Inside the Mind of Cybercriminals
To learn more about how cybercriminals operate on the dark web, we asked our own Andrei Barysevich a few questions. Below is what he had to say.
You have spent a great deal of time studying actual cybercrime activity, forums, and behavior in recent months. What are some of the things you’ve learned that you think all enterprise defenders should know?
Information sharing amongst security specialists is crucial; in the eyes of a criminal, no company is unique. As a rule of thumb, perpetrators will initially cast a wide net and move downstream toward the easiest prey. It’s more likely to become a victim via common attack vector, rather than to experience a highly sophisticated and tailored attack.
On the other hand, security specialists should never underestimate the determination of an attacker. Highly valuable and quickly sold on underground information such as payment, healthcare, and personally identifiable records, as well as sensitive M&A information, must be identified as a targeted asset, quarantined, and stored encrypted. The actionable contingency plan must be rehearsed and quickly activated in the case of a breach including a clear response strategy if extortion is attempted. Security professionals must be aware of upcoming threats and successful mitigation practices when establishing a robust and secure network, making sure the proper data backups are in place.
What are some common misperceptions that security pros have about cybercrime and the people who do it?
The common misperception about cybercriminals we often observe is that it is assumed that illicit actors have diverse skills and experience, allowing them to initiate a wide range of attacks, subsequently earning a hefty amount of money as a result. In reality, the current underground has shifted toward mass plug-and-play automated services, offering the opportunity to participate in illicit activities to a broad number of novice members. Recorded Future has recently identified a survey, conducted among members of a closed underground community, revealing that the majority of cybercriminals are earning a mere $1,000 to $3,000 a month, while only 20% are earning significantly larger amounts of $20,000 a month or more.
Who are these criminals? Are they part of established criminal groups or one-man shows?
For the most part, the largest demographic of members participating in underground communities are lone actors with a clean criminal record and without any ties to organized syndicates. These criminals tend to maintain a stable day job while partaking in illegal activities mostly on an occasional basis. Often these actors are introduced to the life of cybercrime during their early college years and remain active many years to follow.
A separate and significantly more sophisticated cohort are cyber-criminal syndicates which maintain a strict hierarchy, comprised of highly skilled members, each with a very narrow set of responsibilities.
A typical group is controlled by a single mastermind "boss" — a very intelligent and highly educated person — and includes bankers with extensive connections in the financial industry to arrange money laundering and cash out of stolen funds. Additionally, forgers are responsible for fake documents and supporting paperwork and professional project managers oversee the technical aspects of operations, software engineers, and skilled hackers. Some groups include ex-law enforcement agents responsible for information gathering as well as counter-intelligence operations.
Team members tend to have strong ties in real life and often are respected members of their communities, viewed by many as successful businessmen and entrepreneurs. The group will often have a diversified investment portfolio and maintain a presence in real estate, hospitality, and auto-related businesses.
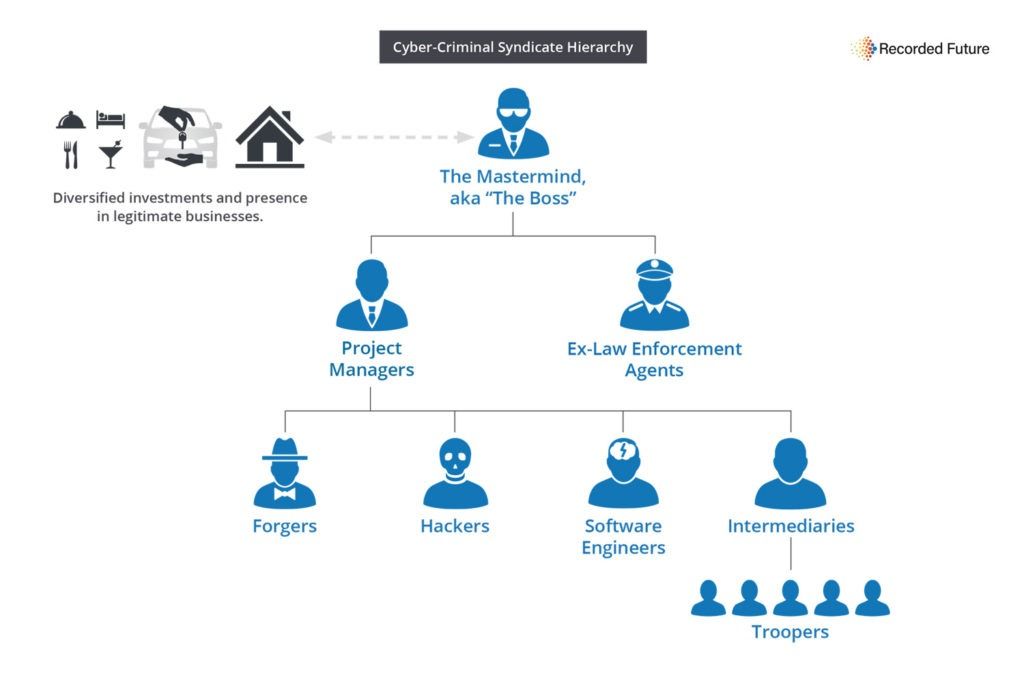
Typical hierarchy in a cyber-criminal syndicate.
