China’s New Cybersecurity Measures Allow State Police to Remotely Access Company Systems


Recorded Future’s Insikt Group analyzed new cybersecurity provisions issued by the Chinese Ministry of Public Security. This report will be of greatest interest to any corporation conducting business within China.
Executive Summary
In August 2017, Recorded Future analyzed the security and risk implications for international companies of China’s Cybersecurity Law, assessing that the law gave China’s Ministry of State Security (MSS) sweeping new powers. In particular, the Cybersecurity Law mandated that several sectors be subject to “national security reviews, ” which could allow the MSS to identify vulnerabilities in foreign technologies that China could subsequently exploit in espionage operations.
On November 1, 2018, China issued new provisions to the law titled “Regulations on Internet Security Supervision and Inspection by Public Security Organs” (公安机关互联网安全监督检查规定). The regulations, likely evolved to clarify portions of China’s 2017 Cybersecurity Law, give the Ministry of Public Security (MPS) broad powers over the computer networks of companies in China. These ostensibly include the authority to remotely conduct penetration testing on almost any business operating in China and copy any information related to user data or security measures found during the inspection.
These new provisions specify no limits on the scope of vulnerability or security inspections and require extremely minimal reporting to be provided back to the corporation. Further, the regulations continue to use vague terminology and do not limit the scope of in-person or remote inspections for network security testing. We assess that the combination of existing MSS regulations with these new Cybersecurity Law provisions for the MPS will support Chinese government attempts to both censor and surveil foreign companies.
Key Judgments
- New regulations give the Ministry of Public Security (MPS) authority to conduct on-site and remote inspections of any company with five or more computers connected to the internet. This wide definition accounts for almost every foreign company in China.
- As of November 2018, the MPS is allowed to copy user information, log security response plans during on-site inspections, and check for vulnerabilities. This information could be leveraged by state surveillance or security organs to monitor a company’s inner workings as well as its customers.
- The People’s Armed Police (PAP) will be present during on-site inspections to ensure that companies comply.
- The MPS can also conduct remote inspections of companies to check for vulnerabilities. These new regulations make remote inspections easier to conduct than physical inspections and are not bound by time or limited in scope. For remote inspections, the MPS is able to involve third-party “cybersecurity service agencies,” increasing the risks of both vulnerability discovery and data leakages.
- These regulations also empower MPS to enforce Chinese prohibited content laws, using network security as a justification to monitor for adherence to censorship laws.
Background
The Ministry of Public Security (MPS) is China’s primary police and security authority. While the organization has a wide variety of internal security duties, such as border security and administrating national identification cards, they are also tasked by various national cybersecurity regulations to handle and collect large amounts of data.
Among many responsibilities, the MPS is in charge of China’s Golden Shield Project (金盾工程), a massive series of legal and technological initiatives — including China’s Great Firewall — meant to improve intelligence assessments and surveillance capabilities of the national police force. Part of this initiative involves the expansion of facial recognition software used with a nationwide system of surveillance cameras, designed to better locate and clamp down on dissenters.
As of 2017, China’s National Cybersecurity Law (CSL) made the MPS one of the organizations responsible for “cybersecurity protection, supervision, and management” within its larger scope of investigating matters in public and internal security, and MPS is specifically tasked with punishing actors that violate the CSL.
The new provisions to the CSL, “Regulations on Internet Security Supervision and Inspection by Public Security Organs,” produced by the MPS specify what measures its branches at the county level and above must implement in order to better protect, supervise, and manage cybersecurity under the CSL. This is an extra authority under the Cybersecurity Law, which already gave China’s Ministry of State Security the power to conduct national security reviews of foreign technology. However, articles within the new provisions contain sweeping measures that should alarm any business currently operating in China.
Analysis
In 2017, Recorded Future analyzed the national security review provisions of the CSL to reveal the sweeping powers given to Chinese state security organizations over foreign technology, especially companies that operated “critical information infrastructure.” While the new CSL regulations do not address critical information infrastructure, they do focus on businesses at large.
