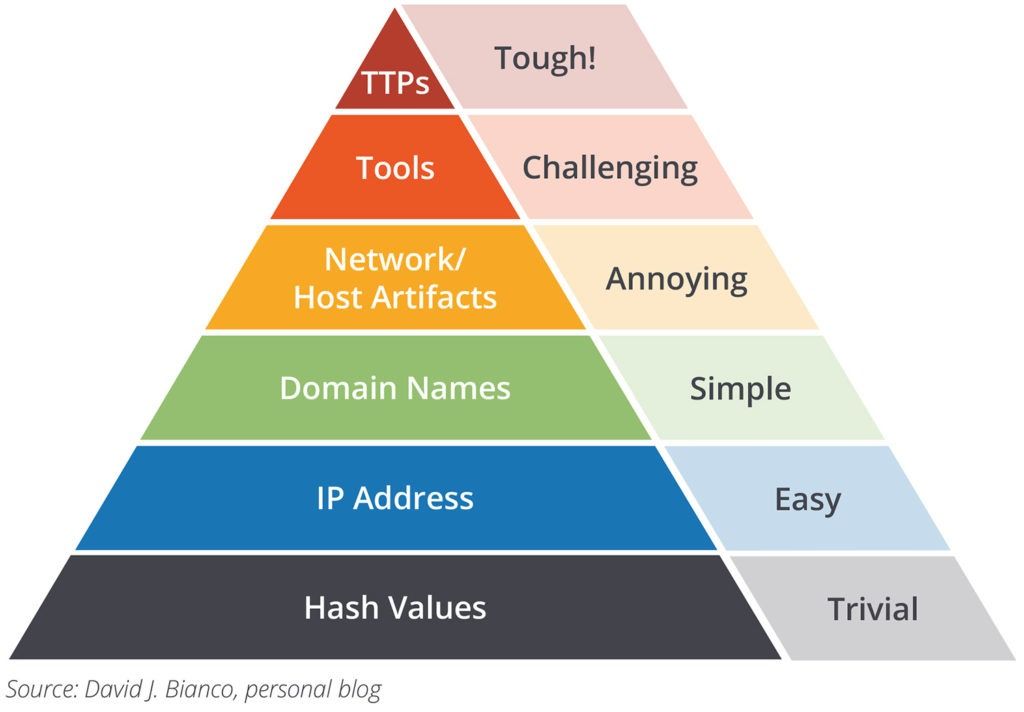
What the pyramid is showing here is although adversary TTPs are the most difficult indicators to detect and verify, they're also the most useful for implementing new security controls.
Recorded Future can be used for powering proactive analysis of new threat actors and TTPs, including identification of new and evolving malware and exploit kit modifications as well as applying intelligence from criminal forums.
Recent improvements in Recorded Future technology are based on a simple methodology for alerting on potential new TTPs:
- Maximize (wide) the hunting criteria
- Minimize (narrow) the context
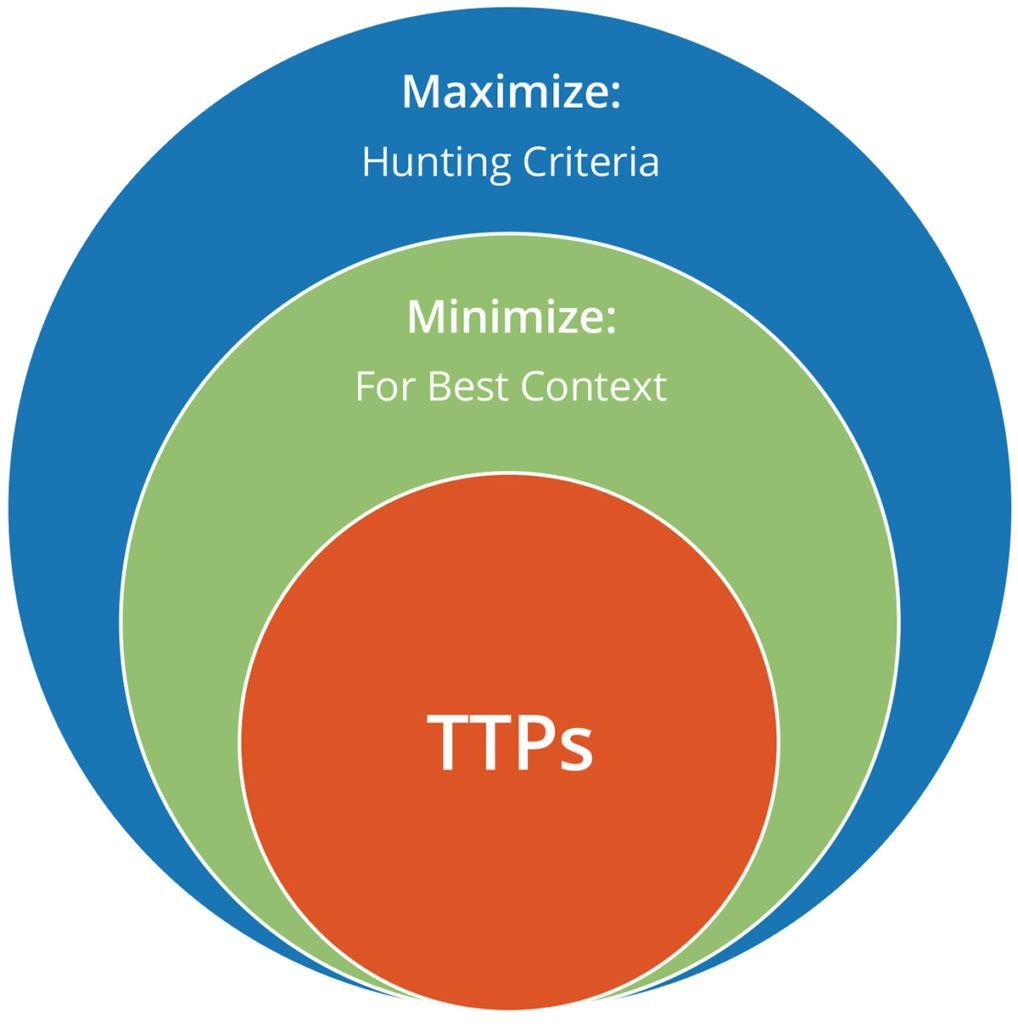
Maximize: Hunting Criteria
We’ve created broad lists of hunting terms and formalized them as recognized entities in Recorded Future. These entities belong in one of five current categories which represent individual ontologies:
- Technology building blocks
- Malware
- Fraud
- Red team
- Control systems
Each ontology is a good place to start hunting, depending on the topic of interest. “Technology building blocks” is the widest set of criteria (terms apply to technologies, programming languages, protocols, etc.) but will also ensure wider coverage of potential new TTPs.
Minimize: For Best Context
Now we can constrain the ontologies above to the most granular media types and languages in Recorded Future to produce maximum fidelity with minimum noise.
For example, we alert on the red team ontology daily, but only within forums, paste sites, and code repositories because that's where TTPs are most likely to appear. We can further constrain the context by adding a second criteria which is language.
