Top Exploited Vulnerabilities in 2020 Affect Citrix, Microsoft Products

Editor’s Note: The following post is an excerpt of a full report. To read the entire analysis,  to download the report as a PDF.
to download the report as a PDF.
This analysis focuses on ransomware, exploit kit, phishing attack, or remote access trojan co-occurrences with vulnerabilities from January 1 to December 31, 2020. We analyzed thousands of sources, including code repositories, underground forum postings, and dark web sites. This is a follow-up to our 2019 report, and the intended audience includes information security practitioners, especially those supporting vulnerability risk assessments.
Executive Summary
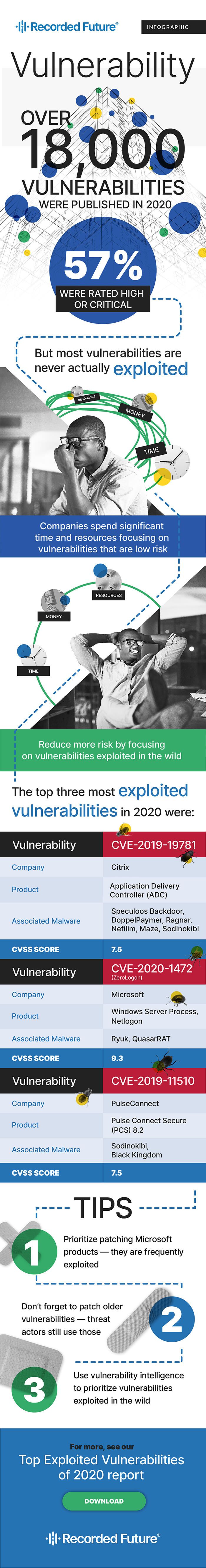
This report highlights the top, most weaponized vulnerabilities in 2020 based on exploitation across all industries and associations with multiple types of malware. For the first time since this report’s inception in 2015, no vulnerabilities in Adobe products make the list. This contrasts the first report published in 2015, where eight of the 10 top exploited vulnerabilities were Adobe products.
Similar to 2019, Recorded Future observed a majority of the top exploited vulnerabilities targeting Microsoft products (seven out of 10). One noticeable difference is that only one of these vulnerabilities targets Internet Explorer, compared to four in 2019. Also unique to 2020, the number of new vulnerabilities released initially dropped in March 2020 after the pandemic began. Ultimately, there were more than 18,000 new vulnerabilities identified in 2020.
Despite fewer overall vulnerabilities identified, the diversity of products impacted this year versus prior years stands out. The shift to working from home for employees globally opened up new avenues for exploitation against a homebound workforce. As such, products such as Citrix’s Application Delivery Controller (ADC), PulseSecure’s Pulse Connect, and Oracle’s WebLogic appear on the list as targeted products for the first time.
The inclusion of more products on the list highlights that even official vulnerability databases and conventional scanning tools cannot arm organizations with one key metric: the overlap between the vulnerabilities in the systems you use and the ones that are being actively exploited by threat actors. Insight into weaponization is necessary to adequately prioritize vulnerabilities to patch, as often less than 1% of vulnerabilities have been weaponized within the past month or year. As such, it is imperative that security professionals know which vulnerabilities that impact a company’s technology stack are included in exploit kits, used to distribute ransomware, a remote access trojan (RAT), or are currently being used in phishing attacks.
Key Judgements
- Seven of the top 10 vulnerabilities target Microsoft products, similar to 2019 and past reports.
- Only one CVE targeting Internet Explorer, CVE-2020-0674, is on the top 10 list, compared to four in 2019.
- There are no Adobe products included in the top targeted technologies, as Adobe Flash Player officially reached its end of life in December 2020.
- Citrix, PulseSecure and Oracle made their first appearances as targeted technologies in the annual top exploited list.
- Three of the top vulnerabilities were included in the top 10 of 2020 Patch Tuesday vulnerabilities: CVE-2020-1472, CVE-2020-0796 and CVE-2020-0674. The top exploited Patch Tuesday CVEs are also included in this report.
- Only two vulnerabilities were repeated from the 2019 top 10 list: CVE-2017-11882 and CVE-2012-0158. Both vulnerabilities were listed on the US-CERT’s top 10 exploited vulnerabilities between 2016 to 2019.
Editor’s Note: This post was an excerpt of a full report. To read the entire analysis,  to download the report as a PDF.
to download the report as a PDF.
Related