These November 2018 updates empower public security organs under the MPS to conduct safety supervision and inspection of internet service providers (ISPs) and networked units to ensure that they are “fulfilling network security obligations stipulated by laws and administrative regulations,” according to Article 2 of the new regulations. These regulatory efforts are framed to resemble cybersecurity legislation enacted by other developed countries, with the crucial difference being that broadened state control is the overriding objective rather than data protection.
According to the Yunnan Network Security Corps, a branch under the MPS, the definition of a networked unit is “a unit with a fixed IP or with five or more computers connected to the internet to conduct internet or internet-related activity.” Networked units are, according to the same Yunnan MPS site, usually registered through the MPS in order to obtain hosting rights on Chinese servers, but also registered through other internet security-related organizations at the municipal and county level.
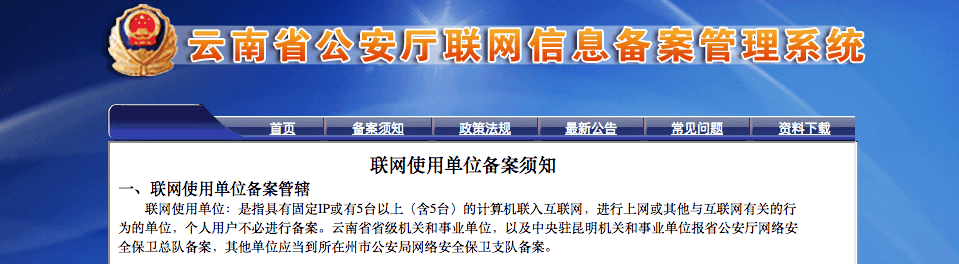
Screenshot of Yunnan Network Security Corps’s description of a networked unit.
The law specifies that public security branches at the county level and above can conduct inspections on networked units and ISPs that provide any of the following: internet access, data centers, content distribution, domain name services, internet information services, public internet services, or other internet services. This broad authority encompasses nearly any company providing any type of internet-related service, from a SaaS company to a company providing internal internet services to its employees, as long as that company has at least five computers that use a router for their internet connection.
In-Person Inspections
According to Article 15, when conducting in-person inspections, MPS branches are entitled to enter almost any company area related to networked units (联网使用单位) in order to check computer systems for network security compliance. Upon entering business premises, computer rooms, and workplaces, MPS officers can view or copy any information related to the inspection. This includes but is not limited to: any and all user information, technical measures for the network, and information security protection, hosting, or domain name information, as well as any content distribution the organization may be conducting.
This inspection also covers other provisions within the wider CSL, including inspecting whether the publication of prohibited information is prevented or censored. According to Articles 10, 11, and 21, companies hosting content that the Chinese government determines as “prohibited information” found through an inspection can be prosecuted under the Cybersecurity Law. We assess that the MPS will use this provision as a means to ensure that companies are complying with prohibited content and censorship laws. Because the scope of inspections given by the regulations is so broad, it is not clear if content published outside of the Chinese language internet also applies. However, not only can refusal to cooperate be punishable by law, but the provisions also require at least two members of the People’s Armed Police (PAP) to assist in and sign off on all inspections.
Article 16 states that MPS branches are able to conduct remote inspections of networked units and ISPs for network security loopholes. It is not immediately clear what the scope of a remote inspection entails; it could encompass anything from a traditional penetration test to the installation of system backdoors. Further, Article 18 includes language that makes remote inspections easier than on-site inspections to conduct, as remote inspections do not require permission from the company. In fact, Article 16 only requires that the MPS notify the inspected company of the date and scope of the inspection. The regulations do not even limit the scope or time frame for an inspection. Finally, Article 17 empowers the MPS to involve third-party “cybersecurity service agencies” in these inspections, a provision which substantially increases the risk of vulnerability discovery and data leakages.
