Additional Entities Targeted by DarkSide Affiliate, TAG-21; Links to WellMess and Sliver Infrastructure


Executive Summary
In mid-May 2021, Insikt Group reported that a further 11 organizations were likely targeted by the same DarkSide affiliate that had compromised Colonial Pipeline. Substantial network communications matching a Recorded Future heuristic behavioral signature were observed on April 27 from 9 of these organizations to a Cobalt Strike command and control (C2) server (176.123.2[.]216) that was used in the operation to target Colonial Pipeline. Insikt Group tracks this ransomware-as-a-service (RaaS) affiliate and its activities internally as TAG-21.
In the two weeks after these organizations were first targeted, 5 of those 9 organizations were also communicating with suspected WellMess and Sliver C2s. Recorded Future Network Traffic Analysis (NTA) confirmed that over 35 entities across multiple verticals and geographies, including Fortune 500 companies, were communicating with the same suspected C2 infrastructure, indicating potential compromise. Almost all of the targeted companies presented external-facing Citrix appliances and software, known to have been targeted by SVR-nexus groups and RaaS affiliates previously. The SVR is Russia’s Foreign Intelligence Service. Based on the data presented in this research, we believe the following scenarios are plausible, in order of decreasing likelihood:
- Two separate groups, RaaS affiliate TAG-21 and an SVR-nexus group, both targeted organizations globally by mass-exploiting vulnerable Citrix servers within enterprises and were co-existing on the 5 overlapping targeted organizations.
- The identified infrastructure linked to WellMess C2s is likely no longer exclusive to SVR-nexus groups and is available to selected RaaS affiliates.
- An SVR-nexus group with access to historical WellMess C2s is engaged in the RaaS ecosystem.
Insikt Group followed responsible disclosure procedures in advance of this publication per Recorded Future’s notification policy.
We strongly recommend that affected organizations and associated entities check for historical or ongoing activity concerning any of the indicators provided in Appendix A of this report, as well as proactively hunt for DarkSide ransomware, Cobalt Strike, WellMess, and Sliver infections. Recorded Future clients are able to detect Cobalt or Silver via the advanced query builder feature in the Recorded Future Platform. See our 2020 Adversary Infrastructure Report to learn about how Recorded Future’s Insikt Group identifies external adversary command and control servers.
Key Judgments
- The significant overlap in targeted organizations shared across 4 distinct C2s, 3 of which are hosted on the same /16 netblock belonging to the same Malaysia-based hosting provider, with 2 of the C2s provisioned within days of each other, indicate this campaign was likely conducted by a single activity group, or 2 groups with overlapping remits.
- The last noted activity between the affected organizations and the C2s was May 8, 2021. Therefore, we suspect the attacker(s) may have either switched over to alternative tooling, or pulled back from targeting these organizations following the unprecedented media coverage of the Colonial Pipeline incident.
- The breadth of targeting across multiple verticals and geographies over an 11-day window coinciding with the Colonial Pipeline incident points to a financially motivated activity group or groups more likely being responsible for the activity. The targeting does not align with traditional SVR intelligence-gathering requirements.
Analysis
WellMess is a custom malware family previously reported as being used by APT29 (aka Cozy Bear, The Dukes, Blue Kitsune) to target COVID-19 vaccine development. However, in more recent reporting, the UK’s National Cyber Security Centre (NCSC) has recalibrated some of its attributory language to pin this activity to the Foreign Intelligence Service of the Russian Federation (SVR). In the same report, NCSC also stated that certain SVR cyber operations used the open source offensive security tool (OST) Sliver, while noting the group had moved on from using tactics, techniques, and procedures (TTPs) that had been previously disclosed.