Cyber-criminal syndicates don't regard themselves as ordinary street criminals and rarely cross paths with everyday gangsters, preferring to remain in the shadows and avoid unnecessary attention from both law enforcement and local mafia branches.
However, on certain occasions, requiring the involvement of a vast number of "troopers," often, related to large cash-out operations, a one-time project can be launched through a chain of intermediaries.
What types of research do you feel are most beneficial for an enterprise security team?
We have to understand no silver bullet will solve every security problem. An effective security perimeter has to include the combination of:
- Automated tools responsible for identification of unusual behavior.
- Alerts on known IOCs and TTPs.
- Intelligence obtained from underground communities.
- Response procedures and guidelines.
Direct access to deep and dark web is crucial, but for a variety of safety reasons, might not be a viable option. Hidden criminal communities are not very fond of researchers, and in certain situations, an inexperienced researcher can draw unnecessary attention to the company and put it in danger.
In one of the recent cases, a poorly trained researcher has openly inquired about penetration solutions in newly adopted infrastructure which was tested at a limited number of corporate locations, immediately observing a sudden surge of malicious activity.
To avoid this, we would recommend utilizing the help of professional threat intelligence providers that operate undercover on a day-to-day basis and are familiar with all of the complex politics of these communities.
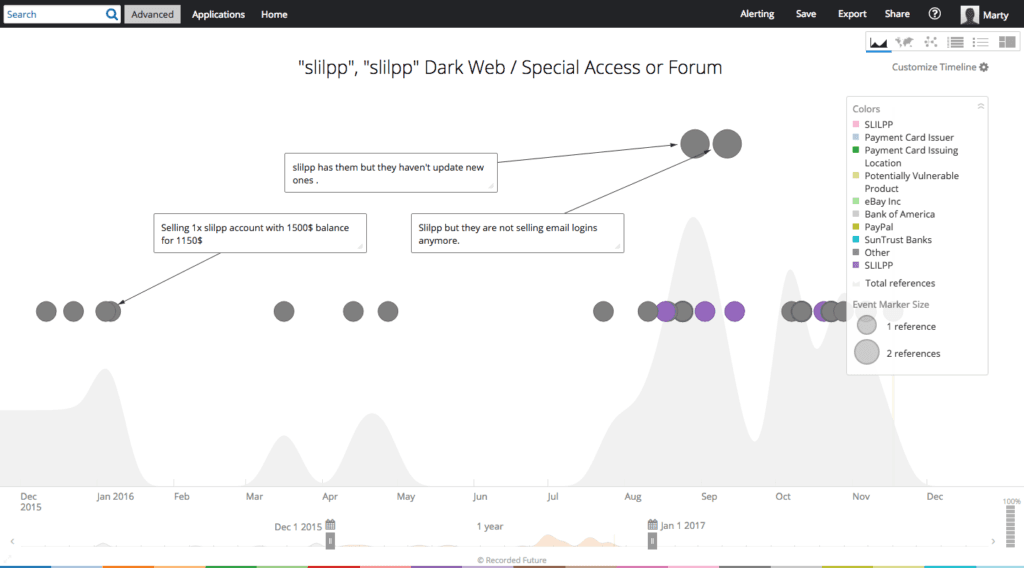
Timeline analysis of SlilPP — the largest marketplace of compromised accounts.
Several providers allow users to research deep and dark web sources in a safe and secure manner, without risking the integrity of the organization.
Companies also must foster internal security teams, ensuring they are capable of discovering relevant and actionable data as well as stimulating the unrestricted environment, providing the opportunity to initiate counter-measures quickly, and minimizing the red-tape procedures.
To learn how Recorded Future’s threat intelligence from the dark web can help your organization, request a demo.
Related