Additionally, Article 6 mandates that the MPS write share reports of the inspections with relevant government departments, while Article 19 requires that MPS branches supervise and guide organizations to mitigate against any hidden network security risks found during inspection. Because the provisions do not specify which PRC government departments are “relevant,” the information obtained could theoretically be leveraged by its state or foreign surveillance arms to monitor corporate and customer data.
Most alarmingly, the regulations contain no obligation for the MPS to disclose the full results of remote or on-site inspections to companies themselves. Article 18 stipulates that a supervisor within the organization being inspected must sign an inspection report produced by the MPS during an on-site inspection; however, there is no requirement for the MPS to provide a report to the organization during a remote inspection. The only required communication between the MPS branch and the organization prior to a remote inspection is an announcement of the inspection time, scope, and “other matters.” Thus, companies subject to remote inspection may not know exactly where in their network MPS officers are conducting inspections, and could be completely ignorant of inspection results.
Since the scope of inspections is not limited in these new regulations, Article 16 may also empower MPS officers to access parts of the company’s enterprise not even related to or within territorial China. The implications for unlimited remote inspections on the networks of international corporations could be far-reaching and create significant risk for customers and international operations.
Impact for Businesses Operating in China
The breadth of inspection authority granted to the MPS by these new regulations could impact almost all foreign businesses operating in China. The extremely broad criteria and lack of specifics in this regulation mean that most companies operating in China could be subjected to MPS inspection for any reason, at any time. Further, with the scope of both on-site and remote inspections so undefined, we assess that the international operations and customers of inspected companies could be at risk of exposure to the Chinese government and security services as well. Thus, almost all foreign businesses will be subject to in-person facility searches, copying of company user data, invasive checking for “illegally published materials,” and remote inspection of company networks.
As recommended in Recorded Future’s previous analysis of China’s Cybersecurity Law, companies need to evaluate three possible risk scenarios:
- Risk to a company’s own machines or networks
- Risk to a company’s product, service, and intellectual property
- Derivative risk to customers, clients, or users around the world
These new regulations place companies’ network infrastructure, data, and proprietary information at a higher risk for MPS intrusion and surveillance operations. Corporate networks and products can be subjected to extensive inspections for “illegal material” and companies could be prosecuted if such material is found. Customers, data, and systems in territorial China are not only at risk of having their data held by the Chinese government, but also are at increased risk for third-party data breaches and Chinese government surveillance.
The risks to companies laid out in Recorded Future’s previous analysis are exacerbated by these new CSL provisions. Because most company products and services sold in China are not dissimilar to their international equivalents, vulnerabilities found by the MPS can be utilized to exploit both domestic and international users. If companies choose not to comply with the new provisions, however, they may need to evaluate a fourth possible risk scenario: risk to employee safety. Any pushback against inspections could be noted and reacted to by the People’s Armed Police officers present.
Recorded Future recommends that all international corporations operating in China take measures to evaluate their technology footprint within the country, their evacuation and government relations policies, and their system architecture to minimize the impact of the law and effectively address the worst-case scenario if subjected to an MPS inspection. Altering company system architecture to keep connections between Chinese and international operations as segmented as possible is important to prevent inspections from spilling into corporate networks or databases with no connection to territorial China. Further, keeping one’s employees safe and informed of the inspections should remain a top priority for companies operating within the country.
As a baseline, companies should properly inspect their systems for known vulnerabilities. To quantify the risk to global operations, offices operating within China should ascertain which parts of their infrastructure have already been registered as networked units (联网使用单位) and prioritize these units when updating and segmenting their systems. While these new regulations now provide the legal authority for MPS officers to probe company systems, patching against known vulnerabilities will prevent inspectors from easily gaining unwanted access or escalating privileges. Organizations or companies operating in China must also determine whether their products or services host material that the Chinese government may deem illegal to publish, and make a decision on where and how to host this data to minimize the impact of the law.
Editor’s Note: This is not meant to replace legal advice or counsel. Please make sure to consult local legal counsel for concerns and/or advice regarding regulations and legislation that may impact your organization.
Related