Understanding Accellion’s FTA Appliance Compromise, DEWMODE, and Its Supply Chain Impact


Editor’s Note: The following post is an excerpt of a full report. To read the entire analysis,  to download the report as a PDF.
to download the report as a PDF.
This report provides a high-level overview of the Accellion File Transfer Appliance compromise and analysis of the DEWMODE webshell employed in the resulting breaches. Insikt Group used open source research (OSINT), PolySwarm, malware analysis, and the Recorded Future® Platform to execute this research. The target audience of this research includes day-to-day security practitioners as well executive decision-makers concerned about targeting of third-party systems and software.
Executive Summary
The compromise of the Accellion File Transfer Appliance (FTA) file sharing service impacting nearly 100 clients of the company was enabled primarily by 4 zero-day vulnerabilities in the tool that allowed threat actors to place the DEWMODE web shell on victim servers and exfiltrate files from those servers. As of February 25, 2021, 13 organizations in multiple sectors (finance, government, legal, education, telecommunications, healthcare, retail, and manufacturing) and multiple countries (Australia, New Zealand, Singapore, the UK, and the US) have suffered data breaches as a result of the Accellion FTA compromise. Victim data has appeared on the website CL0P LEAKS, establishing a link between the operators of this website and the attackers behind the Clop ransomware. There are likely to be reports of additional victims in the near future, and we suspect that these victims will be part of additional industries and countries beyond what have already been reported. Clients using Accellion FTA in their environment are advised to update the software to version FTA_9_12_416 or later and employ Insikt Group’s recommended mitigations to look for related malicious behavior on these servers.
Background
On January 10, 2021, the Reserve Bank of New Zealand reported a data breach due to compromise of a third-party file sharing service, shortly afterward identified as Accellion. The bank released a statement about the breach a day later, in which they stated that the breach may have exposed commercially and personally sensitive information. Reserve Bank governor Adrian Orr said it had been advised by Accellion that the Reserve Bank was not specifically targeted and that other users of Accellion FTA were also compromised.
Shortly afterward, on January 12, Accellion stated in a press release that "less than 50 customers" were affected by a "P0 vulnerability" in its legacy FTA software. They further claimed that they first learned of the vulnerability in mid-December 2020, and that a patch was subsequently released "in 72 hours with minimal impact".
Key Judgements
- The Accellion FTA data breach was enabled by 4 zero-day vulnerabilities, with initial access gained through an SQL injection vulnerability, CVE-2021-27101.
- Based on the changes in statements from Accellion over the course of reporting on this campaign, the company may still not be fully aware of the extent of compromise associated with these vulnerabilities. Furthermore, based on the number of industries and countries that include clients of Accellion, we suspect that future reports of Accellion FTA exploitation will disclose more companies, industries, and countries than have previously been reported.
Threat Analysis
Within a few weeks after Accellion’s initial press release, multiple other companies disclosed data breaches that occurred due to exploitation of Accellion FTA. Additionally, data of victims of Accellion FTA compromise began to appear on the website CL0P LEAKS, establishing a link between the operators of this website and the attackers behind the Clop ransomware. Based on an updated number of potential victims disclosed by Accellion on February 22, and an expanding list of victims up to the time of writing (March 12), we expect additional similar reports to appear over the next month. The following timeline tracks new victim disclosures, security researcher analysis, and updates from Accellion itself.
- January 22 — Australian law firm Allens reports a data breach due to Accellion FTA compromise.
- January 25 — The Australian Securities and Investment Commission discloses that on January 15, it became aware of a data breach due to Accellion FTA compromise.
- February 2 — US law firm Goodwin Procter, the first non-Australian or New Zealand victim, discloses a data breach due to Accellion FTA compromise.
- February 4 — The Office of the US Washington State Auditor discloses a data breach due to Accellion FTA compromise.
- February 9 — Open sources report that the University of Colorado suffered a data breach due to Accellion FTA compromise.
- February 11 — Singaporean telecommunications company Singtel and Australian medical research institute QIMR Berghofer disclose data breaches due to Accellion FTA compromise. QIMR Berghofer claims it was asked by Accellion to implement an emergency patch on January 4; then on February 2, Accellion warned the institute that they might have been compromised.
- February 16 — US law firm Jones Day confirms a data breach due to Accellion FTA compromise. On its GitHub page, Accellion publishes descriptions of 4 vulnerabilities in its FTA software: CVE-2021-27101, CVE-2021-27102, CVE-2021-27103, and CVE-2021-27104.