Suspected WellMess C2 111.90.150[.]176:443
IP address 111.90.150[.]176, hosted on Malaysia-based “Shinjiru Technology Sdn Bhd” infrastructure, was first detected by Insikt Group as a suspected WellMess C2 on April 3, 2020, and has remained active until at least June 5, 2021. The detection was based on a signature keying on distinct characteristics of a TLS certificate configured for WellMess controllers. There were no hostnames resolving to this IP during this time window based on available data; however, the server was updated to run OpenSSH v7.6 on TCP port 22, on or around November 6, 2020, but the WellMess-linked TLS certificate remained installed. Furthermore, the C2 was historically reported by the UK NCSC as being used in the targeting of organizations involved in COVID-19 vaccine development. Network traffic indicated that 10 targeted organizations were communicating with the C2 on May 8, 2021, including:
- A US insurance company
- A US IT services company
- An Australian healthcare district
- A district council in Australia
- A South African management consultancy
- A Swiss state government body
- A South Korean LCD and semiconductor manufacturing company
- Universities in Brazil and Ireland
- An international video game development company
Of the 10 targeted organizations communicating with 111.90.150[.]176, 3 were identified as targets in a previous Insikt investigation into the DarkSide-linked Colonial Pipeline ransomware attack. In that research, we highlighted several organizations that had established network communications with a Cobalt Strike C2 (c2.websecurenetworks[.]xyz |176.123.2[.]216) reportedly used in the Colonial Pipeline intrusion. The 3 organizations were identified communicating with 111.90.150[.]176 just 11 days later on May 8 — the same day Colonial Pipeline announced they had suffered a ransomware attack.
If the overlapping targeting points to an activity group using both Cobalt Strike and infrastructure fingerprinted as a suspected WellMess C2, then given the reported attribution of the Colonial Pipeline intrusion to a DarkSide RaaS affiliate (tracked by Insikt as TAG-21), we can infer the affiliate likely also had access to the suspected WellMess C2s. Another plausible explanation would be the presence of two distinct groups targeting the same organizations.
Suspected WellMess C2 111.90.146[.]143:443
C2 111.90.146[.]143:443 was historically reported by the UK’s NCSC in the advisory outlining APT29’s use of WellMess and WellMail in the targeting of COVID-19 vaccine development. The close overlap in victimology and C2 infrastructure characteristics outlined in this section provide strong evidence that both suspected WellMess C2s covered in this research were deployed by the same activity group.
The 111.90.146[.]143 IP was first identified hosting the distinctive WellMess TLS certificate on port 443 on April 11, 2020 — just 8 days after the first WellMess C2, covered previously, was provisioned. It was hosted on the same provider within the same /16 netblock and it continues to remain active as of June 7, 2021 and there were no hostnames resolving to this IP during this time window based on available data. Like the other WellMess C2, this server was also updated to run OpenSSH v7.6p1 in November 2020, but the WellMess-linked TLS certificate remained installed as well.
Recorded Future identified network traffic that indicated at least 22 organizations, including multiple Fortune 500 companies, were communicating in sustained sessions with the C2 between May 4 and May 8, 2021. 5 of these organizations were previously found to be communicating with the same Cobalt Strike C2 (c2.websecurenetworks[.]xyz | 176.123.2[.]216) used in the Colonial Pipeline attack:
- A South African management consultancy
- A Colombian insurance company
- Universities in Brazil and Ireland
- An international video game development company
Additionally, there were 6 organizations that were also communicating with the suspected TAG-21 WellMess C2 covered in the previous section of this report, 111.90.150[.]176:
- An Australian healthcare district
- A South African management consultancy
- A Swiss state government body
- Universities in Brazil and Ireland
- An international video game development company
Suspected Sliver C2 111.90.147[.]236:80
As with the previously noted suspected WellMess C2s, there was a clear pattern in overlapping victimology relating to the Sliver C2 hosted on 111.90.147[.]236 and the Cobalt Strike C2 used in the Colonial Pipeline incident (176.123.2[.]216). The common hosting provider and netblock, as well as the victimology overlaps between all 3 identified WellMess and Sliver C2s, are a strong indication that a common activity group is likely responsible for this activity.
