How Dragos Protects Industrial Control Systems With Threat Hunting
Editor’s Note: The following blog post is a summary of a presentation from RFUN 2018 featuring Thomas Pope, ICS threat hunting subject-matter expert and adversary hunter at Dragos.
Key Takeaways
- Industrial control system (ICS) security is a highly specialized skill set. Because industrial environments are so different from information technology (IT) environments, threat intelligence for both IT and operational technology (OT) environments is critical.
- ICS intrusions start with IT, beginning by breaching a security stack to gain access to the IT environment and finding “soft spots” that lead to the OT environment.
- Dragos produces unique threat intelligence for ICS industries, and pivoting via Recorded Future can dramatically speed up investigations.
Industrial control system (ICS) security is unlike traditional information technology (IT) security. Very few people possess the necessary skill sets to secure ICS, and the threat landscape is largely uncharted. Threat intelligence for IT and operational technology (OT) can help bridge that knowledge gap and be a crucial resource for defenders.
Traditional threat intelligence works well for IT environments, but what security solutions can be used to effectively secure OT environments?
Late last year, we held our seventh annual Recorded Future User Network (RFUN) conference in Washington, D.C. During the conference, attendees enjoyed a presentation on industrial control system threat hunting by Thomas Pope, adversary hunter at Dragos.
Pope explained the intricacies of a highly specialized industry, the unique threats it’s facing, and how to effectively conduct threat hunting for industrial control systems.
ICS Security: A Highly Specialized Industry
To kick off the conversation, Pope explained that because very few people specialize in industrial control system cybersecurity, the threat landscape is largely unknown. The industry is so specialized, in fact, that Dragos leadership runs non-security employees through training courses to ensure organization-wide understanding of their mission. Pope explained that because the threat landscape is so obscure, it’s vital to share knowledge gained through IT and OT environments and threat intelligence with both employees and customers.
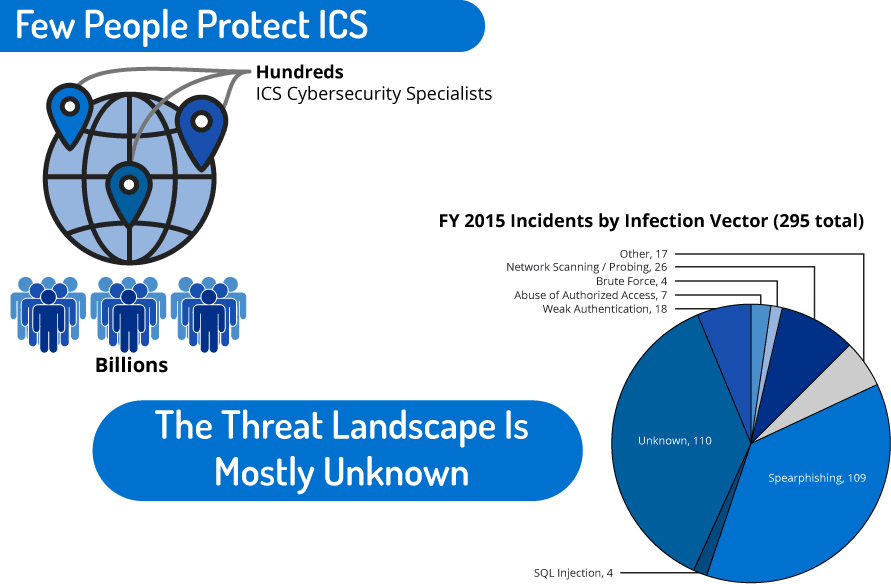
Very few people have expertise in industrial control systems.
Industrial environments are not the same as traditional IT environments that allow for consistent software patches and upgrades. A single, minor change within an industrial network could trigger a chain of damaging events. Consequently, legacy plant control systems commonly run out-of-date operating systems or a specially-designed configuration incompatible with standard IT security packages.
As Pope explained, “A lot of times, you can’t insert yourself into an OT network because things start breaking. It’s very sensitive. A lot of vendors don’t let you patch, and you’re not allowed to put antivirus [software] on most equipment. Sometimes, you patch something and it doesn’t come back up. Then you don’t have use of that asset until a server is rebuilt. A lot of this is unknown just because there is no visibility in the space.”
IT and OT Environments: The Criticality of Threat Intelligence
Early on, the security industry lacked threat intelligence collection; the first known threat actor that engaged in large-scale cyber campaigns was APT1. As time went on and technology advanced, a clear spike in attack frequency occurred, which included ICS-specific targeting, as shown in the ICS threat “Hockey Stick” graph Pope shared in his presentation.
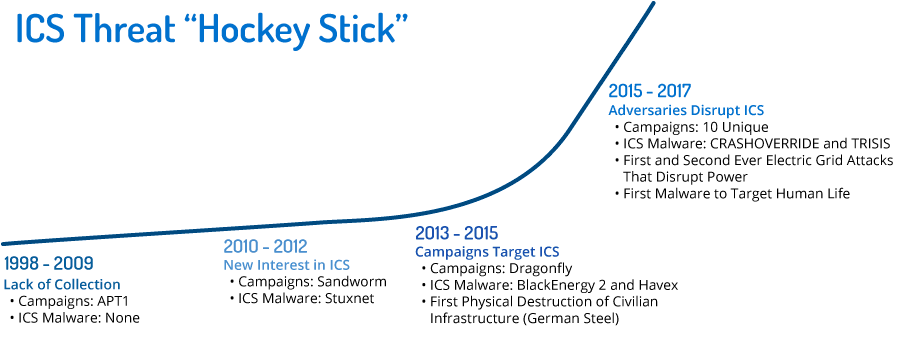
“You can see there wasn’t much in ICS, and then you just see a spike,” Pope said. “Everybody knows about Stuxnet. It’s the most studied piece of code in history … Everyone just tears it apart and wants to know more. Then, you see a sharp spike starting after DragonFly with BlackEnergy and Havex. You see that in 2015, then in 2016, CRASHOVERRIDE happens. Ukraine gets picked on again and the power goes out in the middle of winter. Then you can just see it keep going up from there.”