So for the red team ontology, we alert daily on paste sites in multiple languages separately (including Arabic, Farsi, French, Spanish, Russian, Chinese, and English). We do the same for forums and code repositories. If all seven language alerts fire across all three media types then we receive 21 alerts for that ontology.
Below are a couple of examples to show this methodology in action.
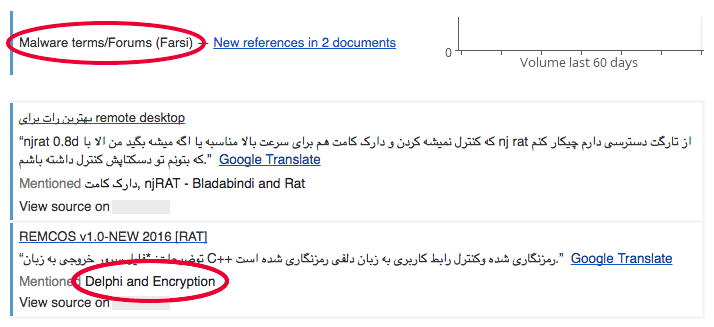
The alert above is configured specifically for malware entities that appeared in a forum(s) AND were written in Farsi (in the past 24 hours). This particular alert fires a few times per week, is extremely high fidelity, and easy to review quickly. In this case, the new Remcos RAT was identified because of references to the “Delphi” and “Encryption” entities.
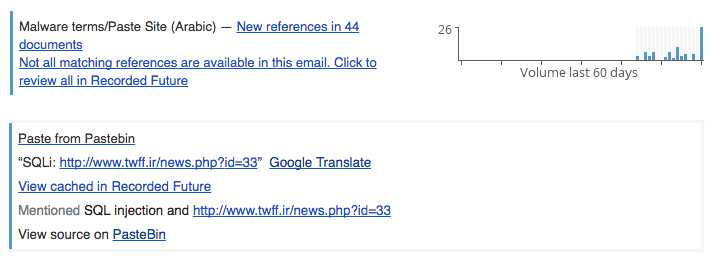
In this second example there are a greater number of references (in the full alert), but also potentially useful information in the form of an Iranian website (twff.ir) that was successfully attacked via SQL injection by a group of Saudis who posted the resulting database to Pastebin.
English language alerts are obviously the largest and when combined with “technology building blocks” and any media type (forums, paste sites, or code repositories), there are a greater number of results requiring analysis.
If you have the analyst horsepower to review daily TTP alerts, these ontologies will produce new TTPs. The ontologies aren't set in stone, they're merely pre-configured starting points. You can add or subtract from the ontologies as you see fit to refine your own hunting methodologies.
Read our previous blog post to see how this methodology has been used to uncover and analyze Cknife, a new web shell originating in China.
Get Started
Would your security team benefit from understanding threat actor TTPs? See this alerting improvement in action today by requesting a demo of Recorded Future.
Related