Fujitsu UK Tracks Dridex, Using Recorded Future
Companies contend with an ever-changing security landscape, which brings a range of strategic and operational demands including continuously evolving external and internal threats, the risk of data leaks and loss of intellectual property, and increasing compliance and regulatory requirements.
To help companies manage and mitigate these risks, Fujitsu UK, a managed security services provider, uses its own expert professional services capabilities combined with Recorded Future to provide customers the 24×7 coverage necessary to protect their businesses.
Rob Norris, Director of Enterprise and Cyber Security at Fujitsu UK said it well, “Working with a strong and established Threat Intelligence partner such as Recorded Future will only enhance our already mature security offerings portfolio and allow customers to gain value from an excellent Threat Intelligence product and our cyber security experts.”
Fujitsu UK shared with us an example of how they use Recorded Future’s real-time threat intelligence to gain insight into Dridex, a strain of malware targeting banks, to enable proactive defense against the malware. The company’s Lead Threat Intelligence Analyst, Cyber Threat Intelligence – SOC, Bryan Campbell, wrote the following use case.
—
Past – Tracking Dridex Developments Accurately
We began to closely observe Dridex in Q4 2014, and with that in mind, we needed a way of observing the development of Dridex. The dashboard seen below enabled us to do so. We observed the evolutions of the malware in relation to technical changes from SSL and UAC bypass to Windows Security. Below is a timeline of known activities around Dridex from 2014 to present day. The ability to see its progression allowed Fujitsu to have a clear view of what had already occurred and anticipate what to expect from the campaigns.
Dridex is a descendant of the ZeuS botnet and was enhanced by its developers to use its backbone to spread. The evolution of Dridex, along with other botnets and other continued daily campaigns, proved difficult to track without proper contextual insight and documented correlations among the campaigns; Recorded Future enabled us to track the development accurately and act proactively. The real-time threat intelligence analysis combined with its multi-year historical archive of facts provided both broad context and deep insight.
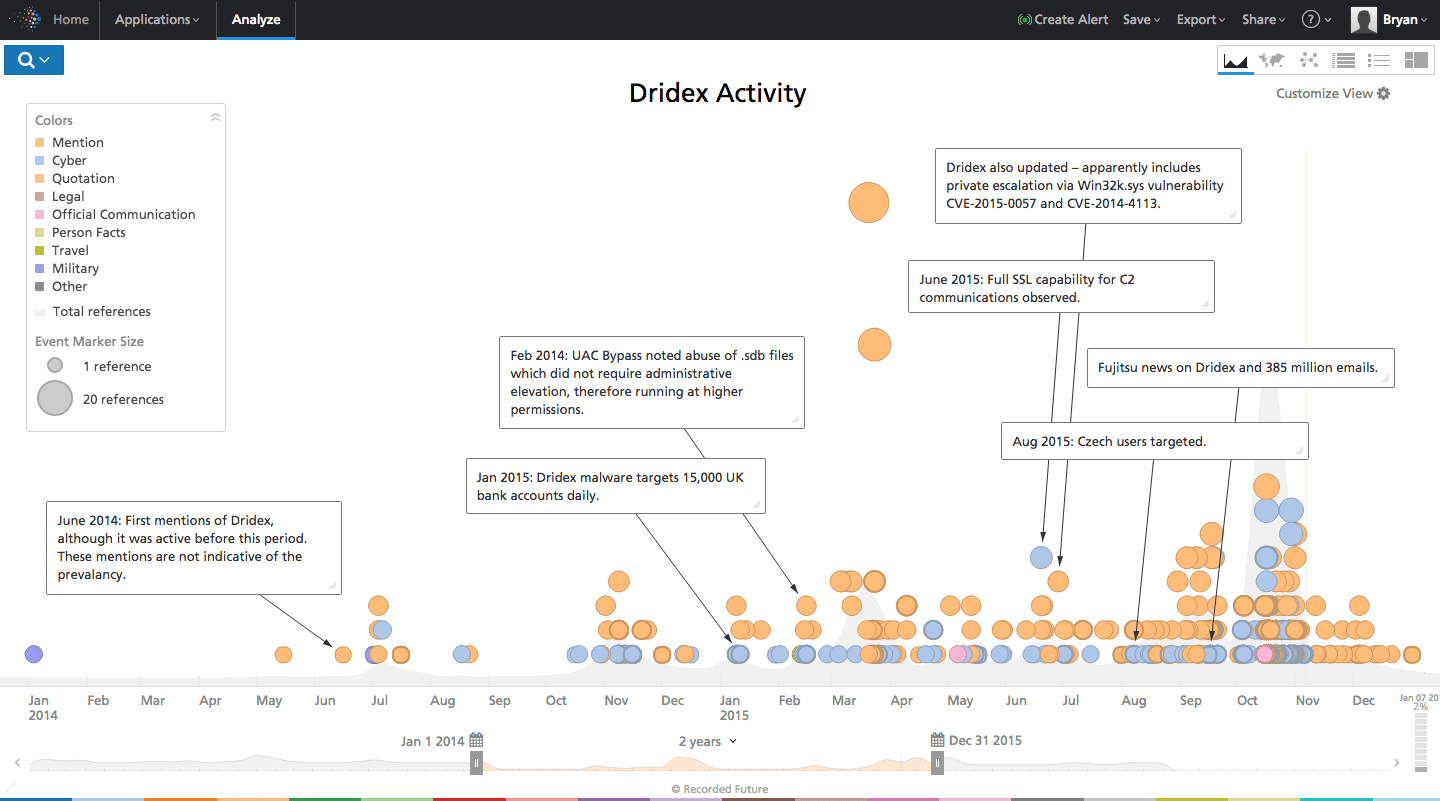
Tracking Dridex developments using Recorded Future.
Present – Acting With Agility
Dridex continues to be a threat despite the most recent media interest – as the publicized takedown has again given it a spotlight. We continue to observe the campaigns and report on Dridex’s capabilities, particularly against increasing numbers of banking targets, with more banks added to the bots’ configuration continually.
During 2014 and 2015, Dridex spread throughout Europe, targeting the UK, France, Spain, and the Czech Republic. We were able to proactively inform our colleagues of the Dridex capabilities by leveraging our knowledge of the botnet, thanks