Chinese State-Sponsored Cyber Espionage Activity Supports Expansion of Regional Power and Influence in Southeast Asia

Editor’s Note: The following post is an excerpt of a full report. To read the entire analysis, click here to download the report as a PDF.
This report profiles trends in Chinese state-sponsored cyber espionage activity targeting Southeast Asian countries. The activity was identified through large-scale automated network traffic analytics and expert analysis. Data sources include the Recorded Future Platform, SecurityTrails, DomainTools, PolySwarm, Farsight, Team Cymru, and common open-source tools and techniques. The research will be of most interest to individuals engaged in strategic and operational intelligence relating to the activities of Chinese military and foreign intelligence agencies in cyberspace and network defenders with a presence in Southeast Asia.
Executive Summary
Recorded Future’s Insikt Group tracks Chinese state-sponsored cyber espionage operations targeting government and private sector organizations across Southeast Asia. In this report, we highlight multiple examples of activity reported to Recorded Future clients throughout 2021. The identified intrusion campaigns almost certainly support key strategic aims of the Chinese government, such as gathering intelligence on countries engaged in South China Sea territorial disputes or related to projects and countries strategically important to the Belt and Road Initiative (BRI).
The activity highlighted includes a group we track as Threat Activity Group 16 (TAG-16), which has compromised several high-profile military and government organizations across Southeast Asia throughout 2021 using custom malware families such as FunnyDream and Chinoxy. Many of the governments targeted by TAG-16 are engaged in ongoing disputes with China over territorial claims in the South China Sea. Additionally, we highlight 2 separate suspected Chinese state-sponsored intrusion campaigns targeting entities in Laos and Cambodia. Both are likely intended to support BRI objectives. Victims in these 2 respective campaigns include the National Committee for Special Economic Zones (SEZs) and National Enterprise Database (NED) in Laos and Cambodia’s Sihanoukville Autonomous Port (PAS).
Key Judgments
- Our research highlights China’s continued strategic and tactical interest in government and private sector organizations in Southeast Asia. This targeting is almost certainly linked to a range of objectives intended to support a deepening of regional influence, including traditional intelligence gathering against regional rivals and allies, economic intelligence gathering against BRI-linked targets, and the South China Sea disputes.
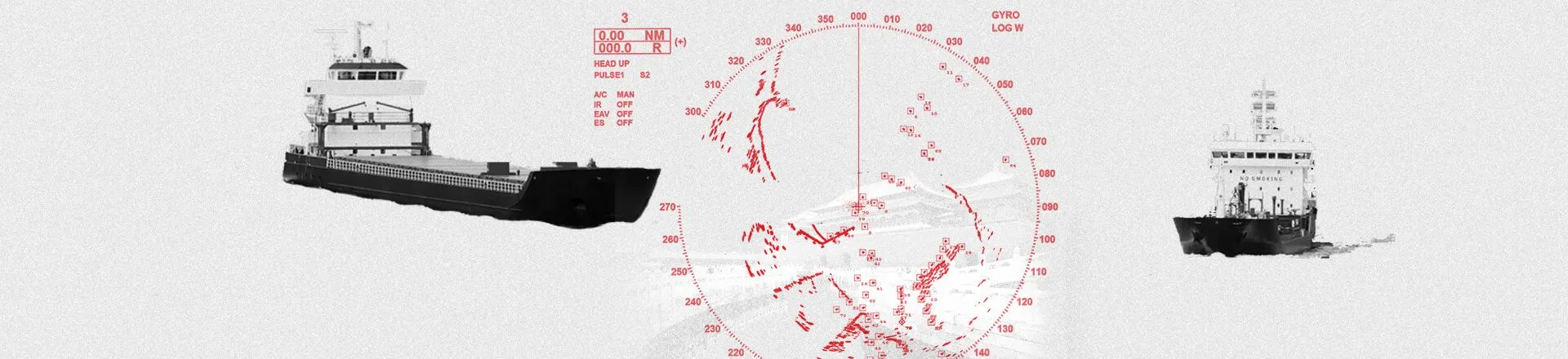
- The operational tasking of TAG-16 is likely linked, in part, to gathering intelligence on South China Sea-related issues. Notably, Insikt Group identified the compromise of navies, prime minister’s offices, ministries of defense, and ministries of foreign affairs across several countries with a presence in the South China Sea.
- The targeting of Cambodia’s Sihanoukville Autonomous Port and Laos’s National Committee for SEZs is likely linked to China’s wider strategic objectives under the BRI. PAS has high strategic significance given its location along the Maritime Silk Road route, while the Lao government has promoted the development of SEZs as an entry point for private sector development, including domestic and foreign direct investment (FDI).
Editor’s Note: This post was an excerpt of a full report. To read the entire analysis, click here to download the report as a PDF.
Related