The suspected Sliver C2 111.90.147[.]236, detected using a unique combination of HTTP header fields, was also hosted in the same /16 netblock belonging to the “Shinjiru Technology Sdn Bhd” as the previously documented WellMess C2s. However, the Sliver C2 was first detected on October 26, 2020 — 6 months after the 2 WellMess C2s were initially provisioned — and remains active as of June 11, 2021. In its advisory published on May 7, the UK’s NCSC highlighted that SVR cyber actors had reacted to the previous publication highlighting APT29 had targeted COVID-19 vaccine development by changing their TTPs and adopting the use of tools such as Sliver.
A total of 21 distinct organizations, globally dispersed across multiple verticals, including Fortune 500 entities, were observed communicating with the Sliver C2 between May 4-8, 2021.
Probable Exploitation of Citrix Devices
Although we cannot confirm the initial infection vector for the suspected intrusions, we believe that TAG-21 used well-documented Citrix exploits given the heavy concentration of Citrix appliances within the list of targeted organizations. Recorded Future found that the overwhelming majority of the organizations targeted by TAG-21 using WellMess, Sliver, and Cobalt Strike were running exposed Citrix appliances and software, such as Citrix Gateway, Citrix NetScaler (now known as Citrix Application Delivery Controller (ADC)), and Citrix Receiver. Figure 1 below shows a Citrix Gateway login portal hosted on an IP identified communicating with the suspected WellMess C2 11.90.150[.]176.
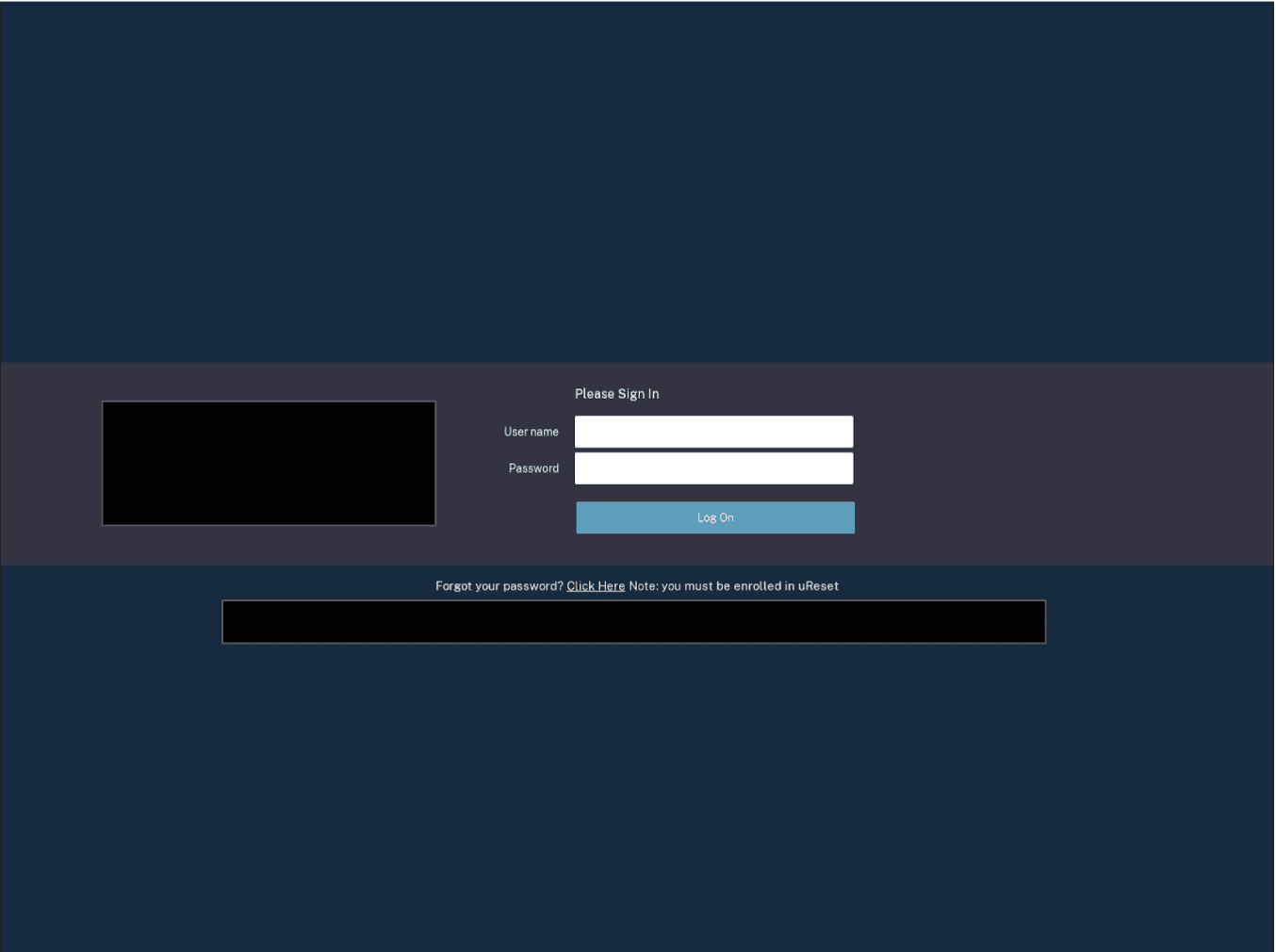 _Figure 1: _Citrix Gateway login for one of the targeted entities. The IP hosting this hostname was found to be communicating with the suspected WellMess C2 111.90.150[.]176:443 on May 8, 2021. (Source: URLScan Pro)
_Figure 1: _Citrix Gateway login for one of the targeted entities. The IP hosting this hostname was found to be communicating with the suspected WellMess C2 111.90.150[.]176:443 on May 8, 2021. (Source: URLScan Pro)