in part to the threat intelligence we received from Recorded Future. Despite the rising challenges, including more banking targets and evolving campaign complexity, we were able to act with agility and provide advice to our clients on how to combat the botnet.
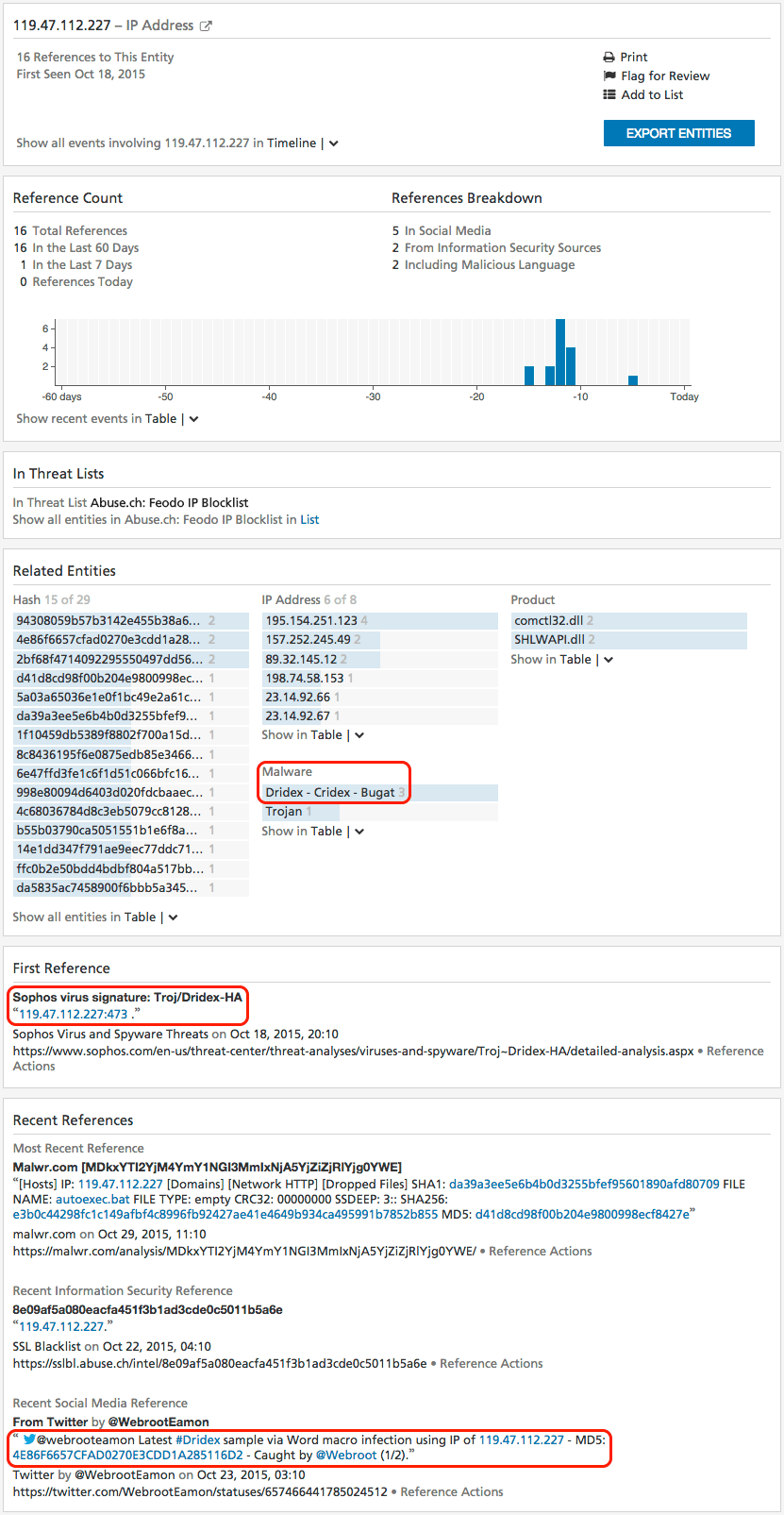
A Recorded Future Indicator Card provides immediate visibility and context into IOCs related to Dridex.
Future – Monitoring Crime Kits and Campaigns
Although Dridex is a P2P botnet and this gives it a great deal of resilience, the bot-herders will seek to monetize the botnet in other ways. Law enforcement gained access to a super node and sent an updated configuration to the victims, which then made the victims report into a sinkhole. However, the crime kits associated with the botnet are still up for sale and we’re still seeing daily campaigns, including new super nodes and the development of updated infection methods. Much like the ZeuS botnet, Dridex will evolve again, but this time we will be prepared.
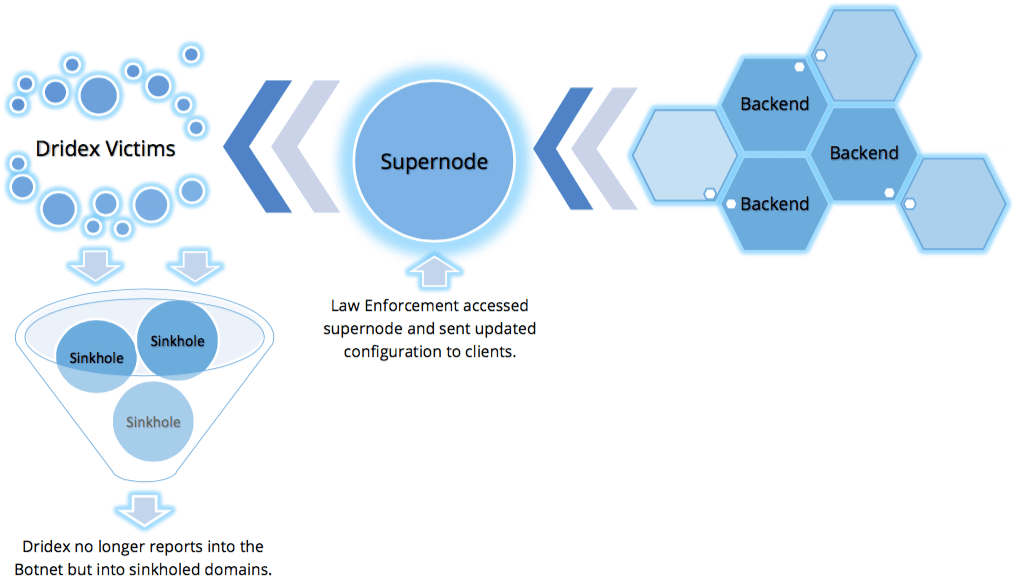
How law enforcement took down a Dridex botnet.
Paul McEvatt, Fujitsu UK’s Senior Cyber Threat Intelligence Manager and Distinguished Engineer summed it up nicely when he said, “Recorded Future has an excellent early warning system for our Security Operations Center. The product has been central to some of our cyber security investigations, particularly around Dridex allowing us to research various threats and utilize indicators of compromise to protect our customers.”
Related
