Suspected Chinese Group Calypso APT Exploiting Vulnerable Microsoft Exchange Servers

Beginning on March 1, 2021, Recorded Future’s Insikt Group identified a large increase in victim communications to PlugX command and control (C2) infrastructure publicly attributed to the suspected Chinese state-sponsored group Calypso APT. We believe that this activity is highly likely linked to the exploitation of recently disclosed Microsoft Exchange vulnerabilities (also known as ProxyLogon — CVE-2021-26855, CVE-2021-27065). Our observations align with recent reporting by ESET in which the group was identified targeting vulnerable Exchange servers to deploy a web shell and ultimately load the PlugX malware post-exploitation.
Targeted organizations were geographically widespread and covered multiple industries, supporting wider industry commentary that the targeting is likely opportunistic. Victims of identified post-exploitation activity included local and national governments, as well as software, defense, finance, IT, legal, and manufacturing organizations in Australia, the Czech Republic, Germany, India, Italy, Kazakhstan, Macedonia, Nepal, Switzerland, Ukraine, and the United States. We identified several high-value targets likely impacted, including a US electronic parts distributor serving defense and aerospace sectors, an Indian heavy engineering company with a presence in strategic defense sectors, local governments in the US and Australia, and a North Macedonian national government department.
The activity identified by Insikt Group began on March 1, 2021, prior to the disclosure of the vulnerabilities. This indicates the group likely had access to the exploit as a zero day prior to Microsoft’s disclosure, corroborating a similar assessment made by ESET.
Infrastructure and Malware Analysis
Insikt Group has been tracking a cluster of PlugX C2 servers and related infrastructure that overlaps with public reporting on Calypso APT by PTSecurity and ESET. We first reported on activity linked to this infrastructure cluster in August 2020 to our customers, following the identification of suspected intrusion activity targeting an Afghan telecommunications provider and government body. The identified cluster is outlined in Table 1 below:
| Current Hosting IP | Domain | Registrar | Registered |
| 91.220.203[.]197 ()
[PlugX C2] |
www.membrig[.]com | NAMECHEAP INC | 2018-12-13 |
| 103.30.17[.]44 () | www.draconess[.]com | NAMECHEAP INC | 2018-02-05 |
| 91.220.203[.]86 ()
[PlugX C2] |
www.rosyfund[.]com | GuangDong NaiSiNiKe Information Technology Co Ltd. | 2018-12-13 |
| 45.144.242[.]216 ()