In July 2020, NCSC reported on SVR-linked targeting of COVID-19 vaccine research using WellMess and WellMail, where they stated that the SVR were successful in exploiting Citrix devices vulnerable to CVE-2019-19781 and that “[SVR] … likely seek to take full advantage of a variety of new exploits when publicised”. The risk of this and other vulnerabilities continuing to be exploited by SVR was further emphasized in a joint Cybersecurity Advisory released by the NSA, CISA and FBI on April 15, 2021.
Further, CVE-2020-8300, published on June 8, 2021, affecting Citrix ADC and Citrix Gateway, highlighted that attackers could gain access to a valid user session by hijacking the SAML authentication through executing a phishing attack.
Attribution Considerations
Based on the evidence presented in this research, there are 3 scenarios that could explain the victimology and C2 infrastructure overlaps noted. In order of decreasing likelihood:
- Two separate groups. RaaS affiliate TAG-21 and another separate, unrelated group compromised some of the same organizations by widely targeting vulnerable Citrix appliances using publicly available exploits.
Between April 27 and May 8, 2021, SVR-linked operators with access to suspected WellMess and Sliver infrastructure targeted 5 organizations that were also targeted by TAG-21 using Cobalt Strike and DarkSide ransomware. The same Cobalt Strike server was used to target Colonial Pipeline. The SVR-linked group likely targeted additional organizations using the identified infrastructure linked to WellMess and Sliver. Further, SVR-linked actors are known to have conducted broad scans of vulnerable devices and have exploited CVE-2019-19781 recently, which is also a common technique used by ransomware affiliates to identify exploitable targets, thus supporting the dual-group hypothesis.
- One group. The identified infrastructure linked to WellMess is likely no longer exclusive to SVR-nexus groups and is available to selected RaaS affiliates, including TAG-21.