- February 17 — Open sources report that Jones Day data has appeared on the CL0P LEAKS extortion website, introducing the possibility that other organizations compromised via Accellion FTA will face similar data exposure from these criminals.
- February 19 — US grocery chain Kroger discloses data breach due to Accellion FTA compromise.
- February 21 — Recorded Future data confirms the appearance of Jones Day data on the CL0P LEAKS website.
- February 22 — FireEye releases a blog detailing links between the Accellion FTA breaches and a group known as UNC2546, the cybercrime group FIN11, the operators of the extortion site for data stolen via Clop ransomware attacks, and a web shell called DEWMODE. On the same day, Accellion releases a statement that "out of approximately 300 total FTA clients, fewer than 100 were victims of the attack".
- February 23 — Canadian airplane manufacturer Bombardier and Australian government agency Transport for NSW disclose data breaches due to Accellion FTA compromise.
- February 24 — Recorded Future logs data exposures for Singtel and Bombardier on the CL0P Leaks website. Five Eyes members issue a joint advisory regarding ongoing attacks exploiting Accellion FTA vulnerabilities. The advisory states that impacted organizations are in "Australia, New Zealand, Singapore, the United Kingdom [from which no organizations have yet disclosed a data breach], and the United States". An open source report discloses that US health insurance company Centene is another victim of data breach due to Accellion FTA compromise.
- March 3 — The security firm Qualys announced that they had suffered a data breach from vulnerable Accellion FTA servers. CL0P LEAKS published screenshots of files allegedly stolen from Qualys containing data such as purchase orders, invoices, tax documents, and scan reports.
- March 6 — Flagstar Bank notified customers that they were impacted by the Accellion FTA compromise, who originally informed Flagstar of a security issue on January 22, 2021. Flagstar has now permanently discontinued the use of FTA. Flagstar states that as a result, customer data was impacted, although operations were not. Flagstar data was published on CL0P LEAKS on March 9.
Accellion’s commentary on the scope of potential exploitation has changed since their original disclosure. On January 12, the company stated that fewer than 50 customers were impacted; by February 22, the company had amended this to fewer than 100 out of 300 total FTA clients.
The graph below shows that the public sector has been most impacted by exploitation of the Accellion FTA vulnerability. However, based on the distribution of customer industries as publicized by Accellion, we suspect that the healthcare, finance, and energy sectors have been impacted more heavily than has been publicly reported.