[PlugX C2] |
www.sultris[.]com | NAMECHEAP INC | 2018-02-02 |
| 91.220.203[.]86 ()
[PlugX C2] |
www.yolkish[.]com | NAMECHEAP INC | 2018-01-29 |
| 45.76.84[.]36
() |
mail.prowesoo[.]com | NAMECHEAP INC | 2018-02-02 |
| 45.76.84[.]36
() |
www.waxgon[.]com | NAMECHEAP INC | 2018-01-31 |
| 107.248.220[.]246
() |
www.rawfuns[.]com1 | NICENIC INTERNATIONAL GROUP CO., LIMITED | 2018-02-05 |
| 45.76.84[.]36
() |
mail.aztecoo[.]com | NICENIC INTERNATIONAL GROUP CO., LIMITED | 2018-02-05 |
Table 1: Suspected Calypso APT infrastructure cluster
Examining the PlugX cluster allowed us to make the following high-level observations regarding Calypso APT’s infrastructure tactics, techniques, and procedures (TTPs):
- The majority of domains used the “www.” subdomain for C2 with no DNS record for the root domain
- Most of the domains were registered using registrar NameCheap
- C2 domains kept operational for more than 2 years
- Operational infrastructure has been hosted on:
- M247 Ltd
- Global Network Transit Limited
- PEG TECH INC
- Web Werks India Pvt. Ltd
- Choopa LLC
Insikt Group identified the following malware samples linked to the identified infrastructure, 2 of which were listed within ESET’s reporting. At this time, we have not undertaken extensive analysis on these samples:
| File Name | SHA256 Hash | Malware Variant | C2 IP/Domain |
| FORTITRAY.EXE | 913fa95829ba3f77c0673f0af5c6afaeb6e6a2bdd0e98c186df65f1d27b9dc1f | Unknown | www.yolkish[.]com |
| msf.exe | f32866258b67f041dc7858a59ea8afcd1297579ef50d4ebcec8775c816eb2da9 | Meterpreter | 45.144.242[.]216 |
| SRVCON.OCX | 5d803a47d6bb7f68d4e735262bb7253def6aaab03122b05fec468865a1babe32 | PlugX Loader | yolkish[.]com and rawfuns[.]com |
| rapi.dll | ab678bbd30328e20faed53ead07c2f29646eb8042402305264388543319e949c | Whitebird Loader | yolkish[.]com and rawfuns[.]com |
Calypso’s Targeting of Microsoft Exchange Servers and Victimology
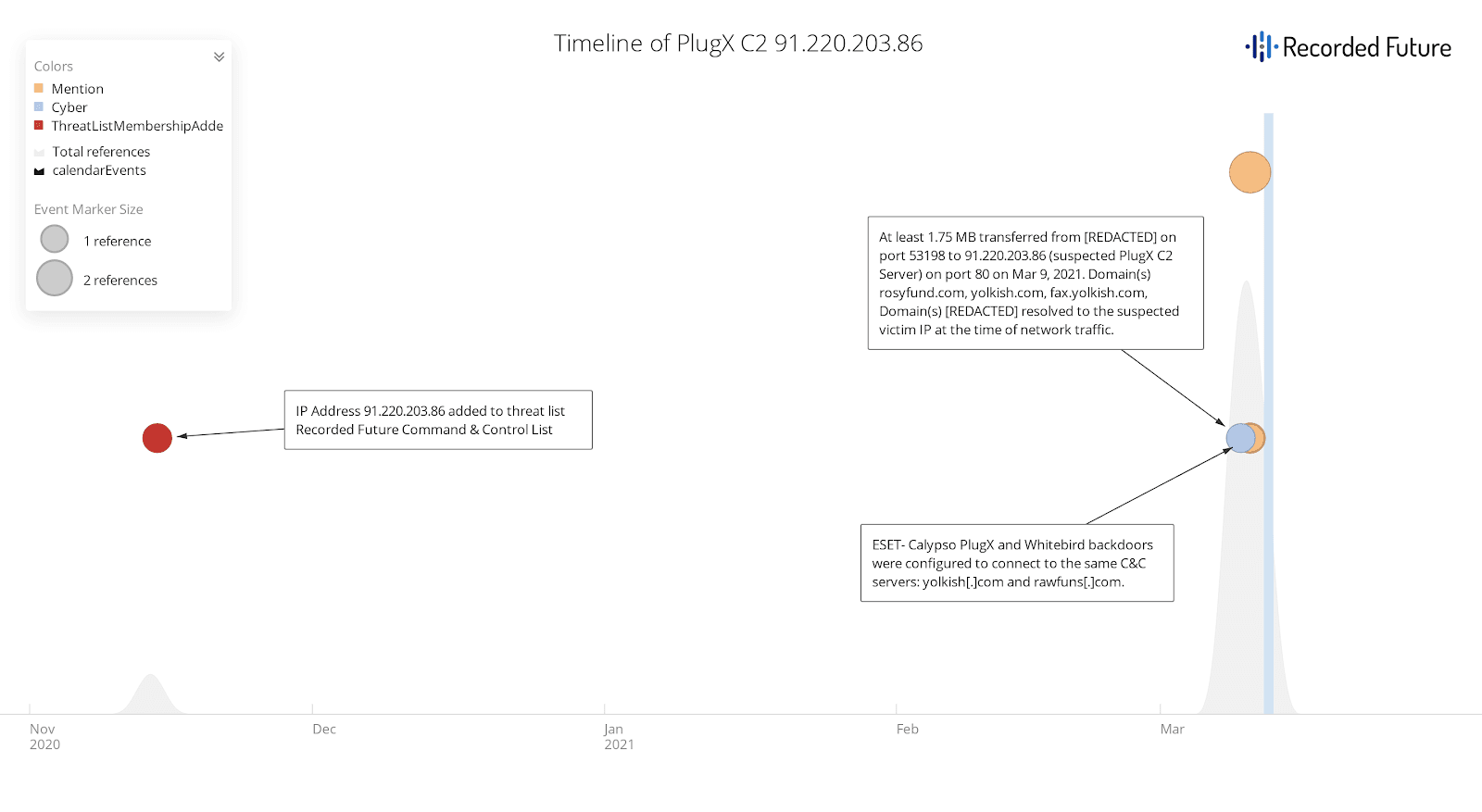 Figure 1: Timeline of PlugX C2 91.220.203[.]86 (Source: Recorded Future)
Figure 1: Timeline of PlugX C2 91.220.203[.]86 (Source: Recorded Future)
Recorded Future first identified the IP 91.220.203[.]86 as a suspected PlugX C2 on November 14, 2020. Using Recorded Future Network Traffic Analysis (NTA), we detected a large increase in activity linked to this C2 server from victim IP addresses hosting Microsoft Exchange services from March 1, 2021 onwards. We believe that this increase in activity is very likely linked to the widespread exploitation of recently publicized vulnerabilities impacting Microsoft Exchange, which were first disclosed on March 2, 2021.