TAG-21 targeted over 35 organizations, including Colonial Pipeline, in intrusion operations between April 27 and May 8, 2021. The group likely exploited well-publicized Citrix vulnerabilities and had access to C2 infrastructure linked to WellMess, Sliver, and Cobalt Strike. TAG-21 also rented the DarkSide ransomware to encrypt files on selected targeted networks. We cannot confirm whether TAG-21 were granted, commandeered, or were sold access to the servers that matched the profile of expected WellMess C2s, but it is clear that the C2s were updated in November 2020 to run OpenSSH, several months after they were first provisioned and used in COVID-19 vaccine development-related targeting per the NCSC.
- **One group. **Similar to hypothesis (2) but TAG-21 is an SVR-linked group that maintains access to historical WellMess C2s and is engaged in the RaaS ecosystem. We assess this to be the least likely scenario.
The joint NCSC, CSE, NSA, and CISA advisory published on July 16, 2020, detailed APT29’s exploitation of many high-profile VPN and email appliance vulnerabilities, including Citrix devices vulnerable to CVE-2019-19781, and the group’s use of WellMess and WellMail to gain persistence within organizations involved in COVID-19 vaccine development. This was the first time a public attribution was made for WellMess, despite it having been first reported 2 years prior in a 2018 campaign covered by JPCERT and LAC.
Since then, public reporting on the use of WellMess has gravitated towards the same APT29 attribution. In April 2021, both NCSC and NSA publicly attributed the SolarWinds and associated intrusions to the SVR. Soon after on May 7, alongside the FBI and CISA, the NCSC published a follow-up advisory highlighting further TTPs being used by SVR operators in cyber operations. This included a key statement:
The NCSC, NSA, CISA and CSE previously issued a joint report regarding the group’s targeting of organisations involved in COVID-19 vaccine development throughout 2020 using WellMess and WellMail malware. SVR cyber operators appear to have reacted to this report by changing their TTPs in an attempt to avoid further detection and remediation efforts by network defenders. These changes included the deployment of the open-source tool Sliver in an attempt to maintain their accesses.
The 2 suspected WellMess C2s detailed in this report were provisioned a week apart in April 2020, prior to the COVID-19 advisory being published. The same C2s still appear active as of June 11, 2021, but their recent activity as highlighted is much wider than typical SVR intelligence requirements, which predominantly include governmental, diplomatic, think-tank, healthcare, and energy targeting globally. The provisioning of the suspected Sliver C2 from October 2020 is also of note, because it aligns with the reported transitioning of SVR TTPs to using Sliver. However, it is a freely available, open source OST and is almost certainly also used by other activity groups, including RaaS affiliates.
The distribution of targeted organizations across multiple verticals and geographies suggests a potential financial motive, as opposed to a solely espionage-driven operation, especially given the Cobalt Strike C2 overlap with the Colonial Pipeline ransomware attack.
Although the affiliation between TAG-21 and groups such as DarkSide and APT29 remains unclear as of this writing, TAG-21 maintains demonstrable operational cyber capabilities to conduct widespread disruption with their targeting of Colonial Pipeline, and their links to the targeting of more than 35 other entities. We have not observed activity from the targeted organizations included in this research to the 4 C2s since May 8, 2021, and suspect that TAG-21, or another overlapping group, has moved to alternative tooling or disbanded following the extensive media coverage of DarkSide and their activities. However, the potential implications of TAG-21’s use of infrastructure linked to WellMess, Sliver, and Cobalt Strike demonstrates an access to capabilities that could prove effective in future operations.
Appendix A — Indicators
| c2.websecurenetworks[.]xyz|176.123.2[.]216 – Cobalt Strike C2 set up with Google Malleable profile68e7bd3cf41bbc3df1159a3481e911d2d4fd588dfdbedcfe5a96dee3777eb920 – Cobalt Strike sample that calls out to 176.123.2[.]216 8dafde4809fae1db6c2de051de9a005c43c4b0218af4e3c1f30fa6a0f65316fc – Cobalt Strike sample that calls out to 176.123.2[.]216 111.90.150[.]176 – Suspected WellMess C2 111.90.146[.]143 – Suspected WellMess C2 111.90.147[.]236 – Suspected Sliver C2 |
Related