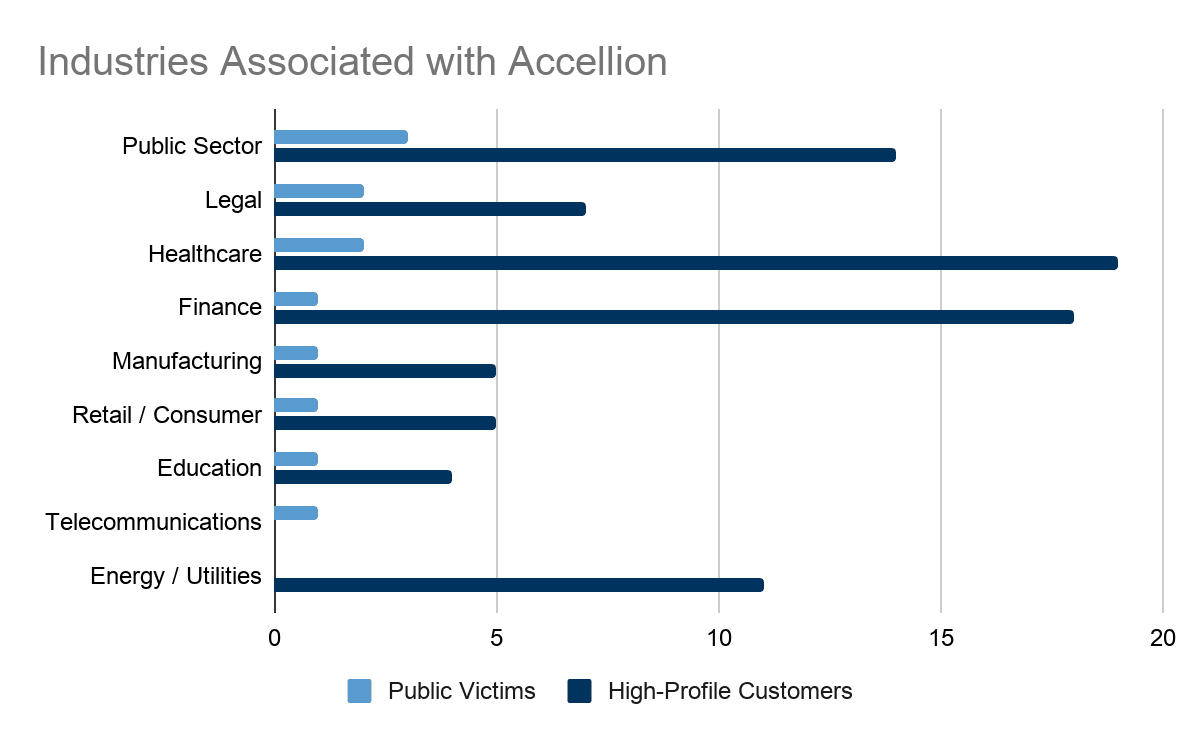 Figure 1: Distribution of industries for publicly disclosed victims of Accellion FTA vulnerability exploitation (light blue) versus distribution of industries for high-profile customers as listed on Accellion’s website (dark blue) (Source: Recorded Future)
Figure 1: Distribution of industries for publicly disclosed victims of Accellion FTA vulnerability exploitation (light blue) versus distribution of industries for high-profile customers as listed on Accellion’s website (dark blue) (Source: Recorded Future)
We anticipate that the countries identified by the Five Eyes report and our research as hosting victims of Accellion FTA compromise (Australia, Canada, New Zealand, Singapore, the UK, and the US) are and will continue to be the most impacted by this series of attacks based on the distribution of victims so far. However, we do not believe that these attacks are based on narrow targeting of these countries. Additionally, as the map below shows, there are several other countries that host customers of Accellion (and therefore potential victims of exploitation), including France, Germany, Israel, Italy, Japan, and the Netherlands.
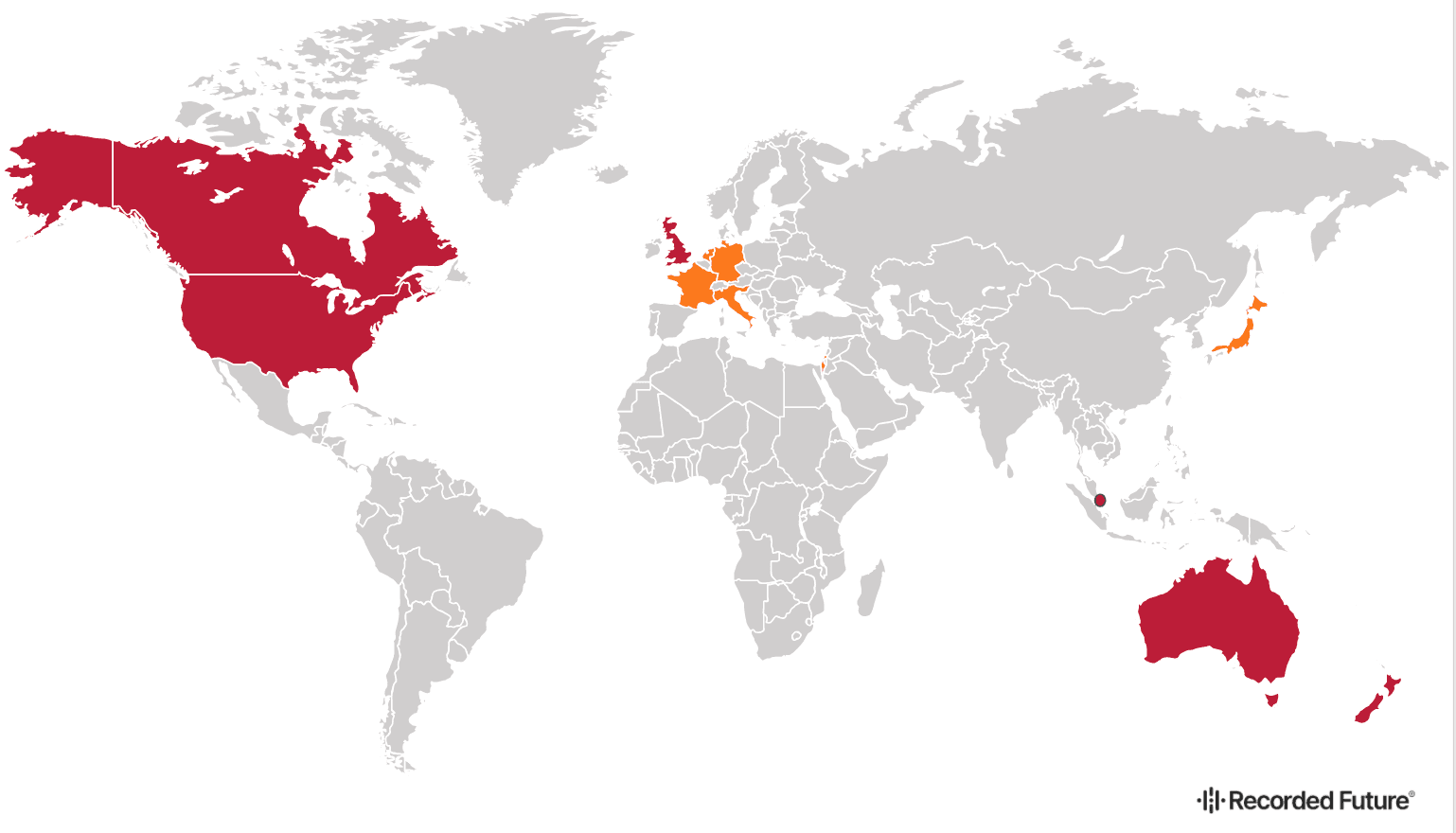 Figure 2: Countries impacted by exploitation of Accellion FTA. The countries in red (Australia, Canada, New Zealand, Singapore, the UK, and the US) are headquarters for confirmed victims of Accellion FTA exploitation. The countries in orange (France, Germany, Israel, Italy, Japan, and the Netherlands) are headquarters for other customers of Accellion as publicized on their website. (Source: Recorded Future)
Figure 2: Countries impacted by exploitation of Accellion FTA. The countries in red (Australia, Canada, New Zealand, Singapore, the UK, and the US) are headquarters for confirmed victims of Accellion FTA exploitation. The countries in orange (France, Germany, Israel, Italy, Japan, and the Netherlands) are headquarters for other customers of Accellion as publicized on their website. (Source: Recorded Future)
Mitigations
While TTPs used in the Accellion breach and in association with the DEWMODE web shell have become widely publicized, and threat actors may modify them to evade detection, Insikt Group advises the following mitigations:
Monitor third-party risk to your organization from this campaign. Potential monitoring parameters can include publicly reported cyberattacks against companies that use Accellion FTA, new references to leaked data on the CL0P LEAKS website, and threat groups or malware associated with UNC2546, FIN11, or Clop ransomware.
Accellion has released patches for all of the vulnerabilities associated with this breach, and organizations using Accellion FTA servers should update to version FTA_9_12_416.