On March 10, 2021, ESET reported on a range of threat activity groups, largely Chinese state sponsored, exploiting a pre-authentication remote code execution (RCE) vulnerability chain that allows an attacker initial access to internet-facing Microsoft Exchange servers:
- CVE-2021-26855 [ProxyLogon]
- CVE-2021-26857
- CVE-2021-26858
- CVE-2021-27065
First reported by Microsoft on March 2, exploitation of these vulnerabilities was initially linked to a China-based activity group tracked as HAFNIUM by Microsoft Threat Intelligence Center (MSTIC). ESET’s findings indicate that the vulnerabilities began to be exploited by additional Chinese activity groups, including Tick, LuckyMouse, and Calypso APT, in late February and early March. This activity occurred prior to the public disclosure of these vulnerabilities and suggests that these additional Chinese activity groups also had access to the exploit as a zero day. While initially exploited by HAFNIUM in “limited and targeted attacks”, from at least February 27 onwards, the vulnerabilities were subject to mass exploitation by an increasing number of groups (1,2,3).
This aforementioned PlugX C2 IP 91.220.203[.]86 currently hosts the domain www[.]yolkish[.]com, referenced within the aforementioned ESET reporting on the exploitation of Microsoft Exchange vulnerabilities. In this activity, the group was identified dropping web shells in the following locations following exploitation:
C:\inetpub\wwwroot\aspnet_client\client.aspx
C:\inetpub\wwwroot\aspnet_client\discover.aspx
Mitigations
Using this web shell access, Calypso APT was then identified loading the aforementioned PlugX and Whitebird malware samples through DLL search-order hijacking using legitimate executables. Insikt Group identified over 30 likely victim organizations communicating with the 91.220.203[.]86 PlugX C2 across a range of geographies and industry verticals, including local and national government, software, defense, finance, IT, legal, and manufacturing organizations in Australia, Czech Republic, Germany, India, Italy, Kazakhstan, Macedonia, Nepal, Switzerland, Ukraine, and the United States. Several of these organizations were not typical targets of cyber espionage activity, supporting wider industry commentary that much of the targeting is likely opportunistic.
We recommend the following measures to detect and mitigate activity associated with the identified Calypso APT activity:
- Configure your intrusion detection systems (IDS), intrusion prevention systems (IPS), or any network defense mechanisms in place to alert on — and upon review, consider blocking connection attempts to and from — the external IP addresses and domains listed in the appendix.
- Recorded Future proactively detects and logs malicious server configurations in the Command and Control Security Control Feed. The Command and Control list includes tools used by Calypso and Chinese state-sponsored threat activity groups, such as PlugX. Recorded Future clients should alert on and block these C2 servers to allow for detection and remediation of active intrusions.
- If you are running on-premises Microsoft Exchange, ensure the latest updates are installed and that the patch is validated.
- Following deployment of updates, follow industry guidance on hunting for web shells installed on Exchange servers post-exploitation (1, 2).
Indicators of Compromise
Readers can access the indicators listed below in our public Insikt Group Github repository: https://github.com/Insikt-Group/Research.
Related