Threat intelligence for both IT and OT is critical for increasing visibility and understanding how to defend networks against evolving threats. Dragos provides the only ICS-focused threat intelligence product that can help asset owners and operators effectively accomplish that.
OT Environment Case Example: TRISIS
Not only is the ICS threat landscape relatively uncharted, but cyberattacks against infrastructure are highly dangerous. In 2017, the TRISIS attack targeted safety systems at an oil and gas facility in Saudi Arabia. Safety systems are built to shut down equipment when unsafe conditions are encountered, and protect the ICS environment and people within it. They communicate with multiple systems along concurrent channels, and determine whether the equipment can run or identify issues that may require the system to shut down.
TRISIS represented a shift in adversary behavior because a cyberattack specifically targeting safety systems could cause catastrophic destruction and, potentially, loss of human life. In the case of TRISIS, the system shut down safely while the attackers were probing the SIS.
The only reasons to target a safety system, Pope said, are destruction of equipment with the operator to incur substantial financial losses — or possible death to operators, which would shut down operations for weeks, if not months.
The TRISIS malware was specifically tailored to affect the safety system in the target environment. However, there is now a blueprint for attackers to leverage similar attacks against other safety systems with the necessary knowledge of a target environment.
OT Environment Case Example: German Steel Mill Attack
Pope also reviewed the first physical destruction of civilian infrastructure — a German steel mill in 2014.
The incident began when attackers accessed the target’s corporate network through spearphishing emails before pivoting to the operational network. Attackers compromised control system components, which caused massive amounts of damage to a furnace at the plant. The attack was not originally treated as a cyber event until all process causes were exhausted.
OT Environment Case Example: CRASHOVERRIDE
In 2016, attackers targeted a transmission substation in Kiev, Ukraine and deployed CRASHOVERRIDE malware. This is the first malware framework designed and deployed to specifically attack electric power grids.
CRASHOVERRIDE was unique: its modular design allowed the adversary to target certain protocols within the ICS environment specific to Ukraine and the European power grid. The modularity lends itself to attacks in other parts of the world, once protocols are known and included in the framework.
Identifying Unique ICS-Targeting Groups
Behaviors developed by threat activity groups designed to disrupt ICS are complex and persistent. Hackers are also becoming more sophisticated with obfuscation methods, even as they use some of the same malware. To provide context, Pope discussed some of the hacking groups that Dragos is actively tracking, looking at their usual targets and methods of attack.
CHRYSENE, for example, is a very active group targeting oil and gas operations, particularly in the Middle East, though they have branched into Europe as well. CHRYSENE is unique because they use IPv6 and 64-bit malware. While the use of 64-bit malware still persists, it is rarely seen in combination with IPv6. Pope said analysts should understand that these patterns aren’t immediate identifiers. It is necessary to use other behaviors and observed tactics, techniques, and procedures (TTPs) to properly categorize activity groups.
Ultimately, attribution is difficult, and Dragos does not attribute this to individuals or states; rather, the company collects and categorizes behaviors by activity group organized to be most useful to defending an ICS network.
Intrusions begin in IT, although the argument that intrusions stem from OT is often made. Pope’s response to this line of thinking is clear: “That’s because someone plugged an outside internet connection directly into the plant.”
Often, intrusions begin by bypassing a security stack — for instance, via stolen credentials or remote access to a target device — and accessing the IT environment to find soft spots that lead to the OT environment. Commodity malware can run rampant without sanitization between networks, and Dragos predicts that this will continue to be an issue for operators in the ICS space.
Integration of Dragos WorldView and Recorded Future
This brings us to the solution. Given the hazardous potential of ICS environments, Dragos and Recorded Future joined forces to create a solution which would integrate both IT and OT intelligence. While Dragos is focused on OT, Recorded Future is an excellent resource for IT, giving clients more complete coverage with both.
Dragos provides an ICS-specific dashboard for clients to review targeted threat information, while the integration of Dragos WorldView and Recorded Future brings additional context to IOCs and activity groups.
WorldView, the Dragos intelligence offering, is designed exclusively for ICS environments.
Pope explained, “If companies with a heavy industrial component are being targeted by a phishing campaign, we’ll dig into the actual intention. Was it commodity malware, information stealing? Were they looking to pivot and steal designs and plans helpful in future operations from workstations? Or were they trying to penetrate control networks?”
In explaining the value of ICS-specific threat intelligence, Pope covered the primary use cases for Dragos WorldView:
- Delivers actionable threat intelligence for companies with ICS environments
- Tracks activity groups and campaigns against ICS asset owners and operators
- Publishes in-depth malware and vulnerability analysis
- Arms defenders with defensive recommendations to mitigate threats
- Distributes reports targeted at all levels of security and OT, from analysts to the C-Suite
To learn more about how Recorded Future can help organizations better understand and prevent threats, request a personalized demo today.
Related