If a system is running Accellion FTA, consider isolating the system from the internet until patches can be applied.
If malicious behavior is identified, CISA recommends resetting the “W1” encryption token and any other security tokens on the system.
Accellion’s FTA product will be reaching end of life on April 30, 2021. Clients using the product should consider alternative options for file-sharing platforms to migrate to as the EOL approaches for FTA.
If your organization was running a vulnerable version of Accellion FTA, an incident response investigation should be undertaken to determine whether there was a breach. The following methods may be used to examine log data for indications of a compromise.
Organizations should monitor for network requests associated with the DEWMODE web shell, including:
GET requests to /about.html?dwn=[encrypted path]&fn=[encrypted filename]
GET requests to /about.html?csrftoken=11454bd782bb41db213d415e10a0fb3c
GET requests to /about.html?aid=1000
According to CISA, there was an incident in which a large amount of data was exfiltrated on port 443 to 194.88.104[.]24 and another in which several TCP sessions had IP address 45.135.229[.]179.
The following file system events were associated with the breach:
Creation of “about.html” in /home/seos/courier or /home/httpd/html
Writes to the file /courier/oauth.api, where data contained matches the description of the eval shell, above
Accesses to /courier/document_root.html, or /courier/sftp_account_edit.php
Several modifications to logs contained in the Apache log directory, /var/opt/apache
While other researchers have linked this threat activity with varying degrees of confidence to the threat actors behind Clop ransomware, Insikt Group does not have enough information to confirm or refute this.
Outlook
Based on the changes in statements from Accellion over the course of reporting on this campaign, the company may still not be fully aware of the extent of compromise associated with these vulnerabilities. Furthermore, based on the number of industries and countries that include clients of Accellion, we suspect that future reports of Accellion FTA exploitation will disclose more companies, industries, and countries than have previously been reported.
As products approach end of life, such as Accellion FTA, they are likely to have less developer support, and update oversight moving forward. Organizations with software or hardware in their technology stack that has reached end of life or is approaching it should continue to monitor these products and develop migration strategies for these tools to more current, supported tools.
Editor’s Note: This post was an excerpt of a full report. To read the entire analysis,  to download the report as a PDF.
to download the report as a PDF.
Related